How to Find the Source of Active Directory Account Lockouts
Get guided on how you can easily find the lockout source in AD
4 min. read
Updated on
Read our disclosure page to find out how can you help Windows Report sustain the editorial team Read more
Key notes
- Getting information about the lockout source in your Active Directory will help you rectify the problem.
- You can use Windows PowerShell or Group Policy Editor on your PC, but they have limitations.
- Otherwise, you may use our recommended tool to quickly get the job done in no time.
Auditing the Active Directory is very important as it can help you review the access rights to important decisions and also monitor who is creating a new account. By default, Active Directory does not audit all your security events. We have a complete guide on how to install Active Directory on Windows Server.
One of the most common problems that an admin of the Active Directory face is how to identify the source of frequent account lockouts. Thankfully, in this guide, we will give you a detailed solution on how to find the account lockout source in Active Directory.
How can I find the source of Active Directory account lockouts?
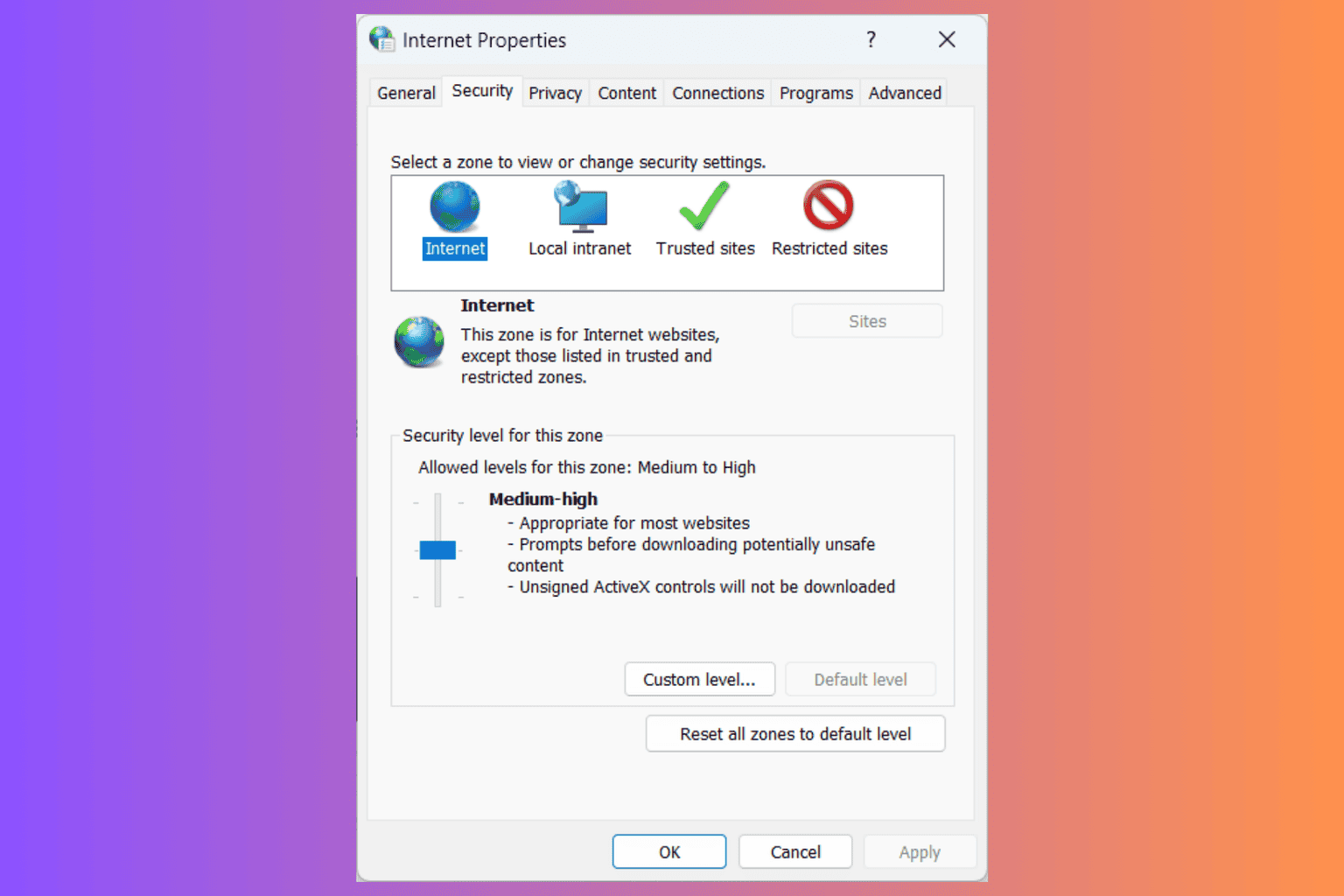
1. Use the Group policy editor
- Login to the domain controller with admin privileges.
