Identify the ransomware that encrypted your data with this free tool
3 min. read
Published on
Read our disclosure page to find out how can you help Windows Report sustain the editorial team. Read more
Malware programs can infect your computer without you even being aware of it, working silently while extracting the information they’re after. On the other hand, malware like ransomware is quite obvious, making no efforts to hide their presence.
Ransomware are malicious programs that restrict access to the infected computer system, only to demand that the user pay a ransom in order to regain access to the system. Ransomware does the dirty deed in two different ways: either it encrypts files on the system’s hard drive or locking the system completely and displaying a message demanding the user to pay.
Companies and individual researchers are developing recovery tools constantly, which is why most of the time malware is successfully removed. However, there are rare cases when decryption is impossible and users pay the ransom for the encryption key.
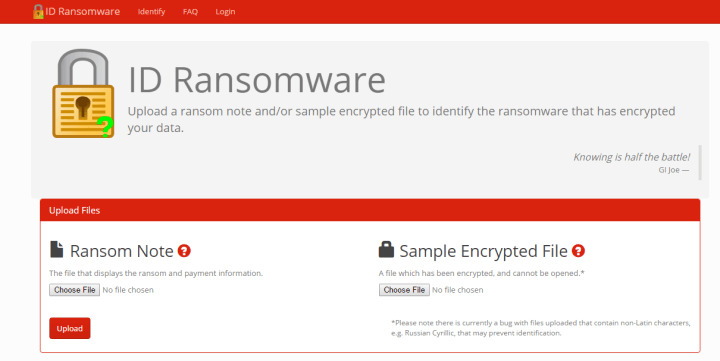
If you have been infected and need to know which malware family encrypted your data, you can use ID Ransomware to find that out. All you have to do is upload an infested file or the message the malware is displaying to your screen. ID Ransomware can currently detect 55 types of ransomware but does not offer any file recovery services. Here’s the list with all the ransomware it can identify:
7ev3n, AutoLocky, BitMessage, Booyah, Brazilian Ransomware, BuyUnlockCode, Cerber, CoinVault, Coverton, Crypt0L0cker, CryptoFortress, CryptoHasYou, CryptoJoker, CryptoTorLocker, CryptoWall 2.0, CryptoWall 3.0, CryptoWall 4.0, CryptXXX, CrySiS, CTB-Locker, DMA Locker, ECLR Ransomware, EnCiPhErEd, Hi Buddy!, HOW TO DECRYPT FILES, HydraCrypt, Jigsaw, JobCrypter, KeRanger, LeChiffre, Locky, Lortok, Magic, Maktub Locker, MireWare, NanoLocker, Nemucod, OMG! Ransomcrypt, PadCrypt, PClock, PowerWare, Radamant, Radamant v2.1, Rokku, Samas, Sanction, Shade, SuperCrypt, Surprise, TeslaCrypt 0.x, TeslaCrypt 2.x, TeslaCrypt 3.0, TeslaCrypt 4.0, UmbreCrypt, VaultCrypt
Uploaded files are analysed against the database of signatures. Results are ordered by the number of matches found between the malware and the data base. If the malware is identified, the files you uploaded are deleted. Once the rasomware type has been identified, you can search by the threat name to get the latest recovery information. Since many ransomware share similar extensions on files, in some cases, the results are not 100% clear.
If no results are found, the uploaded files are shared with trusted malware analysts for further analysis or for identifying a new malware type. As far as data confidentiality is concerned, ID Ransomware states clearly:
With that said, I cannot guarantee files are kept 100% confidential. The data is temporarily stored on a shared host [to be shared with trusted malware analysts if necessary], and I am not responsible for anything done otherwise with this data.
Obviously, our advice is to install an anti-malware software in the first place and avoid suspicious sites or files. We recommend BitDefender’s free BDAntiRansomware.
RELATED STORIES YOU NEED TO CHECK OUT:



User forum
0 messages