9 Best Intrusion Detection Software [Free & Paid]
Choose one of these great IDS software to protect your computer
10 min. read
Updated on
Read our disclosure page to find out how can you help Windows Report sustain the editorial team Read more
Key notes
- Intrusion detection software for Windows will actively scan your device for threats.
- Having a good Windows IDS that uses the latest protection technology is mandatory.
- We’ve included the best premium IDS software that can also remove any found threats.
- Some of these programs have free trials for you to try out before you buy.
Intrusion detection software for Windows checks for changes that are made by all sorts of unwanted programs that could be injected into your system by cyber criminals.
These tools study the data packets, both incoming and outgoing, to check what kind of data transfers are at hand. It will alert you if they find any suspicious activity on the system or in the network.
Intrusion detection software exists as an answer to the increasing frequency of attacks made on systems.
Such tools usually inspect the host configuration for risky settings, password files, and more areas. Then, they detect all kinds of violations that could prove dangerous for the network.
IDS also set in place various ways for the network to record any suspicious activities and potential attack methods and to report them to the admin.
In other words, an IDS is quite similar to the Windows firewall but more than guarding against attacks from outside the network, an IDS is also able to identify suspicious activity from within the network.
Some IDS software is also able to respond to potential intrusion. This is Host Intrusion Prevention System software (HIPS) or just IPS (Intrusion Prevention System).
Generally speaking, Intrusion Detection Software for Windows shows what is happening. The IPS solutions also act upon the known threats.
There are some products which combine these two features, and we’ll present to you the best on the market.

Secure your devices with award-winning cybersecurity technology.

Maximize your PC's security and performance with top-notch digital threat detection.

Keep secure with groundbreaking AI detection and prevention technology.

Browse the web securely for up to 3 devices across Windows, Mac, iOS or Android systems.

Best security tool for intense browsing activity.
What are the types of IDS?
An intrusion detection system (IDS) is a tool created to test the vulnerability exploits against a target system or computer. There are four main types of intrusion detection systems:
- Network intrusion detection system – an independent platform that monitors network traffic, probes hosts, and identifies intruders.
- Host-based intrusion detection system – an agent installed directly on the host and filters malicious traffic that goes through allocation logs, system calls, and file system modifications.
- Perimeter intrusion detection system – creates “perimeter fences” around main system infrastructures to detect and locate intrusion attempts there.
- VM-based intrusion detection system – similar to any of the three above, is deployed remotely via a virtual machine.
Best intrusion detection systems to install on PC
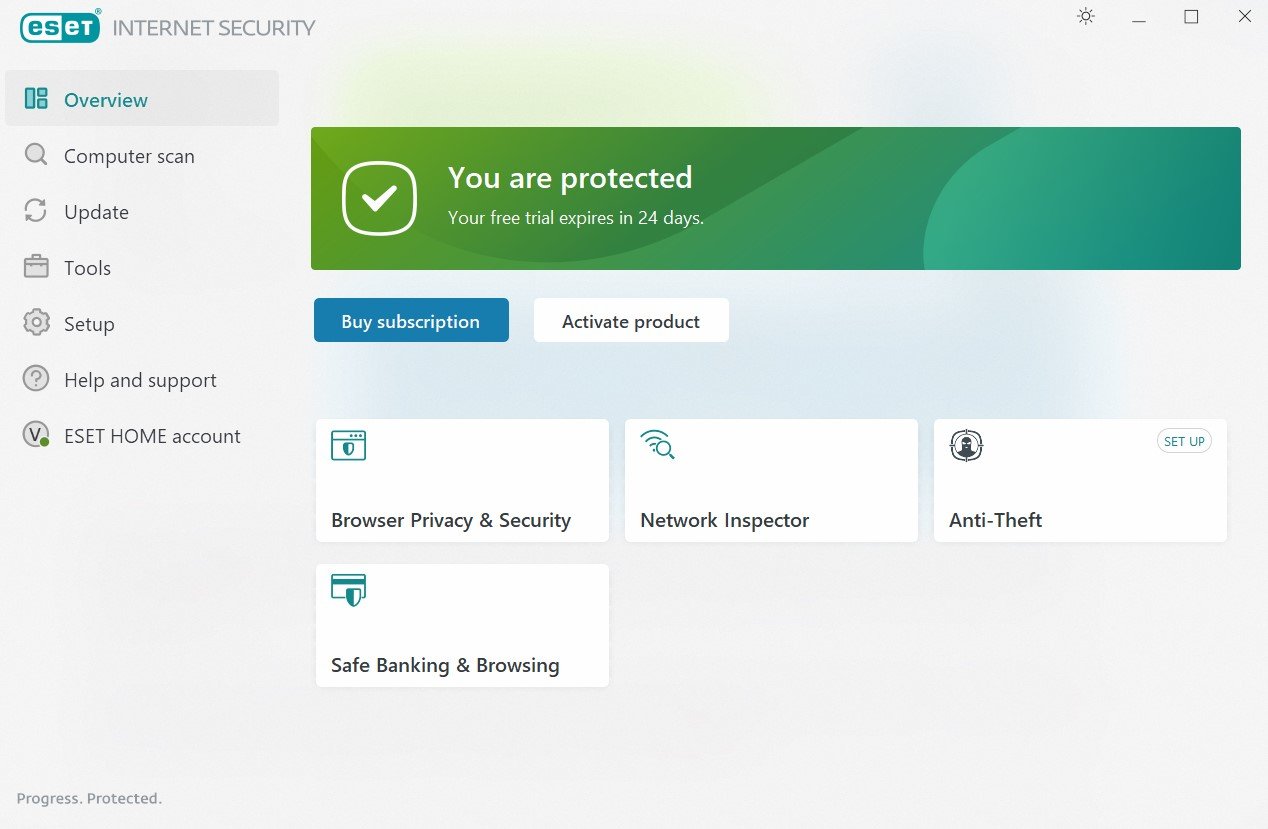
ESET HOME Security Essential – Most comprehensive security features
ESET HOME Security Essential will actively protect your PC from any kind of threat. The software will ensure that your sensitive data, banking transactions, passwords, login credentials, and webcam are safe.
ESET uses advanced AI and machine learning to create proactive protection which will stop known malware and emerging ones from entering and infecting your device.
Since it is cross-platform, the antivirus is ready to secure all kinds of devices, such as Android phones, iPhones, Linux and Windows computers, or MACs.
Here is a list of its core features:
- Privacy protection
- Anti-theft measurements
- Lightweight software with minimal power usage
- Secure active scanning and malware removal
ESET HOME Security Essential
It utilizes advanced AI to scan your computer for harmful software and keep your system safe.Total AV – Best browsing security and system maintenance

If you want complete antivirus protection, TotalAV is the right choice for you. With features to protect your system from any online or offline threats, it’s one of the few antiviruses that offers you a series of tune-up tools to maintain peak performance.
With TotalAV and WebShield, you are completely protected while browsing. Malicious websites and links are automatically blocked, and downloaded files and executables are verified before you even click on them.
Besides full virus protection, it provides a Total Adblocker to reduce all unwanted pop-ups and notifications and load all pages faster.
Some of TotalAV’s key features include:
- Data breach monitoring and alerts
- Blocking of tracking cookies
- Tune-up tools for system maintenance
- PUA protection and zero-day cloud scanning

Total AV
A great intrusion detection software that will protect every aspect of your computer.Bitdefender Internet Security – Most advanced virus protection and prevention
Bitdefender is a self-proclaimed global leader in cyber security, protecting millions of users around the world from online threats.
The software is equipped with multilayered protection to ensure nothing gets past its real-time scanning. In addition, the program is lightweight and doesn’t consume resources from your computer.
Bitdefender Internet Security will perform periodic scans, and it will actively take care of your online data and privacy, prohibiting any intruding software from stealing it.
Let’s have a look at the software’s key features:
- Multiplatform protection
- Privacy firewall
- Parental control is perfect for keeping children safe
- Multilayered antivirus, malware, ransomware, adware protection

Bitdefender Internet Security
Bitdefender Internet Security is an award-winning antivirus with unbeatable virus protection.Malwarebytes Endpoint Protection – Best malware protection
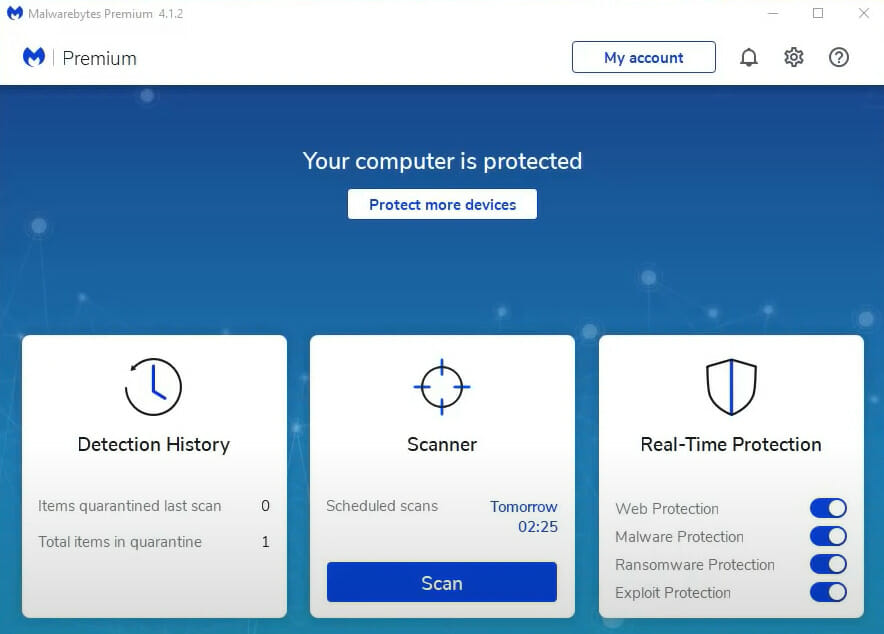
According to Malwarebytes, the industry-leading security software manufacturer, there is no better protection strategy than proactive prevention and we couldn’t agree more.
Malwarebytes Endpoint Protection is an advanced IDS solution for endpoints that uses a layered approach packed with multiple detection techniques to identify and keep malware and other cyber threats away from your systems.
It delivers best-in-class protection against both known and unknown malware, ransomware, and zero-hour threats within one unified solution meant to reduce costs and simplify the deployment process.
Let’s quickly look at its key features:
- Web protection (against malicious websites and ad networks)
- Application hardening (reduces vulnerability exploit surface)
- Application behavior protection (prevents apps’ leveraging and endpoint infection)
- Mitigation (blocks ransomware and attempts to execute code on the endpoint from any distance)
- Machine learning-based anomaly detection
- Pre and post-execution layered detection techniques
- Centralized cloud-console (for easy cloud-enabled deployment and management)

