Statistics You Should Know About Cyber Attacks in 2024
Dive into some important cybersecurity statistics
14 min. read
Updated on
Read our disclosure page to find out how can you help Windows Report sustain the editorial team Read more
Key notes
- Healthcare and the Education sectors were the most vulnerable to cyberattacks in the past few years.
- We will see an exponential increase in the number of cyber attacks in the upcoming years.
- The damage cost estimation of cyber-attacks is expected to grow by 15% YoY to $10 trillion annually by 2025.
Cyber attacks are on the rise, and not only their frequency has grown in numbers, but their varieties have also evolved. Cyber or ransomware attacks have increased in volume and continue to threaten businesses and individuals.
Cybercrime or malware attacks have seen a substantial upward shift due to the COVID-19 pandemic. Cyber attacks include data hacking and data breaches, phishing, identity theft, cyberstalking, etc.
This article aims to provide a comprehensive overview of the current statistics of cyber attacks, including the most common types, their frequency, the industries most affected, and the cost implications.
We will also delve into the future trends in cybersecurity and the measures businesses can take to protect themselves against cyber threats because, spoiler alert, the ransomware attacks are expected to double in 2025.

Secure your devices with award-winning cybersecurity technology.

Maximize your PC's security and performance with top-notch digital threat detection.

Keep secure with groundbreaking AI detection and prevention technology.

Browse the web securely for up to 3 devices across Windows, Mac, iOS or Android systems.

Best security tool for intense browsing activity.
What are the most important cyber attack trends?
Cyber threats or malware attacks are vicious for every industry. While some sectors are less prone to cyber threats, some industries are on the hit list of attackers.
We have listed some of the most vulnerable industries to cyber attacks in 2022 below.
1. Healthcare sector
The most prone or vulnerable to cyber threats or ransomware attacks is the healthcare industry. The reason is pretty simple they hold a large amount of valuable patient data that could be groundbreaking for anyone.
Hackers can use the healthcare industry’s data to sell it to another company for an astronomical amount of money, identity theft of patient data, or sell it on the black market.
Although the average cost of investment in cybersecurity ventures for data protection has increased over the years, it hasn’t proven to be sufficient to tackle modern data cyber thefts.
Attackers can access vital data by different means including targetting employee’s mobile devices, phishing emails, injecting malware, or accessing the server using unsecured networks.
Here is the list of data that cybercriminals can access from the healthcare industry:
- Health records
- Clinical research data
- Patient records, including social security numbers, billing information, and insurance claims
- Data of confidential medicines or healthcare devices/medical devices
2. Financial sector

Institutions like banks and investment firms are also favorite places of cyberattacks for hackers, and why not, as it involves direct access to money and financial gain?
Financial data, bank-related information, passwords, credit card/debit card numbers, SSNs, etc. are of huge importance to cybercriminals to commit fraud or theft.
Again, financial institutions have increased their average cost in cybersecurity ventures to safeguard their assets, but they are still a bit behind the evolving cybercrime.
Moreover, it becomes a bit difficult to neutralize these attacks as millions across the globe use financial apps. Another way of committing a financial cybercrime is by installing crooked ATMs and card traps or simply stealing the machines.
Besides, as the world has moved over to cloud storage, all the critical data are now stored in cloud services and if they have a zero-trust architecture, the data becomes an easy bait.
3. Education sector

In this field, cybercriminals can access student and faculty data, financial information, and research data. Many top institutions partner with government wings for R&D, and this data is of high value.
With online tools such as payment gateways, digital data sources, cloud storage, connected devices, etc., the vulnerability of the education sector is at an all-time high.
Moreover, the basic types of attacks that lead to data breaches in the education sector include access to private networks, malware attacks on mobile devices, password leaks, phishing emails, firewall intrusion, etc.
Below are some of the important information that a hacker can get access to after a cybersecurity breach in any educational institution:
- Student’s and faculty’s personal information
- Banking details of the institution
- Records of any research
- University programs
4. Government organizations
Well, we all know that the world is moving towards some sort of war, and this time, it will be less of a war of guns and arms but more of data and technology.
Government organizations are one of the most vulnerable sectors, according to different cybersecurity statistics.
This is because any country can hire cybercriminals to extract confidential government information of their enemy country and prepare for a counterattack. For example, for years, Russia and the US have been known to breach each other’s defense contracts and steal military infrastructure.
While the average cost spent on cybersecurity measures, including military-grade antivirus software, is at the highest level in government organizations, data breaches are still more prevalent in this sector.
Cybercriminals are actively looking to breach government institutions as not only can they help their country stay ahead in the modern-day race to become a superpower, but their value is astronomical.
5. Retail industries

Trade has been one of the major economic boosters for many countries and it holds some of the most vital information. Since the world has become digital, digital fraud tools are also on the rise.
Retailers most commonly suffer from DDoS attacks, which basically disrupt the targetted server, websites, etc. The reason is that the retail industry is known to rely on low-standard network security.
The method of social engineering attack is the one that is most commonly used for data breaches in retail industries according to various cybersecurity experts. These attacks can easily help get customers’ account information, credit card details passwords, etc.
Retailers, by simply adopting the usage of two-factor authentication, where an OTP is sent on mobile devices to verify access, can significantly reduce the number of attacks. Moreover, strong passwords are also key to protection against cybersecurity threats.
6. Manufacturing industries

Cyber attack statistics show that manufacturing industries have now increasingly become a popular target for hackers.
Since everything is now automated using machines and software, any attack on the manufacturing process can hamper or malfunction the machines.
This could lead to physical damage, loss of lives, billions of dollars in damage, production halt, and much more.
Hackers attack manufacturing companies to hack the ICS (Industrial Control Systems), monitoring, and control the industrial processes.
Any attack on the manufacturing facilities of a country or state can lead to large-scale disruptions and economic losses. While this industry isn’t at the top list of attackers, if it is targeted, the disruption factor is very high.
What are the costs of cyber attacks?

