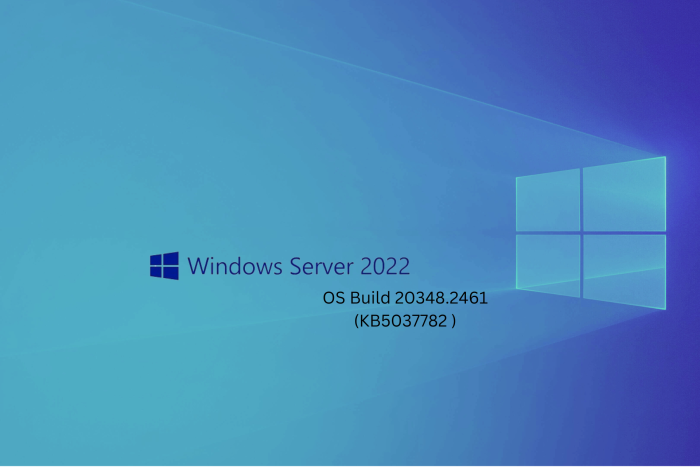
Windows Server KB5037782 update brings quality improvements and fixes the NTLM bug
The update brings the version to OS build 20348.2461
4 min. read
Published on
Read our disclosure page to find out how can you help Windows Report sustain the editorial team Read more
Recently, Microsoft acknowledged that KB5036909, released on April 9, 2024, had bugs that caused various issues, including NTLM traffic spikes in Domain Controllers (DCs) and LSASS crashes.
Microsoft fixed the issue with the latest update, released on Tuesday, 14 May 2024, which is also called the Patch Tuesday update. This update brings the version to OS Build 20348.2461.
As mentioned on the Microsoft Learn website, the NTLM traffic issue was resolved on 2024-05-14, 10:00 PT; here is what the resolution in the notes says:
Resolution: This issue was resolved by Windows updates released May 14, 2024 (KB5037782), and later. We recommend you install the latest security update for your device. It contains important improvements and issue resolutions, including this one.
This issue affected these platforms:
- Windows Server 2008
- Windows Server 2008 R2
- Windows Server 2012
- Windows Server 2012 R2
- Windows Server 2016
- Windows Server 2019
- Windows Server 2022
Here is the list of other quality improvements added in the KB5037782 Server update
- This update addresses a known issue that might affect domain controllers (DC). NTLM authentication traffic might increase.
- This update addresses an issue that affects IE mode. A webpage stops working as expected when there is an open modal dialog.
- This update addresses an issue in that affects IE mode. It stops responding. This occurs if you press the left arrow key when an empty text box has focus and caret browsing is on.
- This update addresses an issue that affects Wi-Fi Protected Access 3 (WPA3) in the Group Policy editor. HTML preview rendering fails.
- This update addresses an issue that affects a server after you remove it from a domain. The Get-LocalGroupMember cmdlet returns an exception. This occurs if the local groups contain domain members.
- This update affects next secure record 3 (NSEC3) validation in a recursive resolver. Its limit is now 1,000 computations. One computation is equal to the validation of one label with one iteration. DNS Server Administrators can change the default number of computations. To do this, use the registry setting below.
- Name: \HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\DNS\Parameters\MaxComputationForNsec3Validation
- Type: DWORD
- Default: 1000
- Max: 9600
- Min: 1
- This update addresses an issue that affects a network. An error occurs when credentials expire.
- This update addresses an issue that occurs when you use LoadImage() to loada top-down bitmap. If the bitmap has a negative height, the image does not load, and the function returns NULL.
- This update includes quarterly changes to the Windows Kernel Vulnerable Driver Blocklist file, DriverSiPolicy.p7b. It adds to the list of drivers that are at risk for Bring Your Own Vulnerable Driver (BYOVD) attacks.
- This update addresses an issue that affects a workstation that is not in a domain. When you connect from it to a share and use an IPV6 address, you get the error, “ERROR_BAD_NET_NAME.”
- This update addresses a known issue that might cause your VPN connection to fail. This occurs after you install the update dated April 9, 2024, or later.
- This update addresses an issue that might affect Virtual Secure Mode (VSM) scenarios. They might fail. These scenarios include VPN, Windows Hello, Credential Guard, and Key Guard.
- This update addresses an issue that affects Group Policy Folder Redirection in a multi-forest deployment. The issue stops you from choosing a group account from the target domain. Because of this, you cannot apply advanced folder redirection settings to that domain. This issue occurs when the target domain has a one-way trust with the domain of the admin user. This issue affects all Enhanced Security Admin Environment (ESAE), Hardened Forests (HF), or Privileged Access Management (PAM) deployments.
The resolution or the list of improvements does not mention the LSASS crashes issue, so we are unclear whether it has been resolved.
Microsoft also mentioned a known issue in the update:
Symptom Workaround After installing this update, you might be unable to change your user account profile picture.When attempting to change a profile picture by selecting the button Start> Settings > Account > Your info and, under Create your picture, clicking on Browse for one, you might receive an error message with error code 0x80070520. We are working on a resolution and will provide an update in an upcoming release
To install the update, you can simply head to Settings>Windows Update, or you can also download & install the update from the Microsoft Update Catalog website.
Have you installed the update yet? If so, share your experience with our readers in the comments section below.