Malwarebytes Endpoint Protection
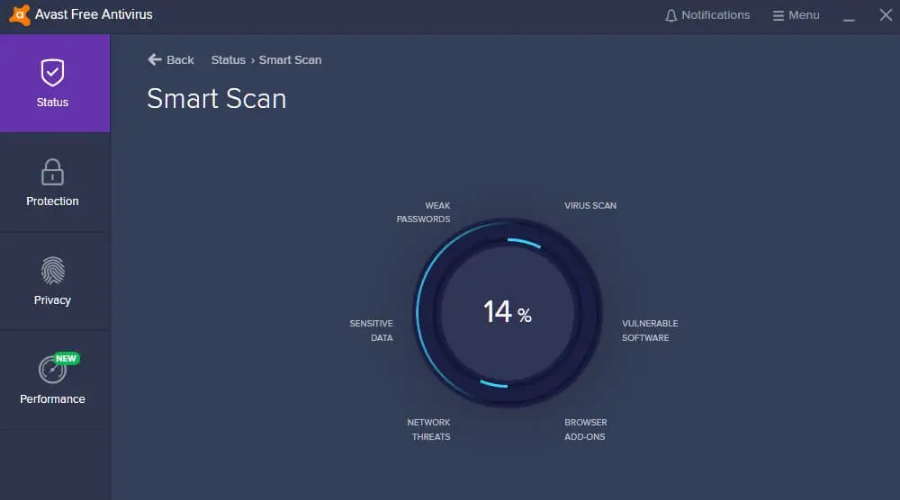
The best protection strategy is prevention. Keep your endpoints safe with Malwarebytes!Avast Free Antivirus– Great basic free protection
One other great malware detection software is Avast Free Antivirus. The program also uses advanced AI to optimize its scans and find all harmful software and viruses on your PC.
The free version of this program comes with the malware scanner and removal tool which is more than enough for those who want to keep their data secured.
If you choose to upgrade to the premium version, you’ll benefit from these key features:
- Premium malware scanner and removal
- PC cleaner and optimizer
- Customer support and remote control
- Wi-fi inspector
Avast Free Antivirus
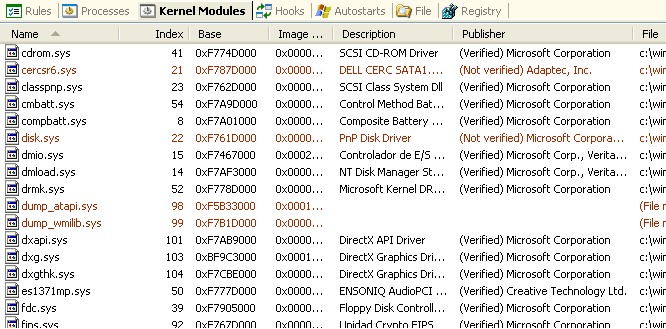
Avast gives you more than any other competitors, providing excellent antivirus protection for free.Malware Defender – Great for advanced users
This is a free Windows-compatible IPS software that provides network protection for its advanced users.
The software will successfully handle intrusion prevention and also malware detection. It is very well-suited for home use even if its instructional material is a bit too complex for average users.
Acting as a host intrusion prevention system, the tool monitors a single host for any kind of suspicious activity.
Malware Defender was initially a commercial program, but its excellent features changed its ownership a while ago, and then a new version was released that was freeware.
Let’s quickly look at its key features:
- Default installation into learning mode to reduce the number of initial alerts to a minimum
- Files, registry, application modules, and network protection
- Connection Monitor (the perfect companion to Windows native firewall, with more detailed control)
The software is an excellent performer, but its only minus would be the fact that its complexities make it unsuitable for the average user.
On the other hand, all mistakes can be rectified by changing rule permission from the log entries.
Although if you have already denied a vital system function you won’t be able to do much more to get things back the way they were before, so you should pay attention.
Snort for Windows – Open-source network IDS
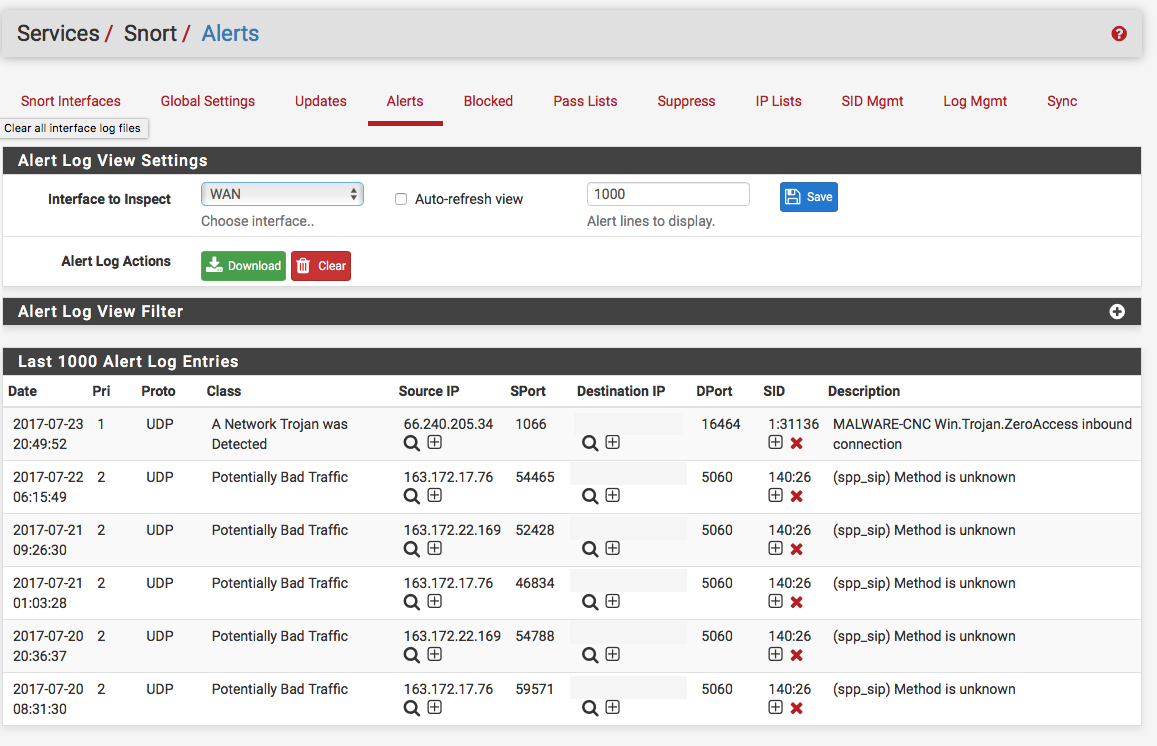
Snort for Windows is an open-source network intrusion software that delivers real-time traffic analysis and packet logging on IP networks.
The software is able to perform protocol analysis, and content searching/matching can be used to detect a variety of attacks and probes, such as buffer overflows.
It will also analyze stealth port scans, CGI attacks, SMB probes, OS fingerprinting attempts, and much more.
The program is straightforward to deploy, and it has a vast number of open-source developers. The Snort community supports the software, but it also provides the core rule sets for some commercial IDS/IPS products.
Protect your home network with the firewall devices on this thorough list and never worry about malware again.
Let’s quickly look at its key features:
- Returns everything that it sees including detailed packet decodes
- Easy configuration to only present alerts from its set of rules
- Robust tools for gathering and for analyzing network traffic.
- Deployment across very large network infrastructures is also possible
Due to its ability to be quickly deployed, its very comprehensive capabilities, and its great open-source community support, Snort is usually everyone’s favorite.
There is also the commercial version which is available as an appliance from Sourcefire, and it’s guided by Snort’s developer as its CEO.
Roesch managed to blend perfectly the best parts of the open-source and the commercial worlds into the Sourcefire offerings.
The Bro Network Security Monitor / Zeek – Good framework analysis
This is a powerful network analysis framework that is very different from the typical IDS you may have known until now. Bro’s domain-specific scripting language will enable site-specific monitoring policies.
The program comes packed with analyzers for lots of protocols, and it enables high-level semantic analysis in the application layer. It also keeps a great application-layer state about the network that it monitors.
Let’s quickly look at its key features:
- No traditional signatures (interfaces with other applications for real-time exchange of information)
- Comprehensive logs archive
- Targets especially high-performance networks
If you are looking for the best free and paid Windows 10 FTP clients, check out this awesome list with the best products on the market and decide for yourself.
While the program focuses on network security monitoring, it will also provide users with a comprehensive platform for more general network traffic analysis.
It is well-grounded in more than 15 years of research the software managed to successfully bridge the traditional gap between academics and operations from its very beginning.
The user community of Bro includes some major universities, supercomputing centers, research labs, and also lots of open-science communities.
 NOTE
NOTE
OSSEC Free IDS for Businesses – Good multi-purpose IDS
This is an open-source host-based IDS that performs file integrity checking, log analysis, policy monitoring, rootkit detection, real-time alerting, and active responses and it runs on almost all platforms including Windows.
The software watches it all, and it actively monitors all aspects of the system’s activity. With this program, you will not be in the dark regarding what is happening to your valuable computer assets anymore.
Let’s quickly look at its key features:
- Real-time analytics and insights into your network security events (via alert logs and email alerts)
- Full host-based intrusion detection across multiple platforms
- Fully open-source, and free to use
- Fully customizable (extensive configuration options, add your very own customized alert rules and writing scripts, modify the source code and add new capabilities)
- Detect and alert unauthorized file system modifications and malicious behavior based on entries in the log files
Securing your enterprise these days doesn’t have to be a nightmare and a back-breaking ordeal. All the solutions that we mentioned above will provide you with industrial-strength protection against all intrusion attempts.
All these tools combine the most popular open-source security software into one unified solution stack that will be easy enough to install and use. So feel free to pick your favorite one according to your needs.