Well, according to cyber attacks statistics, if it were measured as a country, the damages that cybersecurity attacks totaled $6 trillion in 2021, which would be the third-largest economy, behind the US and China, and ahead of the UK and Germany.
Notably, Cybersecurity Ventures believes that cyber-attacks are expected to grow exponentially, and the damage cost estimation is speculated to grow dramatically by 15% YoY, reaching a staggering $10.5 trillion annually by 2025.
Besides, the costs of cybercrime are expected to be worth 1% of the global GDP. The damage injected by ransomware attacks was 57 times more lethal in 2021 than in 2015.
While the above cyber attacks statistics represent the value or worth of the entire cybercrime presently and in the years to come, according to the IBM report for 2023, below is the list that shows the cost of different types of cyber attacks:
- Business email compromise cost $4.89 million (compared to $5.01 million in 2021)
- Phishing attacks stood at $4.91 million (compared to $4.65 million in 2021)
- Malicious insider attacks amounted to $4.18 million (compared to $4.61 million in 2021)
- Social engineering criminal attacks cost $4.10 million (compared to $4.47 million in 2021)
- Vulnerabilities in third-party software cost around $4.55 million (compared to $4.33 million in 2021)
The average cost of data breaches globally stood hit the $4.35 million mark in 2022. According to Cybercrime Magazine, global cybercrime costs are expected to grow by 23 percent/year and will reach $23.84 trillion annually by 2027.
By next year, i.e., 2024, online payment fraud will reach a high and will cause around $25 billion in annual losses. Ransomware costs are expected to bill around $30 billion globally in 2023.
The cost of cyber attacks will rise in the current year 2023 because for multiple reasons, one being the economic woes across the globe. Inflation and energy crises in major parts of the world are also going to be responsible for the increased cyber security costs.
Some other important reasons could give rise to the cost of cyber attacks:
- Easy access to powerful malware kits
- Geopolitical tension among major economies
- Rapidly expanding attack surface
A study done in 2020 showed that, execessive screen time could cause increase the levelas anxiety, sadnesss, uncertainity, and aggression, also increased cyberattacks during pandemic.
What are the types of cyber attacks?
1. Malware attacks
According to cyber attack statistics, 92% of the malware is distributed through email attachments, and it takes up to 49 days to get detected.
Generally, software is utilized in malware attacks to access the IT network and disrupt the entire network and associated devices.
Around 4.1 million websites are malware-infected, and 18% of them are known to contain critical cybersecurity threats.
Malware attacks are generally a bit complex to detect but are easier to protect against by using reliable anti-malware software.
98% of the malware attacks are targeted toward Android mobile device users. Ransomware attacks are a subset of malware attacks; the frequency of ransomware attacks has increased, for instance, 11% in 2022 compared to 7.8% in 2021.
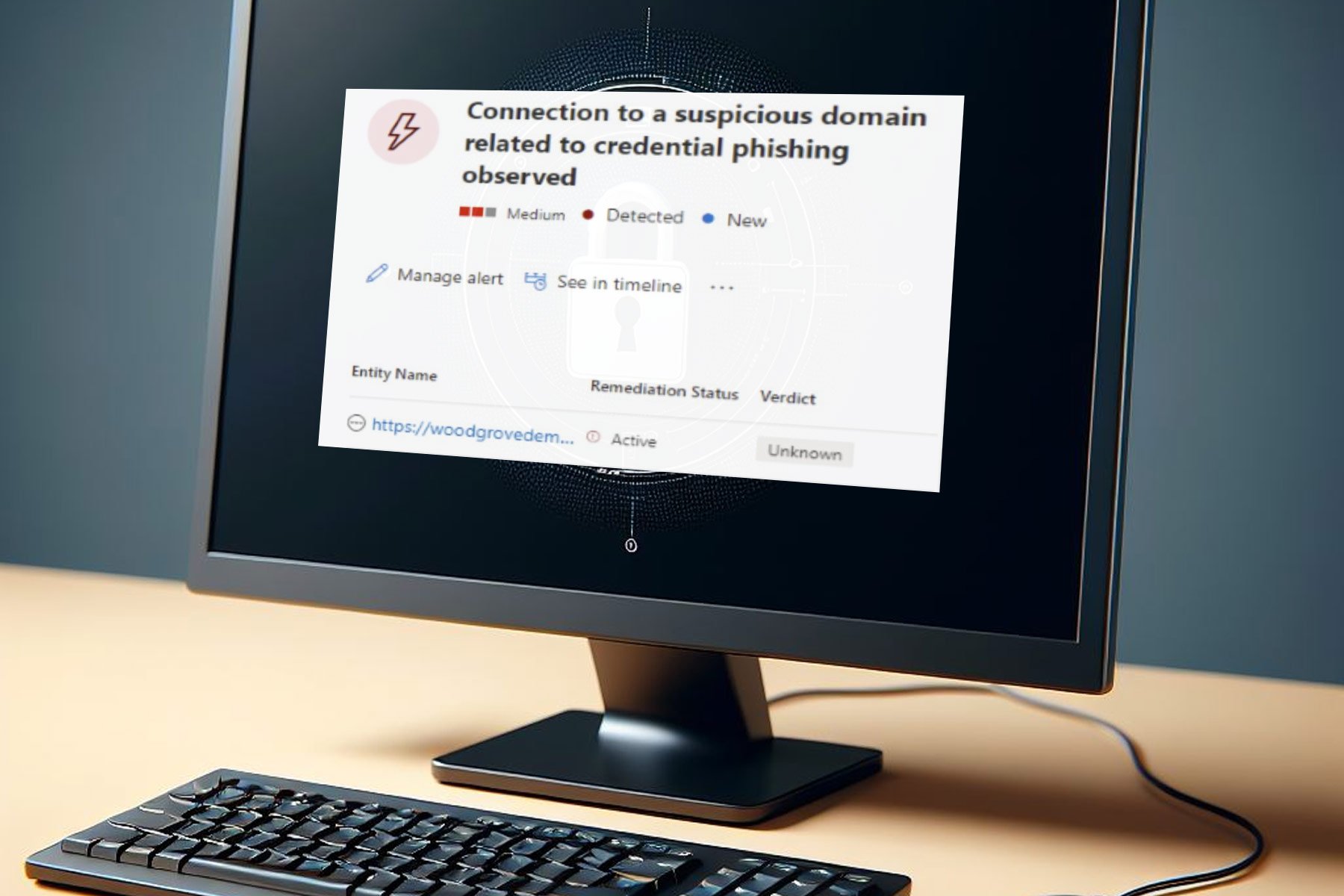
2. Phishing
Phishing attacks are a type of attack that makes use of email, SMS, or phone and other social engineering techniques to get hold of one’s device and access sensitive information.
There are different types of phishing attacks such as spear phishing, whaling, SMishing, and Vishing. Phishing attacks are usually successful; however, can be pretty easy to protect against.
Phishing attacks are on the rise and according to a report by Lookout, 2022 recorded the highest level of mobile phishing attacks.
Some of the best ways to protect oneself from phishing are to never click on a link in an email that arrives in your inbox randomly, not enter your personal information on any random website, change passwords regularly, install firewalls, keep your antivirus software up to date, verify the integrity of a website before visiting, etc.
3. Supply chain attacks
As per Gartner statistics, by 2025 around 45% of organizations will experience an attack on their supply chains.
Supply chain attacks target open-source code or third-party APIs developed by developers. However, relying on third-party software means any disruptions in the software can unintentionally introduce vulnerabilities to the main system.
Supply chain attacks can be a bit hard to detect in case they are discovered too late and spread like wildfire as it is distributed via some software update or installation package.
Such attacks can be significantly reduced by deploying strong integrity code policies, using endpoint detection and response solutions, rolling out regular security patches, applying multi-factor authentication all across the system, use of strong passwords, checking digital signatures, etc.
4. DDoS attacks
DDoS attacks originate from multiple systems and are harder to block because of their origin. In the Distributed Denial of Service attack is malicious as it can disrupt a network and flood it with internet traffic.
In 2022, Microsoft officially reported that an average of 1,435 DDoS attacks daily were mitigated by security experts.
One of the most significant and recent DDoS attacks occurred in March 2023 on the website of the French National Assembly orchestrated by Russian hackers.
Some of the best practices to prevent DDoS attacks are:
- Improve network security
- Ensure server redundancy and usage of multiple servers
- Use cloud-based protection
- Look for warning signs and have a quick response in place
5. IoT attacks
