Nasty Office bug fixed with the September 2021 Patch Tuesday
4 min. read
Updated on
Read our disclosure page to find out how can you help Windows Report sustain the editorial team Read more
Key notes
- This month’s Patch Tuesday event brings users everywhere a total of 67 fixes.
- Almost half of the patches released tackle user privilege issues on a computer.
- Executing arbitrary code on a victim’s computer is also a problem fixed now.
- The MSHTML component of Microsoft Office is also being actively exploited.
The Redmond company’s regular clutch of updates takes on the greatest importance this month as the company releases a fix for a critical-severity bug.
This is currently being referred to by its vulnerability designation reference, CVE-2021-40444.
We also know that it is currently being exploited, in Office documents, as well as significant patches for Microsoft products and cloud services.
Microsoft fixes security breaches via Patch Tuesday
During this month’s Patch Tuesday event, Microsoft released a total of 67 fixes for many of its products.
The largest number of fixes, which is 27, was to repair problems that an attacker might use to raise their own privilege level on a computer.
If you were wondering about the second-largest number, which in this case is 14, address the ability of an attacker to execute arbitrary code on a victim’s computer.
It’s important to know that all but one of the critical vulnerabilities fall into the Remote Code Execution category.
This includes the -40444 bug, which was nicknamed the Microsoft MSHTML Remote Code Execution Vulnerability.
The non-RCE critical vulnerability is an information disclosure bug that affects Azure Sphere (CVE-2021-36956), a platform Microsoft created, that is intended to add a security layer to Internet-of-Things (IoT) devices.
Some of the nasty bugs affecting the Edge browser on both the Android and iOS platforms were also fixed by the tech giant.
Users of that browser on those devices will, necessarily, have to obtain their fixed versions from the relevant app store for their device, both of which are subject to a vulnerability that Microsoft describes as spoofing.
The critical vulnerabilities affecting Windows itself (CVE-2021-36965 and CVE-2021-26435) apply to a component called the WLAN AutoConfig Service.
If you didn’t know, this is part of the mechanism that Windows 10 uses to choose the wireless network a computer will connect to, and to the Windows Scripting Engine, respectively.
Microsoft provided no additional information prior to the Patch Tuesday release deadline about the mechanism by which these bugs execute code on a system.
Redmond developers tackle huge Office bug this month
After this bug was discovered and became public knowledge on September 7, security researchers and analysts began swapping proof-of-concept examples of how an attacker might leverage the exploit.
Unfortunately, the high profile of this bug means that attackers will have taken notice and are likely to begin exploiting the vulnerability.
This nasty bug involves the MSHTML component of Microsoft Office, which can render browser pages in the context of an Office document.
In the exploitation of the bug, an attacker creates a maliciously-crafted ActiveX control and then embeds code into an Office document that calls the ActiveX control when the document gets opened or previewed.
