CoralRaider abuses a CDN cache to spread information-stealing malware
Researchers at Cisco Talos exposed them
3 min. read
Published on
Read our disclosure page to find out how can you help Windows Report sustain the editorial team Read more

Researchers have found a new threat actor who is using a content delivery network (CDN) cache to spread information-stealing malware as part of an ongoing campaign targeting systems in the UK, Germany, the US, and Japan.
According to Cisco Talos, CoralRaider is identified as the threat actor behind it based on similarities in techniques, tactics, and procedures with past attacks. It focuses on stealing credentials, social media accounts, and financial data.
The hackers distribute Cryptbot, Rhadamanthys, and LummaC2 info stealers that are accessible from underground forums from malware-as-a-service platforms for a subscription fee.
How does the attack happen?
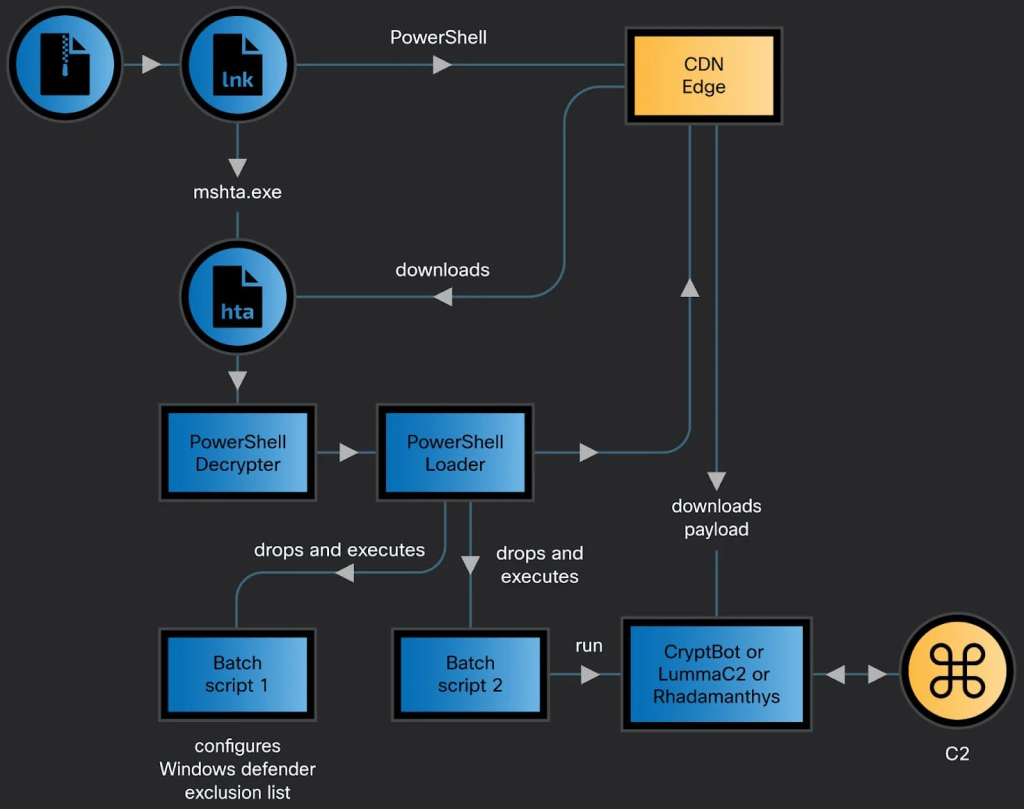
The attack chain starts with victims opening an archive consisting of a malicious Windows shortcut file (.LNK). Meanwhile, the delivery method of the archive is not clear, but it could be easily sent through emails, malvertising, or downloads from untrusted sources.
Once executed, the .LNK file sets off the PowerShell commands, which in turn download and execute a heavily obfuscated HTML Application (HTA) file from an attacker-controlled subdomain on the Bynny CDN platform
By using the CDN cache for malware delivery, the threat actor focuses on bypassing network defense and preventing request delays.
The HTA file comprises JavaScript that decodes and runs the PowerShell decrypter script, which then unpacks the second script, which writes a batch script in a temp folder to make changes to the Windows Defender exclusions.
Furthermore, the FoDHelper.exe LoLBin is used to modify registry keys and circumvent User Access Control (UAC) security features.
After this, the PowerShell script downloads and runs one of three information stealers: Cryptbot, LummaC2, or Rhadamanthy, which are already added in locations excluded from Defender’s scanning.
CoralRaider usually uses the latest versions of Rhadamanthys and LummaC2, which are popular because of their advanced features, like reviving expired Google account cookies and capturing RDP logins.
However, in some recent attacks, the latest variant of Cryptbot, released in January, was used. It has enhanced obfuscation, anti-analysis mechanisms, and an expanded list of targeted apps.
Cisco Talos also mentioned that Cryptbot aims at databases for password managers and authenticator app data, with the notion of stealing cryptocurrency wallets protected with two-factor authentication.
CoralRaider has been active since 2023, and according to researchers, it is based in Vietnam. Its primary victims are from Asian and Southeast Asian countries. However, its operations have expanded and victimized users in other regions, including the US, Pakistan, Nigeria, and more.
The researchers have tried to track and reduce CoralRaider’s activities. The threat actor has been evolving its tactics and expanding its reach, but it still poses a significant threat to individuals and companies globally.
What are your thoughts on the matter? Share your opinions with our readers in the comments section below.