Warning: These VPN extensions for Chrome leak your DNS
Key notes
- There are plenty of Chrome extensions out there that can leak your DNS to third parties.
- When that happens, you should either remove the extensions or get a VPN service.
- However, things may be a tad more complicated and require a more advanced approach.
- Check out our guide and learn how you can keep your Chrome extensions from leaking DNS.

World-class 24/7 support with 82% for a 2 years plan and 2 months free
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Amazing connection speed with 61% off and 4 months free for the 2-years plan.

Best security protocols with 83% off and 2 months free for a 2-year plan.
Recent reports confirmed that many VPN tools actually leak your IP address to third-party entities. We recently came across a new security report that suggests things are even worse when it comes to Chrome VPN extensions.
As a matter of fact, a whopping 70% of all the tested extensions leak your DNS.
Security researcher John Mason and ethical hacker File Descriptor tested 15 VPN services and found out that 10 of them actually leak your DNS through their browser extensions.
A VPN that doesn’t leak your IP or DNS
Since you can’t rely on extensions too much, you will either have to remove them or go for a full-fledged VPN service. Whichever you may choose, the VPN recommended below is a go-to solution.
This tool is owned by Kape Technologies, and it is backed up by 35,906 servers in 77 different countries, allowing unparalleled access to all geo-restricted content.
The VPN is extremely easy to use, to the point where it can be considered easier to manage than an actual browser extension.
Your connection will remain secure thanks to the encryption, and you won’t have to worry about common VPN-related issues, such as latency or limited bandwidth.

Private Internet Access
A reliable VPN service that is easier to use than a browser extension that offers full security features. Now at a discount price for a limited time only!As John Mason explains, Chrome uses DNS Prefetching to reduce website loading latency by predicting what websites you’re going to visit.
Chrome provides users with two modes to set up proxy connections after installing a VPN extension: fixed_servers and pac_script.
The majority of VPN extensions use the PAC-script mode. However, this mode allows dynamic HTTPS/SOCKS proxy server host changes. Up to a certain point, this is a good thing as it optimizes the VPN connection depending on what websites users choose to visit.
So, if you use your extension to play games, the script will select a proxy server that’s optimized for playing games.
However, this behavior leaves users vulnerable to DNS leaking. The certain webpage might force visitors to leak DNS requests.
In other words, when you type a website address in the address bar, the suggested URL is actually DNS prefetched. This means that ISPs can then collect this information about the websites that you often visit even if you use a VPN extension.
The list of VPN extensions affected by DNS leaks includes: Hola VPN, TunnelBear, Betternet, Ivacy VPN, DotVPN and more.
Private Internet Access is on the list of VPNs that are not leaking your DNS.
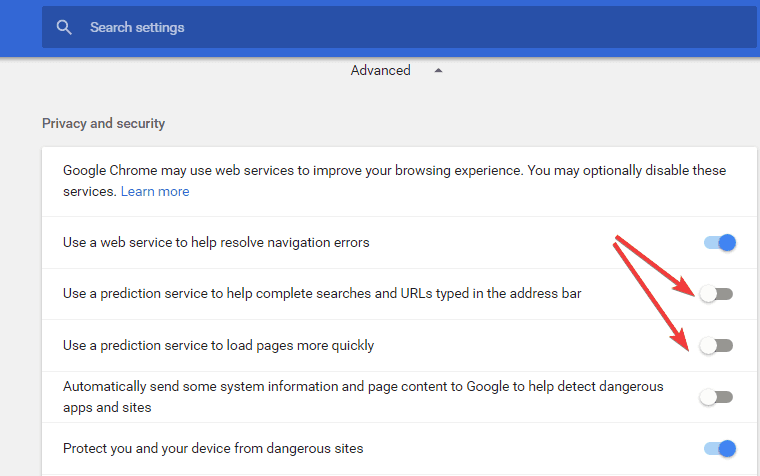
You can mitigate this DNS leak problem by disabling the predictive service from Chrome‘s Settings.
DNS leaks may severely affect your online privacy and security. To keep your DNS protected, you can also use DNS Server 1.1.1.1 on your PC, or use a DNS protection tool such as DNS Lock.
Read our disclosure page to find out how can you help Windows Report sustain the editorial team. Read more








User forum
0 messages