Microsoft Rushes to Patch a Huge Exploit affecting US Military PCs
3 min. read
Published on
Read our disclosure page to find out how can you help Windows Report sustain the editorial team. Read more

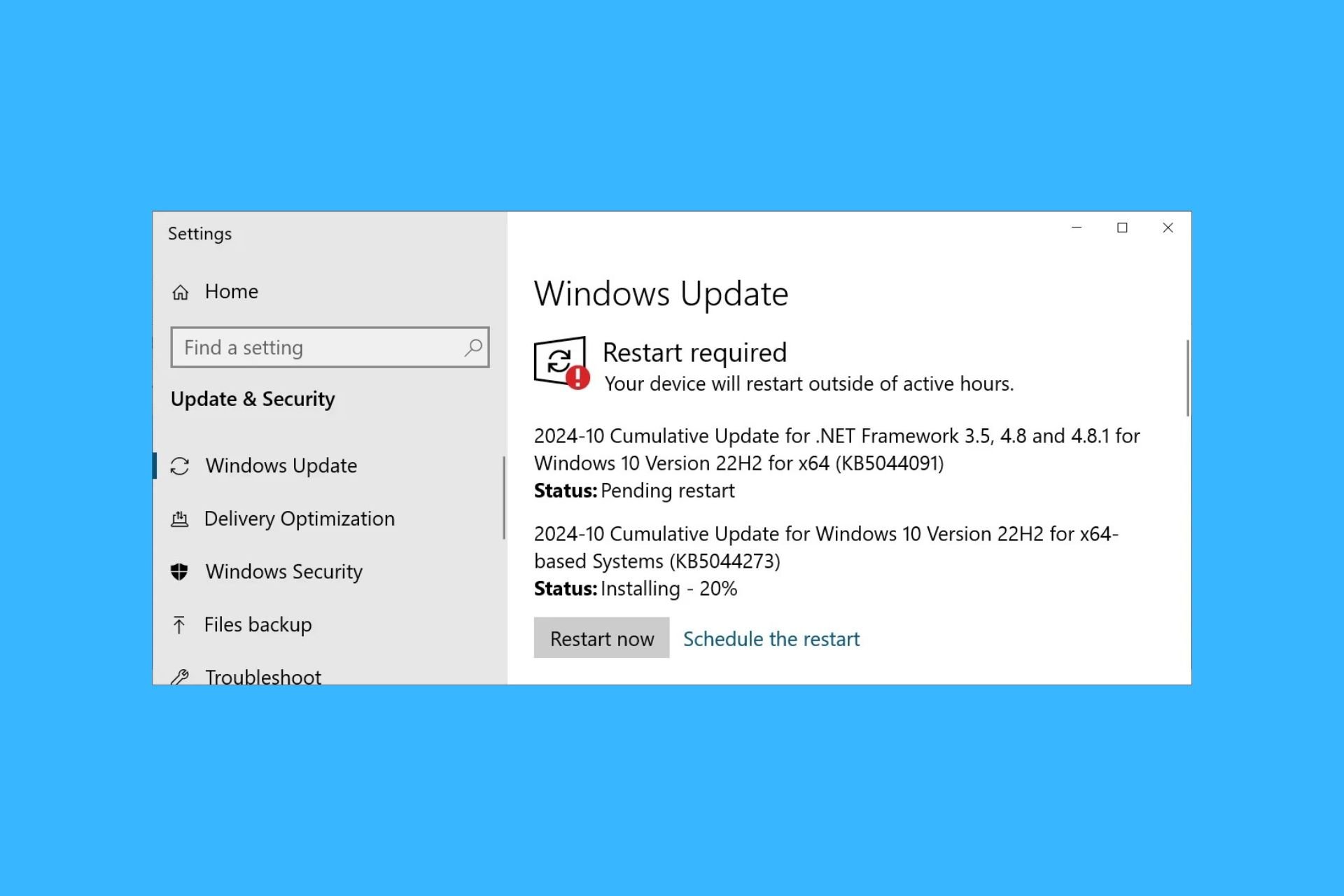
The first Patch Tuesday of 2020 is right around the corner, and is seems that Microsoft is not starting the year very well.
After a very quiet December 2019 Patch Tuesday with little to no changes, the new update is set to address a very important security vulnerability tied to a core cryptographic component found in all versions of Windows.
Microsoft released a security patch prior to Patch Tuesday
The component is called Crypt32.dll and is responsible for the implementations of most Certificate and Cryptographic Messaging functions in the CryptoAPI:
Crypt32.dll is a module that comes with the Windows and Windows Server operating systems, but different versions of this DLL provide different capabilities.
While this may sound a bit to technical, the most important thing you’ll need to know is that the CryptoAPI helps developers to add more security to Windows apps through cryptography. The encryption and decryption of data is done using digital certificates.
To further confirm this security breach, it seems that the big M supposedly released a patch to fix it before the January 14 Patch Tuesday. It was sent to important customers, companies that work with Internet infrastructure, and branches of the U.S. military.
Of course, Microsoft made sure that none of them can disclose the issue before January 14th through non-disclosure agreements. As a response to KrebsonSecurity , the company stated:
Through our Security Update Validation Program (SUVP), we release advance versions of our updates for the purpose of validation and interoperability testing in lab environments. Participants in this program are contractually disallowed from applying the fix to any system outside of this purpose and may not apply it to production infrastructure.
The implications as well as the security risks are huge, considering the fact that the U.S. military and other high-priority targets were the first in line on Microsoft’s list.
Can this vulnerability affect my Windows PC?
Somewhat confirming the vulnerability, Will Dormann, Vulnerability Analyst at the CERT/CC, shared a very interesting tweet:
I get the impression that people should perhaps pay very close attention to installing tomorrow's Microsoft Patch Tuesday updates in a timely manner. Even more so than others.
I don't know… just call it a hunch?
¯_(ツ)_/¯— Will Dormann (@wdormann) January 13, 2020
If you were wondering about first-hand implications, know that the security flaw can affect basic Windows functions, personal data from Internet Explorer/Edge, authentication and login security, and other third-party apps.
This is very concerning, as it can lead to malware attacks and loss of private data.
As a reminder, all Windows versions are affected, including Windows XP and Windows Vista or 7. So prepare yourself for a very bumpy Patch Tuesday and keep an eye on WindowsReport’s January 14 Patch Tuesday articles to find out any new development.





User forum
0 messages