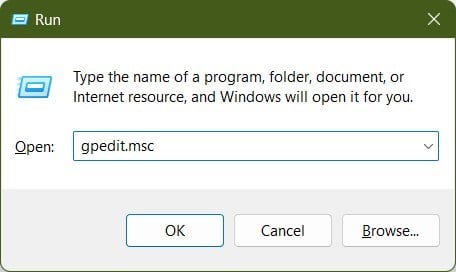
- Press Win + R keys to open the Run dialogue.
- Type gpedit.msc and hit Enter.
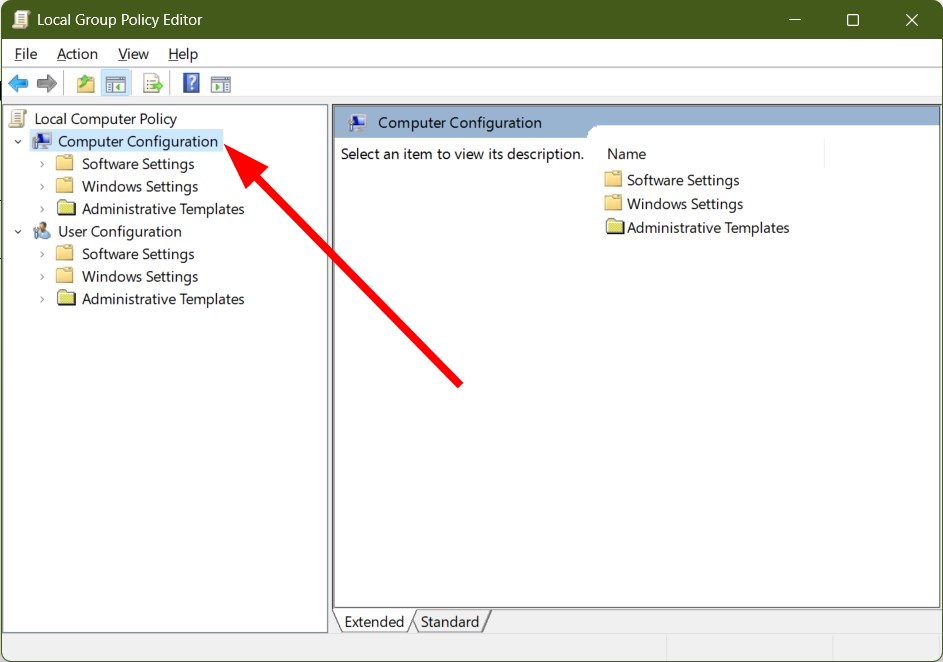
- Expand Computer Configuration.
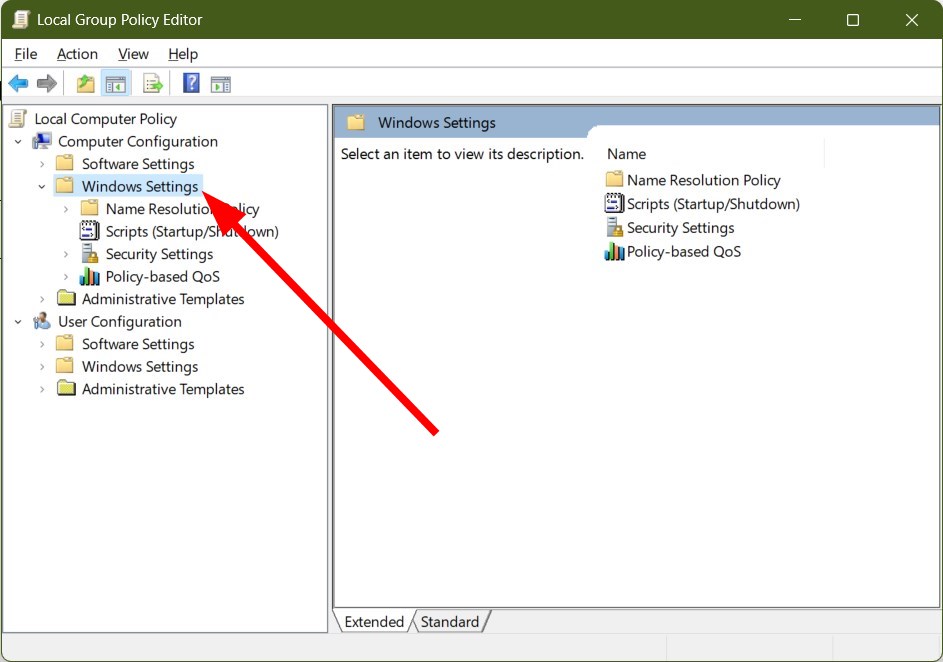
- Select Windows Settings.
