Hackers say Microsoft can't revoke leaked Secure Boot policies
3 min. read
Published on
Read our disclosure page to find out how can you help Windows Report sustain the editorial team Read more
Back in July, we reported that Microsoft had managed to fix a major security vulnerability that would have allowed hackers to unlock Windows RT tablets and run non-Windows operating systems. According to recent reports, it appears the security patch wasn’t that successful, with the vulnerability still able to be exploited.
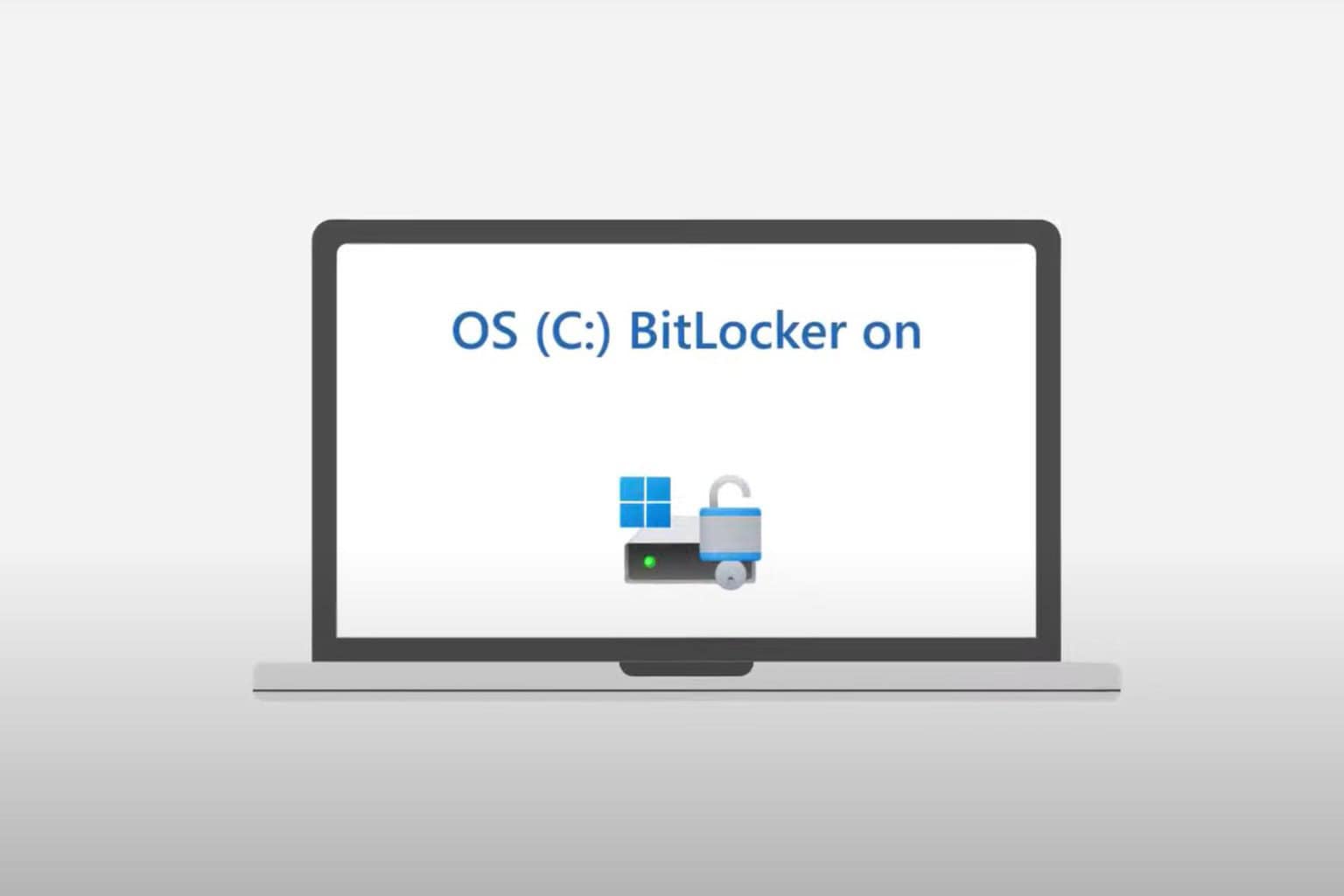
Microsoft’s firmware incorporates a feature called Secure Boot which allows devices to only boot up operating systems cryptographically signed by the tech giant. The Secure Boot feature is activated during early startup by the Windows boot manager. But there is a way to disable Secure Boot check using a special policy known as “the golden backdoor key”. If users manage to get their hands on this policy and install it on their devices, then the Windows boot manager will boot any operating system they want.
The tech giant is desperately trying to patch this vulnerability, but some hackers say it’s impossible for Microsoft to invalidate the leaked keys.
[…] Either way, it’d be impossible in practice for MS to revoke every bootmgr earlier than a certain point, as they’d break install media, recovery partitions, backups, etc.
This major vulnerability also revives the debate around the secure golden key feature started by intelligence and security services. Long story short, security services have long pushed software giants to implement a secure golden key system that could grant investigators full access to user computers. But such universal keys can easily fall into the wrong hands, as ethical hackers warn:
A backdoor, which MS put in to secure boot because they decided to not let the user turn it off in certain devices, allows for secure boot to be disabled everywhere! You can see the irony. Also the irony in that MS themselves provided us several nice “golden keys” (as the FBI would say 😉 for us to use for that purpose 🙂 About the FBI: are you reading this? If you are, then this is a perfect real world example about why your idea of backdooring cryptosystems with a “secure golden key” is very bad! […] You seriously don’t understand still? Microsoft implemented a “secure golden key” system. And the golden keys got released from MS own stupidity. Now, what happens if you tell everyone to make a “secure golden key” system?
For the time being, Microsoft is silent as always and has yet to issue any comment on this matter.
The entire report published by the two white hat hackers who investigated this vulnerability is available online.
RELATED STORIES YOU NEED TO CHECK OUT:
- Hackers send emails to Windows users pretending to be from Microsoft’s Support Team
- Windows XP is now a Very Easy Target for Hackers, Windows 10 Update is Mandatory