Netgear working on stable fix for a security hole in its routers
2 min. read
Published on
Read our disclosure page to find out how can you help Windows Report sustain the editorial team Read more

Several Netgear routers were exposed to a critical security vulnerability last week, potentially allowing hackers to take control of those devices. The flaw enables code injection tactics by hackers with which they can gain root privileges into Netgear routers.
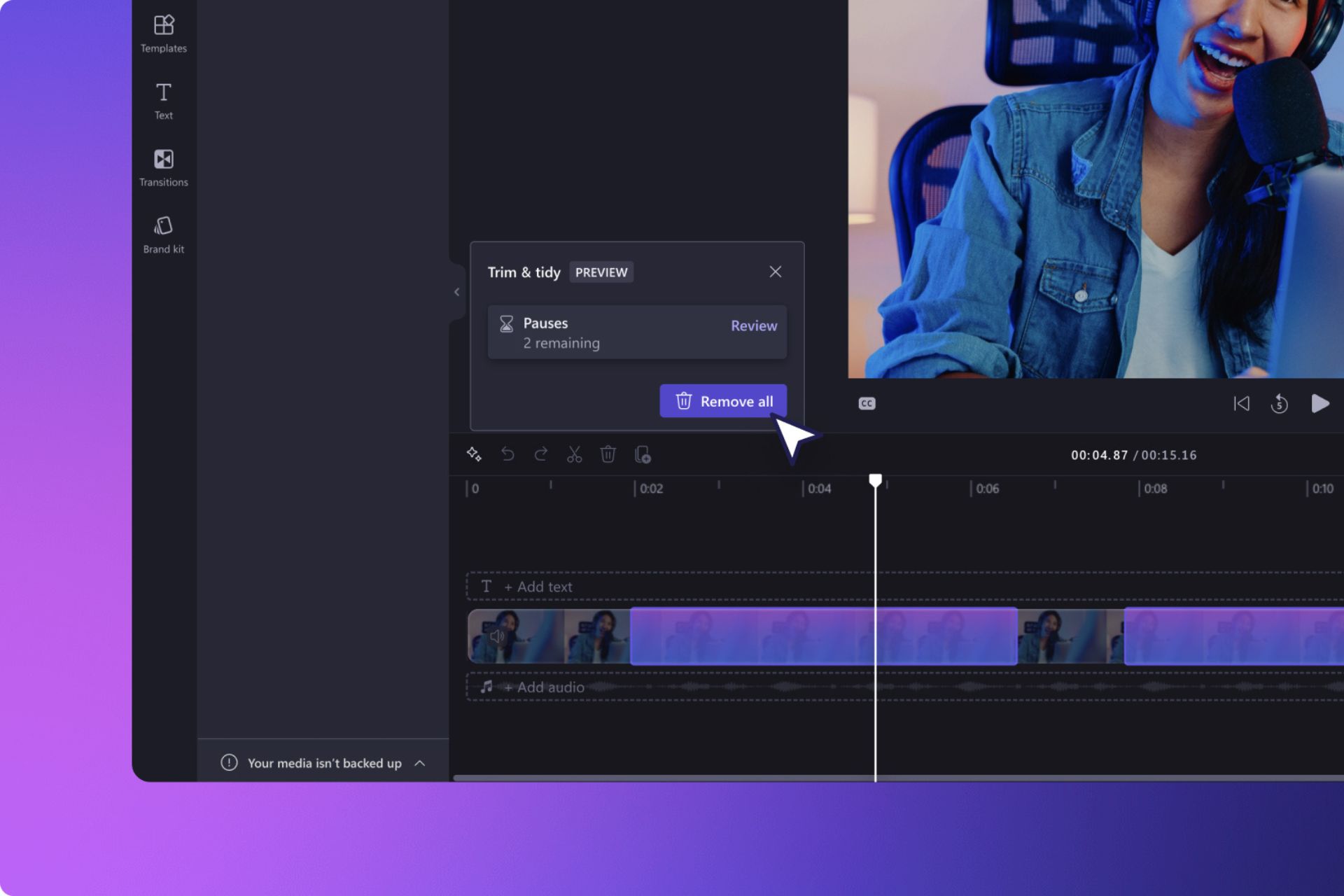
Netgear released a beta firmware to temporarily plug the security hole, but also admitted that it hadn’t tested the fix yet. Now, the company says that it is working on production firmware to patch the security flaw.
Netgear explains that the production firmware will fix the command injection vulnerability, which lets web pages transmit form input to the command-line interface even without authentication. The company says that it will roll out the production firmware once available.
The company said in a blog post:
While we are working on the production version of the firmware, we are providing a beta version of this firmware release. This beta firmware has not been fully tested and might not work for all users. Netgear is offering this beta firmware release as a temporary solution, but Netgear strongly recommends that all users download the production version of the firmware release as soon as it is available.
The following products now have beta firmware fix available:
- R6250
- R6400
- R6700
- R6900
- R7000
- R7100LG
- R7300DST
- R7900
- R8000
- D6220
- D6400
Netgear is still reviewing the extent of the vulnerability to develop fixes for other router models exposed. The company added:
If any other routers are affected by the same security vulnerability, we plan to release firmware to fix those as well…Netgear constantly monitors for both known and unknown threats. Being pro-active rather than re-active to emerging security issues is fundamental for product support at Netgear.
The beta fix offers a better alternative to US CERT’s advisory that recommends turning off affected routers.
While Netgear works on the production firmware, users can check out Netgear’s beta firmware to protect their routers from attackers. The temporary patch is now available to download. If you’ve been affected by the flaw and used the beta firmware, let us know in the comments if it worked.