Petya virus affected only about 20,000 machines, most on Windows 7, says Microsoft
3 min. read
Published on
Read our disclosure page to find out how can you help Windows Report sustain the editorial team Read more

Earlier this week, the Petya ransomware attack pretty much took everyone by surprise, just a month after the previous WannaCry outbreak paralyzed a lot of Windows PCs across the world (most of them were running Windows 7, as it turns out). Compared to the WannaCry ransomware, Petya uses the same SMB exploit and is a bit more sophisticated, but new evidence shows that the outbreak is not as bad as we thought.
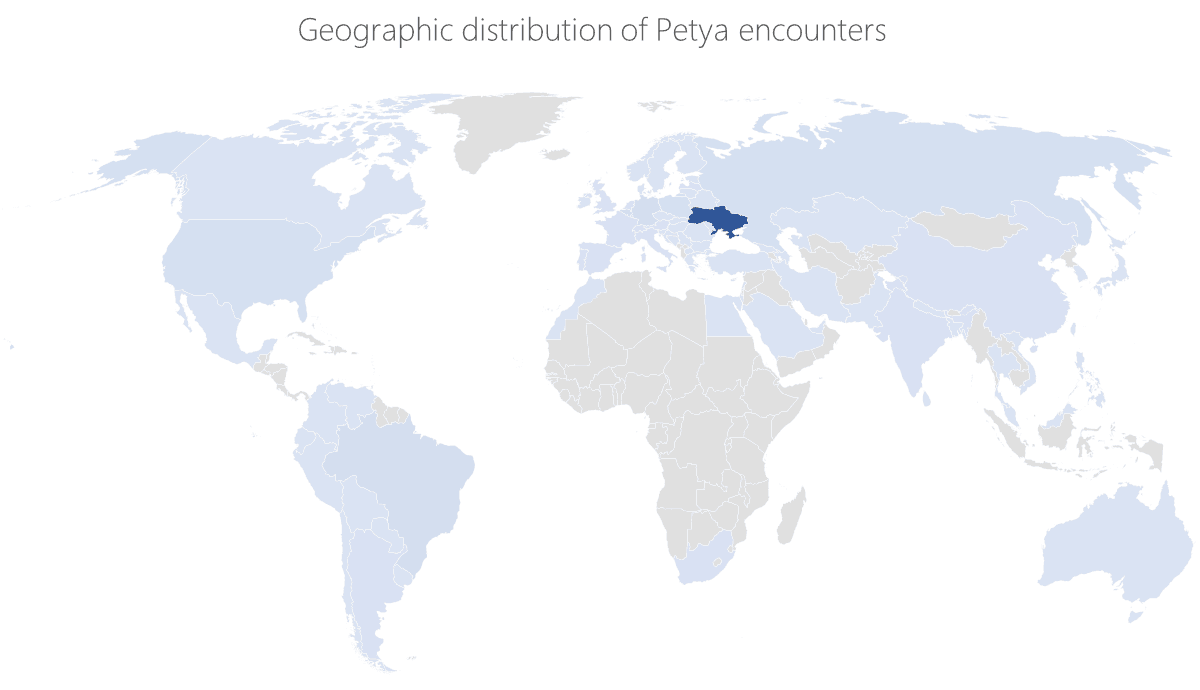
“The new Petya variant is highly sophisticated malware, but our telemetry shows it had far less reach than we expected (less than 20,000 machines), given its worm-like spreading capabilities,” explained Microsoft yesterday on its Windows Security blog. According to the company, the attack started in Ukraine and managed to spread to machines in other countries, but “in significantly lower volumes.” Moreover, the Redmond giant says that “the majority of infections were observed in Windows 7 machines,” even though Microsoft previously issued a series of patches for this type of exploit earlier this year.
Microsoft’s blog post also reveals many interesting details about the new ransomware, including the fact that the impact of Petya’s worm behavior is limited by its design:
- First of all, Petya has a limited execution time to spread to other machines. “As part of its execution command, it receives a time that it can run performing lateral movement and exploitation before rebooting the system,” explains Microsoft.
- In addition, Microsoft found out that the worm code does not run again on an infected machine that is successfully rebooted. “This reduced the reach of the attack, as observed in our telemetry,” explained Microsoft.
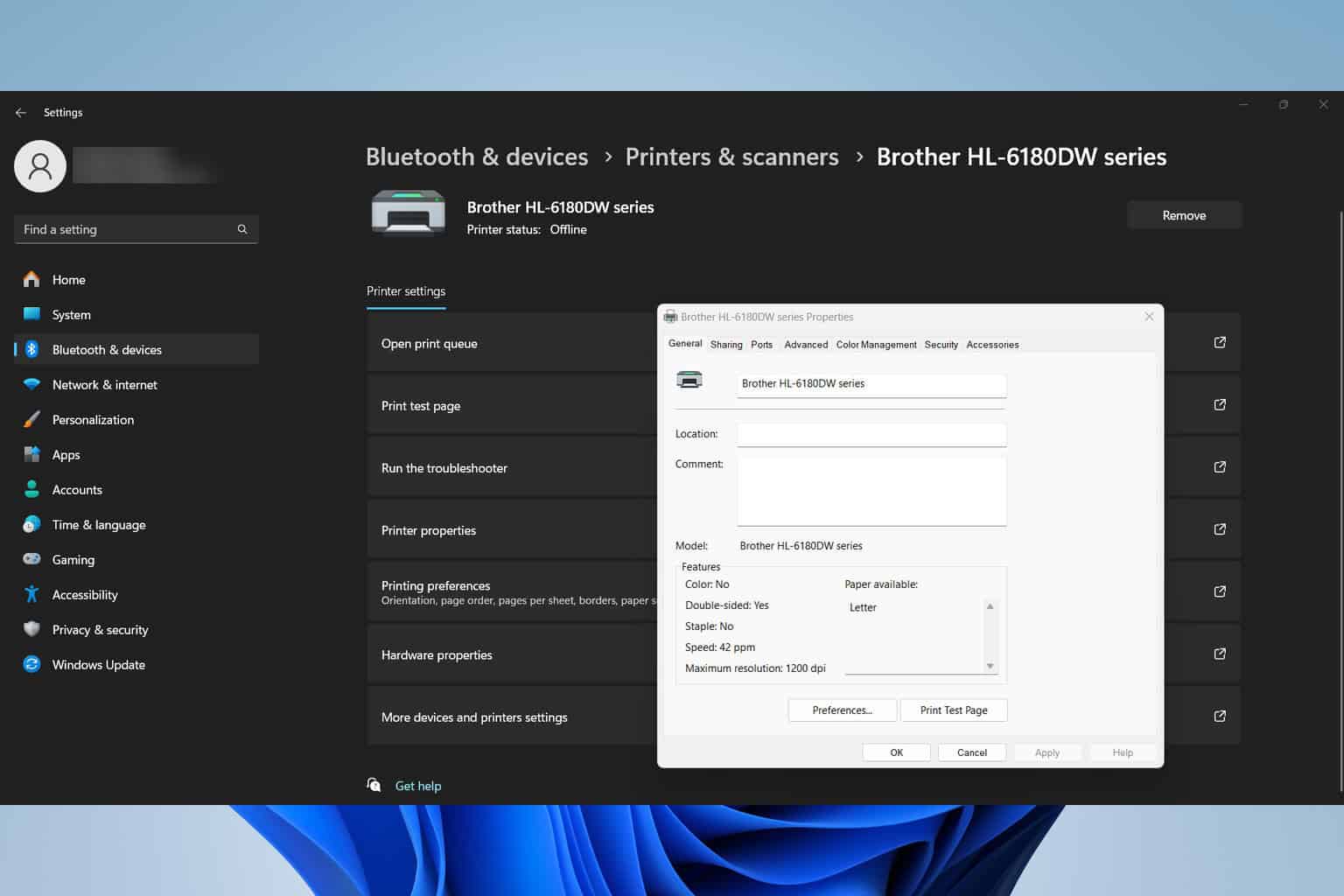
- Last but not least, Petya causes some damage to the operating system’s boot code, though only Windows 7 machines that were upgraded from XP would normally have their boot manager corrupted (on most modern machines, boot manager is now its on own partition, not C:). However, there are still some boot recovery options in certain specific cases, and we invite you to read the full blog post to get all the details.
Overall, Microsoft remains worried about “the ever-increasing sophistication of ransomware attacks,” and the company is urging consumer and businesses to update their PCs to the much more secure Windows 10. “Windows 10 has defenses that can mitigate ransomware attacks like Petya,” explained Microsoft. Earlier this week, the company also announced that next generation security features are coming later this year with the Fall Creators Update, and the timing of the announcement was obviously very appropriate.