8 Best Anti-Exploit Software to Protect Your Browser
8 min. read
Updated on
Read our disclosure page to find out how can you help Windows Report sustain the editorial team. Read more
Key notes
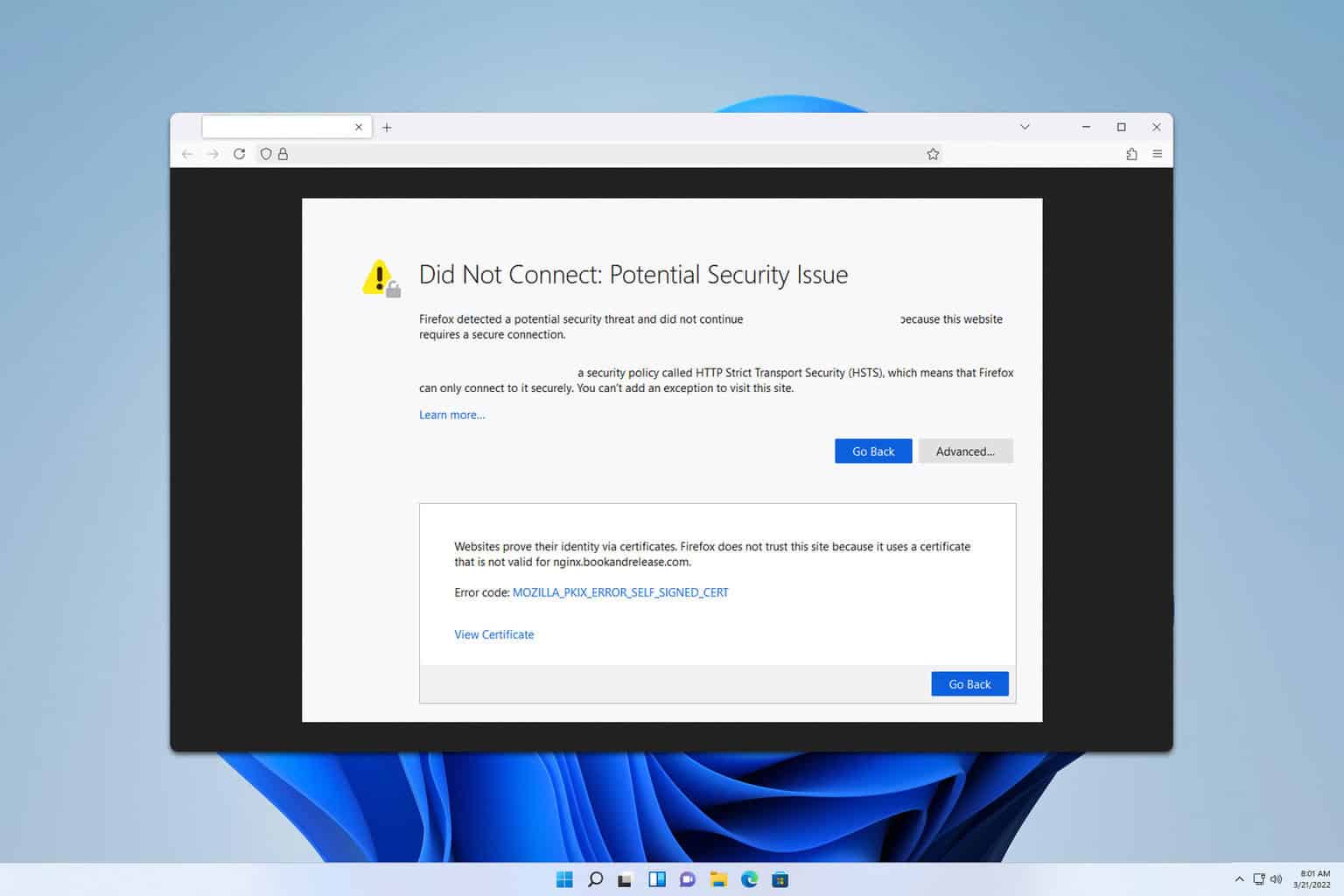
- Hackers tend to benefit from security vulnerabilities, but you can protect your computer with anti-exploit software.
- There is effective software that will keep your PC safe from malicious Internet websites or potentially unwanted apps.
- For ultimate protection against hackers, we suggest using anti-exploit software.
- If you want to add an additional layer of security, use a reliable web browser with a built-in VPN.

