Zero-day exploit in Windows Event Log allows hackers to remain hidden
The exploit can't be performed remotely and it can't run any code
2 min. read
Published on
Read our disclosure page to find out how can you help Windows Report sustain the editorial team Read more

A new vulnerability has been found in Windows Event Log that allows hackers to crash the Windows Event Log service on all supported versions of Windows.
So how does this exploit work and how dangerous it is? Keep on reading to find out!
A new Event Log exploit has surfaced, and it covers hackers’ tracks
This exploit was first found by a Twitter user Florian while working on a fuzzer.
According to Florian, he tested this exploit in a network that consists of Windows 10 and Windows Server 2022 domain controller.
He states that he was able to crash the Event Log service on the domain controller from his Windows 10 machine. And this didn’t even require administrative privileges, meaning anybody can do it.
Acros Security tested this exploit, and it was confirmed that it’s present on Windows 11 as well. To make matters worse, it only takes a second for the attacker to perform this exploit.
After crashing the Windows Event Log service three times, it won’t restart anymore, and if the hacker manages to crash the system, Security and System events won’t be stored.
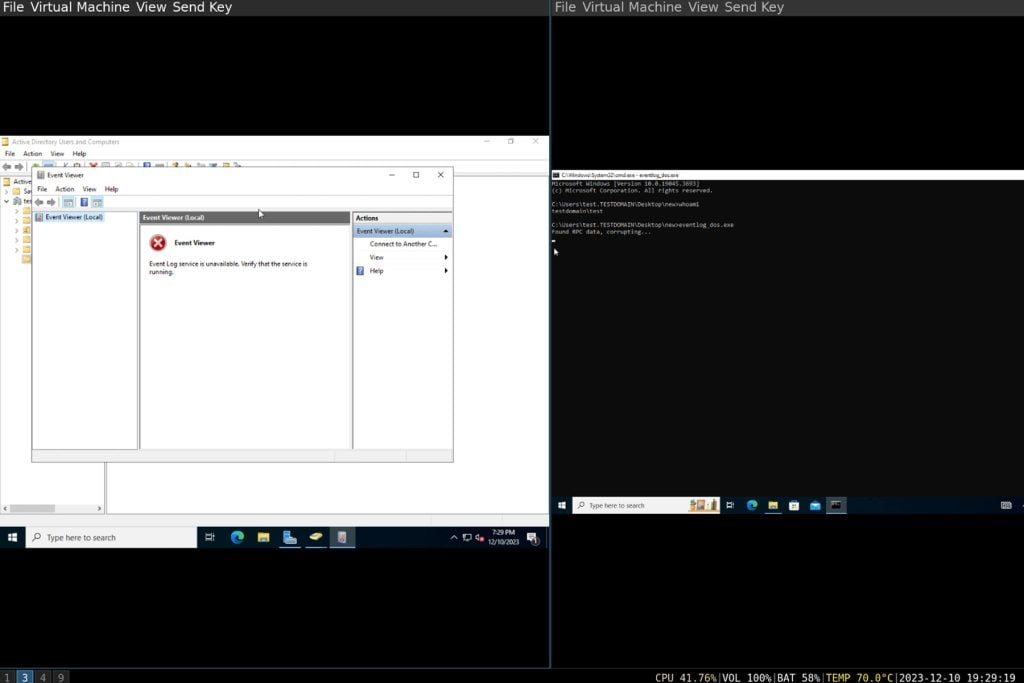
While this exploit doesn’t allow the hackers to run any code or gain administrative privileges, it prevents the gathering of logs making any malicious activity hidden from administrators.
While this looks scary, there is some good news. This exploit doesn’t work remotely, and it can only be used in a local network.
Microsoft hasn’t addressed this issue, however, a micro patch from Acros is available, so concerned administrators can install it.
Microsoft is quick to address security problems, and they did the same with a recent Azure Pipelines security issue and CVE-2024-0519 vulnerability in Edge, so we expect an official patch to be released soon.