Microsoft confirms signing Netfilter rootkit malware
Key notes
- G Data security analysts stumbled upon this major issue and brought it to public attention.
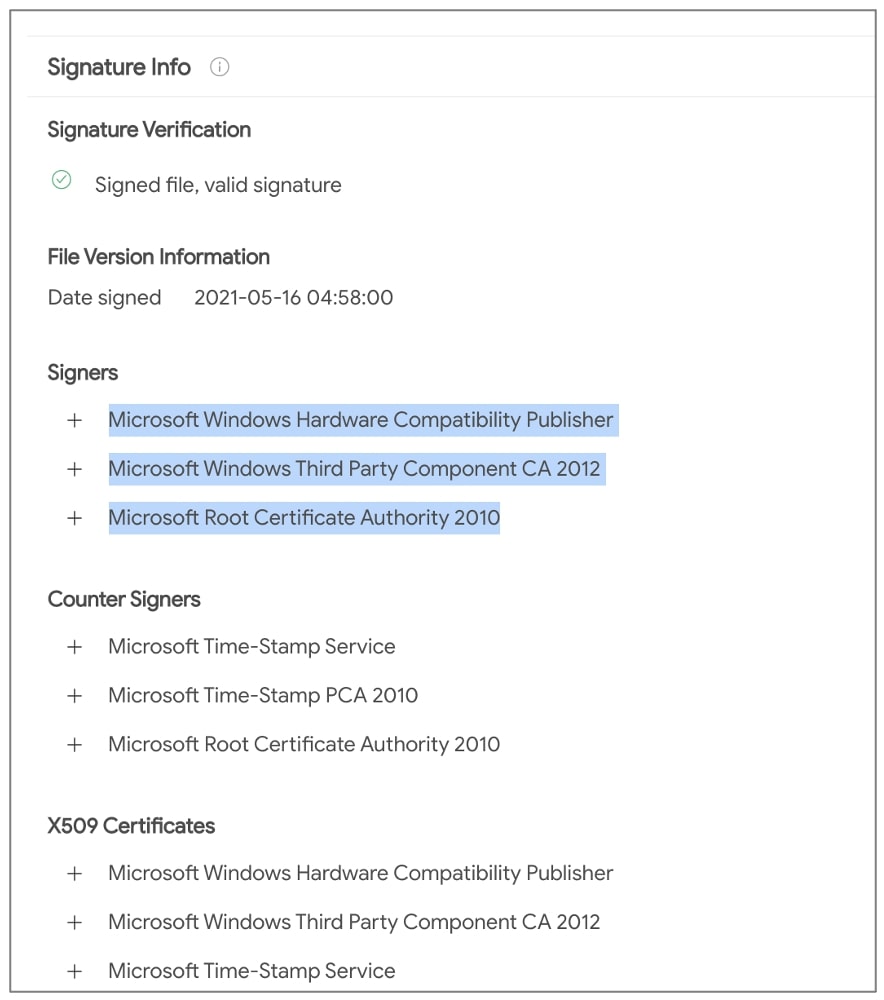
- Microsoft has admitted to having signed the Netfilter driver, which contains rootkit malware.
- The malicious Netfilter driver connects to, belonged to Ningbo Zhuo Zhi Innovation Network Technology Co.
- Microsoft has also refrained from attributing this incident to a specific nation or other third parties yet.

Were you wondering what Microsoft has been up to these days, except preparing Windows 11 for the big release, later this year?
Well, this time the Redmond company really got careless, as they signed a malicious driver, that has been distributed within gaming environments.
These are not rumors anymore, as Microsoft already admitted to this monumental fiasco.
The Netfilter driver is Microsoft’s rootkit
The driver we are talking about, called Netfilter, is actually a rootkit that was monitored while communicating with Chinese command-and-control (C2) IPs.
Analysts from the security firm G Data first noticed this event last week and already started tracing and analyzing the malicious drivers that had Microsoft’s seal on them.
Needless to say that the incident in cause has once again exposed the threats to software supply-chain security, only this time it started from a weakness in Microsoft’s code-signing process.
G Data researchers spent quite some time thoroughly analyzing the driver and have concluded it to be malware. As specified in the blog post, the discoveries they made shook them to their very core.
Worth knowing is that the C2 IP 110.42.4.180 that the malicious Netfilter driver connects to, belonged to Ningbo Zhuo Zhi Innovation Network Technology Co., Ltd.
Microsoft admitted to being guilty in this sensitive matter
According to the tech giant, the threat has been mainly targeting the gaming sector in China with these malicious drivers, but there are no signs of enterprise environments having been affected so far.
Microsoft has also refrained from attributing this incident to a specific nation just yet.
We have suspended the account and reviewed their submissions for additional signs of malware.
If you didn’t already know, falsely signed binaries can be continuously abused by sophisticated third parties in order to facilitate large scale software supply chain attacks.
The worst thing for Microsoft is that this incident has exposed weaknesses in a legitimate code-signing process, exploited by malicious third parties in order to acquire Microsoft-signed code without compromising any certificates.
We will keep an eye out for any developments in this story and keep you updated.
Read our disclosure page to find out how can you help Windows Report sustain the editorial team. Read more







User forum
0 messages