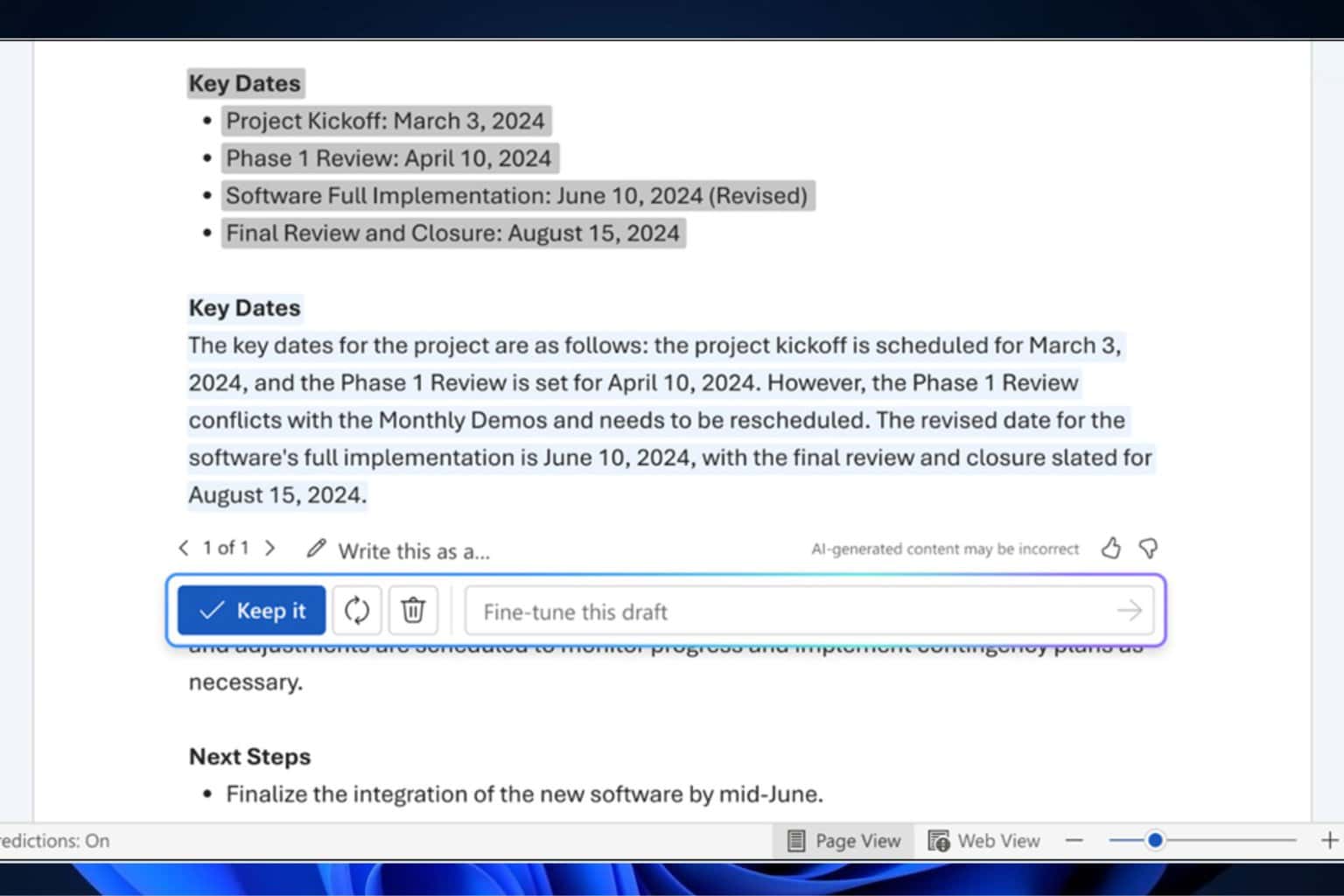
The stages of the attack are, in general terms:
- Target receives a .docx or .rtf Office document and opens it
- The document pulls down remote HTML from a malicious web address
- The malicious website delivers a .CAB archive to the target’s computer
- The exploit launches an executable from inside the .CAB (usually named with a .INF extension)
The malicious scripting uses the built-in handler for .cpl files (Windows Control Panel) in order to run the file with a .inf extension (which is actually a malicious .dll) extracted from the .cab file.
A lot of people have not only crafted functional proof-of-concept (PoC) exploits, but a few have created and published builder tools that anyone can use to weaponize an Office document.
The original version of the exploit used Microsoft Word .docx documents, but we’ve already spotted some versions that use .rtf file extensions.
Attackers use the techniques not only to launch .exe files but also malicious .dll files, using rundll32. There’s no reason to believe the exploit won’t expand their range to other Office document types, as well.
It’s good to know that Redmond officials are doing the best they can to keep us safe, but this is all about a common effort, so we also have to do our parts.
What are your thoughts on this month’s Patch Tuesday updates? Share your opinion with us in the comments section below.