Windows 7 KB4284826, KB4284867 enhance Spectre protection
2 min. read
Updated on
Read our disclosure page to find out how can you help Windows Report sustain the editorial team Read more
Windows 7 received two new updates on June Patch Tuesday: KB4284826 and KB4284867. Both these security updates focus on improving computer protection against Spectre malware attacks.
Here are the official patch notes:
- Provides support to control use of Indirect Branch Prediction Barrier (IBPB) on some AMD processors (CPUs) for mitigating CVE-2017-5715, Spectre Variant 2 when switching from user context to kernel context. (See AMD Architecture Guidelines for Indirect Branch Control and AMD Security Updates for more details). For Windows client (IT pro) guidance, follow the instructions in KB4073119. For Windows Server guidance, follow the instructions in KB4072698. Use these guidance documents to enable use of IBPB on some AMD processors (CPUs) for mitigating Spectre Variant 2 when switching from user context to kernel context.
- Provides protections from an additional subclass of speculative execution side channel vulnerability known as Speculative Store Bypass (CVE-2018-3639). These protections aren’t enabled by default. For Windows client (IT pro) guidance, follow the instructions in KB4073119. For Windows Server guidance, follow the instructions in KB4072698. Use this guidance document to enable mitigations for Speculative Store Bypass (CVE-2018-3639) in addition to the mitigations that have already been released for Spectre Variant 2 (CVE-2017-5715) and Meltdown (CVE-2017-5754).
It seems that the Spectre curse is haunting Microsoft event to this day. First revealed at the beginning of this year, this threat allows hackers to access valuable information stored on your computer, including: personally identifiable information, private banking information, usernames, passwords and similar critical information.
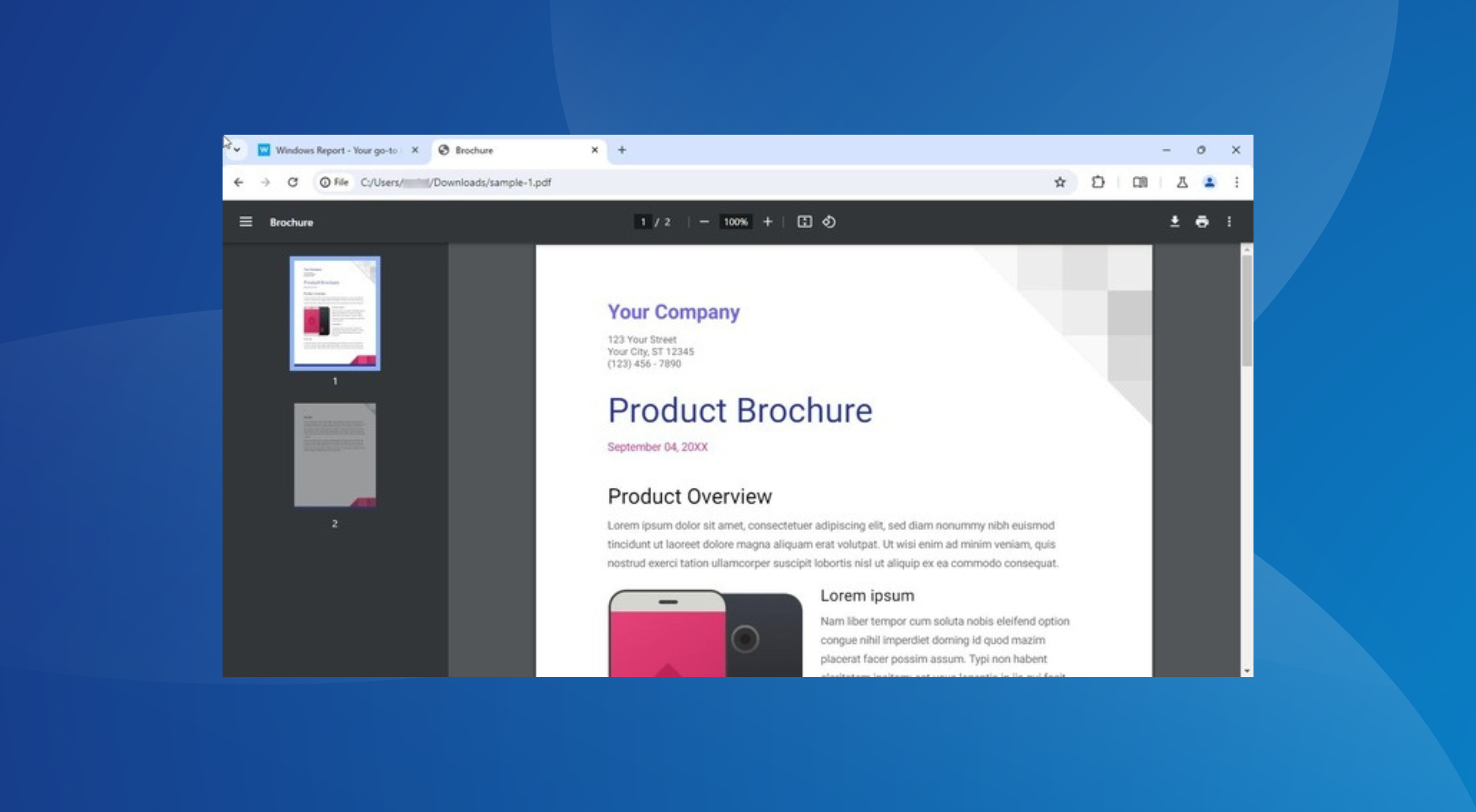
Spectre is extremely dangerous as hackers can launch it from your browser using a specially crafted script. So, if you want to keep your computer protected, check for updates and install the latest patches on your machine.
For more information about the newest Windows 7 updates, go to Microsoft’s support pages:
RELATED STORIES TO CHECK OUT: