Microsoft announces VBS Enclaves, a new and better way to protect apps from being hacked
The enclaves are based on virtualization-based security.
3 min. read
Published on
Read our disclosure page to find out how can you help Windows Report sustain the editorial team Read more
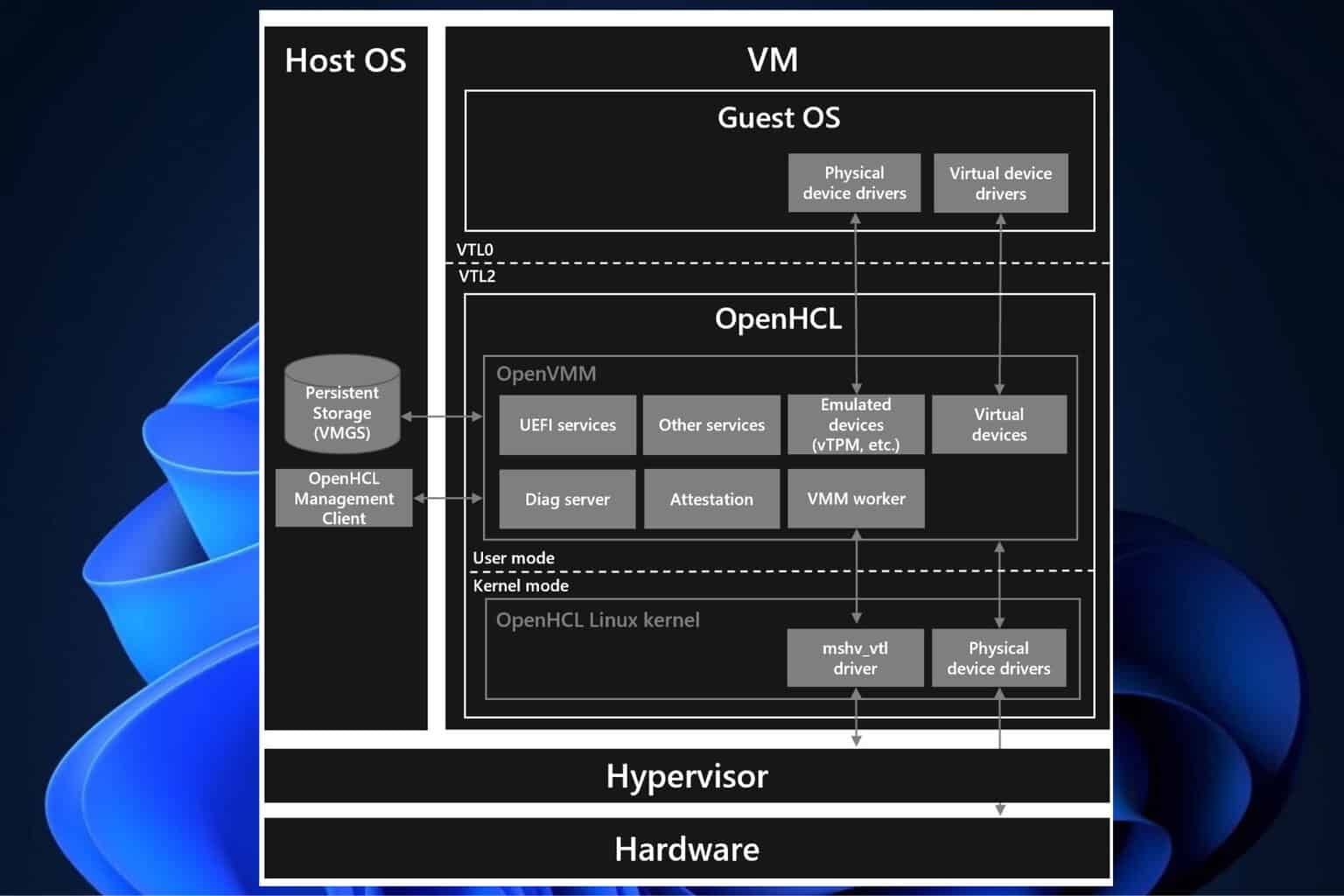
Microsoft has introduced a new security capability in Windows 11 called VBS Enclave. Based on virtualization-based security (VBS), this characteristic intends to provide more safeguarding, particularly for third-party applications.
VBS Enclaves can be seen as a kind of Dynamic Link Library (DLL) file that protects important operations and secrets in an application’s memory space. Here’s how it works.
According to the official announcement, the VBS Enclave creates a Trusted Execution Environment (TEE) inside the host application. This environment isolates crucial parts of the program to protect them from outside dangers.
A VBS enclave is a software-based trusted execution environment (TEE) inside a host application. This is a revolutionary change in our security model for the application, allowing an app to protect its secrets using the power of VBS, from admin-level attacks.
Microsoft
The isolation occurs by utilizing Virtual Trust Levels (VTLs), and the enclave operates at an elevated privilege level that cannot be reached in a normal operating environment. It’s similar to having a secure room built into your application where you can keep your important data safe from being seen by others who might want to look at it without permission.
The Windows Hyper-V hypervisor, which creates this separate and special space called VTL1, makes all of this possible. It’s different from the normal Windows environment we use daily – VTL0. Anything inside VTL1 stays safe because it’s not affected by lower privilege levels. It’s a fancy method to hide the good parts, making the application work normally.
As for the prerequisites, there are some things you need to do before you can use VBS Enclaves. First, your device should have VBS/HVCI enabled (the default setting in Windows 11 and later). Second, make sure that the operating system on it is running Windows 11 or later versions; alternatively, if using a server computer, then choose Windows Server 2019 onwards as well.
Last but not least important – Microsoft has shared details about creating their own VBS enclave via a webpage, providing information that will help developers better protect their apps by utilizing this technology.
In this age of digital systems, the need for security is very high. Threats from cyberspace are becoming more advanced and clever, so having an extra layer can help stop them. Developers can make applications that provide users peace of mind, knowing their data is protected. For others, it means confidence that their daily applications are working hard to keep their information secure.
Microsoft’s start of VBS Enclaves is a big move forward in cybersecurity. It gives an application its safe area where important data and functions can be kept away from dangers outside. This offers more security to those who create and use the application.


User forum
0 messages