Warning! Nasty new Office 365 phishing attack doing the rounds

A new and very nasty phishing attack has been doing the rounds, and it is extremely difficult to spot. Here is what you need to look out for.
First of all, we should thank Xavier Mertens for being the first to spot it. If you want to see the code that the phishing attack uses, pop over to this website.
How does this attack work?
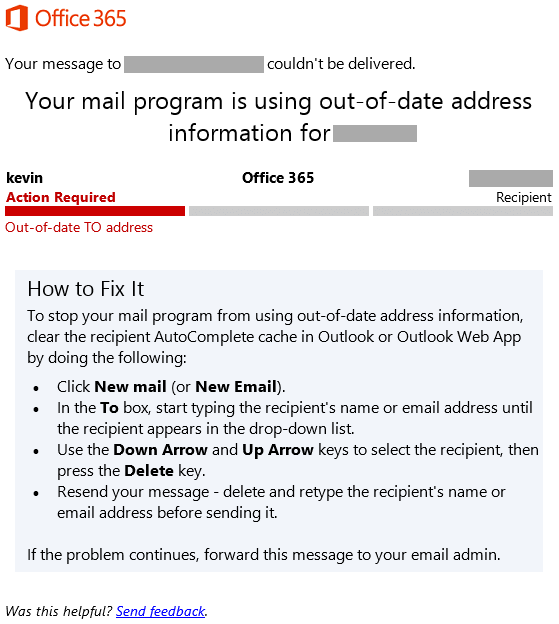
A recipient gets a Non Delivery Receipt (NDR) from what looks like a trusted account. It tells the recipient that “Microsoft found several undelivered messages”.
The next step that the phisherman wants you to do is click the ‘Send Again’ button. This will take you to a page that looks very much like the Office 365 page.
Fake phishing attack login page
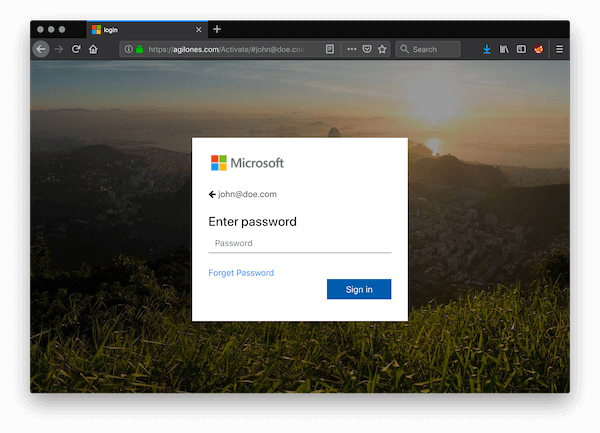
Check out the website address in the image above. It is obviously not the address of Office 365, Microsoft, Windows, or anything remotely linked to Microsoft, and yet I am sure many people entered their login information.
When you do enter your login info, you get sent to Outlook, so it looks very much like you have not been phished. Unfortunately, your Office 365 login details have just been sent to the bad guys, and they now have access to your Office Account and everything that goes with it.
Genuine Non Delivery Receipt
Now, you all know how much I love to rant against Microsoft (in a constructive way, of course), but I really don’t think we can blame Microsoft for this. While the email address for the original phishing attack looks like it is ‘sort of’ official, there is no way that anyone should fall for the login address.
In case you want to be secure while surfing the internet, you will need to get a full-dedicated tool to secure your network. Install now Cyberghost VPN and secure yourself. It protects your PC from attacks while browsing, masks your IP address and blocks all unwanted access.
Guys, always check the web addresses and if you are in any doubt, do NOT login from a link. Go into your browser and type in the address you want in the normal way, and then login. It ain’t rocket surgery, guys, just basic online safety rules.
Have you received this phishing attack. Did you spot it as phishing immediately, or did you have to double check? Or did you fall for it? Don’t worry if you did; I fell for a PayPal phishing scam once. The address was PayPel. In my defence, it was about 10 years ago. Let us know in the comments below.
RELATED ARTICLES YOU SHOULD CHECK OUT:
Read our disclosure page to find out how can you help Windows Report sustain the editorial team. Read more








User forum
0 messages