Beware! Nobelium phishing attack is after your personal data
3 min. read
Published on
Read our disclosure page to find out how can you help Windows Report sustain the editorial team Read more
Key notes
- Microsoft has issued a new cyber-attack warning that involves the Nobelium hacker group.
- Attack attempts are now more credible, as the malicious party uses a former USAID account.
- More than 3000 accounts that are linked to government and non-government agencies have been already attacked.
- Microsoft's Tom Burt has explained exactly how this phishing scheme works against its victims.

Microsoft has issued a serious warning concerning cybersecurity for everyone out there, as attack levels have begun to spike once again.
The Russian-backed group Nobelium is at it again and, this time, the tactics they employed could fool even the most vigilant of observers.
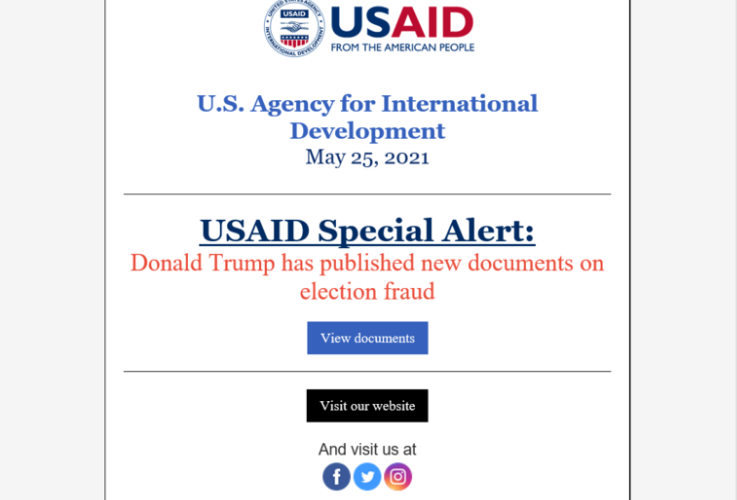
Nobelium is using a hacked USAID account for phishing
As we mentioned above, the Russian hackers have now gotten their hands on a Constant Contact email marketing platform formerly used by USAID, in order to conduct their shady business.
Estimations show that more than 3000 accounts that are linked to government agencies, consultants, think tanks, as well as other non-governmental organizations, were targeted by this phishing scheme.
And even though most of Nobelium’s efforts were concentrated mostly on the US, it seems that the malicious content reached more than 24 countries, according to Microsoft.
Tom Burt, the vice president of customer security and trust from Microsoft, explained how the Native Zone malware was inserted into victim’s computers.
Nobelium launched this week’s attacks by gaining access to the Constant Contact account of USAID. From there, the actor was able to distribute phishing emails that looked authentic but included a link that, when clicked, inserted a malicious file used to distribute a backdoor we call Native Zone. This backdoor could enable a wide range of activities from stealing data to infecting other computers on a network.
As an attempt to not incriminate Microsoft, by allowing people to think that flaws in the system may have facilitated these attacks, Burton said that many of the emails were blocked, thus vulnerability of any Microsoft products can be ruled out.
How does Nobelium attack its victims?
The email that the hackers send has a link included and, once this link is clicked, its pretty much like handing thieves the keys to your house.
After clicking the above-mentioned link, an ISO is delivered to the machine in question, that contains a decoy document, a shortcut, and a DLL executable with a Cobalt Strike Beacon loader (Native Zone).
When users actually run this shortcut, the DLL is executed and Nobelium has free access to all your data, thus extracting any information they want, and can even deliver additional malware.
This malware distributing campaign was first discovered back in February 2021, by Microsoft, as detailed in the post from the Microsoft Threat Intelligence Center.
Microsoft has kicked it into full gear in the battle against these malicious groups and has enlisted the help of other nations that are willing to stand up and act against cyber oppression, according to Tom Burt.
Microsoft will continue to work with willing governments and the private sector to advance the cause of digital peace.
Remember that the internet is not only cool wallpapers, great music and funny cat videos. Staying protected in this dangerous cyber environment should be everyone’s first concern while online.
We will keep our eyes on this developing story and inform you of any, if any, changes on this matter that may occur. As you may know by now, we cover subjects that involve serious ransomware threats.
Have you ever been a victim of cyber-attacks? Tell us all about it in the comments section below.