Cerber ransomware strikes again, Windows Defender is defenseless
2 min. read
Published on
Read our disclosure page to find out how can you help Windows Report sustain the editorial team Read more
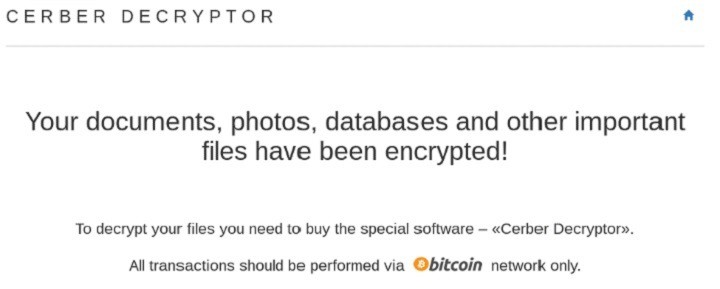
The notorious Cerber ransomware is attacking Windows users again, and this time it’s more powerful than ever. The Cerber3 ransomware is a third generation ruthless malware that encrypts your files, prompting you to pay money to regain access to your documents.
Hacker don’t sleep even when times are quiet, and the fact that Cerber3 has been let loose can only mean that new generations of ransomware will soon emerge. Unfortunately, it appears that antivirus programs, Windows Defender included are basically…defenseless against this threat.
Cerber ransomware attacks Windows users
my files are converted as a extension of .cerber3 which is a encrypted virus and it has attack my files
please help me to decrypt this extension without paying a money to ransomware please help me to recover my files by decryption
Cerber3 is usually distributed via infected email attachments or links to maliciously crafter websites. According to user reports, the attackers send you a notification email on behalf of a shipping company, allegedly to inform you they couldn’t deliver you a package. Most users are intrigued by this possibility and open the email or click on the malicious link although they know nobody was supposed to send them anything. Yes, curiosity killed the cat.
The Cerber3 ransomware attacks all Windows versions, and encrypts all productivity files, adding the .cerber3 extension so that users can no longer open them. Once the computer is infected, Cerber 3 creates the #HELP DECRYPT link, inviting you to pay the ransom.
The bad news is that it’s impossible to completely recover the files affected by the Cerber3 ransomware. There are only two solutions available:
- pay the ransom, which only encourages the attackers to continue and helps them reach their goal; this solution should be avoided at all costs
- use dedicated recovery software to try to restore the infected files, although this may not always work.
Taking into account the severity of these malware attacks, prevention is truly better than cure: don’t open suspicious emails and don’t click on suspicious links. In the unfortunate case your computer gets infected, immediately report this to the law enforcement agency in your country.
RELATED STORIES YOU NEED TO CHECK OUT: