UPnP bug exposes Windows 10 devices to RCE attack
2 min. read
Updated on
Read our disclosure page to find out how can you help Windows Report sustain the editorial team Read more
Key notes
- A UPnP, vulnerability, CallStranger, lets bad actors discover and steal data from networked devices.
- Affected devices include Windows 10 PCs, access points, and routers.
- For more updates on the latest threats to web-facing apps and devices, check out our Cybersecurity section.
- Also, you may visit the Security & Privacy page for IT security guides, tips, and news.

Data theft is lucrative business, and has been for a long time. That’s why cyber criminals are making billions of dollars per year by stealing and selling personal data like names, credit card details, and health records. They use different tools and techniques to breach IT networks, and a UPnP bug is one of the latest to get the attention of the National Institute of Standards and Technology (NIST).
How hackers can exploit the UPnP bug to exfiltrate data
Recently, NIST updated the National Vulnerability Database (NVD) with information about the Universal Plug and Play protocol exploit (CVE-2020-12695). The organization is currently analyzing it.
The bug, named CallStranger, has been around since 2019 when a cybersecurity researcher reported it (via Bleeping Computer).
Ideally, UPnP should be a convenient way for devices to register each other’s presence on your network. Windows 10 PCs, routers, printers, and Wi-Fi access points are some of the gadgets that may use the networking technology.
Usually, no authentication is necessary for these devices to discover each other via UPnP. Moreover, they’re usually part of a local, trusted network.
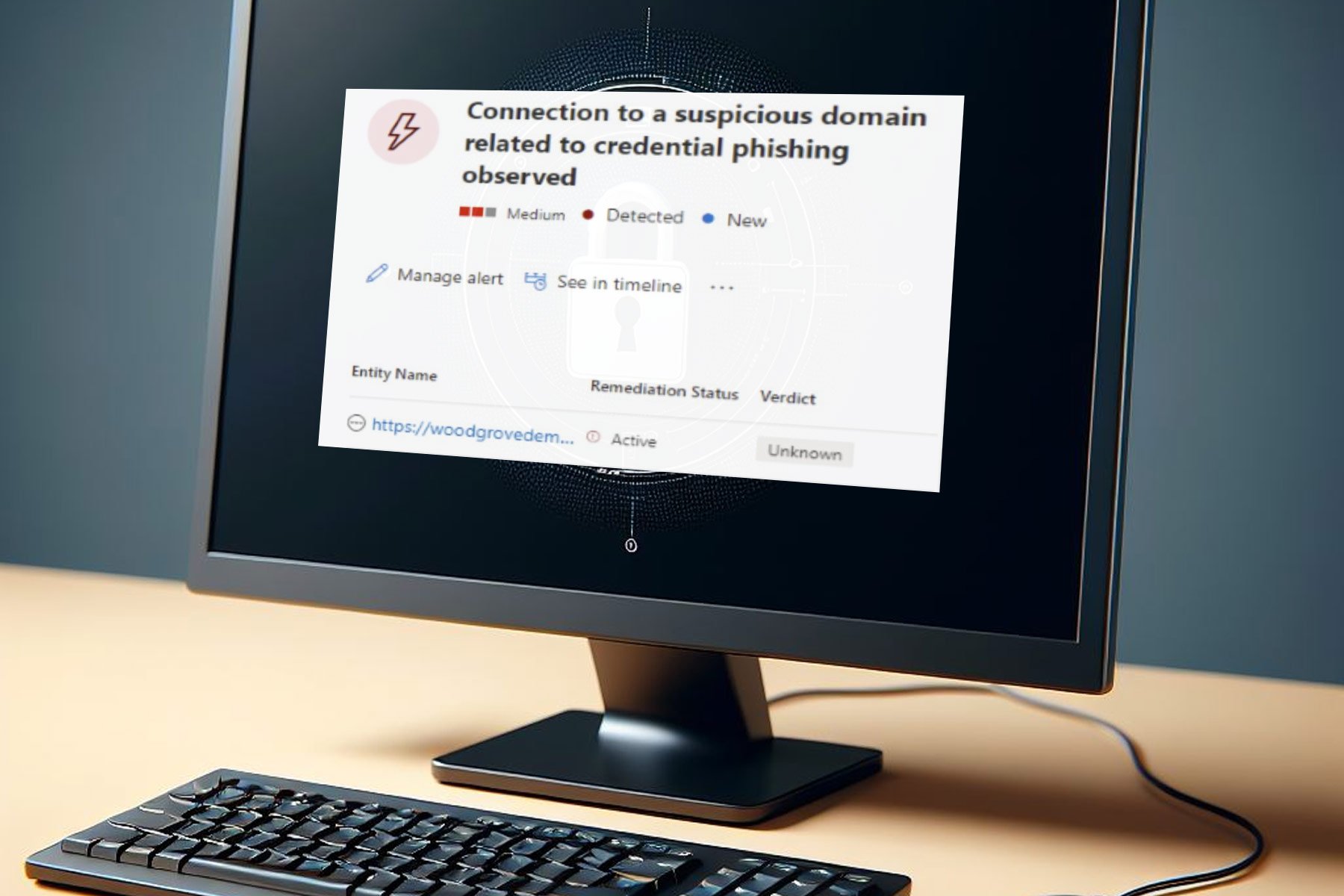
That wouldn’t be a problem except for the possibility of hackers exploiting the CVE-2020-12695 vulnerability in UPnP. In other words, a malicious actor can scan for the connectivity ports and use them to gain entry into a device.
For example, an attacker could remotely leverage the UPnP bug to discover a Windows 10 PC connected to your network. In the case of CallStranger, the malware could sidestep all data loss prevention and network security measures in place.
This way, the bad actor can easily access and steal data stored on your PC. That’s not the only IT risk, sadly.
CallStranger can also be remotely deployed in a Distributed Denial of Service (DDoS) attack. Hackers could also use it to scan internal networks.
Have you had any experience with the UPnP bug? Feel free to share it (or ask any questions) in the comments section below.
[wl_navigator]