Tor Browser→ Download for PC [Windows 32 & 64-bit, Free]
Browse the internet with ease with this browser option
4 min. read
Updated on
Read our disclosure page to find out how can you help Windows Report sustain the editorial team. Read more
Key notes
- Tor is one of the most secure browsers out there and is available for download on all major operating systems, including Windows.
- You can download the Tor installer from the official website and get done with the whole process in less than a few minutes.
- Also, find out why you should use the Tor browser.
Tor Browser is a tool that has been designed to preserve your privacy online by masking who you are and where you are connecting.
For people who might want privacy and occasional anonymity, the Tor browser provides an efficient platform and an easy way to browse on the Tor network.
Tor browser works by rebounding traffic around a global network of servers which it calls ‘onion routers’. In Onion Routing, thick layers of encryption make it impossible to trace messages back to the point of origin.
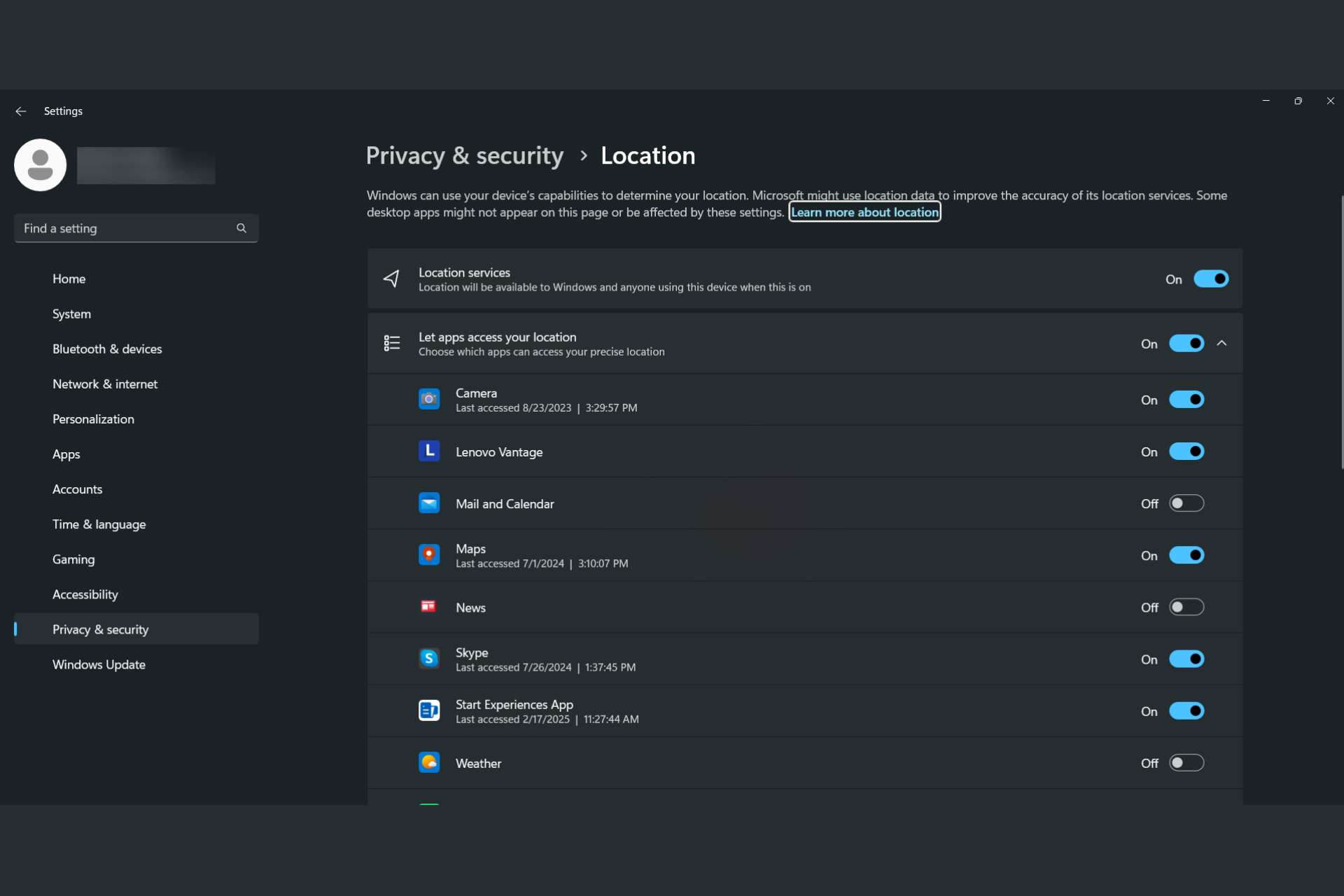
This means that not only is your identity concealed from the sites you are trying to connect to. It also makes it impossible for anyone to intercept and read the communication en route.
Due to its unprecedented levels of privacy, the Tor browser has garnered a large audience base and is being used globally by people from different sectors.
Individuals use Tor to keep websites from tracking them, corporations use Tor to protect sensitive procurements patterns from eavesdroppers and conduct competitive analysis.
Journalists use Tor to effectively communicate with whistleblowers, and the government uses Tor to ensure safe communications between diplomats.
Quick Tip:
If you want privacy without compromising on versatility and the freedom to create your own workspace with extensions, add-ons, and integrations, try Opera One instead.
It’s a Chromium-based browser with a similar level of security to Tor, with a built-in VPN and an anti-tracking feature. It’s lighter than Tor and is compatible with more devices, including iOS.

Opera One
Benefit from online security with unlimited VPN bandwidth, secure page filtering, anti-tracking, and many more.Here are 5 main reasons why we like Opera One so much:
- There are no ad or tracking scripts and third parties can’t collect user data to generate specific user profiles.
- The browser comes with a built-in privacy-focused search engine but you can use whatever search engine you want.
- The built-in VPN fully encrypts your connection.
- You can fully personalize the browser (wallpaper, home screen, download pages included).
- Files get downloaded much faster compared to other browsers.
So, if you’re curious to see what Opera One offers, download it on your PC and give it a try.
Is Tor Browser available for Windows 10/11?
Yes, the Tor browser is available for download and installation on both Windows 11 and Windows 10. It works seamlessly on both iterations, so you shouldn’t face any trouble.
Also, there’s a separate download link for the Windows OS on the official website, along with that for Mac, Linux, and Android.
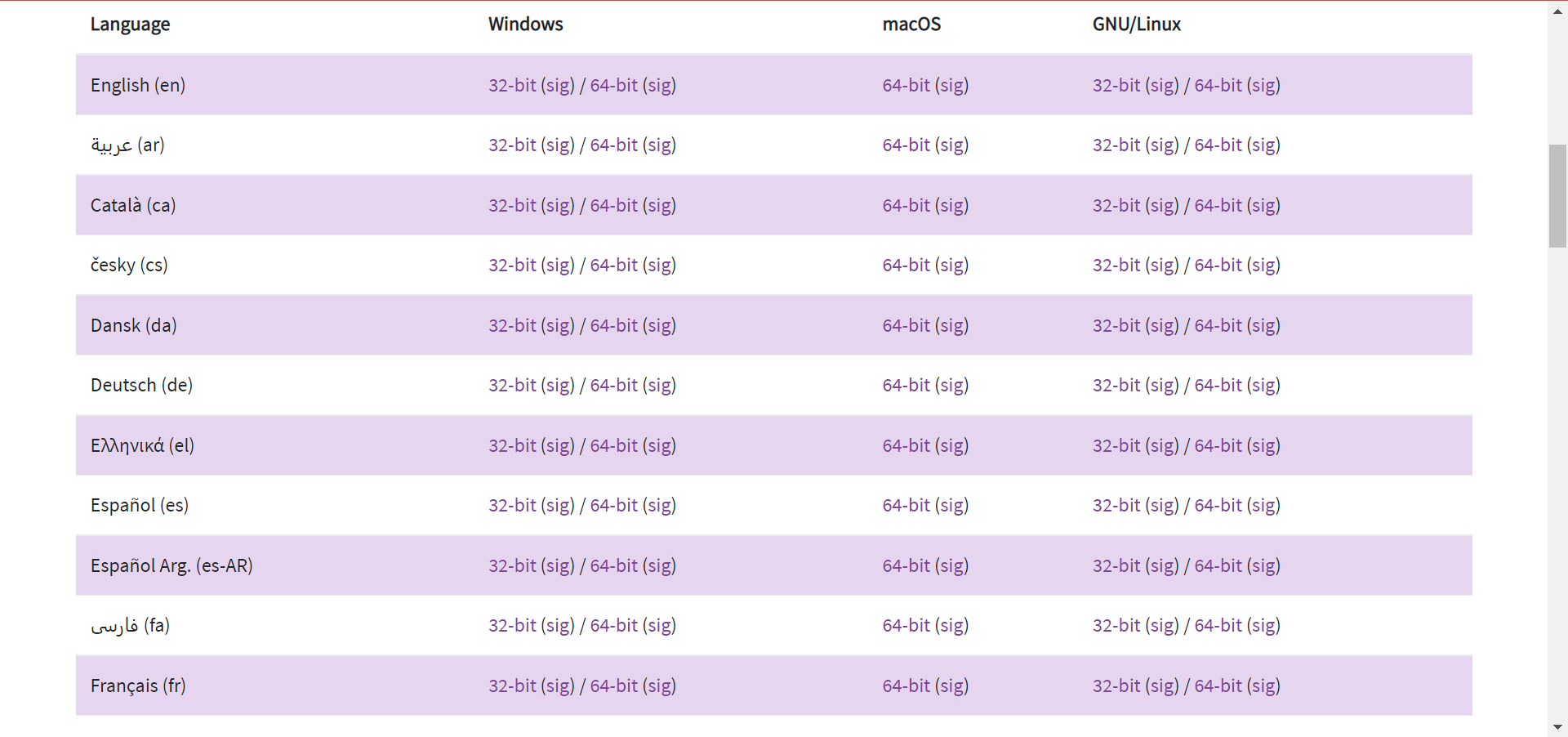
Is Tor available for 64/32 bit on PC?
