NSA’s EternalBlue exploit was ported to Windows 10, so what does that mean for you?
3 min. read
Updated on
Read our disclosure page to find out how can you help Windows Report sustain the editorial team Read more
The NSA’s EternalBlue exploit was ported to devices running Windows 10 by white hats and because of this, every unpatched version of Windows back to XP can be affected, a terrifying development considering EternalBlue is one of the most powerful cyber attacks ever made public.
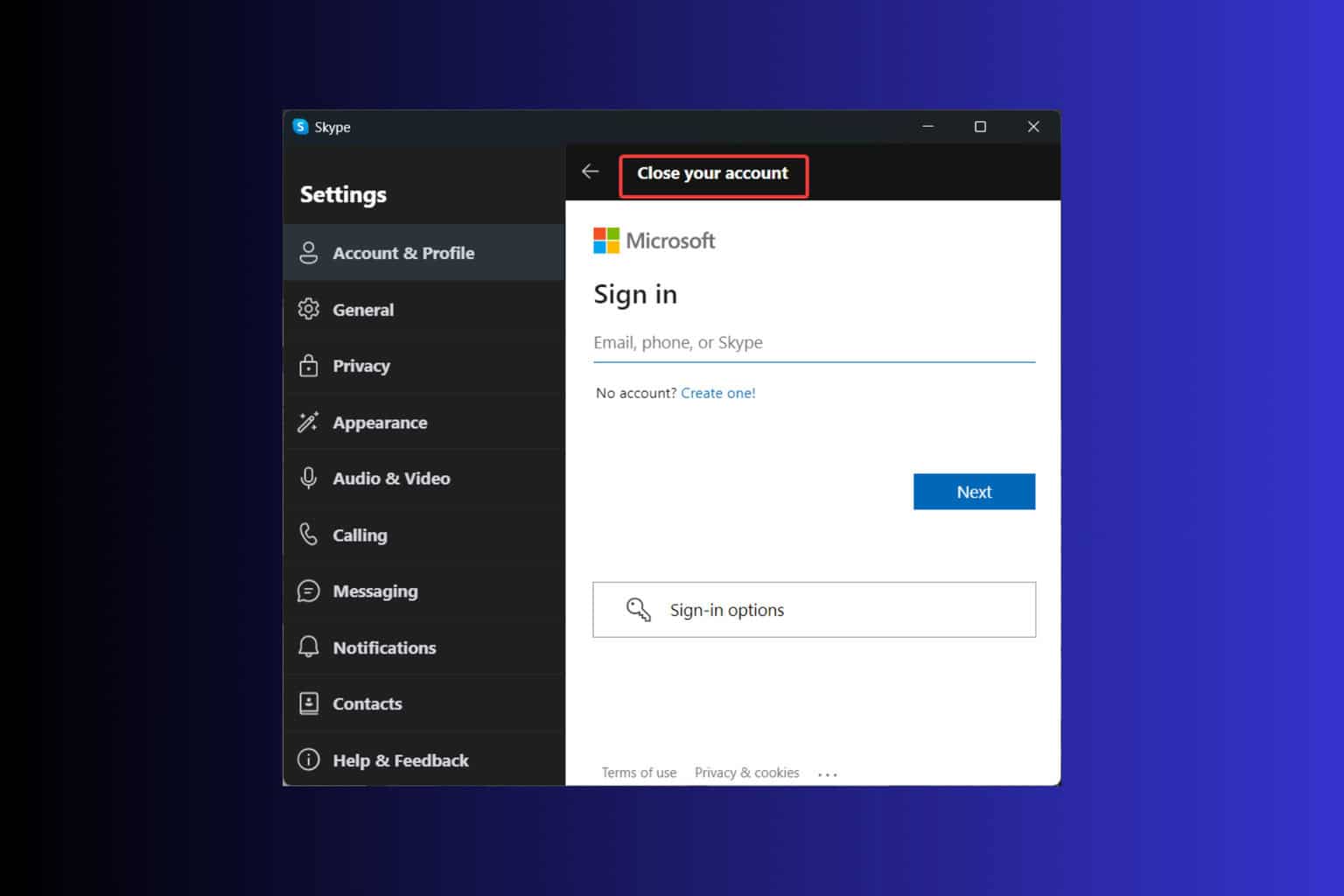
The best defense against EternalBlue
RiskSense’s researchers were among the first to analyze EternalBlue and concluded they would not release the source code for the Windows 10 port. A such. the best defense against EternalBlue remains to apply the MS17-010 update provided by Microsoft back in March.
RiskSense researchers published a report explaining what was necessary to bring the NSA exploit to Windows 10 and examining the measures implemented by Microsoft that could keep these attacks moving forward.
Senior research analyst Sean Dillon stated that the research was for the white hat information security industry to enhance the awareness of the exploits and lead to the development of new prevention techniques.
The new port targets Windows 10
The new port targets Windows 10 x64 version 1511 codenamed Threshold 2 released back in November. It supported Current Branch for Business. Researchers managed to bypass mitigations introduced in Windows 10 that were missing from Windows XP, 7 or 8 and they were also able to defeat EternalBlue bypassed for DEP and ASLR.
The ShadowBrokers’s leaks were snapshots of the NSA’s offensive capabilities and not an image of their current arsenal. By now, the NSA probably has a Windows 10 version of EternalBlue but until today, this option hasn’t been available to defenders.
It is believed that the NSA may have alerted Microsoft about the impending ShadowBroker leak to give the company enough time to build, test and deploy the MS17-010 before the leak.
The best type of exploit
According to Dillon, the best exploit an attacker has at his disposal is EternalBlue’s ability to instantly facilitate unauthenticated execution of remote code on Windows.
The feat managed to break a lot of new ground and Dillon said that this is a heap-spray attack on the Windows kernel. Heap-spray attacks are probably one of the most difficult types of exploitation specifically for Windows, an OS that doesn’t have source code available.
Performing such a heap spray on Linux would be tough but would be easier than this, according to Dillon. For more information, you can download the PDF report that security researchers from RiskSense published on this exploit.
RELATED STORIES TO CHECK OUT: