How to Set Up VPN MFA to Increase Your Security
How about an extra layer of security for your VPN with MFA?
6 min. read
Updated on
Read our disclosure page to find out how can you help Windows Report sustain the editorial team Read more
Key notes
- In a world where data breaches are becoming more common, businesses need to be extra cautious about their security.
- A VPN can help you protect your business from hackers and other cybercriminals.
- But a VPN alone is not enough. You should also implement multi-factor authentication (MFA) to further secure your devices.
Using a VPN is one of the best ways to increase your security and privacy. However, most VPNs don’t provide any additional security features to keep your account secure. That’s why it’s important to set up multi-factor authentication (MFA) with your VPN provider.
The best way to stay secure is to ensure your VPN has multi-factor authentication. If a hacker gets a hold of your account credentials, they’ll still need an additional code that only you know to log in and access your data.
What is VPN MFA?
VPN MFA is a technology that allows you to use a second-factor authentication (2FA) with your VPN. This means that when you log in to your VPN, a code will be sent to your phone or email. You’ll need to enter the code before logging in.
Why do I need VPN MFA?
One of the main reasons why people use VPNs is to access the internet anonymously. Other reasons include:
- Extra protection – It adds another layer of protection against malicious attacks on your devices and data.
- Privacy – A VPN hides your real IP address, making it harder for third parties to track your online activities.
- Prevent fraud – With a VPN MFA, you can also ensure that the person using your VPN is who they say they are.
Now that you understand how important VPN MFA is, you’ll need the help of third-party tools to complete the process. Below, we look at some of the programs that offer these services.
How do I enable MFA on VPN?
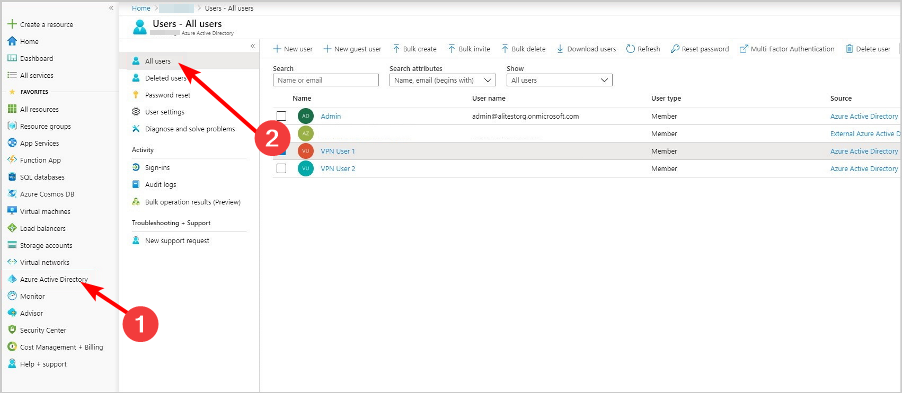
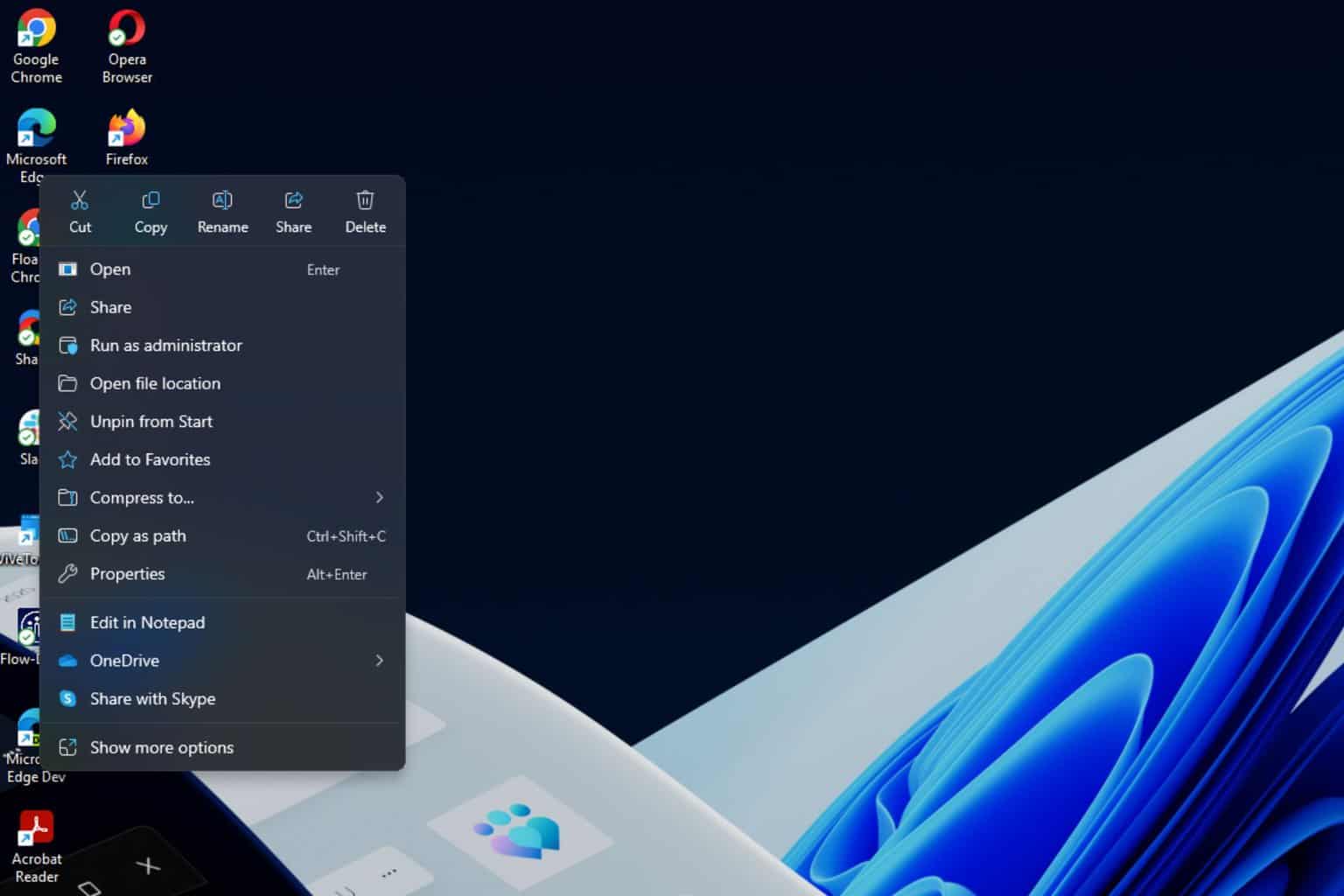
- Sign in to your AD account (In this case Azure portal).
- Navigate to Azure Active Directory and select All users.
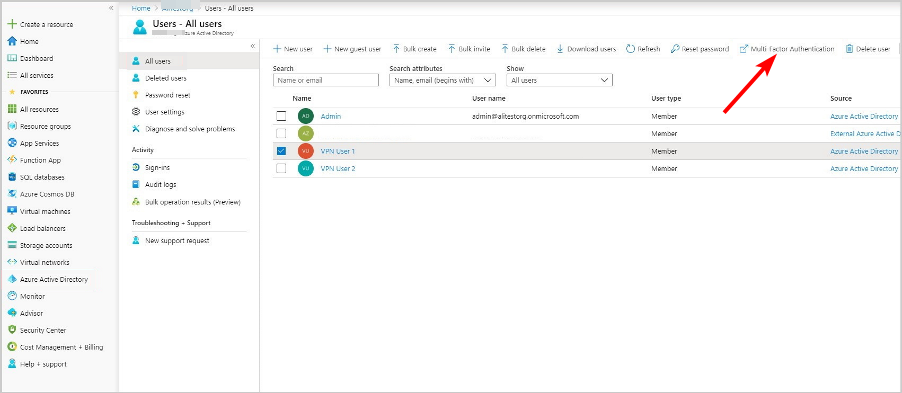
- Click on Multi-Factor Authentication.
