Microsoft source codes for Bing and Cortana stolen by the LAPSU$ group
3 min. read
Updated on
Read our disclosure page to find out how can you help Windows Report sustain the editorial team Read more
Key notes
- Microsoft has confirmed that it has indeed been hacked by the known cybercriminals group.
- The infamous LAPSU$ hacking group could have stolen source code for Cortana, and Bing.
- This information has first surfaced over Twitter, where some screenshots were published.
- There is currently an ongoing investigation and efforts are being made to prevent such attacks.

Supposedly, this hack is actually linked to the LAPSU$ group, which also conducted attacks on major companies such as Nvidia, Samsung, and Vodafone.
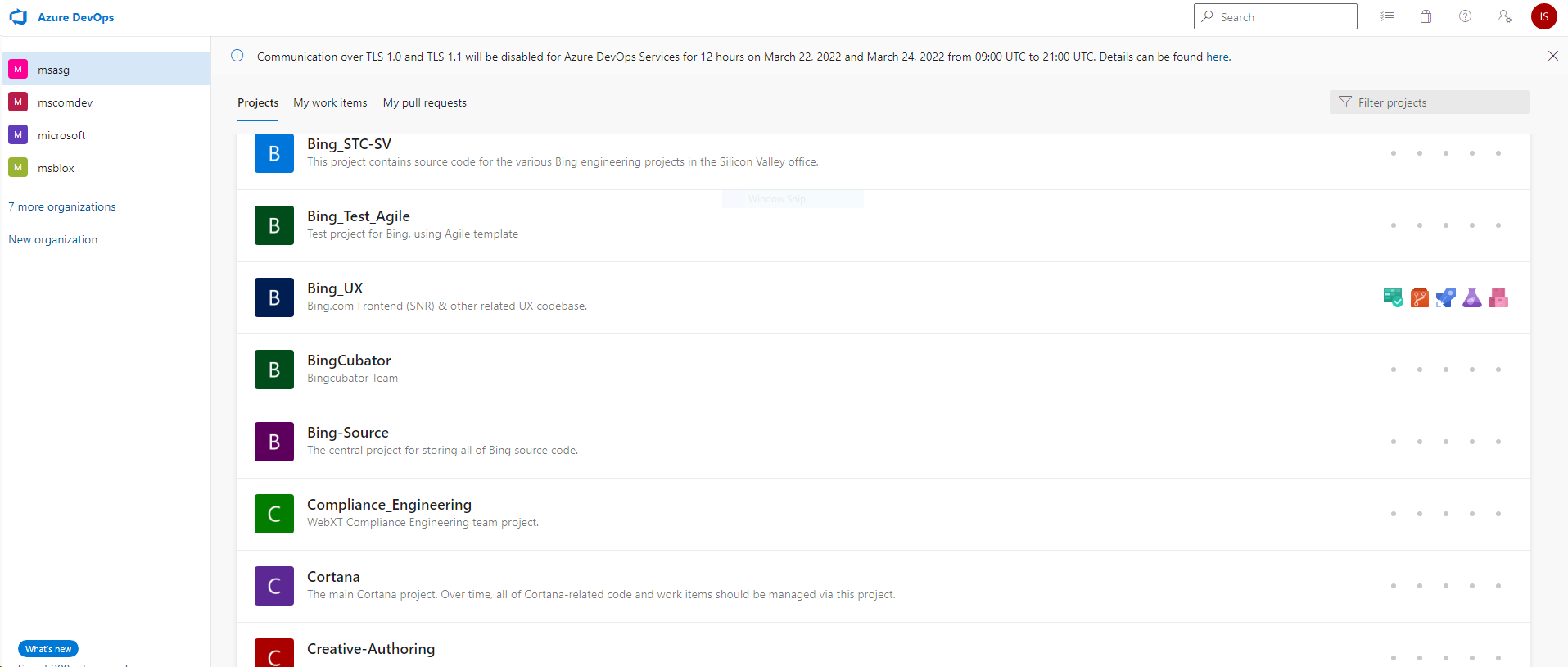
Evidence of what transpired was published on Twitter, in the form of screenshots showing a Telegram conversation and what appears to be an internal folder listing of Microsoft source code repositories.
The above-mentioned pictures indicate that the cybercriminals downloaded source codes of Cortana and several Bing services.
Microsoft unable to protect its own source code
UPDATE: Microsoft confirms the attack and says that the LAPSU$ group has expanded its scope in recent times to target a large number of corporate and individual entities all across the globe.
It normally utilizes phone-based social engineering, SIM-swapping, and bribing employees to gain access to multi-factor authentication (MFA) systems and internal systems.
Some of their other methods also include deploying password stealers, analyzing public code repositories to spot rogue credentials, and purchasing credentials from criminal forums.
You can think of the LAPSU$ group as a bit different because, unlike most such groups, this one tries to get a ransom for downloaded data from the companies that it attacked.
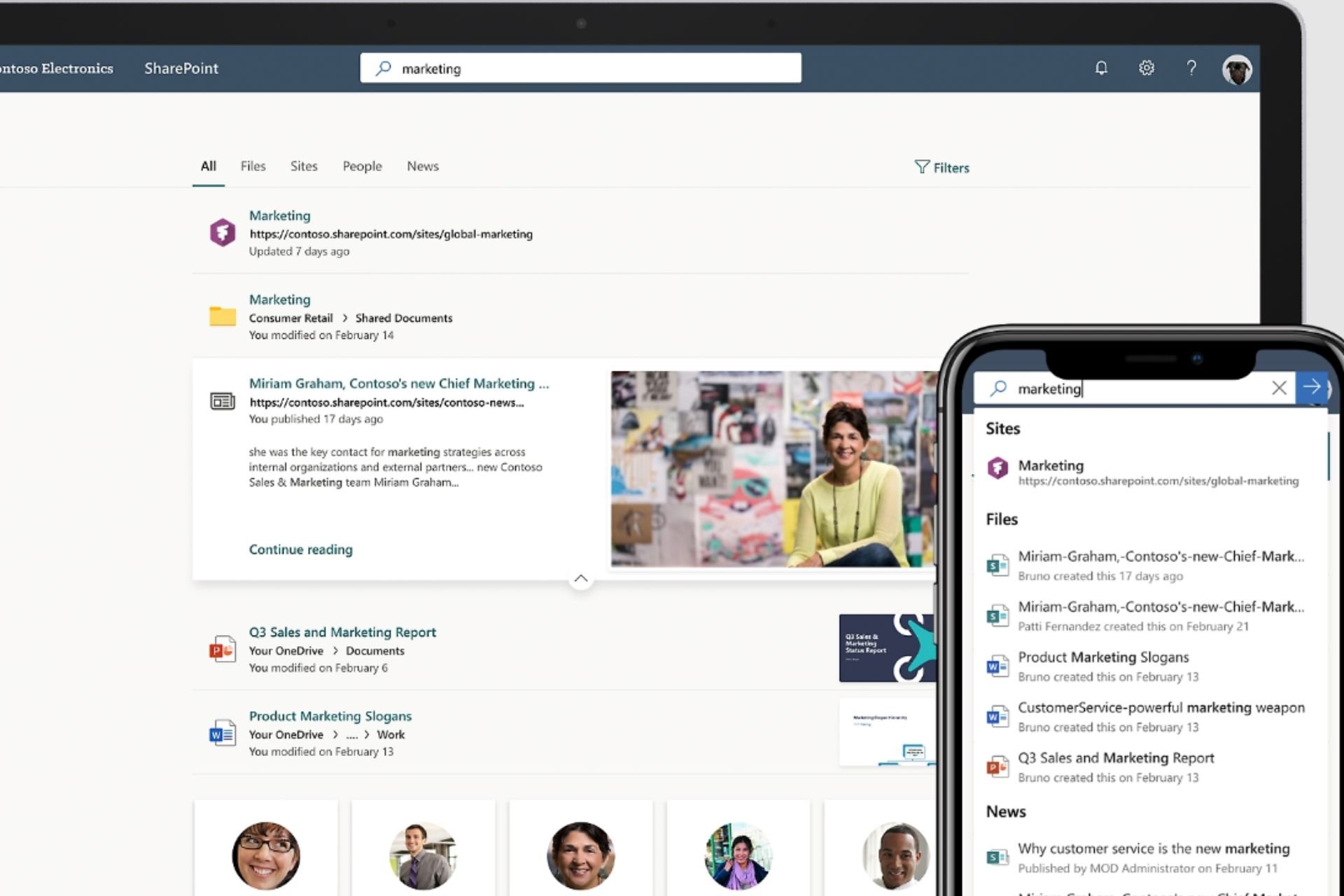
LAPSU$ may have downloaded the source code from what appears to be Bing, Bing Maps, and Cortana.
It is unclear at this point whether the full source codes have been downloaded by the attackers, and whether other Microsoft applications or services are included in the dump.
As source codes may contain valuable information, they can be analyzed for security vulnerabilities that other malicious third parties could exploit.
Also possible is that these source codes include valuable items such as code signing certificates, access tokens, or API keys, which can also be leveraged.
That being said, the Redmond-based tech giant has a development policy in place that actually stops the inclusion of such items.
After learning of what had just transpired, Redmond officials had this to say about it:
The search terms used by the actor indicate the expected focus on attempting to find secrets. Our development policy prohibits secrets in code and we run automated tools to verify compliance.
Even though the evidence is pretty compelling, there is still a lot of uncertainty as to what really happened between Microsoft and LAPSU$.
However, looking back and judging purely based on the hacking group’s track record, it is likely that the reported hack did actually occur.
The question of whether the downloaded data is valuable enough to get a ransom from Microsoft for not publishing it on the Internet is open for debate.
What is your opinion on the matter? Share your thoughts with us in the comments section below.