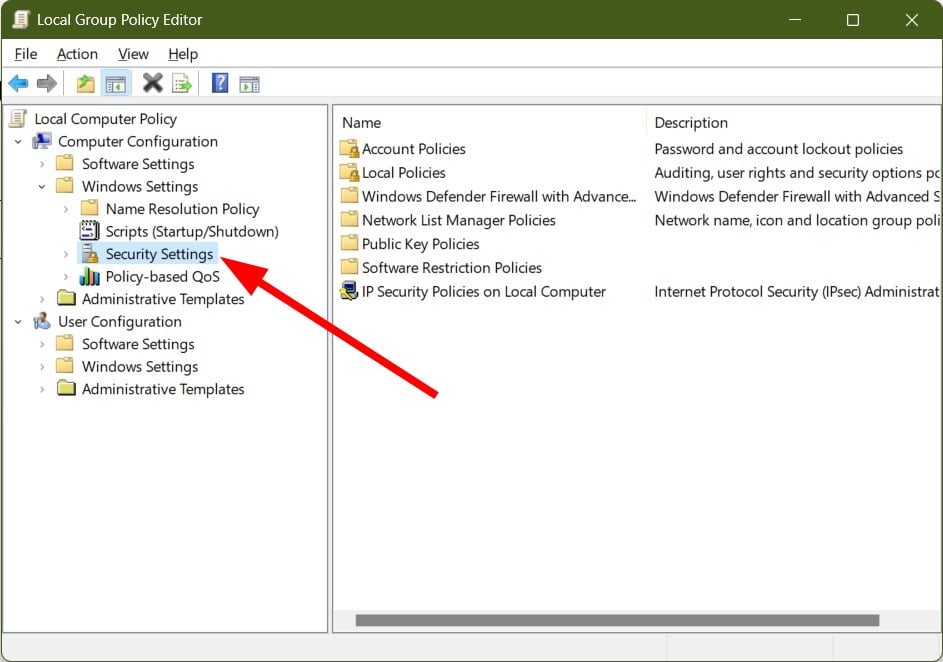
- Expand Security Settings.
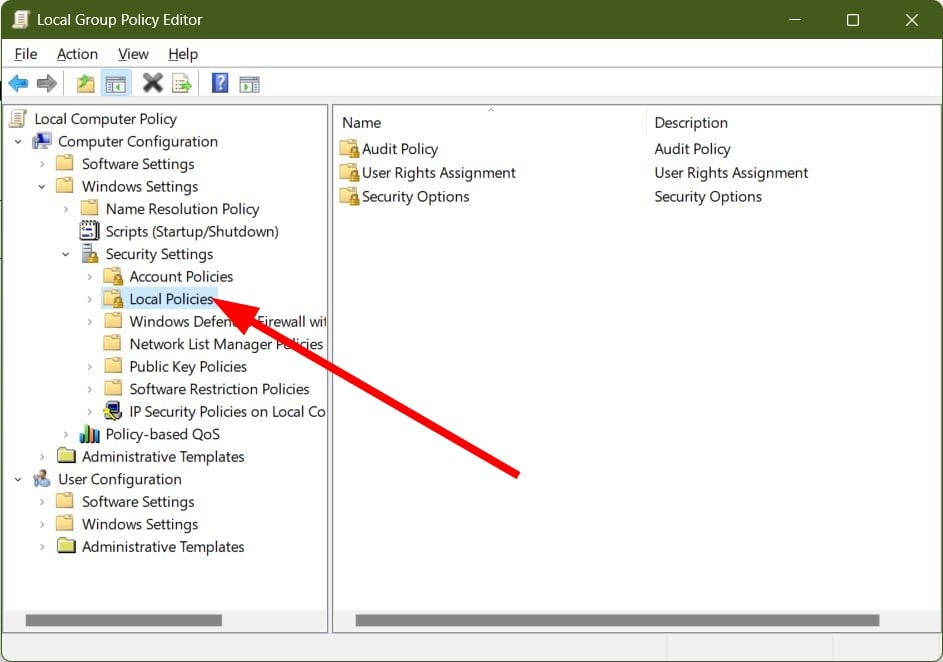
- Choose Local Policies.
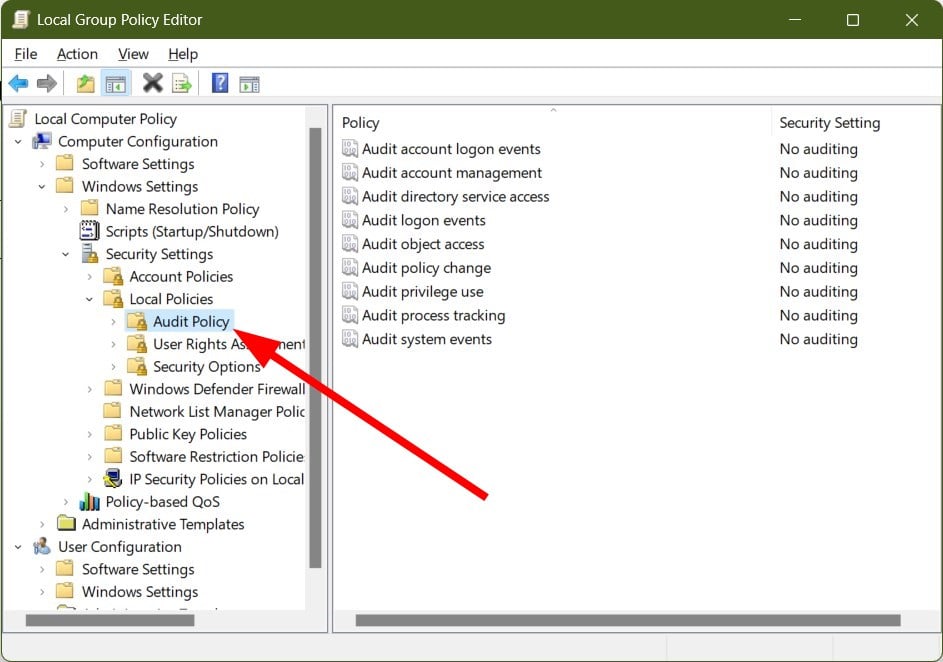
- Click on Audit Policy.
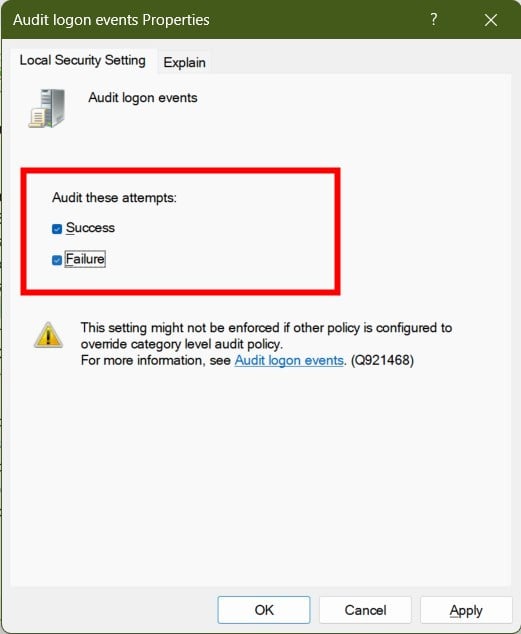
- Open Audit process tracking and check the Success and Failure boxes.
- Click OK.
- Open Audit logon events and check the Success and Failure boxes.
- Click OK.
- Press the Win key to open the Start menu.
- Type Event Viewer and open it.
- Search for the Security log for event ID 4625.
- You will find the source of Active Directory account lockouts.
2. Use Windows PowerShell
- Press the Win key to open the Start menu.
- Search for Windows PowerShell and open it as an admin.
- Type the below command and press Enter to install the PowerShell Active Directory module.
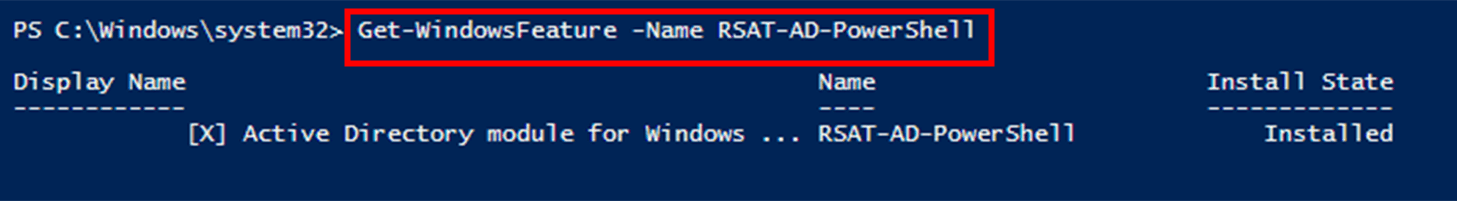
Install-WindowsFeature RSAT-AD-PowerShell - You can verify the installation by running the below command.
Get-WindowsFeature -Name RSAT-AD-PowerShell - Run the below command to find the locked-out user account.
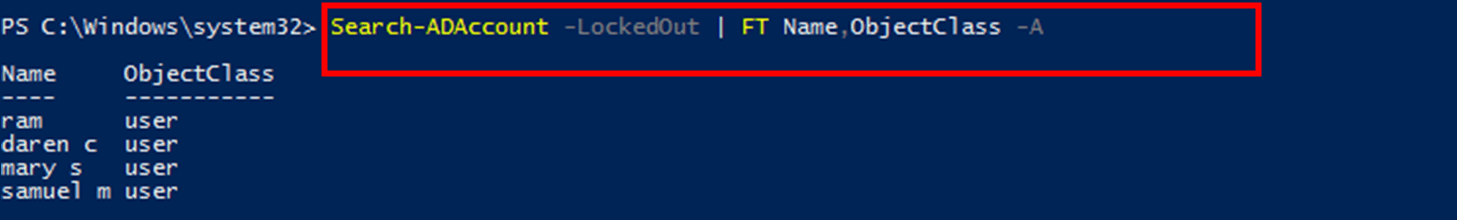
Search-ADAccount -LockedOut | FT Name,ObjectClass -A - You will see a list of locked accounts.
While this method may seem pretty easy as you only have to run a few commands, this process will only give you a list of names of the accounts that are locked out. It won’t give you the exact reason for the lockout.
For that, we would suggest you check out the below solution.
