Windows 10 gets silent security patch to deal with SWAPGS vulnerability
2 min. read
Published on
Read our disclosure page to find out how can you help Windows Report sustain the editorial team Read more
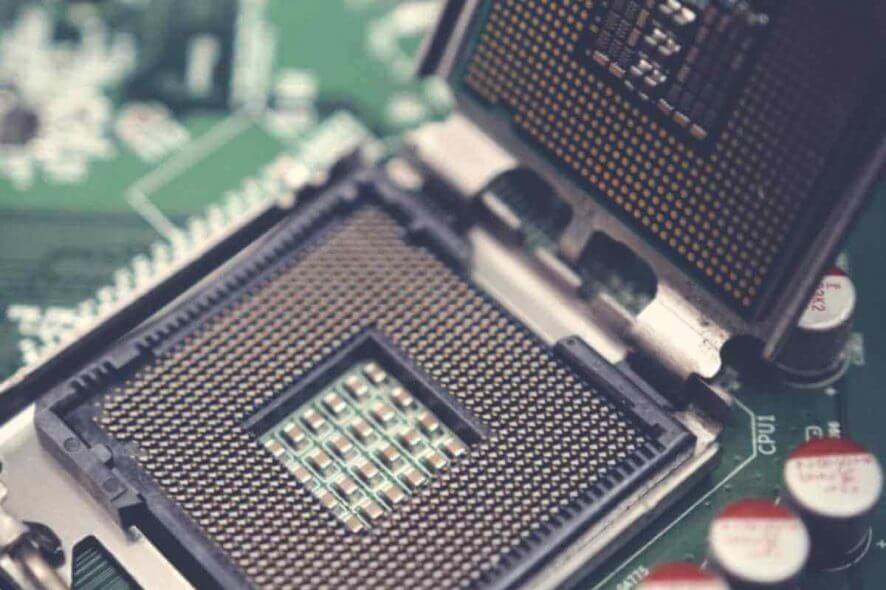
Windows PCs with Intel and AMD chips might be vulnerable again, as Spectre returns after almost a year.
New SWAPGS vulnerability bypasses previous mitigations
This time, the designated CVE-2019-1125 issue similar to Spectre and Meltdown is more powerful and bypasses previous security barriers. The SWAPGS vulnerability mainly affects Intel CPUs produced after 2012.
The vulnerability reads sensitive kernel memory and a malware attack could use it to get passwords and encryption keys out of RAM.
As such, Microsoft released a silent patch to address the problem. The update to the Linux kernel was part of last month’s Patch Tuesday, but it wasn’t revealed until recently, at the BlackHat security conference.
Updating the kernel seems to solve the problem
Here’s what RedHat had to say about CVE-2019-1125:
Red Hat has been made aware of an additional spectre-V1 like attack vector, requiring updates to the Linux kernel. This additional attack vector builds on existing software fixes shipped in previous kernel updates. This vulnerability only applies to x86-64 systems using either Intel or AMD processors.
This issue has been assignedCVE-2019-1125and is ratedModerate.
An unprivileged local attacker can use these flaws to bypass conventional memory security restrictions to gain read access to privileged memory that would otherwise be inaccessible.
Because the kernel patch builds on existing spectre mitigations from previous updates, the only solution is updating the kernel and rebooting the system.
Neither AMD nor Intel are extremely concerned with the issue, and don’t have plans to release microcode updates because the vulnerability can be addressed in software.
Bitdefender, who originally found Spectre, created a page that will give you more info on how to protect your system against critical SWAPGS attacks.