Ransoc is a bold ransomware that threatens legal action if you don't pay
2 min. read
Published on
Read our disclosure page to find out how can you help Windows Report sustain the editorial team Read more
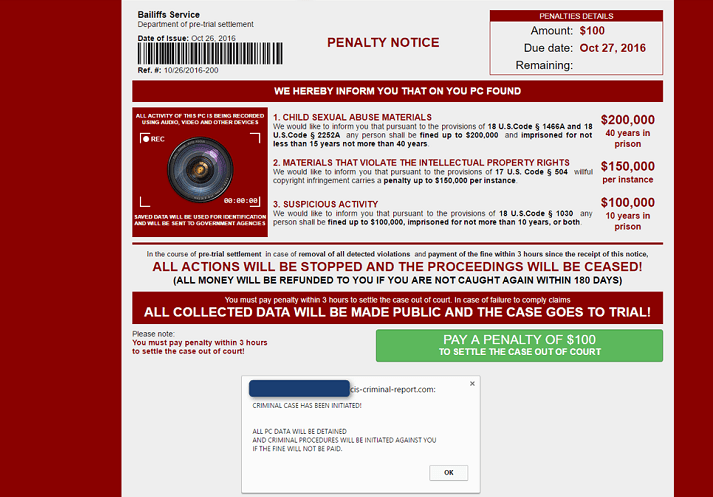
Security researchers have recently detected a new vicious, bold ransomware named “Ransoc“. This malicious program sneaks into your computer, searches for illegally downloaded content, takes a look at your social media accounts and then threatens to make your disreputable content public if you don’t pay the ransom.
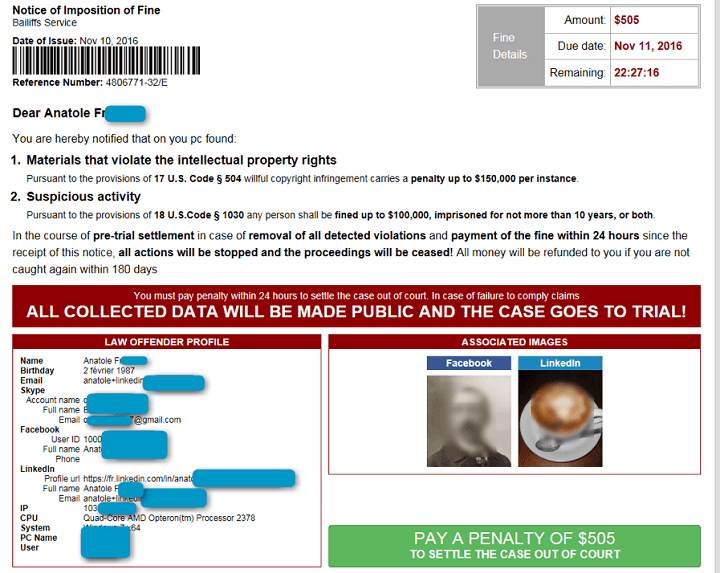
If you’ve saved materials that violate intellectual property rights, sexual abuse materials or other suspicious content, Ransoc offers you the possibility to settle the case out of court.
Ransoc is definitely not your regular ransomware. Instead of encrypting your files, the malware searches for illegally downloaded content and stores personal information found on your social media accounts. The ransom note includes images from social media accounts together with a legal action thread.
The ransomware threatens to expose the so-called evidence to the public and the fact that it displays actual social media information helps it lure its victims to pay the money. We must admit that targeting reputation rather than the files themselves is a very smart move. Moreover, to encourage payment, the ransom note promises that money will be sent back if the victims “stay clean” in the next 180 days.
According to security researchers, this ransomware is spread via malvertising traffic primarily fed by the Plugrush and Traffic Shop traffic exchanges on adult websites and its favorite target is Internet Explorer. If you’re running old, unsupported versions of Internet Explorer, you need to upgrade your browser version as soon as possible.
In a sandbox environment, we observed this new malware perform an IP check and send all of its traffic through the Tor network. Further examination revealed that the malware scanned local media filenames for strings associated with child pornography.We also noticed that it was running several routines interacting with Skype, LinkedIn, and Facebook profiles. […] It appears that this penalty notice only appears if the malware finds potential evidence of child pornography or media files downloaded via Torrents and customizes the penalty notice based on what it finds.
The good news is that Ransoc uses a registry autorun key. This means that rebooting in Safe Mode should allow users to remove the malware. As always, prevention is better than a cure and we recommend you install one of the following anti-hacking tools on your computer.
RELATED STORIES YOU NEED TO CHECK OUT: