Microsoft's October 2024 Patch Tuesday Fixes 5 Zero-Days, 118 Flaws in total
Install the updates ASAP.
9 min. read
Published on
Read our disclosure page to find out how can you help Windows Report sustain the editorial team. Read more
Microsoft’s October 2024 Patch Tuesday updates address 118 security vulnerabilities, including five zero-day flaws.
All of these vulnerabilities happen across different platforms, including Microsoft Office, Microsoft Edge, Visual Studio, Azure CLI, Microsoft Defender for Endpoint, Windows Storage, Windows Remote Desktop, DeepSpeed, and various components of Windows 10, 11, and Windows Server
- 3 vulnerabilities are critical
- 108 are important
- 7 are low-severity
The three critical flaws are all remote code execution vulnerabilities, which, if exploited, could allow an attacker to run arbitrary code on your device. They include remote code execution bugs, elevation of privilege flaws, denial of service issues, spoofing vulnerabilities, and security feature bypass bugs. Thus, installing the October 2024 Patch Tuesday updates becomes essential, and it should be done ASAP.
Microsoft also fixed a critical zero-day RCE vulnerability in the Microsoft Management Console (MSC), a Windows component used to create, save, and open administrative tools called consoles, such as the Device Manager or the Event Viewer. The zero-day, tracked as CVE-2024-43572, could be exploited by an attacker to execute code on your device by convincing you to open a specially crafted malicious MSC file. The Redmond-based tech giant confirmed it had been exploited in the wild.
Another actively exploited zero-day is a Windows MSHTML platform spoofing vulnerability identified as CVE-2024-43573.
The MSHTML platform is part of Microsoft’s Trident engine, previously used by Internet Explorer and the old version of Microsoft Edge. Although Microsoft has retired both browsers, the company continues to support some of its components in the new Edge.
Other zero-days addressed by Microsoft in the October 2024 Patch Tuesday updates include:
- CVE-2024-20659: A UEFI security feature bypass vulnerability in Windows Hyper-V.
- CVE-2024-43583: A Windows Winlogon elevation of privilege vulnerability that could be exploited to give an attacker system privileges. This bug requires the presence of a first-party Microsoft IME to be fixed.
- CVE-2024-6197: A remote code execution vulnerability in libcurl, the popular open-source client-side URL transfer library, fixed in Windows’ bundled version of the tool.
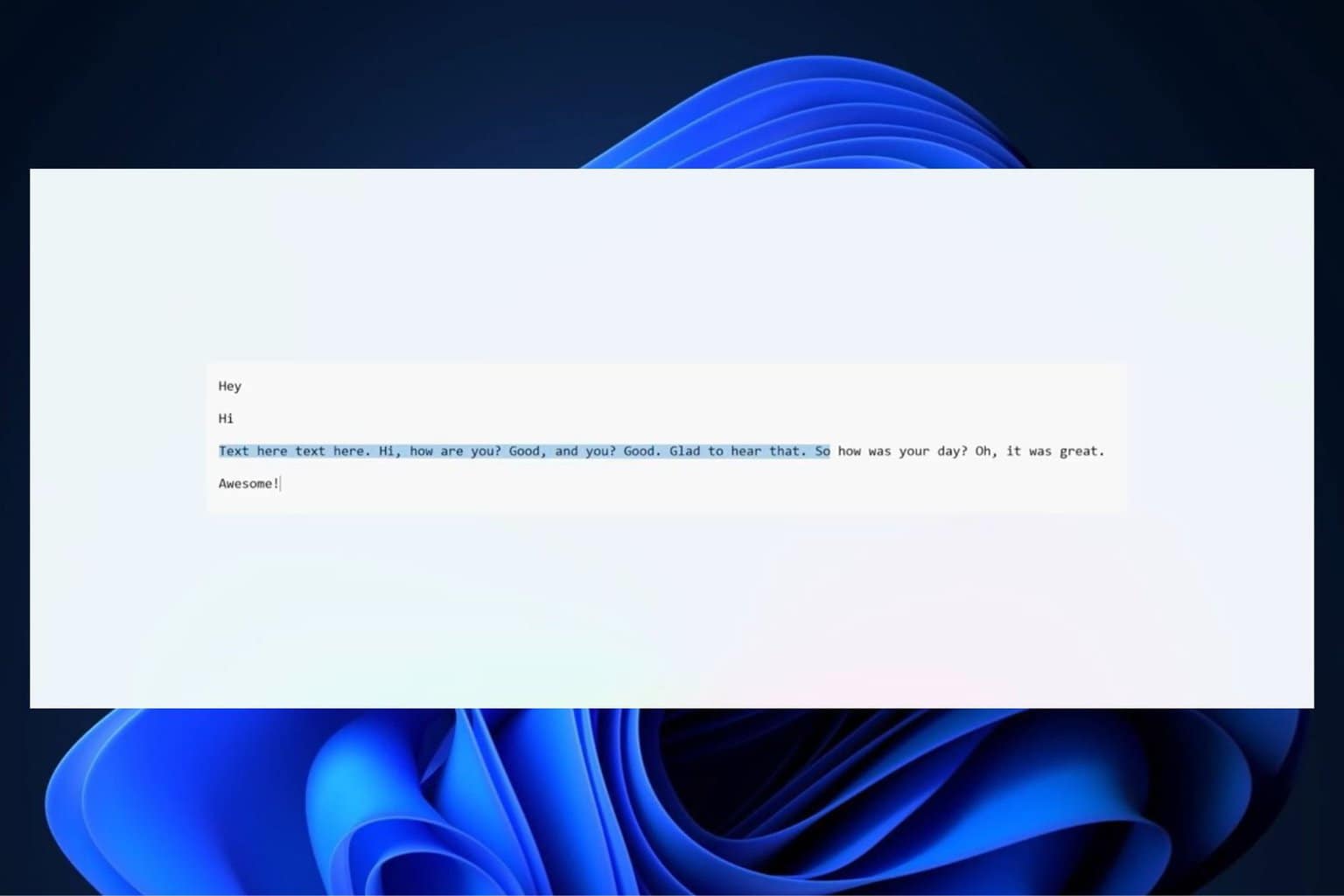
To install the October 2024 Patch Tuesday security updates, visit Settings > Update & Security > Windows Update and click the Check for updates button.
Take a look at the complete list of security flaws addressed with October 2024 Patch Tuesday updates:
| Tag | CVE ID | CVE Title | Severity |
|---|---|---|---|
| .NET and Visual Studio | CVE-2024-38229 | .NET and Visual Studio Remote Code Execution Vulnerability | Important |
| .NET and Visual Studio | CVE-2024-43485 | .NET and Visual Studio Denial of Service Vulnerability | Important |
| .NET, .NET Framework, Visual Studio | CVE-2024-43484 | .NET, .NET Framework, and Visual Studio Denial of Service Vulnerability | Important |
| .NET, .NET Framework, Visual Studio | CVE-2024-43483 | .NET, .NET Framework, and Visual Studio Denial of Service Vulnerability | Important |
| Azure CLI | CVE-2024-43591 | Azure Command Line Integration (CLI) Elevation of Privilege Vulnerability | Important |
| Azure Monitor | CVE-2024-38097 | Azure Monitor Agent Elevation of Privilege Vulnerability | Important |
| Azure Stack | CVE-2024-38179 | Azure Stack Hyperconverged Infrastructure (HCI) Elevation of Privilege Vulnerability | Important |
| BranchCache | CVE-2024-43506 | BranchCache Denial of Service Vulnerability | Important |
| BranchCache | CVE-2024-38149 | BranchCache Denial of Service Vulnerability | Important |
| Code Integrity Guard | CVE-2024-43585 | Code Integrity Guard Security Feature Bypass Vulnerability | Important |
| DeepSpeed | CVE-2024-43497 | DeepSpeed Remote Code Execution Vulnerability | Important |
| Internet Small Computer Systems Interface (iSCSI) | CVE-2024-43515 | Internet Small Computer Systems Interface (iSCSI) Denial of Service Vulnerability | Important |
| Microsoft ActiveX | CVE-2024-43517 | Microsoft ActiveX Data Objects Remote Code Execution Vulnerability | Important |
| Microsoft Configuration Manager | CVE-2024-43468 | Microsoft Configuration Manager Remote Code Execution Vulnerability | Critical |
| Microsoft Defender for Endpoint | CVE-2024-43614 | Microsoft Defender for Endpoint for Linux Spoofing Vulnerability | Important |
| Microsoft Edge (Chromium-based) | CVE-2024-9369 | Chromium: CVE-2024-9369 Insufficient data validation in Mojo | Unknown |
| Microsoft Edge (Chromium-based) | CVE-2024-9370 | Chromium: CVE-2024-9370 Inappropriate implementation in V8 | Unknown |
| Microsoft Edge (Chromium-based) | CVE-2024-7025 | Chromium: CVE-2024-7025 Integer overflow in Layout | Unknown |
| Microsoft Graphics Component | CVE-2024-43534 | Windows Graphics Component Information Disclosure Vulnerability | Important |
| Microsoft Graphics Component | CVE-2024-43508 | Windows Graphics Component Information Disclosure Vulnerability | Important |
| Microsoft Graphics Component | CVE-2024-43556 | Windows Graphics Component Elevation of Privilege Vulnerability | Important |
| Microsoft Graphics Component | CVE-2024-43509 | Windows Graphics Component Elevation of Privilege Vulnerability | Important |
| Microsoft Management Console | CVE-2024-43572 | Microsoft Management Console Remote Code Execution Vulnerability | Important |
| Microsoft Office | CVE-2024-43616 | Microsoft Office Remote Code Execution Vulnerability | Important |
| Microsoft Office | CVE-2024-43576 | Microsoft Office Remote Code Execution Vulnerability | Important |
| Microsoft Office | CVE-2024-43609 | Microsoft Office Spoofing Vulnerability | Important |
| Microsoft Office Excel | CVE-2024-43504 | Microsoft Excel Remote Code Execution Vulnerability | Important |
| Microsoft Office SharePoint | CVE-2024-43503 | Microsoft SharePoint Elevation of Privilege Vulnerability | Important |
| Microsoft Office Visio | CVE-2024-43505 | Microsoft Office Visio Remote Code Execution Vulnerability | Important |
| Microsoft Simple Certificate Enrollment Protocol | CVE-2024-43544 | Microsoft Simple Certificate Enrollment Protocol Denial of Service Vulnerability | Important |
| Microsoft Simple Certificate Enrollment Protocol | CVE-2024-43541 | Microsoft Simple Certificate Enrollment Protocol Denial of Service Vulnerability | Important |
| Microsoft WDAC OLE DB provider for SQL | CVE-2024-43519 | Microsoft WDAC OLE DB provider for SQL Server Remote Code Execution Vulnerability | Important |
| Microsoft Windows Speech | CVE-2024-43574 | Microsoft Speech Application Programming Interface (SAPI) Remote Code Execution Vulnerability | Important |
| OpenSSH for Windows | CVE-2024-43615 | Microsoft OpenSSH for Windows Remote Code Execution Vulnerability | Important |
| OpenSSH for Windows | CVE-2024-43581 | Microsoft OpenSSH for Windows Remote Code Execution Vulnerability | Important |
| OpenSSH for Windows | CVE-2024-38029 | Microsoft OpenSSH for Windows Remote Code Execution Vulnerability | Important |
| Outlook for Android | CVE-2024-43604 | Outlook for Android Elevation of Privilege Vulnerability | Important |
| Power BI | CVE-2024-43612 | Power BI Report Server Spoofing Vulnerability | Important |
| Power BI | CVE-2024-43481 | Power BI Report Server Spoofing Vulnerability | Important |
| Remote Desktop Client | CVE-2024-43533 | Remote Desktop Client Remote Code Execution Vulnerability | Important |
| Remote Desktop Client | CVE-2024-43599 | Remote Desktop Client Remote Code Execution Vulnerability | Important |
| Role: Windows Hyper-V | CVE-2024-43521 | Windows Hyper-V Denial of Service Vulnerability | Important |
| Role: Windows Hyper-V | CVE-2024-20659 | Windows Hyper-V Security Feature Bypass Vulnerability | Important |
| Role: Windows Hyper-V | CVE-2024-43567 | Windows Hyper-V Denial of Service Vulnerability | Important |
| Role: Windows Hyper-V | CVE-2024-43575 | Windows Hyper-V Denial of Service Vulnerability | Important |
| RPC Endpoint Mapper Service | CVE-2024-43532 | Remote Registry Service Elevation of Privilege Vulnerability | Important |
| Service Fabric | CVE-2024-43480 | Azure Service Fabric for Linux Remote Code Execution Vulnerability | Important |
| Sudo for Windows | CVE-2024-43571 | Sudo for Windows Spoofing Vulnerability | Important |
| Visual C++ Redistributable Installer | CVE-2024-43590 | Visual C++ Redistributable Installer Elevation of Privilege Vulnerability | Important |
| Visual Studio | CVE-2024-43603 | Visual Studio Collector Service Denial of Service Vulnerability | Important |
| Visual Studio Code | CVE-2024-43488 | Visual Studio Code extension for Arduino Remote Code Execution Vulnerability | Critical |
| Visual Studio Code | CVE-2024-43601 | Visual Studio Code for Linux Remote Code Execution Vulnerability | Important |
| Windows Ancillary Function Driver for WinSock | CVE-2024-43563 | Windows Ancillary Function Driver for WinSock Elevation of Privilege Vulnerability | Important |
| Windows BitLocker | CVE-2024-43513 | BitLocker Security Feature Bypass Vulnerability | Important |
| Windows Common Log File System Driver | CVE-2024-43501 | Windows Common Log File System Driver Elevation of Privilege Vulnerability | Important |
| Windows Cryptographic Services | CVE-2024-43546 | Windows Cryptographic Information Disclosure Vulnerability | Important |
| Windows cURL Implementation | CVE-2024-6197 | Open Source Curl Remote Code Execution Vulnerability | Important |
| Windows EFI Partition | CVE-2024-37982 | Windows Resume Extensible Firmware Interface Security Feature Bypass Vulnerability | Important |
| Windows EFI Partition | CVE-2024-37976 | Windows Resume Extensible Firmware Interface Security Feature Bypass Vulnerability | Important |
| Windows EFI Partition | CVE-2024-37983 | Windows Resume Extensible Firmware Interface Security Feature Bypass Vulnerability | Important |
| Windows Hyper-V | CVE-2024-30092 | Windows Hyper-V Remote Code Execution Vulnerability | Important |
| Windows Kerberos | CVE-2024-43547 | Windows Kerberos Information Disclosure Vulnerability | Important |
| Windows Kerberos | CVE-2024-38129 | Windows Kerberos Elevation of Privilege Vulnerability | Important |
| Windows Kernel | CVE-2024-43502 | Windows Kernel Elevation of Privilege Vulnerability | Important |
| Windows Kernel | CVE-2024-43511 | Windows Kernel Elevation of Privilege Vulnerability | Important |
| Windows Kernel | CVE-2024-43520 | Windows Kernel Denial of Service Vulnerability | Important |
| Windows Kernel | CVE-2024-43527 | Windows Kernel Elevation of Privilege Vulnerability | Important |
| Windows Kernel | CVE-2024-43570 | Windows Kernel Elevation of Privilege Vulnerability | Important |
| Windows Kernel | CVE-2024-37979 | Windows Kernel Elevation of Privilege Vulnerability | Important |
| Windows Kernel-Mode Drivers | CVE-2024-43554 | Windows Kernel-Mode Driver Information Disclosure Vulnerability | Important |
| Windows Kernel-Mode Drivers | CVE-2024-43535 | Windows Kernel-Mode Driver Elevation of Privilege Vulnerability | Important |
| Windows Local Security Authority (LSA) | CVE-2024-43522 | Windows Local Security Authority (LSA) Elevation of Privilege Vulnerability | Important |
| Windows Mobile Broadband | CVE-2024-43555 | Windows Mobile Broadband Driver Denial of Service Vulnerability | Important |
| Windows Mobile Broadband | CVE-2024-43540 | Windows Mobile Broadband Driver Denial of Service Vulnerability | Important |
| Windows Mobile Broadband | CVE-2024-43536 | Windows Mobile Broadband Driver Remote Code Execution Vulnerability | Important |
| Windows Mobile Broadband | CVE-2024-43538 | Windows Mobile Broadband Driver Denial of Service Vulnerability | Important |
| Windows Mobile Broadband | CVE-2024-43525 | Windows Mobile Broadband Driver Remote Code Execution Vulnerability | Important |
| Windows Mobile Broadband | CVE-2024-43559 | Windows Mobile Broadband Driver Denial of Service Vulnerability | Important |
| Windows Mobile Broadband | CVE-2024-43561 | Windows Mobile Broadband Driver Denial of Service Vulnerability | Important |
| Windows Mobile Broadband | CVE-2024-43558 | Windows Mobile Broadband Driver Denial of Service Vulnerability | Important |
| Windows Mobile Broadband | CVE-2024-43542 | Windows Mobile Broadband Driver Denial of Service Vulnerability | Important |
| Windows Mobile Broadband | CVE-2024-43557 | Windows Mobile Broadband Driver Denial of Service Vulnerability | Important |
| Windows Mobile Broadband | CVE-2024-43526 | Windows Mobile Broadband Driver Remote Code Execution Vulnerability | Important |
| Windows Mobile Broadband | CVE-2024-43543 | Windows Mobile Broadband Driver Remote Code Execution Vulnerability | Important |
| Windows Mobile Broadband | CVE-2024-43523 | Windows Mobile Broadband Driver Remote Code Execution Vulnerability | Important |
| Windows Mobile Broadband | CVE-2024-43524 | Windows Mobile Broadband Driver Remote Code Execution Vulnerability | Important |
| Windows Mobile Broadband | CVE-2024-43537 | Windows Mobile Broadband Driver Denial of Service Vulnerability | Important |
| Windows MSHTML Platform | CVE-2024-43573 | Windows MSHTML Platform Spoofing Vulnerability | Moderate |
| Windows Netlogon | CVE-2024-38124 | Windows Netlogon Elevation of Privilege Vulnerability | Important |
| Windows Network Address Translation (NAT) | CVE-2024-43562 | Windows Network Address Translation (NAT) Denial of Service Vulnerability | Important |
| Windows Network Address Translation (NAT) | CVE-2024-43565 | Windows Network Address Translation (NAT) Denial of Service Vulnerability | Important |
| Windows NT OS Kernel | CVE-2024-43553 | NT OS Kernel Elevation of Privilege Vulnerability | Important |
| Windows NTFS | CVE-2024-43514 | Windows Resilient File System (ReFS) Elevation of Privilege Vulnerability | Important |
| Windows Online Certificate Status Protocol (OCSP) | CVE-2024-43545 | Windows Online Certificate Status Protocol (OCSP) Server Denial of Service Vulnerability | Important |
| Windows Print Spooler Components | CVE-2024-43529 | Windows Print Spooler Elevation of Privilege Vulnerability | Important |
| Windows Remote Desktop | CVE-2024-43582 | Remote Desktop Protocol Server Remote Code Execution Vulnerability | Critical |
| Windows Remote Desktop Licensing Service | CVE-2024-38262 | Windows Remote Desktop Licensing Service Remote Code Execution Vulnerability | Important |
| Windows Remote Desktop Services | CVE-2024-43456 | Windows Remote Desktop Services Tampering Vulnerability | Important |
| Windows Resilient File System (ReFS) | CVE-2024-43500 | Windows Resilient File System (ReFS) Information Disclosure Vulnerability | Important |
| Windows Routing and Remote Access Service (RRAS) | CVE-2024-43592 | Windows Routing and Remote Access Service (RRAS) Remote Code Execution Vulnerability | Important |
| Windows Routing and Remote Access Service (RRAS) | CVE-2024-43589 | Windows Routing and Remote Access Service (RRAS) Remote Code Execution Vulnerability | Important |
| Windows Routing and Remote Access Service (RRAS) | CVE-2024-38212 | Windows Routing and Remote Access Service (RRAS) Remote Code Execution Vulnerability | Important |
| Windows Routing and Remote Access Service (RRAS) | CVE-2024-43593 | Windows Routing and Remote Access Service (RRAS) Remote Code Execution Vulnerability | Important |
| Windows Routing and Remote Access Service (RRAS) | CVE-2024-38261 | Windows Routing and Remote Access Service (RRAS) Remote Code Execution Vulnerability | Important |
| Windows Routing and Remote Access Service (RRAS) | CVE-2024-43611 | Windows Routing and Remote Access Service (RRAS) Remote Code Execution Vulnerability | Important |
| Windows Routing and Remote Access Service (RRAS) | CVE-2024-43453 | Windows Routing and Remote Access Service (RRAS) Remote Code Execution Vulnerability | Important |
| Windows Routing and Remote Access Service (RRAS) | CVE-2024-38265 | Windows Routing and Remote Access Service (RRAS) Remote Code Execution Vulnerability | Important |
| Windows Routing and Remote Access Service (RRAS) | CVE-2024-43607 | Windows Routing and Remote Access Service (RRAS) Remote Code Execution Vulnerability | Important |
| Windows Routing and Remote Access Service (RRAS) | CVE-2024-43549 | Windows Routing and Remote Access Service (RRAS) Remote Code Execution Vulnerability | Important |
| Windows Routing and Remote Access Service (RRAS) | CVE-2024-43608 | Windows Routing and Remote Access Service (RRAS) Remote Code Execution Vulnerability | Important |
| Windows Routing and Remote Access Service (RRAS) | CVE-2024-43564 | Windows Routing and Remote Access Service (RRAS) Remote Code Execution Vulnerability | Important |
| Windows Scripting | CVE-2024-43584 | Windows Scripting Engine Security Feature Bypass Vulnerability | Important |
| Windows Secure Channel | CVE-2024-43550 | Windows Secure Channel Spoofing Vulnerability | Important |
| Windows Secure Kernel Mode | CVE-2024-43516 | Windows Secure Kernel Mode Elevation of Privilege Vulnerability | Important |
| Windows Secure Kernel Mode | CVE-2024-43528 | Windows Secure Kernel Mode Elevation of Privilege Vulnerability | Important |
| Windows Shell | CVE-2024-43552 | Windows Shell Remote Code Execution Vulnerability | Important |
| Windows Standards-Based Storage Management Service | CVE-2024-43512 | Windows Standards-Based Storage Management Service Denial of Service Vulnerability | Important |
| Windows Storage | CVE-2024-43551 | Windows Storage Elevation of Privilege Vulnerability | Important |
| Windows Storage Port Driver | CVE-2024-43560 | Microsoft Windows Storage Port Driver Elevation of Privilege Vulnerability | Important |
| Windows Telephony Server | CVE-2024-43518 | Windows Telephony Server Remote Code Execution Vulnerability | Important |
| Winlogon | CVE-2024-43583 | Winlogon Elevation of Privilege Vulnerability | Important |
In other news, the October 2024 Patch Tuesday updates are also the first released to Windows 11 24H2, which still doesn’t fix the ongoing Roblox issue. Windows 10 has also received them, although some versions of this operating system are no longer eligible for Patch Tuesday updates.




User forum
0 messages