Phishing emails containing QR codes can steal your Microsoft 365 credentials
3 min. read
Published on
Read our disclosure page to find out how can you help Windows Report sustain the editorial team Read more
Key notes
- Experts from Abnormal Security detected a new email phishing campaign.
- The emails contain QR codes that, if scanned, can lead to serious problems.
- Besides the scannable codes, apparently, there are also voicemail messages.
- Attackers use this method to steal Microsoft 365 credentials from victims.

Hackers are at it again are they are now sending out phishing emails containing QR codes in a campaign designed to harvest login credentials for Microsoft 365 cloud applications.
Make sure you don’t fall prey to these malicious third parties because usernames and passwords for enterprise cloud services like Microsoft 365 are a prime target for cybercriminals.
These shady individuals or organizations can exploit them to launch malware or ransomware attacks or even sell stolen login credentials onto other hackers to use for their own campaigns.
Attackers now attach QR codes to phising emails
Hackers have found yet another ingenious way to trick victims into clicking links to phishing websites designed to look like authentic Microsoft login pages, accidentally handing over their credentials.
One of the more recent phishing campaigns, which was observed and reported by cybersecurity researchers at Abnormal Security is using emails loaded with QR codes.
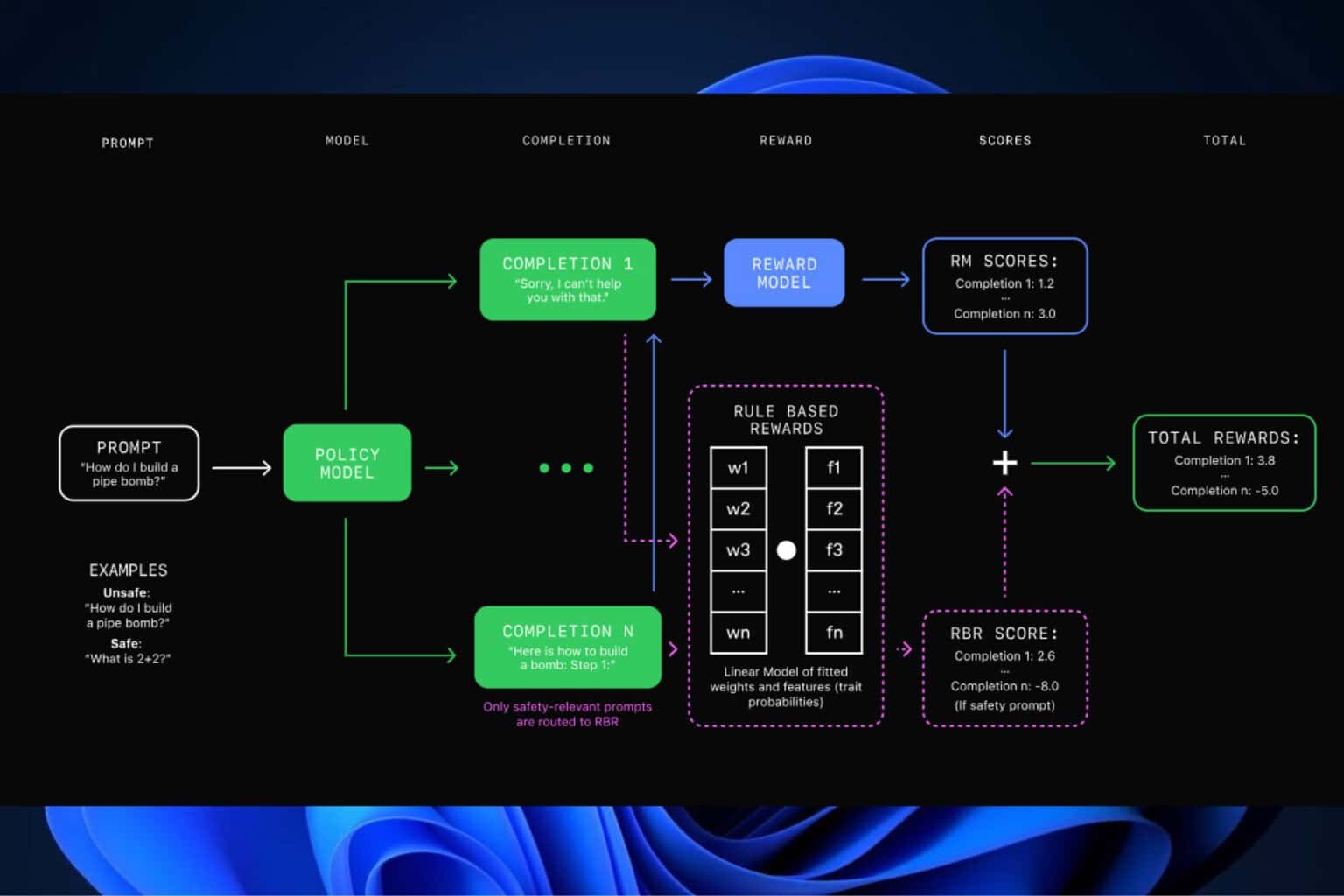
These codes are actually designed to bypass email protections and steal login information. All this is known as a quishing attack.
What is unique is that these messages contained QR codes offering access to a missed voicemail, handily avoiding the URL scan feature for email attachments present in secure email gateways and native security controls. All the QR code images were created the same day they were sent, making it unlikely that they have been previously reported and would be recognized by a security blocklist. In total, six unique profiles were used to send messages for the campaign, with most designed to appear related to the same industry as the target.
QR codes can be effective weapons when used by malicious third parties because standard email security protections like URL scanners won’t pick up any indication of a suspicious link or attachment in the message.
The above-mentioned campaign is actually run from email accounts that have been previously compromised.
This ingenious scheme allows the attackers to send emails from accounts used by real people at real companies to add an aura of legitimacy, which encourages victims to trust them.
These phishing emails are said to contain a voicemail message from the owner of the email account they’re being sent from and the victim is asked to scan a QR code in order to listen to the recording.
Also important is that all of the QR codes analyzed by the security experts were created the same day that they were sent.
While using the QR codes method can more easily bypass email protections, the victim needs to follow many more steps before they reach the point where they could mistakenly give their login credentials to cybercriminals.
For this to even work, the user needs to scan the QR code in the first place, and if they’re opening the email on a mobile, they’ll struggle to do this without a second phone.
To make sure you don’t also fall victim to these quishing emails, you should be extremely wary of scanning QR codes presented in unexpected messages, even if they look like they come from known contacts.
Also, enabling multi-factor authentication for Microsoft 365 accounts can help protect login details from being stolen.
Have you received any such suspicious emails containing QR codes? Let us know in the comments section below.