Internet of Things attacks will continue to grow because of the increase in the usage of smart home appliances like TVs, speakers, security cameras, and others.
In IoT attacks, hackers attack a network and get hold of all the interconnected devices. The IoT attacks have seen an exponential increase of 87% in 2022 compared to the previous year.
Some of the best ways to protect against IoT attacks are listed below:
- Keep the firmware updated
- Ensure IoT devices are secured properly with passwords
- Limit access of users connected to the devices
- Set a unique password for all connected devices
How can I protect against cyber attacks?
1. Apply the basic measures
One of the easiest ways an attacker can access a business is via its employees. Businesses should train their employees in some basic measures, some of which are listed below:
- Educate them about checking the links or malicious email attachments before opening them
- Have them verify each email or website before visiting or opening them
- Apply common sense before sending confidential data over the network. Ask them to call the person before actioning the request
- Apply strong passwords and remind them to change the passwords frequently
- Restrict employees from using their personal devices in the workspace for office work
2. Keep firmware updated
You should ensure that the network’s connected devices are regularly updated. Businesses should have a patch management system that will manage all the software and system updates.
Attackers look for any type of vulnerabilities; the best is outdated systems or software. Most security incidents can be prevented by keeping the firmware up to date.
3. Install firewall and antivirus
It goes without saying that having a dedicated and reliable antivirus is essential to keep a business free from general attacks that could happen on a daily basis.
The network must be put behind a firewall and a sophisticated one because it will help avoid any brute attack and give you time to safeguard all of your crucial data.
4. Protect your customers
Businesses should protect their customers because losing customer information can lead to a bad reputation in the industry.
Investments should be made in online security for transactions and customer information storage. Complicated security policies should be in place to safeguard customer data to avoid data loss.
5. Backup data and consider cybersecurity insurance
It is a known fact that cybercriminals have their way around sophisticated secured networks. In such a scenario, it is important that businesses have backed up their data.
This could prevent loss of data, downtime, and other problems because of cyber attacks. Besides, investing in cybersecurity insurance can help at times because the cost of dealing with a cyber attack is more than that just repairing the databases, fixing compromised devices, etc.
Cybersecurity jobs
While the current scenario of jobs isn’t that good as a lot of companies are laying off their staffs due to troubling economic issues, cybersecurity jobs have seen tremendous growth in recent years.
Going by the numbers, the cybersecurity job vacancies grew by 350% in 2021, from 1 million openings in 2013 to 3.5 million vacancies in 2021. Cybersecurity is a growing field and the industry is projected to grow by 11% in 2023 and by 20% in 2025.
While there is a huge demand surge in cybersecurity jobs, it comes with a lot of responsibility on the shoulders of cybersecurity professionals.
- They are responsible for the company’s data and information
- They are responsible for the company’s reputation in the market
- Have to save the company’s valuable assets
- Are responsible for saving the company’s unnecessary spending on tackling cyber threats
The above are some of the responsibilities of a cybersecurity specialist. There are different roles that you can take up in this field, some of which are listed below:
- Chief Information Security Officer (CISO) – Should have IT experience, communication and presentation skills, must be certified as Certified Information Security Manager (CISM) and Certified Information Systems Security Professional (CISSP) and risk management skills
- Cybersecurity Engineer – Networking knowledge, computer science background, knowledge of C/C++, Python, Java, and other languages, strong communication and presentation skills, must be a Certified Ethical Hacker or a CompTIA Security+ certified professional
- Malware analyst – Knowledge of different operating systems, use tools such as IDA Pro, OllyDbg, RegShot, and TCP view, coding should be the stronghold
- Penetration Tester – Networking skills, trained in Java, Python, and Perl, must know black-box testing, and knowledge of different OSs
How many cyber attacks happen each year?
According to multiple research reports, over 800,000 people fall victim to cyber-attacks each year, which is expected to continue to increase in the coming years.
How many cyber attacks occur each day?
Speaking of the number of cyber attacks each day, it is estimated that a cyber attack usually occurs every 39 seconds. Research companies have found that more than 2,200 cyber attacks happen each day.
This can be attributed to the online piracy statistics, which indicate that a large number of people visit illegal sites on a daily basis.
That is it from us in this guide. To conclude the only thing that we would say is that it is a digital world out there, and while have to rely on them, our safety and security are of utmost importance.
Anything you can do right now to protect your data and information should be done today and shouldn’t be left for tomorrow, as vicious cyber-attacks are happening every second.
Please feel free to add more on cyber attack statistics in the comments below, which will help others get some crucial information.