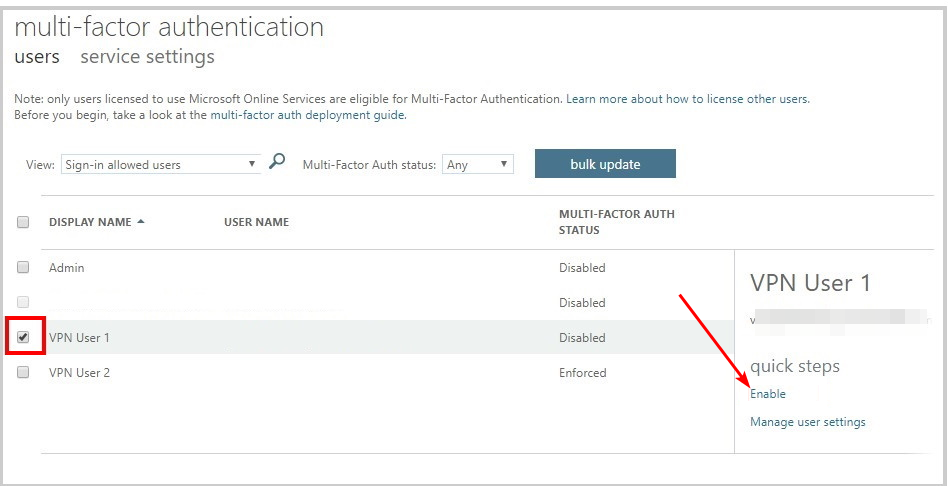
- Select the user(s) for whom you wish to enable MFA and click Enable.
It’s important to note that the steps will differ depending on the AD tool you’re using, but with these, you get a rough picture of how it should go.
For Azure users who want to fine-tune the settings and enable MFA on an application basis, you need to upgrade to the premium license that offers conditional access.
What are some of the Active Directory tools that support VPN MFA?
ADSelfService Plus – All-inclusive security tool
ADSelfService Plus is an online service that allows you to manage your account passwords and other important information. It provides a secure way to access your computer and network resources from anywhere.
With ADSelfService Plus, you can use your Windows credentials to connect to your VPN. You don’t need to remember any passwords or follow complex setup instructions. The easy-to-use interface makes it simpler for you to connect to your VPN.
Other features include:
- ADSelfService Plus is compatible with the most popular VPN services
- You can enable multi-factor authentication on a number of services including Gmail, Office 365 and Dropbox, etc
- Easily manage multiple accounts

ADSelfService Plus
Get the best tool to manage your accounts and passwords and connect yo your VPN!ADAudit Plus – Expert monitoring tool
ADAudit Plus tool allows remote VPN control and access to the network. The solution also provides the ability to enforce MFA for users that are logging into their devices using AD credentials.
In order to enable MFA for your VPN users, you need to install the Authentication Activity Monitor module on the ADAudit Plus server and configure it in accordance with your requirements.
The Authentication Activity Monitor module allows you to monitor all authentication activity performed by your users against AD resources.
Other features include:
- Customizable authentication method
- Allows remote access
- Can analyze authentication logs from any VPN solution

ADAudit Plus
Get seamless access to your network and the remote VPN control to get monitor all authentication.Azure AD – Identity protection tool
Azure AD is built on top of Microsoft Identity Manager (MIM) and leverages its multi-tenant capabilities. It provides cloud-based identity management as a service to help you manage users across your IT environment, including in the cloud.
When you enable multi-factor authentication for Azure AD, users can’t sign in unless they have an approved device, such as a phone or tablet, registered with Azure AD.
If a user attempts to sign in from an unknown device or from an unapproved device, especially for virtual machines or RDP connections, they must verify their identity by entering their username and password along with a code provided by an authenticator app.
Other features include:
- Integration with Microsoft services
- Passwordless authentication
- Identity protection feature to detect risky behavior associated with compromised credentials
Is VPN the same as MFA?
No, VPNs are not the same as MFA (Multi-Factor Authentication). Virtual Private Network (VPN) is a technology that allows you to create a secure connection to another network over the Internet.
Companies often use it to allow their employees to access internal resources such as servers, databases, and email servers securely.
MFA stands for Multi-Factor Authentication. This is a security measure that increases the security of your data by requiring more than one method of identification.
In most cases, this means that you will need to use something other than just a password for verification, like a code sent via SMS or an app on your phone.
In the question of whether a VPN is considered an MFA, VPNs are similar to MFA in that they provide an additional layer of security and identity verification. However, they aren’t exactly the same thing.
Most people who use a VPN have it configured to log in automatically. This means that anyone with access to your computer can simply start up the VPN and begin using it for their own purposes, even if you’re not around.
But by setting up MFA on your VPN, you’ll make it much harder for someone else to log in without your permission.
You may also benefit from password managers especially if you easily forget your passwords. Better yet, you can easily set up VPN for Remote Desktop if you have a large team to manage.
We’d love to hear your thoughts on how you have been able to beef up security while using VPNs in the comment section below.