Intel and Microsoft share vital mitigations for the CVE-2022-0001 vulnerability
The vulnerability affects a wide array of Intel CPUs

In March‘24, researchers discovered a Branch History Injection (BHI) vulnerability, CVE-2022-0001, in Intel CPUs where attackers could manipulate the branch history. This exposed critical information on the device.
As per Intel’s official website, the vulnerability can be described as,
Branch History Injection (BHI) describes a specific form of intra-mode BTI, where an attacker may manipulate branch history before transitioning from user to supervisor or guest to VMX root mode in an effort to cause an indirect branch predictor to select a specific predictor entry for an indirect branch, and a disclosure gadget at the predicted target will transiently execute. This may be possible since the relevant branch history may contain branches taken in previous security contexts, and in particular, in other predictor modes.
The CVE-2022-0001 vulnerability in Intel CPUs was a major security threat, given the large number of affected processors. Subsequently, mitigations had to be quickly shared to minimize the damage!
Microsoft and Intel share mitigations to counter CVE-2022-0001
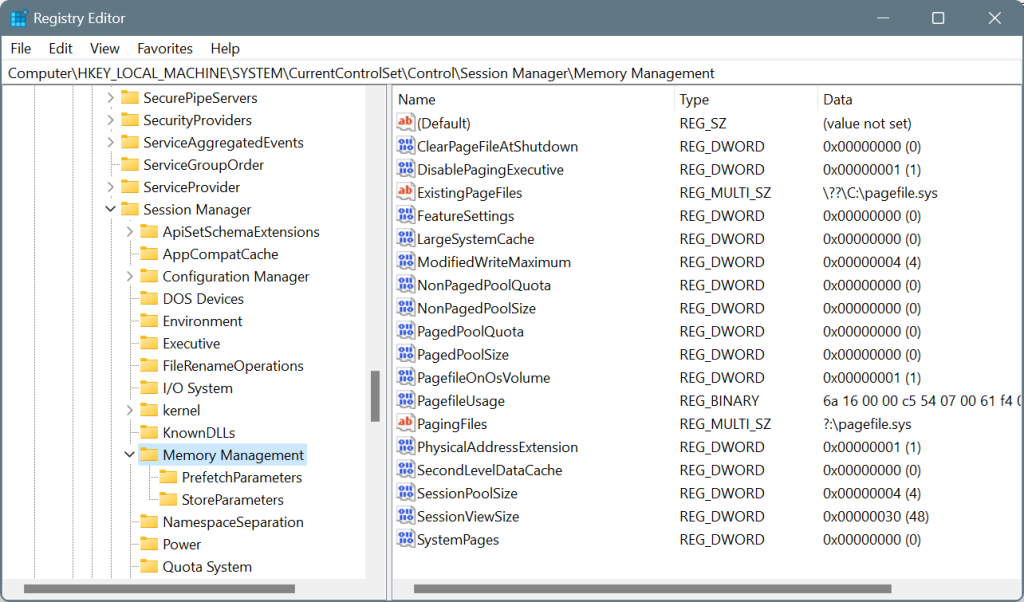
Microsoft, on its part, recommends modifying the Registry to eliminate the risks posed by the Branch History Injection vulnerability. On the dedicated vulnerability page, it suggests the following changes:
reg add “HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\Session Manager\Memory Management” /v FeatureSettingsOverride /t REG_DWORD /d 0x00800000 /f
reg add “HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\Session Manager\Memory Management” /v FeatureSettingsOverrideMask /t REG_DWORD /d 0x00000003 /f
Remember, these are to be manually applied only to Windows devices running Intel processors. Also, back up the Registry before making the changes. Or, in case things go wrong, you can always undo changes to the Registry or even restore the Registry without a backup.
These mitigations may also affect the performance but are your best bet until Microsoft or Intel discovers a more viable solution for CVE-2022-0001.
As for the CPU manufacturer, Intel has shared mitigations on the official website to protect the branch history. Intel also states that its future processors may contain mitigations for CVE-2022-0001 on the hardware level, and you won’t have to manually enforce them!
We recommend all users make the changes recommended by Intel and Microsoft as the Branch History Injection vulnerability poses a great risk on unprotected systems. There’s no way around it!
Such vulnerabilities arise from time to time, and a fix is shared soon. For instance, another recent vulnerability, Rust CVE-2024-24576, allowed hackers to quickly gain access to your systems. To counter this, you had to update the Rust storage library to version 1.77.2.
If you face any problems enforcing the mitigations, let us know in the comments section.
Read our disclosure page to find out how can you help Windows Report sustain the editorial team. Read more






User forum
0 messages