New Windows 10 security flaw gives system privileges to hackers
2 min. read
Published on
Read our disclosure page to find out how can you help Windows Report sustain the editorial team Read more

Recently, a security researcher @SandboxEscaper disclosed in a tweet which has been deleted (the account also has been removed), that the task scheduler is vulnerable to hackers’ attacks. More specifically, a successful attack will involve the user downloading a malicious app on a target machine which will then offer hackers full system priviliges.
Phil Dormann, a CERT researcher, confirmed the bug on the social network. He explained that it works “on a fully-patched 64-bit Windows 10 system. LPE right to SYSTEM!”
CERT also offered additional information on this security vulnerability:
Local privilege escalation vulnerability is contained in a Microsoft Windows task scheduler in the Advanced Local Procedure Call (ALPC) interface, which enables a local user to obtain SYSTEM privileges,” the advisory reads. Elevated (SYSTEM) privileges might be gained by local users.
Microsoft may fix this security issue in September
Microsoft already confirmed that they’re working on a fix which should be available in September. Most likely, the hotfix will be available on Patch Tuesday, which means that Windows 10 computer will be vulnerable to attacks for two more weeks.
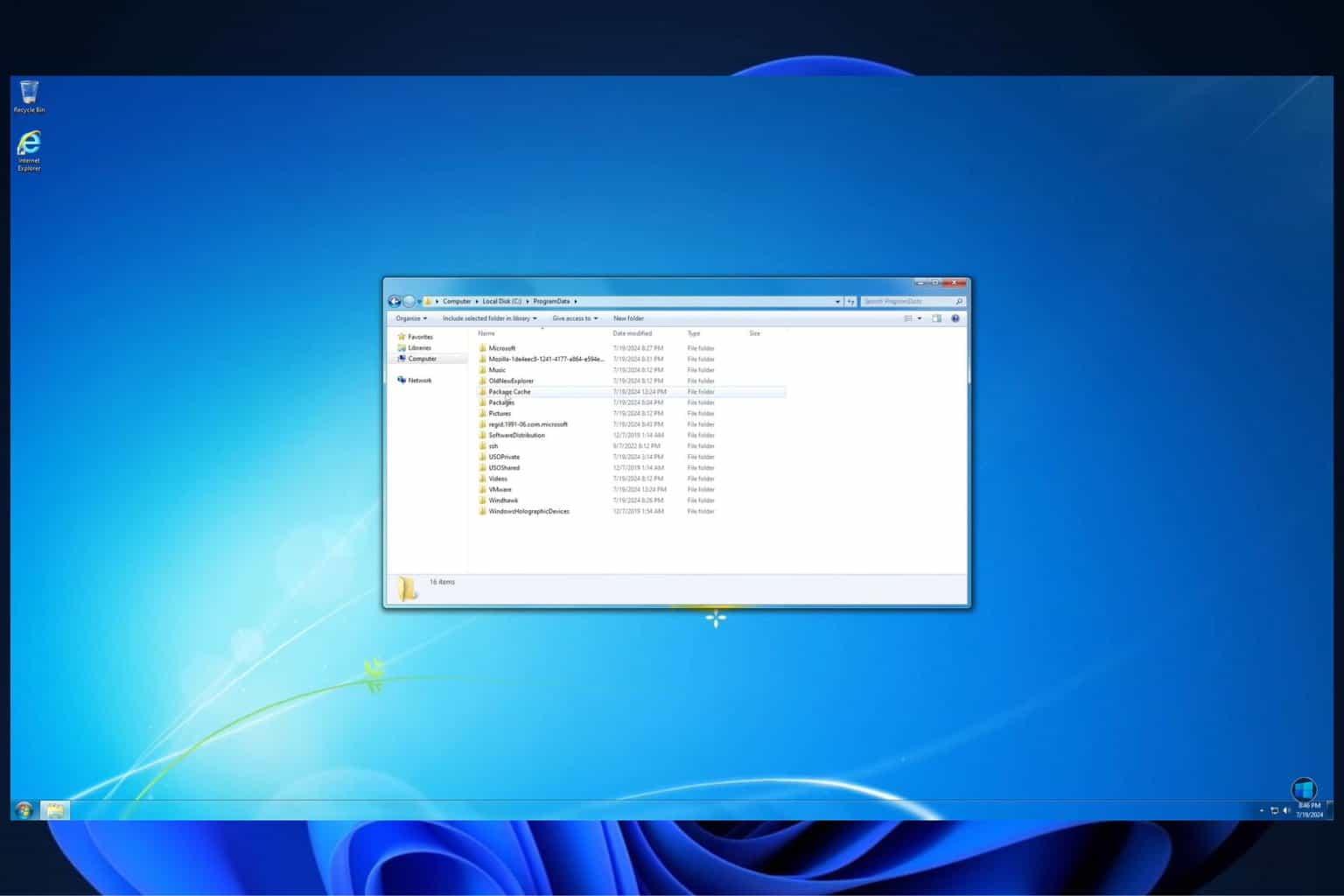
It seems all Windows 10 versions are affected, regardless of the patch level. Fully up-to-date systems are vulnerable as well. However, older Windows version, such as Windows 7 and Windows 8.1, are not affected by the problem..
We do recommend that you protect your Windows PC by using a strong antivirus program such as Bitdefender, BullGuard, or Malwarebytes. You can also install a specific program to scan and remove hidden malware in order to detect and remove any malware that may have sneaked in your computer.
RELATED STORIES TO CHECK OUT:
- Here’s how Windows 10 RS5 improves PC security, Skype, and Edge
- Lazy FP State Restore security vulnerability affects Intel CPUs
- BlueBorne vulnerability puts all Bluetooth-capable devices in danger