Windows vulnerability roundup: Updates on PrintNightmare, PowerShell, and NETGEAR compromise
3 min. read
Published on
Read our disclosure page to find out how can you help Windows Report sustain the editorial team Read more

Recently, it has felt like Windows vulnerabilities have been piling up as various third-party endpoint connections lead to large swaths of personal information being compromised.
Fortunately, it seems Microsoft is aware of the latest compromises and is underway issuing updates and companion information on its known vulnerabilities.
Working from semi-oldest to newest, Microsoft published an update to PowerShell 7.0 and 7.1 to protect a .NET Core remote code execution vulnerability reported last week.
More specifically, Microsoft listed on its GitHub repository at the time that “a remote code execution vulnerability exists in .NET 5 and .NET Core due to how text encoding is performed.” As it stood, it vulnerable package is System.Text.Encoding.Web and left versions 4.00-4.5.0, 4.6.0-4.7.1, and 5.0.0 vulnerable.
Fortunately, Microsoft’s July 1 update can be applied to version 7.0 to 7.0.6 and version 7.1 to 7.1.3 and appears to protect against the new vulnerability. Meanwhile, Microsoft also claims that “Windows PowerShell 5.1 isn’t affected by this issue.”
Next up is the now infamous “PrintNightmare” remote code execution vulnerability that’s affecting Windows Print Spooler services. The “PrintNightmare” compromise is a bit stickier in that it deals with a more widely used Windows execution, printing.
By creating a middle-man setup between print processes and Windows, “An attacker who successfully exploited this vulnerability could run arbitrary code with SYSTEM privileges. An attacker could then install programs; view, change, or delete data; or create new accounts with full user rights,” according to Microsoft.
Microsoft has not gotten a handle on the “PrintNightmare” vulnerability it has issued an update on the situation via Twitter.
The MSRC has updated CVE-2021-34527 with more information.https://t.co/QZATXCPXnx
— Security Response (@msftsecresponse) July 2, 2021
Issuing CVE-2021-34527 to “PrintNightmare” means Microsoft can now also highlight some ways to mitigate exploitation while the company continues to work on a solution.
- Administrators
- Domain Controllers
- Read Only Domain Controllers
- Enterprise Read Only Domain Controllers
- Certificate Admins
- Schema Admins
- Enterprise Admins
- Group Policy Admins
- Power Users
- System Operators
- Print Operators
- Backup Operators
- RAS Servers
- Pre-Windows 2000 Compatible Access
- Network Configuration Operators Group Object
- Cryptographic Operators Group Object
- Local account and member of Administrators group
There are also some recommended workarounds that can include disabling print spooler service or disabling inbound remote printing through Group Policy. To read the impacts of doing either option, visit the MSRC page here.
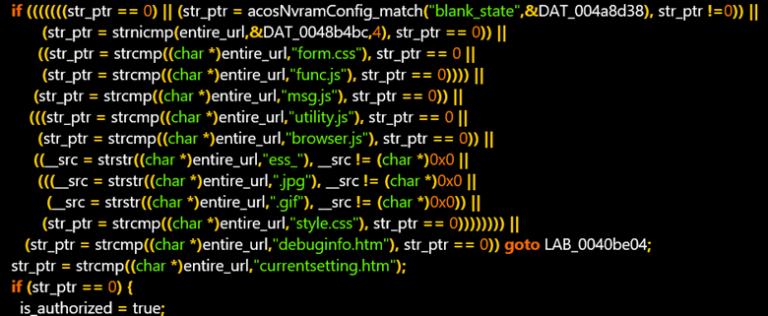
Last and the most recent Windows vulnerability includes NETGEAR firmware vulnerabilities that could, in Microsoft’s words, “lead to identity theft and full system compromise.”
Microsoft discovered the vulnerabilities in NETGEAR DGN-2200v1 series routers that can be used to compromise a network’s security structure.
More specifically, Microsoft’s Security Vulnerability Research team found three vulnerabilities in the router firmware that they have been able to reliably replicate.
However, working with NETGEAR, Microsoft and the router company were able to issue a critical security issue score (CVSS) of 7.1 9.4., to which NETGEAR has already begun issuing fixes. To read the full breakdown, Microsoft outlines unpacking the firmware, the codes to identify the specific vulnerabilities, deriving saved router credentials, how information is retrieved, and preparatory steps for prevention, here.