The July 2023 Patch Tuesday addresses 132 CVEs
You can install the latest Patch Tuesday updates now.
20 min. read
Updated on
Read our disclosure page to find out how can you help Windows Report sustain the editorial team Read more
Key notes
- For July 2023, Microsoft released a long list of 132 new security updates.
- Out of all the CVEs, 9 are Critical, 121 of them are listed as important, and 2 are advisories.
- We've included each and everyone in this article, with direct links as well to updates as well.

It’s that time of the month, again. Yes, you’ve guessed it. The July 2023 Patch Tuesday is here and amongst the features that it brings, the rollout also addresses 132 flaws. Of these flaws, 9 of them are critical, and 121 are important. There are also 2 advisories.
This is a good step for Windows 11, considering last month, Microsoft addressed and fixed 69 flaws in security and privacy with the rollout then.
For these updates to take effect, please update your Windows 11 as soon as possible. Your device should automatically download updates, and it will only ask you to restart your PC. But if not, go to Settings > Windows update > Check for updates. And then let Windows 11 do the work.
However, if you want to install them on your own here are the direct links. KB5028185 and KB5028182.
Microsoft provides fixes for 132 flaws in July 2023
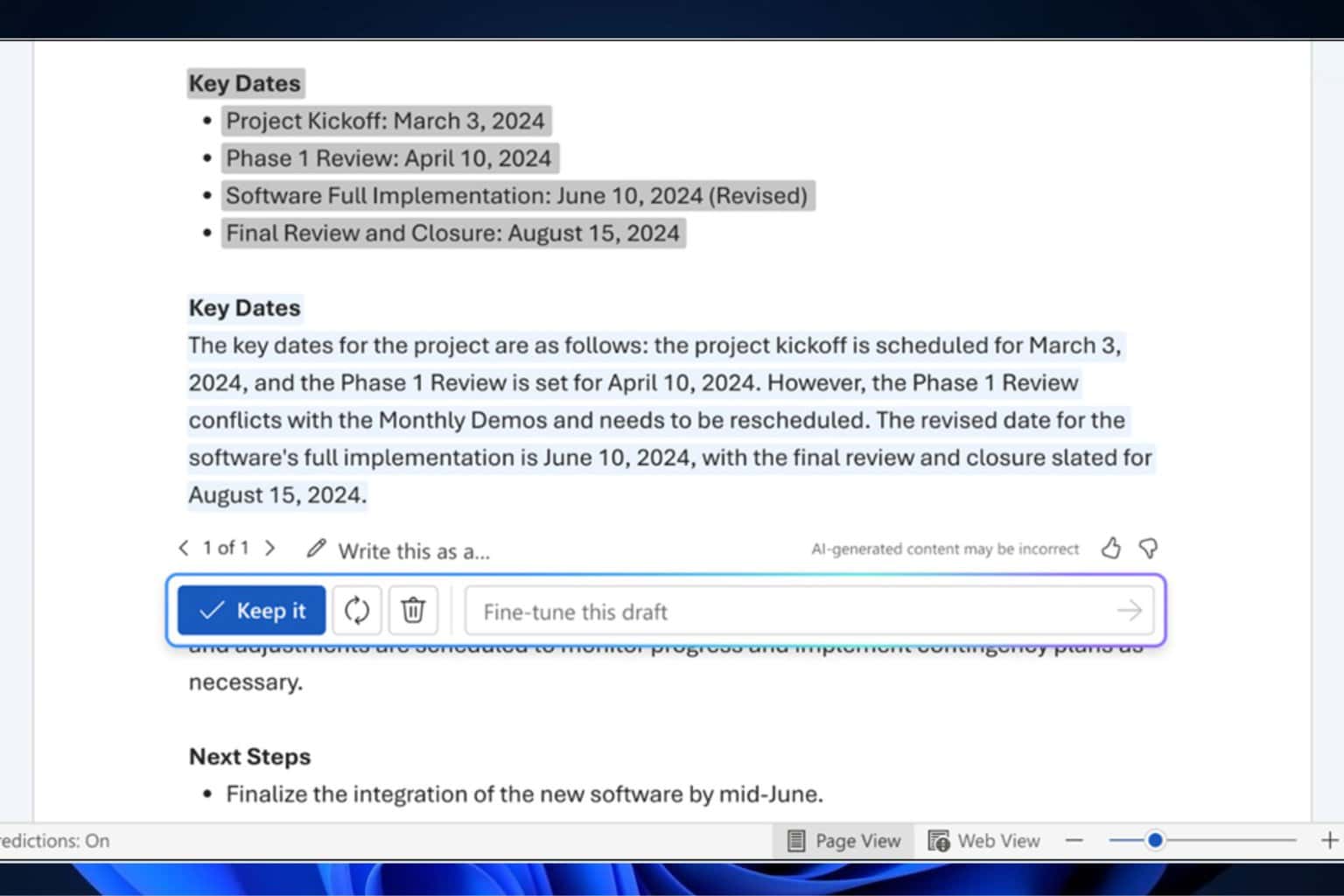
Below there are all the CVEs addressed in this Patch Tuesday rollout. As you can see in the Tag section, each CVE is related to one of Microsoft’s products and Windows features.
| Tag | CVE | Base Score | CVSS Vector | Exploitability | FAQs? | Workarounds? | Mitigations? |
|---|---|---|---|---|---|---|---|
| Windows Certificates | ADV230001 | Exploitation Detected | No | No | No | ||
| Windows EFI Partition | ADV230002 | Exploitation Less Likely | No | No | No | ||
| Windows Netlogon | CVE-2023-21526 | 7.4 | CVSS:3.1/AV:N/AC:H/PR:N/UI:N/S:U/C:H/I:H/A:N/E:U/RL:O/RC:C | Exploitation More Likely | Yes | No | No |
| Microsoft Graphics Component | CVE-2023-21756 | 7.8 | CVSS:3.1/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Windows Admin Center | CVE-2023-29347 | 8.7 | CVSS:3.1/AV:N/AC:L/PR:L/UI:R/S:C/C:N/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Windows Cluster Server | CVE-2023-32033 | 6.6 | CVSS:3.1/AV:N/AC:H/PR:H/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Windows Remote Procedure Call | CVE-2023-32034 | 6.5 | CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:N/I:N/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | No | No | No |
| Windows Remote Procedure Call | CVE-2023-32035 | 6.5 | CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:N/I:N/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | No | No | No |
| Windows Layer 2 Tunneling Protocol | CVE-2023-32037 | 6.5 | CVSS:3.1/AV:A/AC:L/PR:N/UI:N/S:U/C:H/I:N/A:N/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Windows ODBC Driver | CVE-2023-32038 | 8.8 | CVSS:3.1/AV:N/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | Yes |
| Microsoft Printer Drivers | CVE-2023-32039 | 5.5 | CVSS:3.1/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:N/A:N/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Microsoft Printer Drivers | CVE-2023-32040 | 5.5 | CVSS:3.1/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:N/A:N/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Windows Update Orchestrator Service | CVE-2023-32041 | 5.5 | CVSS:3.1/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:N/A:N/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Windows OLE | CVE-2023-32042 | 6.5 | CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:N/A:N/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Windows Remote Desktop | CVE-2023-32043 | 6.8 | CVSS:3.1/AV:N/AC:H/PR:N/UI:R/S:U/C:H/I:H/A:N/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Windows Message Queuing | CVE-2023-32044 | 7.5 | CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:N/I:N/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | No | No | No |
| Windows Message Queuing | CVE-2023-32045 | 7.5 | CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:N/I:N/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | No | No | No |
| Windows MSHTML Platform | CVE-2023-32046 | 7.8 | CVSS:3.1/AV:L/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Detected | Yes | No | No |
| Paint 3D | CVE-2023-32047 | 7.8 | CVSS:3.1/AV:L/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Unlikely | Yes | No | No |
| Windows SmartScreen | CVE-2023-32049 | 8.8 | CVSS:3.1/AV:N/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H/E:F/RL:O/RC:C | Exploitation Detected | Yes | No | No |
| Windows Installer | CVE-2023-32050 | 7.0 | CVSS:3.1/AV:L/AC:H/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Microsoft Windows Codecs Library | CVE-2023-32051 | 7.8 | CVSS:3.1/AV:L/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Microsoft Power Apps | CVE-2023-32052 | 6.3 | CVSS:3.1/AV:N/AC:L/PR:L/UI:R/S:U/C:H/I:L/A:N/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Windows Installer | CVE-2023-32053 | 7.8 | CVSS:3.1/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Windows Volume Shadow Copy | CVE-2023-32054 | 7.3 | CVSS:3.1/AV:L/AC:L/PR:L/UI:R/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Windows Active Template Library | CVE-2023-32055 | 6.7 | CVSS:3.1/AV:L/AC:L/PR:H/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Windows Server Update Service | CVE-2023-32056 | 7.8 | CVSS:3.1/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Windows Message Queuing | CVE-2023-32057 | 9.8 | CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | Yes |
| Windows Failover Cluster | CVE-2023-32083 | 6.5 | CVSS:3.1/AV:N/AC:L/PR:H/UI:N/S:U/C:H/I:N/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Windows HTTP.sys | CVE-2023-32084 | 7.5 | CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:N/I:N/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | No | No | No |
| Microsoft Printer Drivers | CVE-2023-32085 | 5.5 | CVSS:3.1/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:N/A:N/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| .NET and Visual Studio | CVE-2023-33127 | 8.1 | CVSS:3.1/AV:N/AC:H/PR:N/UI:N/S:U/C:H/I:H/A:H/E:P/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Microsoft Office SharePoint | CVE-2023-33134 | 8.8 | CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation More Likely | Yes | No | No |
| Microsoft Office | CVE-2023-33148 | 7.8 | CVSS:3.1/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Microsoft Graphics Component | CVE-2023-33149 | 7.8 | CVSS:3.1/AV:L/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Microsoft Office | CVE-2023-33150 | 9.6 | CVSS:3.1/AV:N/AC:L/PR:N/UI:R/S:C/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Microsoft Office Outlook | CVE-2023-33151 | 6.5 | CVSS:3.1/AV:N/AC:L/PR:N/UI:R/S:U/C:H/I:N/A:N/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Microsoft Office Access | CVE-2023-33152 | 7.0 | CVSS:3.1/AV:L/AC:H/PR:N/UI:R/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Microsoft Office Outlook | CVE-2023-33153 | 6.8 | CVSS:3.1/AV:N/AC:H/PR:N/UI:R/S:U/C:N/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Windows Partition Management Driver | CVE-2023-33154 | 7.8 | CVSS:3.1/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Windows Cloud Files Mini Filter Driver | CVE-2023-33155 | 7.8 | CVSS:3.1/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Windows Defender | CVE-2023-33156 | 6.3 | CVSS:3.1/AV:L/AC:H/PR:L/UI:N/S:U/C:N/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Microsoft Office SharePoint | CVE-2023-33157 | 8.8 | CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation More Likely | Yes | No | No |
| Microsoft Office Excel | CVE-2023-33158 | 7.8 | CVSS:3.1/AV:L/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Microsoft Office SharePoint | CVE-2023-33159 | 8.8 | CVSS:3.1/AV:N/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Microsoft Office SharePoint | CVE-2023-33160 | 8.8 | CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Microsoft Office Excel | CVE-2023-33161 | 7.8 | CVSS:3.1/AV:L/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Microsoft Office Excel | CVE-2023-33162 | 5.5 | CVSS:3.1/AV:L/AC:L/PR:N/UI:R/S:U/C:H/I:N/A:N/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Windows Network Load Balancing | CVE-2023-33163 | 7.5 | CVSS:3.1/AV:A/AC:H/PR:N/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Windows Remote Procedure Call | CVE-2023-33164 | 6.5 | CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:N/I:N/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | No | No | No |
| Microsoft Office SharePoint | CVE-2023-33165 | 4.3 | CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:N/I:L/A:N/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Windows Remote Procedure Call | CVE-2023-33166 | 6.5 | CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:N/I:N/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | No | No | No |
| Windows Remote Procedure Call | CVE-2023-33167 | 6.5 | CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:N/I:N/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | No | No | No |
| Windows Remote Procedure Call | CVE-2023-33168 | 6.5 | CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:N/I:N/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | No | No | No |
| Windows Remote Procedure Call | CVE-2023-33169 | 6.5 | CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:N/I:N/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | No | No | No |
| ASP.NET and .NET | CVE-2023-33170 | 8.1 | CVSS:3.1/AV:N/AC:H/PR:N/UI:N/S:U/C:H/I:H/A:H/E:P/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Microsoft Dynamics | CVE-2023-33171 | 6.1 | CVSS:3.1/AV:N/AC:L/PR:N/UI:R/S:C/C:L/I:L/A:N/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Windows Remote Procedure Call | CVE-2023-33172 | 6.5 | CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:N/I:N/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | No | No | No |
| Windows Remote Procedure Call | CVE-2023-33173 | 6.5 | CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:N/I:N/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | No | No | No |
| Windows Cryptographic Services | CVE-2023-33174 | 5.5 | CVSS:3.1/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:N/A:N/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Microsoft Printer Drivers | CVE-2023-35296 | 6.5 | CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:N/A:N/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Windows PGM | CVE-2023-35297 | 7.5 | CVSS:3.1/AV:A/AC:H/PR:N/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Windows HTTP.sys | CVE-2023-35298 | 7.5 | CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:N/I:N/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Windows Common Log File System Driver | CVE-2023-35299 | 7.8 | CVSS:3.1/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Windows Remote Procedure Call | CVE-2023-35300 | 8.8 | CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Microsoft Printer Drivers | CVE-2023-35302 | 8.8 | CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | Yes | No |
| Microsoft Windows Codecs Library | CVE-2023-35303 | 8.8 | CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Windows Kernel | CVE-2023-35304 | 7.8 | CVSS:3.1/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Windows Kernel | CVE-2023-35305 | 7.8 | CVSS:3.1/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Microsoft Printer Drivers | CVE-2023-35306 | 5.5 | CVSS:3.1/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:N/A:N/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Windows MSHTML Platform | CVE-2023-35308 | 4.4 | CVSS:3.1/AV:L/AC:L/PR:N/UI:R/S:U/C:N/I:L/A:L/E:P/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Windows Message Queuing | CVE-2023-35309 | 7.5 | CVSS:3.1/AV:N/AC:H/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Role: DNS Server | CVE-2023-35310 | 6.6 | CVSS:3.1/AV:N/AC:H/PR:H/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Microsoft Office Outlook | CVE-2023-35311 | 8.8 | CVSS:3.1/AV:N/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H/E:F/RL:O/RC:C | Exploitation Detected | Yes | No | No |
| Windows VOLSNAP.SYS | CVE-2023-35312 | 7.3 | CVSS:3.1/AV:L/AC:L/PR:L/UI:R/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation More Likely | Yes | No | No |
| Windows Online Certificate Status Protocol (OCSP) SnapIn | CVE-2023-35313 | 6.7 | CVSS:3.1/AV:L/AC:L/PR:H/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Windows Remote Procedure Call | CVE-2023-35314 | 5.3 | CVSS:3.1/AV:N/AC:H/PR:L/UI:N/S:U/C:N/I:N/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | No | No | No |
| Windows Layer-2 Bridge Network Driver | CVE-2023-35315 | 8.8 | CVSS:3.1/AV:A/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Windows Remote Procedure Call | CVE-2023-35316 | 6.5 | CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:N/A:N/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Windows Server Update Service | CVE-2023-35317 | 7.8 | CVSS:3.1/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Windows Remote Procedure Call | CVE-2023-35318 | 6.5 | CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:N/I:N/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | No | No | No |
| Windows Remote Procedure Call | CVE-2023-35319 | 6.5 | CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:N/I:N/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | No | No | No |
| Windows Connected User Experiences and Telemetry | CVE-2023-35320 | 7.8 | CVSS:3.1/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Windows Deployment Services | CVE-2023-35321 | 6.5 | CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:N/I:N/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | No | No | No |
| Windows Deployment Services | CVE-2023-35322 | 8.8 | CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Windows Online Certificate Status Protocol (OCSP) SnapIn | CVE-2023-35323 | 7.8 | CVSS:3.1/AV:L/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Microsoft Printer Drivers | CVE-2023-35324 | 5.5 | CVSS:3.1/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:N/A:N/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Windows Print Spooler Components | CVE-2023-35325 | 7.5 | CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:N/A:N/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Windows CDP User Components | CVE-2023-35326 | 5.5 | CVSS:3.1/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:N/A:N/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Windows Transaction Manager | CVE-2023-35328 | 7.8 | CVSS:3.1/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Windows Authentication Methods | CVE-2023-35329 | 6.5 | CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:N/I:N/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | No | No | No |
| Windows SPNEGO Extended Negotiation | CVE-2023-35330 | 6.2 | CVSS:3.1/AV:L/AC:L/PR:N/UI:N/S:U/C:N/I:N/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | No | No | No |
| Windows Local Security Authority (LSA) | CVE-2023-35331 | 6.5 | CVSS:3.1/AV:A/AC:L/PR:N/UI:N/S:U/C:N/I:N/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Windows Remote Desktop | CVE-2023-35332 | 6.8 | CVSS:3.1/AV:N/AC:H/PR:N/UI:R/S:U/C:H/I:H/A:N/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Microsoft Media-Wiki Extensions | CVE-2023-35333 | 7.1 | CVSS:3.1/AV:N/AC:H/PR:L/UI:R/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Microsoft Dynamics | CVE-2023-35335 | 8.2 | CVSS:3.1/AV:N/AC:L/PR:N/UI:R/S:C/C:H/I:L/A:N/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Windows MSHTML Platform | CVE-2023-35336 | 6.5 | CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:N/I:L/A:L/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Windows Win32K | CVE-2023-35337 | 7.8 | CVSS:3.1/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Windows Peer Name Resolution Protocol | CVE-2023-35338 | 7.5 | CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:N/I:N/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | No | No | No |
| Windows CryptoAPI | CVE-2023-35339 | 7.5 | CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:N/I:N/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | No | No | No |
| Windows CNG Key Isolation Service | CVE-2023-35340 | 7.8 | CVSS:3.1/AV:L/AC:H/PR:L/UI:N/S:C/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Windows Media | CVE-2023-35341 | 6.2 | CVSS:3.1/AV:L/AC:L/PR:N/UI:N/S:U/C:H/I:N/A:N/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Windows Image Acquisition | CVE-2023-35342 | 7.8 | CVSS:3.1/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Windows Geolocation Service | CVE-2023-35343 | 7.8 | CVSS:3.1/AV:L/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Role: DNS Server | CVE-2023-35344 | 6.6 | CVSS:3.1/AV:N/AC:H/PR:H/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Role: DNS Server | CVE-2023-35345 | 6.6 | CVSS:3.1/AV:N/AC:H/PR:H/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Role: DNS Server | CVE-2023-35346 | 6.6 | CVSS:3.1/AV:N/AC:H/PR:H/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Windows App Store | CVE-2023-35347 | 7.1 | CVSS:3.1/AV:L/AC:L/PR:L/UI:N/S:U/C:N/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Azure Active Directory | CVE-2023-35348 | 7.5 | CVSS:3.1/AV:L/AC:H/PR:H/UI:N/S:C/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Windows Active Directory Certificate Services | CVE-2023-35350 | 7.2 | CVSS:3.1/AV:N/AC:L/PR:H/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Windows Active Directory Certificate Services | CVE-2023-35351 | 6.6 | CVSS:3.1/AV:N/AC:H/PR:H/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Windows Remote Desktop | CVE-2023-35352 | 7.5 | CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:N/I:H/A:N/E:U/RL:O/RC:C | Exploitation More Likely | Yes | No | No |
