Hackers used the Phorpiex botnet to spread the LockBit Black ransomware
Threat actors delivered over a million phishing emails
3 min. read
Published on
Read our disclosure page to find out how can you help Windows Report sustain the editorial team Read more

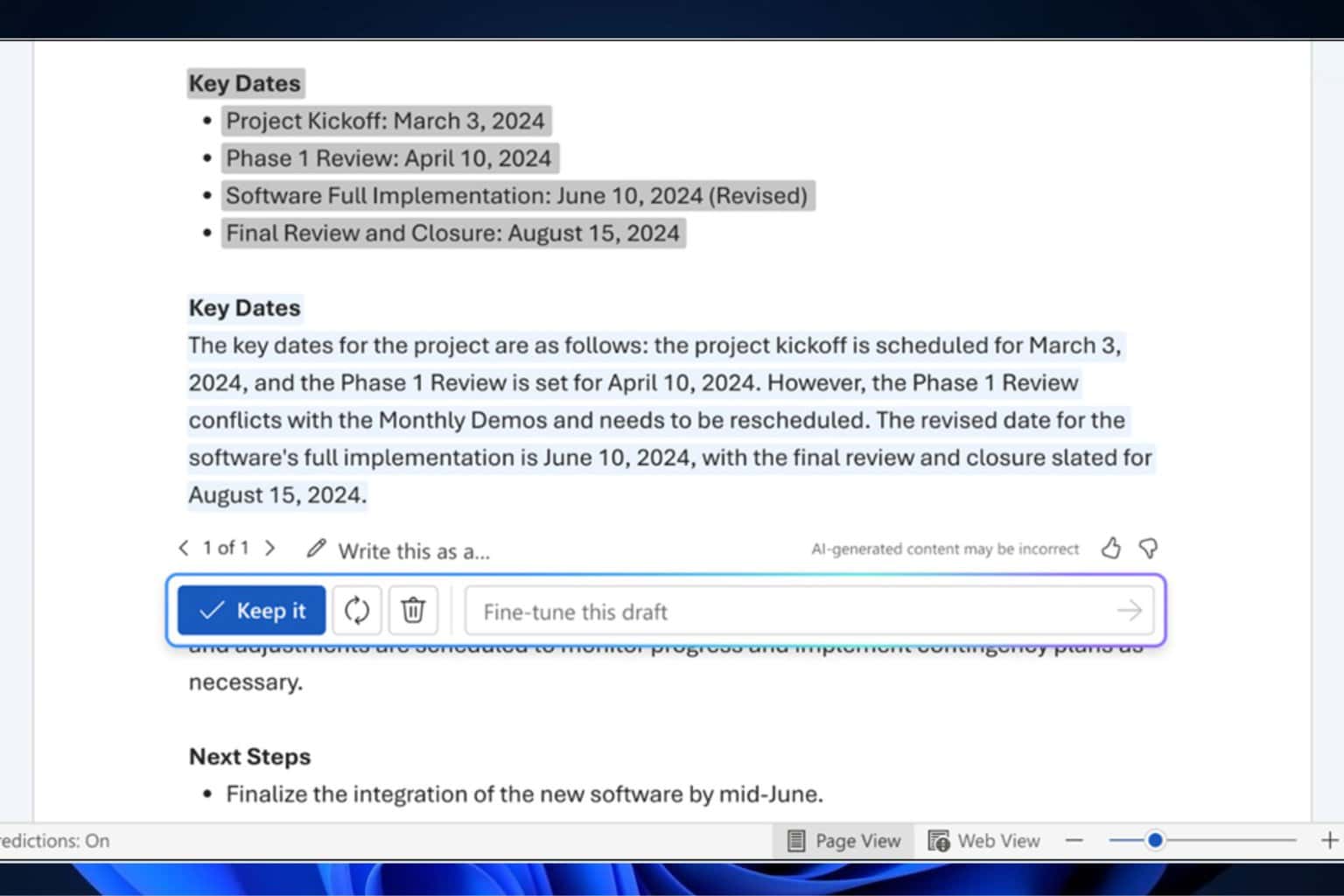
Threat actors sent millions of phishing emails through the Phorpiex botnet since April. Their goal was to conduct a LockBit Black ransomware campaign. According to New Jersey’s Cybersecurity and Communications Integration Cell (NJCCIC), the wrongdoers used ZIP files containing the LockBit Black payload. The ransomware can encrypt your system once you launch it.
In addition, according to Bleeping Computer, attackers built the malware using the LockBit 3.0 builder, which surfaced on Twitter in September 2022.
The phishing emails share some characteristics. For example, they use the same aliases, Jenny Green or Jenny Brown. Additionally, the message usually states that a document or a photo from the ZIP attachment belongs to you. Also, the hackers send emails from 1.500 IP addresses worldwide, including Kazakhstan, Uzbekistan, Iran, Russia, and China.
How does the LockBit Black ransomware campaign work?
The threat actors sent the emails containing a ZIP doc through the Phorpiex botnet. Afterward, when someone opens the document, it starts running the malware inside. Then, the virus installs LockBit Black ransomware from the Phorphiex botnet. When the installation finishes, the malicious program tries to encrypt files, steal data, and terminate services.
The approach used by hackers is not new. However, the LockBit Black ransomware campaign is efficient due to the high number of sent emails. Yet, compared to other cyberattacks, this one lacks complexity.
According to the cybersecurity experts from Proofpoint, cybercriminals target companies across various industry verticals worldwide. Also, they begin their operations on April 24, 2024.
What is the Phorpiex botnet?
The Phorpiex botnet is an IRC-controlled trojan. It used to spread through USB drives, Skype, and Windows Live Messenger. On top of that, it has been active for over a decade. In addition, cybercriminals used it for more operations besides the LockBit Black ransomware campaign.
The virus gained control over millions of devices. So, its developers tried to sell it on a hijacking forum after they shut down the Phorpiex infrastructure. In addition, wrongdoers used it to spam over 30,000 sextortion emails per hour and delivered over a million emails.
Recently, cybercriminals used a clipboard hijacker module with malware. This method allowed them to replace the cryptocurrency wallet addresses copied to the Windows clipboard of their victims with other ones controlled by them. After a year, they hijacked 969 transactions and stole 3.64 Bitcoin ($172,300), 55.87 Ether ($216,000), and $55,000 worth of ERC20 tokens.
Ultimately, to protect your device from the LockBit Black ransomware and Phorpiex malware, use endpoint security solutions, email filtering tools, or features, and implement ransomware mitigation strategies. In addition, do not open any ZIP files from shady emails, and double-check the sender.
Do you have some ransomware mitigation strategies? Let us know in the comments.