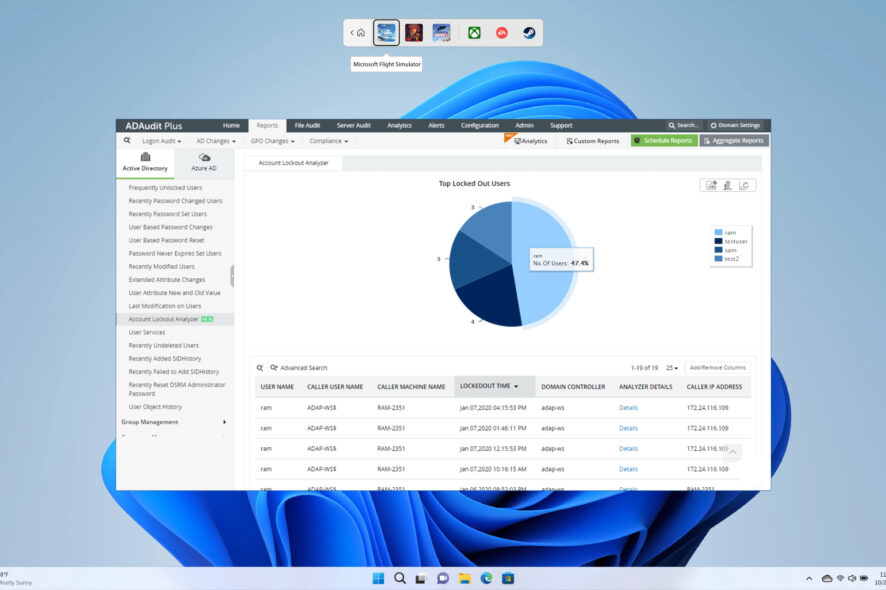
3. Use a dedicated tool
- Download ManageEngine ADAudit Plus.
- Install the program on your PC.
- Launch the program.
- Click on Reports at the top menu bar.
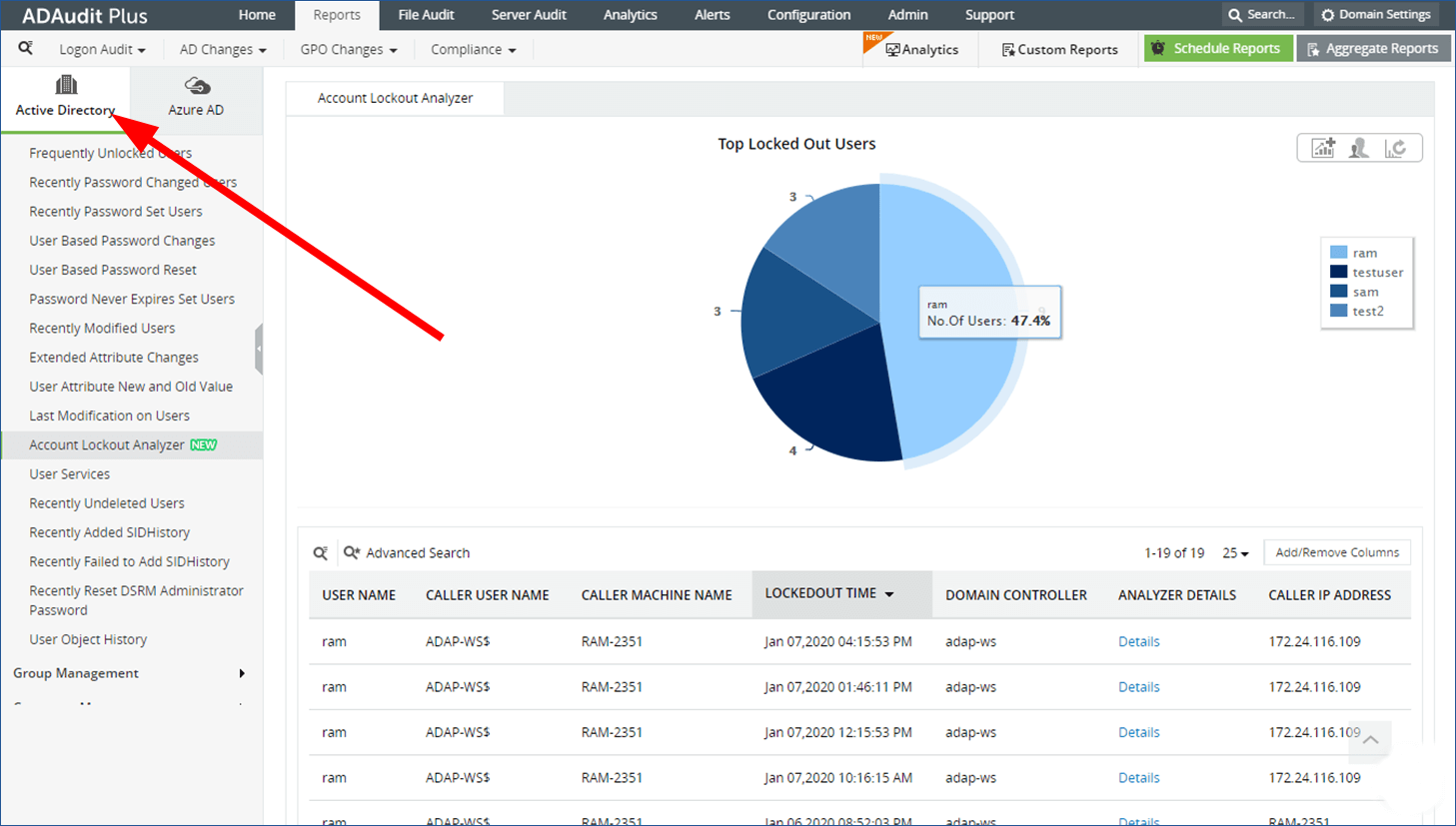
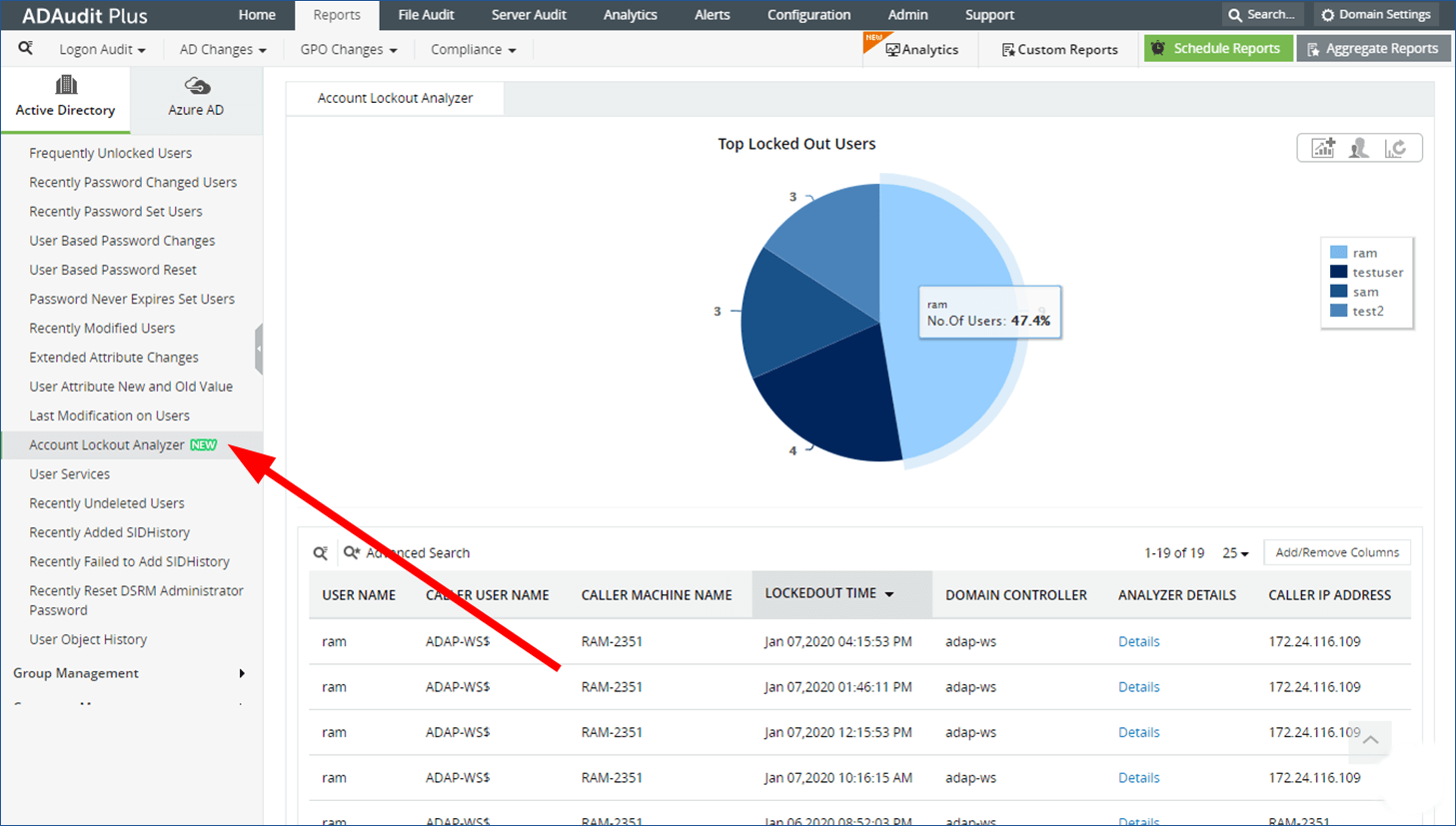
- Select Active Directory.
- Click on User Management.
- Select Account Lockout Analyzer.
