Windows 10 Zero-Day vulnerability to be fixed by third-party micropatch
Key notes
- One of Windows 10's zero-day vulnerabilities will finally get fixed.
- 0Patch will deliver an unofficial micropatch to solve the problem.
- The vulnerability targetted here is known as CVE-2021-34484.
- Microsoft is still working on a fix and might deliver it next month.
Microsoft has yet to fully fix a zero-day vulnerability in Windows 10 that gives escalated privileges to successful attackers. However, 0Patch developed an unofficial micropatch that aims to solve the problem.
This bug is known by the tech giant under its alias CVE-2021-34484. Microsoft already issued a fix during August Patch Tuesday earlier this year. According to the company, the flaw is an arbitrary directory-deletion problem.
0Patch is going to fix this Windows vulnerability
Redmond officials deemed this a low priority because a threat actor would need to have local access to exploit a system. Even so, with that access, the attacker would only be able to delete folders.
However, security researcher Abdelhamid Naceri later found that the flaw could also be a gateway to privilege escalation.
This would actually give the threat actor access to system resources, servers, and other parts of a network, although, they would still need local access to start the chain.
He also found that Microsoft’s fix didn’t really work because attackers can bypass it, and 0Patch confirmed this in one of their blog posts.
The vulnerability lies in the User Profile Service, specifically in the code responsible for creating a temporary user profile folder in case the user’s original profile folder is damaged or locked for some reason.
Abdelhamid discovered that the process (executed as Local System) of copying folders and files from the user’s original profile folder to the temporary one can be attacked with symbolic links.

By doing so, malicious third parties would create attacker-writable folders in a system location from which a subsequently launched system process would load and execute the attacker’s DLL.
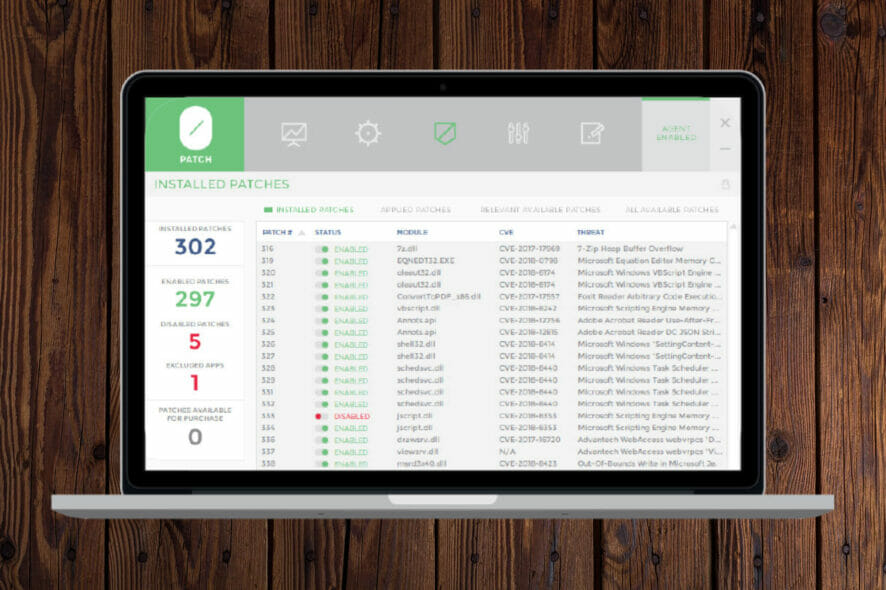
0Patch wrote its own micropatch to cover Microsoft’s tracks and close the vulnerability. The company says the patch protects all affected Windows versions, including 20H2, 2004,1909, and Windows Server 2019.
The Redmond tech giant has not said when it will roll out an official patch, considering it still sees this as a low priority issue because of the local access.
This means that a plausible ETA could be the December Patch Tuesday software rollout.
What’s your take on the entire situation? Share your opinion with us in the comments section below.
Read our disclosure page to find out how can you help Windows Report sustain the editorial team. Read more







User forum
0 messages