| Windows Connected User Experiences and Telemetry | CVE-2023-35353 | 7.8 | CVSS:3.1/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Windows Kernel | CVE-2023-35356 | 7.8 | CVSS:3.1/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Windows Kernel | CVE-2023-35357 | 7.8 | CVSS:3.1/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Windows Kernel | CVE-2023-35358 | 7.8 | CVSS:3.1/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Windows NT OS Kernel | CVE-2023-35360 | 7.0 | CVSS:3.1/AV:L/AC:H/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Windows NT OS Kernel | CVE-2023-35361 | 7.0 | CVSS:3.1/AV:L/AC:H/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Windows Clip Service | CVE-2023-35362 | 7.8 | CVSS:3.1/AV:L/AC:H/PR:L/UI:N/S:C/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Windows Kernel | CVE-2023-35363 | 7.8 | CVSS:3.1/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Windows NT OS Kernel | CVE-2023-35364 | 8.8 | CVSS:3.1/AV:L/AC:L/PR:L/UI:N/S:C/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Windows Routing and Remote Access Service (RRAS) | CVE-2023-35365 | 9.8 | CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | Yes |
| Windows Routing and Remote Access Service (RRAS) | CVE-2023-35366 | 9.8 | CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | Yes |
| Windows Routing and Remote Access Service (RRAS) | CVE-2023-35367 | 9.8 | CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | Yes |
| Mono Authenticode | CVE-2023-35373 | 5.3 | CVSS:3.1/AV:N/AC:H/PR:L/UI:N/S:U/C:H/I:N/A:N/E:P/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Paint 3D | CVE-2023-35374 | 7.8 | CVSS:3.1/AV:L/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Visual Studio Code | CVE-2023-36867 | 7.8 | CVSS:3.1/AV:L/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H/E:P/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Service Fabric | CVE-2023-36868 | 6.5 | CVSS:3.1/AV:A/AC:L/PR:N/UI:N/S:U/C:H/I:N/A:N/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Azure Active Directory | CVE-2023-36871 | 6.5 | CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:N/I:H/A:N/E:F/RL:O/RC:C | Yes | No | No | |
| Microsoft Windows Codecs Library | CVE-2023-36872 | 5.5 | CVSS:3.1/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:N/A:N/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Windows Error Reporting | CVE-2023-36874 | 7.8 | CVSS:3.1/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Detected | Yes | No | No |
| Microsoft Office | CVE-2023-36884 | 8.3 | CVSS:3.1/AV:N/AC:H/PR:N/UI:R/S:C/C:H/I:H/A:H/E:F/RL:U/RC:C | Exploitation Detected | No | No | Yes |
Microsoft Office is especially among the apps affected. If you remember, Microsoft Teams is particularly vulnerable to a lot of attacks. A team of researchers found out that Teams is prone to modern malware attacks that could massively disrupt organizations that use it.
So while Microsoft has said that the vulnerabilities addressed by the team were not critical, it’s still good to see that the Redmond-based tech giant is releasing updates to improve security on Teams.
Have you found any other issues after installing this month’s security updates? Share your opinion in the comments section below.