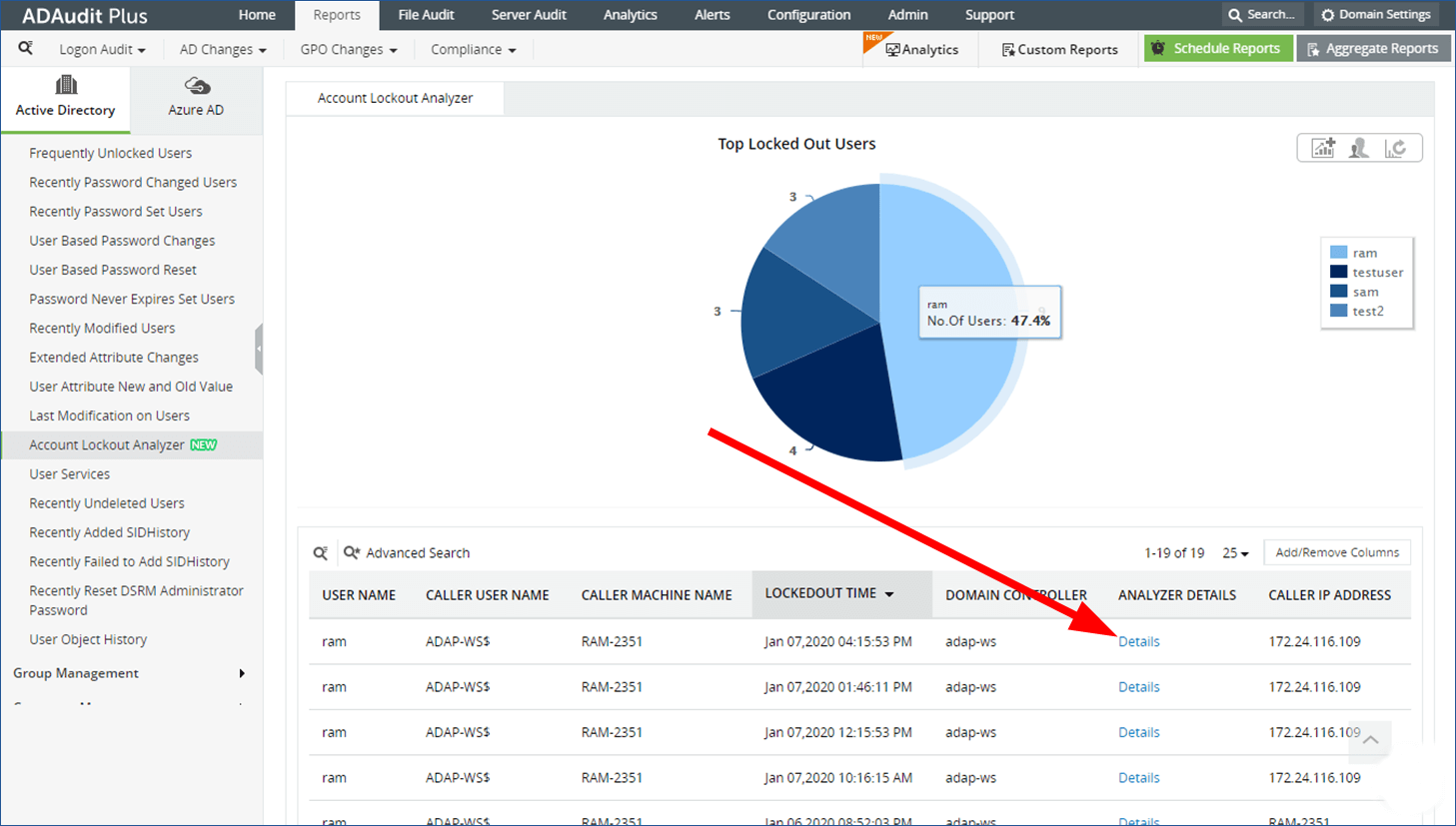
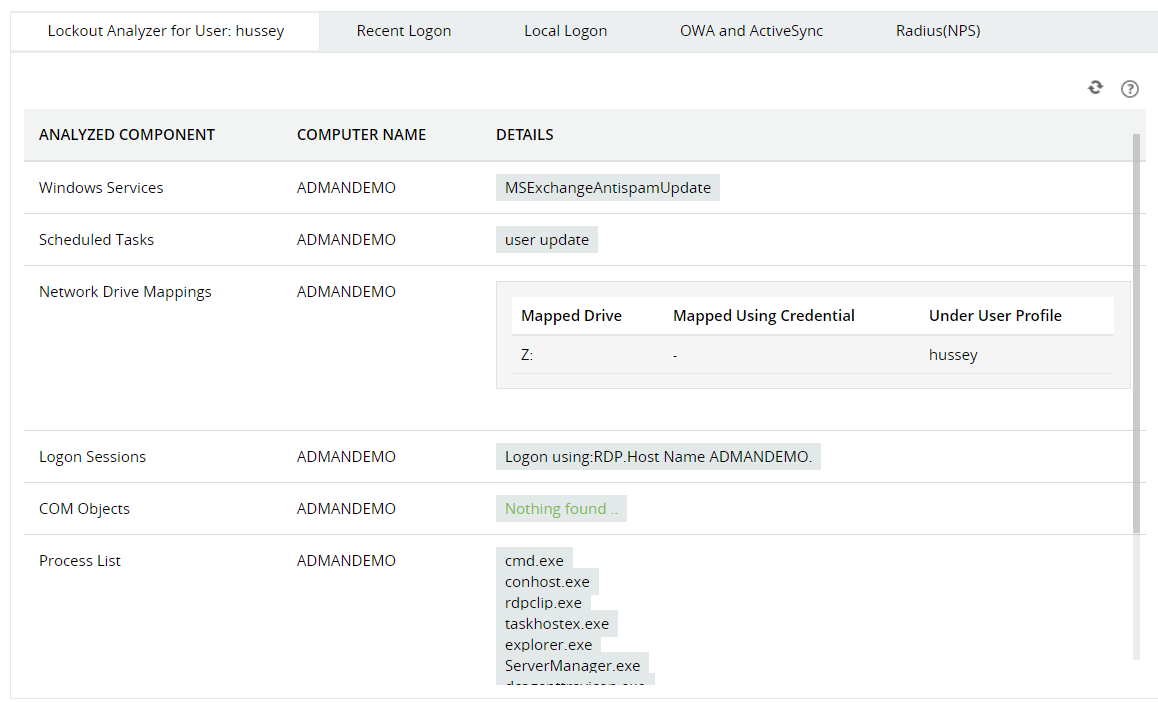
- Click on Details under the ANALYZER DETAILS section.
