Download August 2016 Patch Tuesday with nine security updates
2 min. read
Published on
Read our disclosure page to find out how can you help Windows Report sustain the editorial team Read more
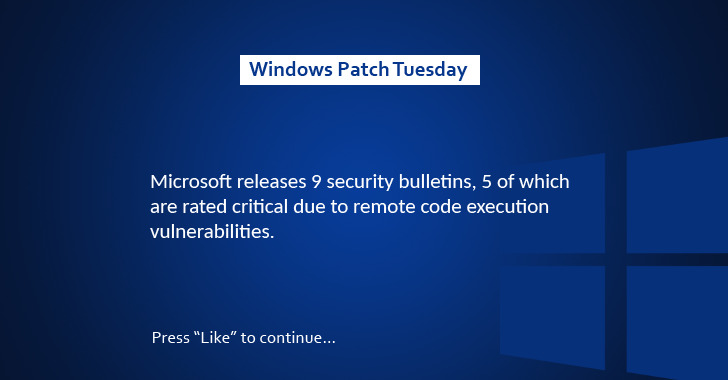
This month’s Patch Tuesday includes nine security bulletins, with five of them rated critical. We see a smaller number of patches because, according to Michael Gray, Vice President of Technology at Thrive Networks, “Microsoft may have kept things simple so as not to over-shadow the release of their Windows 10 Anniversary update.”
Critical
Two of the cumulative monthly fixes are for Internet Explorer (MS16-095) and Microsoft Edge (MS16-096). The first one resolves five memory corruption vulnerabilities and four information disclosure flaws, while the former fixes eight bugs (four memory corruption flaws, three information disclosure holes, and one Microsoft PDF RCE vulnerability).
The third critical fix is MS16-097 and is a security update that addresses RCE vulnerabilities in Microsoft graphics component. MS16-099 fixes three Office memory corruption vulnerabilities, one Microsoft OneNote information disclosure bug, and one graphics component memory corruption vulnerability. Finally, MS16-102 fixes one RCE flaw in Microsoft Windows PDF library and Core Security principal software engineer Jon Rudolph has explained that it’s important to keep an eye out for CVE-2016-3319 aka “Microsoft PDF Remote Code Execution Vulnerability.
Important
According to the change log, MS16-098 fixes four elevation of privilege vulnerabilities in Windows kernel-mode drivers; MS16-100 gets rid of a security feature bypass bug in Windows Secure Boot which would allow attackers to disable code integrity checks and to load test-signed executables and drivers into a target device. The third patch, MS16-101, fixes two elevation of privilege vulnerabilities: a Kerberos EoP flaw and a Netlogon EoP bug.
As for MS16-103, this patch addresses an information disclosure flaw in ActiveSyncProvider for Windows 10 and Windows 10 Version 1511. Microsoft stated that “The vulnerability could allow information disclosure when Universal Outlook fails to establish a secure connection,” adding that “The update addresses the vulnerability by preventing Universal Outlook from disclosing usernames and passwords.”
RELATED STORIES TO CHECK OUT: