New Hyper-V integration in WSL 2 leads to traffic leaking
2 min. read
Published on
Read our disclosure page to find out how can you help Windows Report sustain the editorial team Read more
Key notes
- The possibility of leaking Internet traffic when running Linux under WSL 2 is not encouraging.
- The WS for Linux 2 uses Hyper-V virtual networking, which is the root of the problem this time.
- Check out this Security & Privacy Software section for useful tricks on how to protect your data.
- Don’t hesitate to bookmark our News Hub if you want to easily keep an eye on the latest stories.
The Windows Subsystem for Linux 2 may not be as secure as claimed. Traffic from the Linux guest bypasses all normal layers of the Windows 10 firewall and any configured rules.
The next step is directly out onto the network. In these conditions, no security blocking in the firewall is taken into consideration.
More precisely, this prevents even the Always require VPN security feature from working as it should, which raises concerns among users thinking of Internet traffic leaks.
However, others are aware of what WSL 2 means and aren’t that worried. Here’s what one user said:
WSL 2 is another OS, running with Windows, not on top of it. It’s a level 1 hypervisor. It isn’t subject to the same network restrictions as Windows.
How does the WSL 2 leak take place?
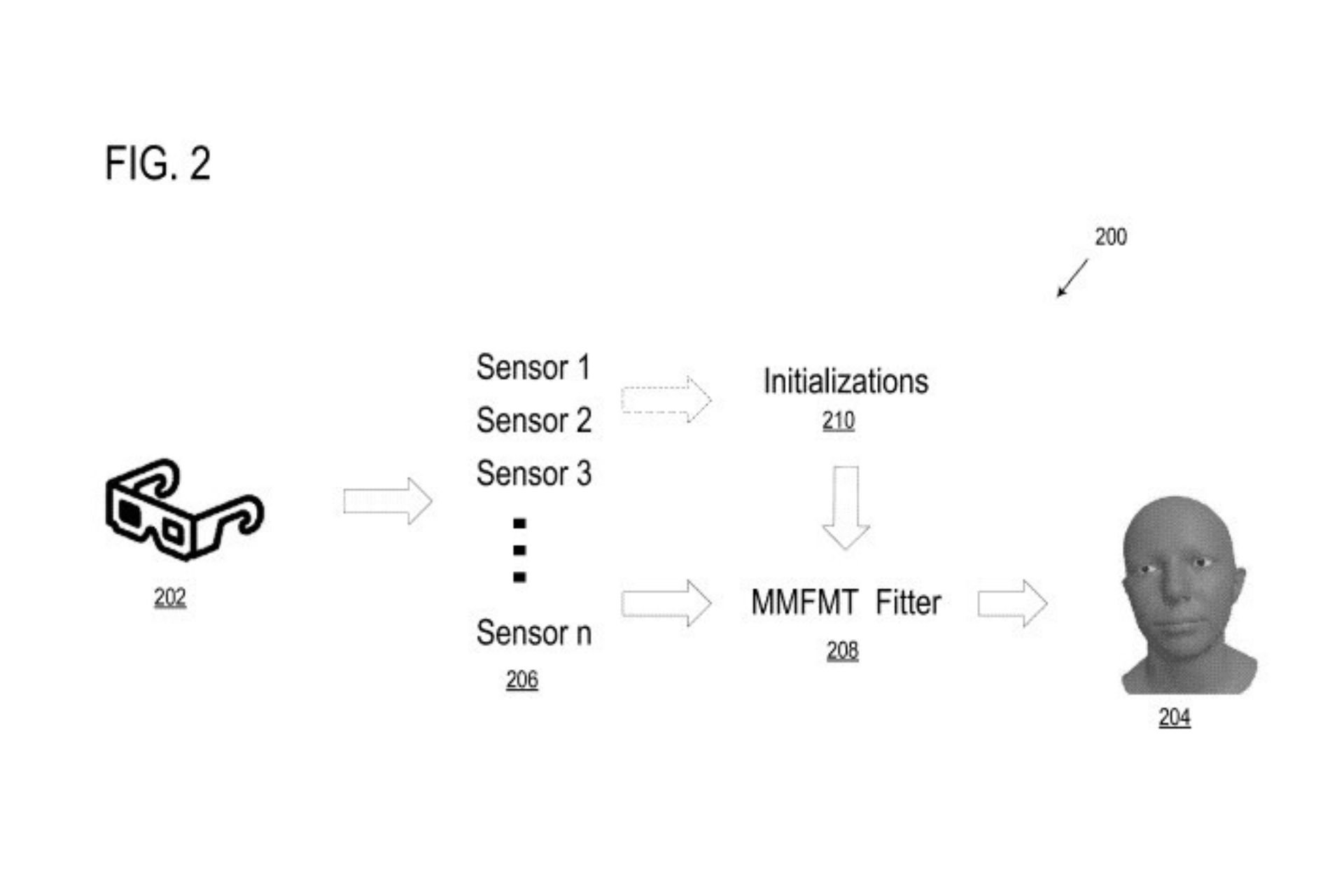
Unlike the first version of the Windows Subsystem for Linux (WSL 1), WSL 2 uses Hyper-V virtual networking. That’s the root of the issue under discussion.
WSL 1 is based on a Linux-compatible kernel. Fortunately, this one translates Linux system into calls that are perfectly compatible with the Windows NT kernel.
Therefore, any network traffic is filtered through the Windows Advanced Firewall. However, WSL 2 functions on a true Linux kernel operating in a Hyper-V virtual machine.
This involves a Hyper-V virtual network adapter and all traffic is going out the default route of the host machine. This happens without being inspected by the usual layers of WFP.
This turns into an issue since WSL 2 distributions can support multiple Linux applications, including server implementations.
That’s why it isn’t necessarily unusual to be considered an independent operating system that cannot rely on the Windows Firewall.
However, users should become aware of the fact that configured Windows Firewall rules are ignored under these circumstances.
Until waiting for an official response from Microsoft, do you keep on using the rather powerful WSL 2 over the more secure WSL 1? Let us know in the comments area below.
[wl_navigator]