- You will now see the possible reasons behind each account lockout.
Using the ManageEngine ADAudit Plus tool, not only do you get other benefits, but you also get comprehensive details on how to find account lockout source in Active Directory.
Speaking of other features, you can track down the lockout source faster, improves desk efficiency, and productivity is improved, server downtime is minimized, and get compliance standards such as GDPR, SOX, HIPAA, FISMA, PCI DSS, and GLBA.
Over 10,000+ organizations across the globe are using the services of the ManageEngine ADAudit Plus tool with their Active Directory.

ManageEngine ADAudit Plus
A well-packed and complete Active Directory Auditing and Reporting tool.How to perform account lockout analysis?
Now that you have got your report on the account, analyzing it and getting meaningful information from it is very important.
- In the Account Lockout Analyzer, you will who, when and where, and even why of every lockout. It can be exported to formats such as CSV, PDF, XML, and HTML.
- Clicking on Details gives you the entire information which would have been pretty tedious when using Event Viewer or PowerShell.
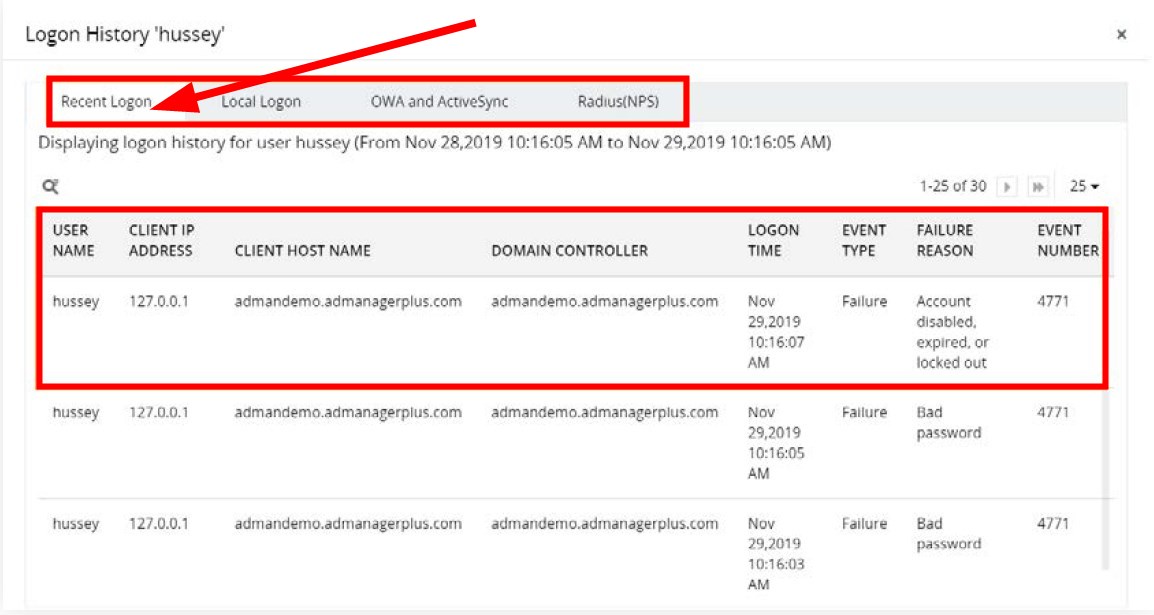
- The Recent Logon history of the user is the main area that will help you narrow the source of the account lockout. This section gives you details such as:
- User name
- Client IP address
- Client host name
- Domain controller
- Logon time
- Event type
- Failure reason
- Event number
You can also check out our guide on how you can enable Active Directory users and computers in Windows 10 as well as Windows 11.
Feel free to let us know your views on which solution you made use of to answer your query on how to find the account lockout source in Active Directory.