Are you worried about penetration attacks from malicious software even though you have an antivirus? What you probably need is anti-exploit software.
An anti-exploit program shields your web browser and programs from vulnerabilities, hence, boosting your computer security options.
This provides a good defense against exploiting techniques and tools from hijacking your web browsers. You can get an additional security layer that prevents attacks on your web browser and plugins.
Meanwhile, the Windows Report team has compiled this list of anti-exploit software that you can use on your Windows PC.
However, we have also included in this article, antiviruses software that comes with built-in protection for your browser and online activities.
What is anti-exploit protection?
Protecting against malware that infects devices and spreads by exploiting vulnerabilities is made easier by anti-exploit technology. The mitigations that makeup exploit prevention can be implemented on either the operating system as a whole or on specific applications on their own.
Even though vulnerability prevention is enabled by default in Windows 10 and Windows 11, you may still make use of third-party applications.
What is an example of an exploit?
An exploit is a piece of software, a bit of data, or a series of commands that takes advantage of a defect or vulnerability to make computer software, hardware, or other electronic devices behave in an undesired or unexpected way.
One such example is a computer virus that enters your computer without your notice and starts modifying or stealing data. With the help of anti-hacking software, you will prevent unnecessary suffering.
Quick Tip:
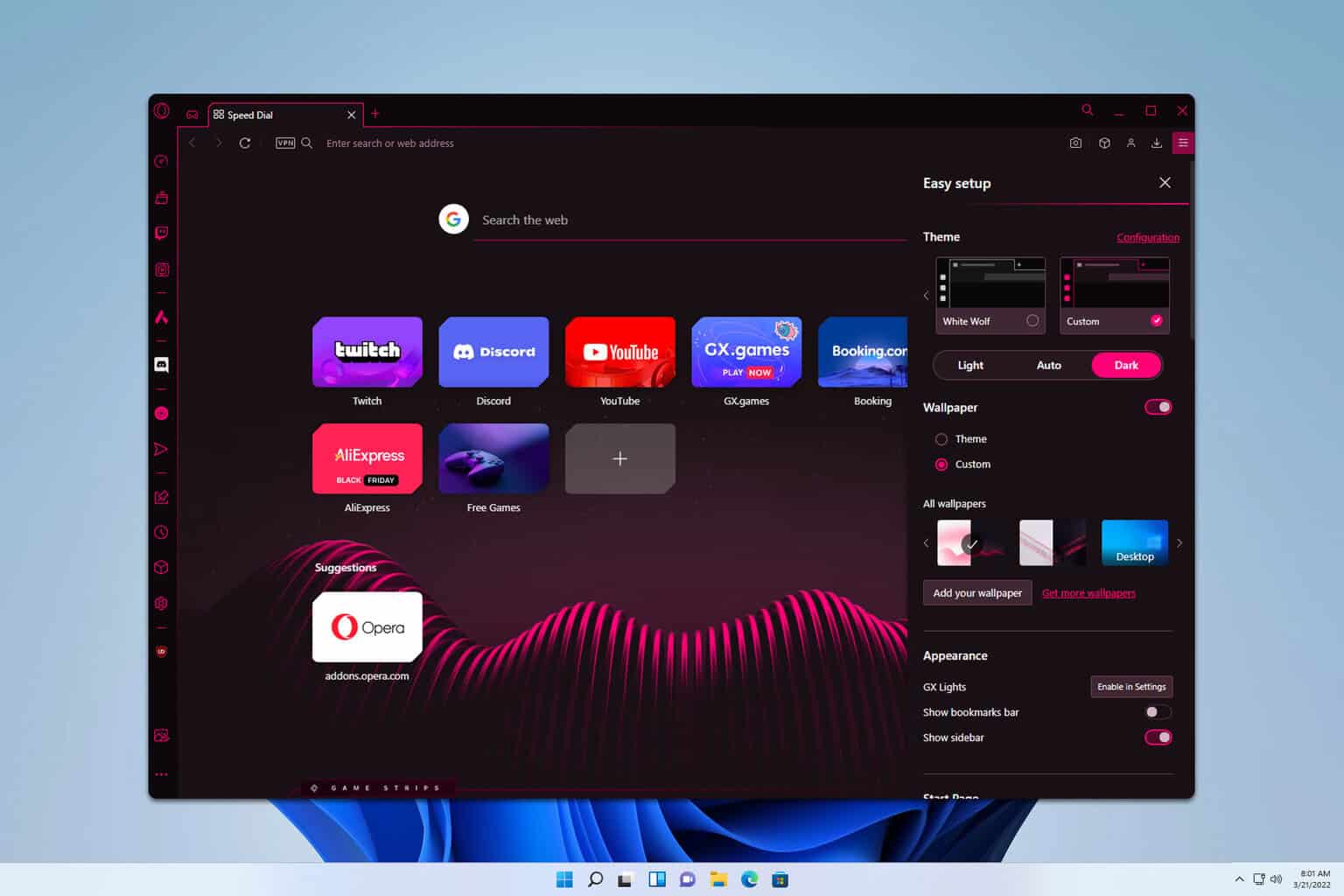
Use a browser with built-in security. Being secure while browsing should be the top priority for millions of Internet users. But, instead of relying on a tool, this browser relies on its own protective measures.
Besides features such as a built-in VPN, Ad blocker and AI, it is rather fast and packs an intuitive design based on the Chromium platform. Also, it features a modular AI-ready design.

Opera One
Use one of the most secure and fast browsers, that also includes plenty of security features.What are the best anti-exploit software tools for browsers?
ESET HOME Security Essential
ESET HOME Security Essential is a legendary antivirus trusted by millions of users worldwide. It protects your browser and your online activity as well
This tool features a special secured browser through which you can safely pay online. Furthermore, you run any supported browser in secured mode by default (after the setup).
Additionally, ESET automatically protects you while you perform internet banking activities, and access web-based crypto-wallets.
It encrypts communications between the keyboard and the browser for safer transactions and notifies you when using the feature on public Wi-Fi.
In addition, this light antivirus software guarantees reliable defense from phishing attacks or email scams that can access your private data.
You can as well inspect your web vulnerabilities with the Network Inspector utility to find the weak spots and better secure your online data.
ESET HOME Security Essential
Protect your browser and your computer from online threats such as keyloggers, and malware.Guardio
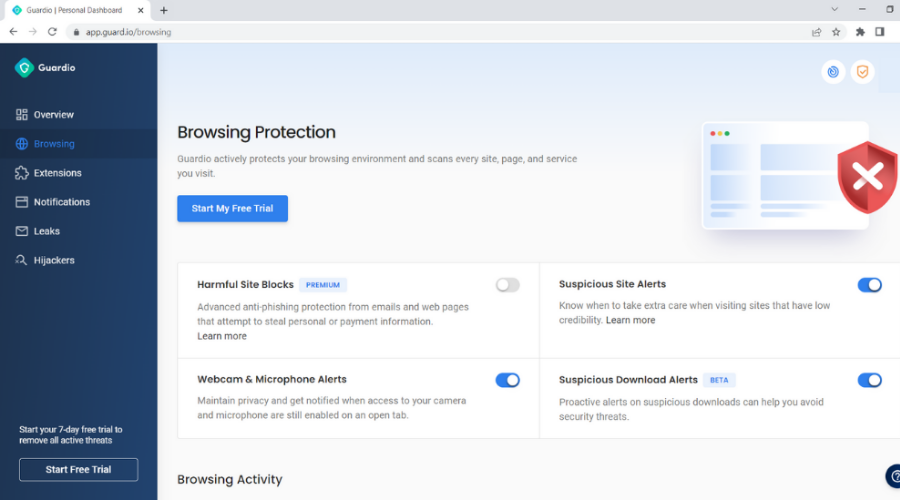
Guardio browser security can guard all your private online tasks and avoid harmful websites and exploit attacks.
This protection tool has a 1,000,000 user base and works as a browser extension and is capable to detect various cyber threats or personal information leaks from your browser.
You can get reliable threat protection functionality that will guard you against malicious web pages or phishing email attacks.
That means you can gain advanced protection for your browsing behaviors and perform financial activities with no risks of data theft. Plus it is now available with the same subscription on Android and iOS systems.
Another essential aspect of browser security is exactly browser extensions. Monitoring browser extensions will help you detect corrupted plugins that may affect your browser settings.
In addition, you have identity and information leak monitoring tools, social media account protection, and 24/7 customer support.

Guardio
Benefit from exhaustive browser security and protect online private data with effective antivirus or anti-phishing tools.Malwarebytes
This software is the perfect Internet security system that shields your personal computer from vulnerabilities.
Malwarebytes Anti-Exploit program is capable of detecting bugs on your system as well as removing them from your PC.
It shields applications such as Microsoft Office, VLC Media Player, Adobe PDF Reader, and many more.
This program works by wrapping security layers around web browsers and applications; hence, preventing compromising exploits from taking over your PC.
The best feature of this tool? It is known for detecting and removing threats that traditional antivirus solutions can’t handle. It does this using the power of artificial intelligence.
Trojans, spyware, ransomware, worms, or viruses don’t stand a chance of entering your system thanks to the real-time protection offered by Malwarebytes.

Malwarebytes
Top anti-exploit software that offers total protection for your browser and device with Malwarebytes Premium.Avira
Avira is another freeware antivirus that you can use to protect yourself from all sort of online exploits, malware, and threats.
Its core technology will block any online threats, including malicious websites, ransomware, and spyware. Thus, you can browse the Internet without worries.
Additionally, Avira can keep you safe from phishing attacks on social networks, including your inbox, or email scams.
Not enough? It also includes a free VPN tool, that will secure your online activities, and make your searches anonymous.

Avira
Stay safe from exploits with a free antivirus that will block any malicious websites.IObit Malware Fighter
IObit Malware Fighter is anti-exploit software that is designed to shield your personal computer from any online attacks.
In addition, you also get protection against malware, Trojans, and viruses that may intrude on your PC while surfing the web.
It features an Anti-ransomware Engine. This is a useful tool since ransomware attacks are getting more popular.
Malicious links that are sent via email are blocked by IObit. It even blocks exploits that try to get access to your web camera.
Finally, viruses are a thing of the past with two different scanning and cleaning engines. One from IObit and the other one from Bitdefender.

IObit Malware Fighter
Protect your personal data and guard all browser activity with IObit Malware Fighter.Avast Free Antivirus
Avast Free Antivirus protects your computer against viruses and malware, and it helps you protect your home network against intruders.
Moreover, you can add the Avast plugin to your browser. It will check each website you visit and warn you if it’s unsafe or if it simply has a bad reputation.
Additionally, this will stop websites from collecting data on you and tracking your browsing history via cookies. Thus, you can surf the web knowing you are safe.
Avast is packed with the largest threat-detection network, machine-learning, and browser protection. All these security features won’t slow down your PC.
Avast Free Antivirus
Keep your computer safe from exploits with one free and comprehensive antivirus solution.Microsoft EMET

Microsoft EMET otherwise known as Enhanced Mitigation Experience Toolkit is one of the oldest anti-exploit software around.
This free program targets system administrators who can implement this software on multiple PCs on a large computer network.
This software uses application hardening which prevents exploitation of various software application vulnerabilities.
In addition, EMET uses 12 different security mitigations to protect other software applications and running processes on the PC.
However, Microsoft EMET is no longer available for Windows 10 OS because Windows 10 contains protections such as AppLocker, Control Flow Guard (CFG), and Device Guard
HitmanPro
This premium software is an ideal anti-exploit tool for your PC. There are two software options from which you can choose, depending on your needs.
HitmanPro Cleans malware, viruses, trojans, worms, keyloggers, rootkits, trackers, spyware, and more.
HitmanPro.Alert version, includes the previous one and stops complex attacks and exploits in real time while increasing privacy.
If you want to protect your web browsers from exploits, you should give this program a try. HitmanPro.Alert blocks hacking attempts and impedes ransomware on your PC.
However, you should use an antivirus along with the anti-exploit program; but not two anti-exploit programs at the same time to prevent overlapping.
However, we do recommend any of this anti-exploit software for you to shield your Windows PC from any techniques and tools used by hijackers.
Also, you can use an antivirus that includes anti-exploit solutions. If you want to discover even more security tools, check our guide, including the best antivirus for Windows 10.
Do share with us your experience after using any of the programs we mentioned. Feel free to comment below.








User forum
0 messages