KB5004237 addresses Primary Refresh Tokens vulnerability
2 min. read
Published on
Read our disclosure page to find out how can you help Windows Report sustain the editorial team Read more
Key notes
- Microsoft takes security seriously and is now hard at work filling gaps in the security section.
- KB5004237 was issued to address a major security vulnerability that had the tech company's employees on edge.
- This issue was centered around the weak inscription of Primary Refresh Tokens, and the implications this could have.
- This means that an administrator with access to a vulnerable system can extract and potentially decrypt the token for reuse until the token expires or is renewed.

We all know that lately, the Redmond-based tech giant has been struggling with some vulnerabilities that other, not that friendly, third-parties were exploiting in the wild.
The most recent and popular one is the Print Nightmare vulnerability, which Microsoft already patched up, but of course, there are others as well.
With the release of this Patch Tuesday, the tech company also addressed another important security vulnerability that relates to Microsoft’s Azure.
Primary Refresh Tokens weren’t properly encrypted
Before we get into it, remember that this issue is only related to the 2004 version of the Windows 10 OS.
Just to refresh your memory on what Primary Refresh Tokens (PRT) are, they represent a key artifact of Azure AD authentication on Windows 10, Windows Server 2016, and later versions, iOS, and Android devices.
It is a JSON Web Token (JWT) specially issued to Microsoft first-party token brokers to enable single sign-on (SSO) across the applications used on those devices.
Microsoft just issued KB5004237, as a part of the July 2021 Patch Tuesday, which specifies that a vulnerability in which these tokes and not strongly encrypted is being addressed.
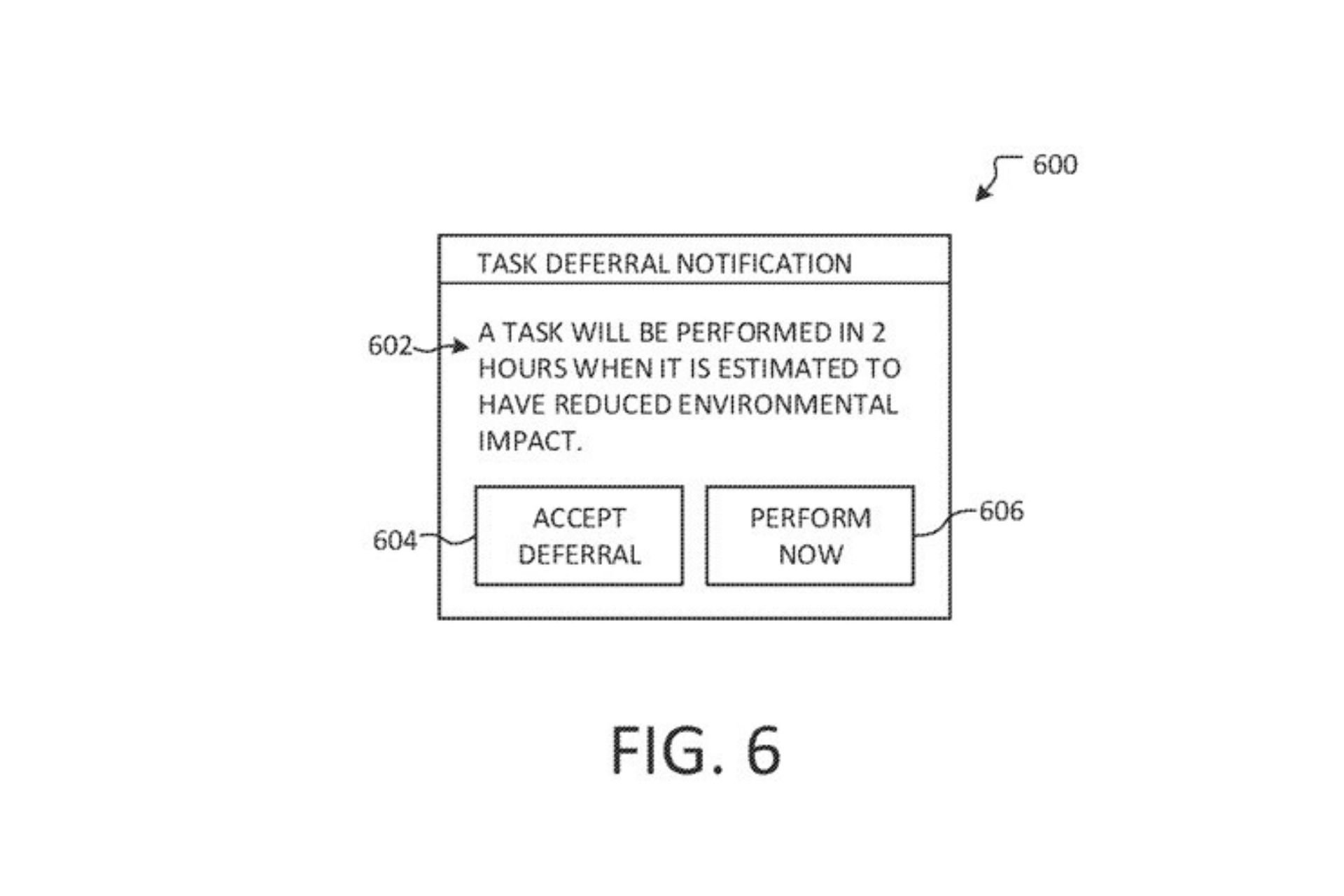
This vulnerability relates to Primary Refresh Tokens which are usually stored in the TPM security chips, which as you remember, are a mandatory requirement for running the upcoming OS, Windows 11.
These tokens are usually used for SSO for Azure AD accounts and are not encrypted in a strong enough manner, which means that an administrator with access to a vulnerable system could extract and potentially decrypt the token for reuse until the token expires or is renewed.
A great and somewhat expected initiative from Microsoft, considering the damage such exploitation could cause for millions of users if the information simply fell into the wrong hands.
It’s good to know that, even though they are still hard at work perfecting flagship apps and designing new operating systems, the Redmond tech giant still finds the time to fill important security gaps.
After all, security is the biggest concern right now, in this evergrowing online world, after so many cyber-attacks that were conducted these past months.
Were you aware of this exploitation? If so, are you aware of other security threats that Microsoft users are facing? Let us know in the comments section below.