Yes, the Tor browser is available for download on both 64/32 bit versions in Windows 10/11 and the links for both are available on the website.
In addition to that, the browser is also available in 36 different languages to cater to a larger set of users, and more are to be added soon.
Why should I use the Tor browser?
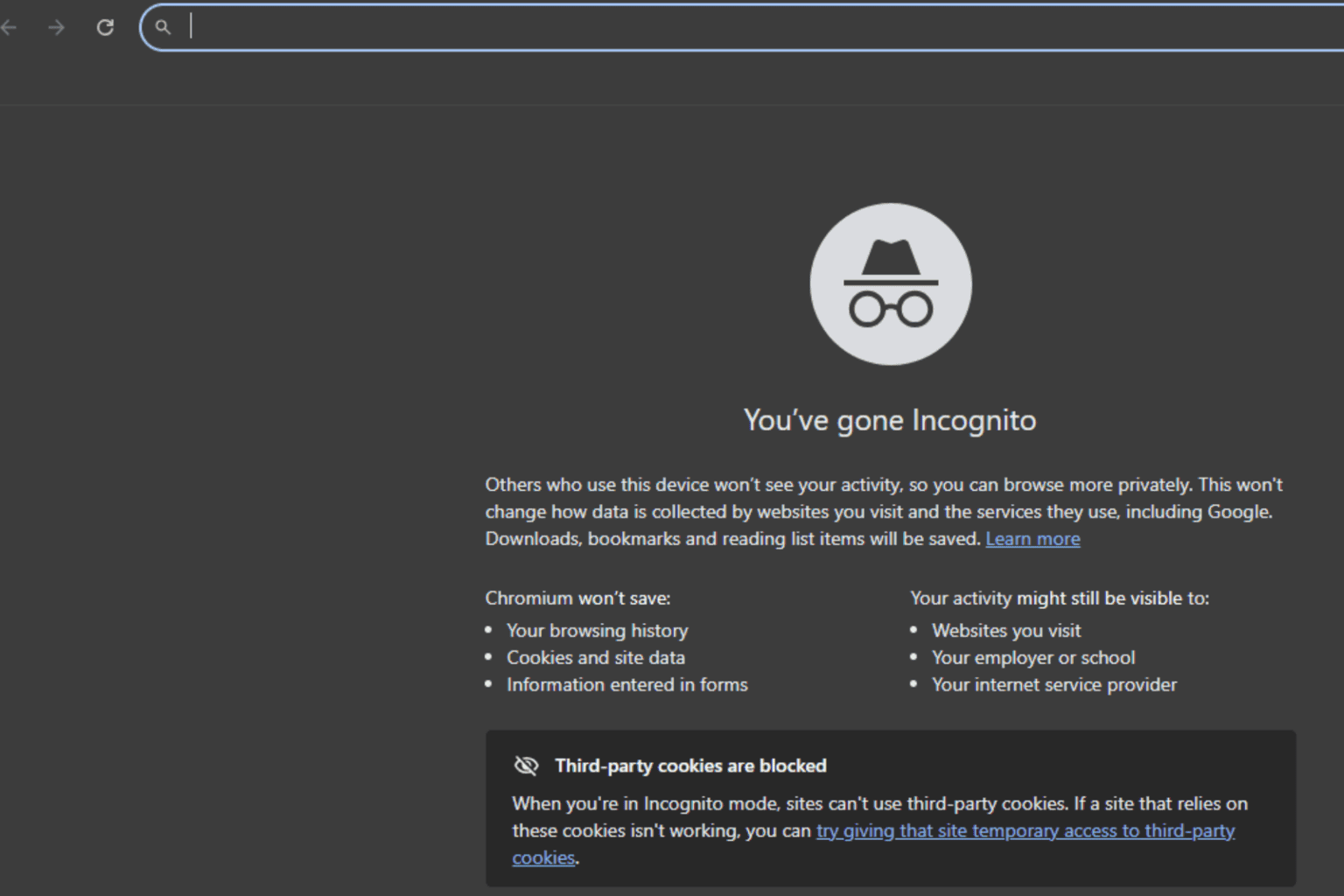
Given the advanced working mechanism, Tor has remained quite user-friendly and is easy to use. Also, it’s believed to be one of the safest browsers. Tor doesn’t share your data with the websites or store the cookies, making it difficult to track your online activity.
And the best of all, Tor is free to use. Besides, it allows users to access the dark web, though we recommend that you follow extreme caution.
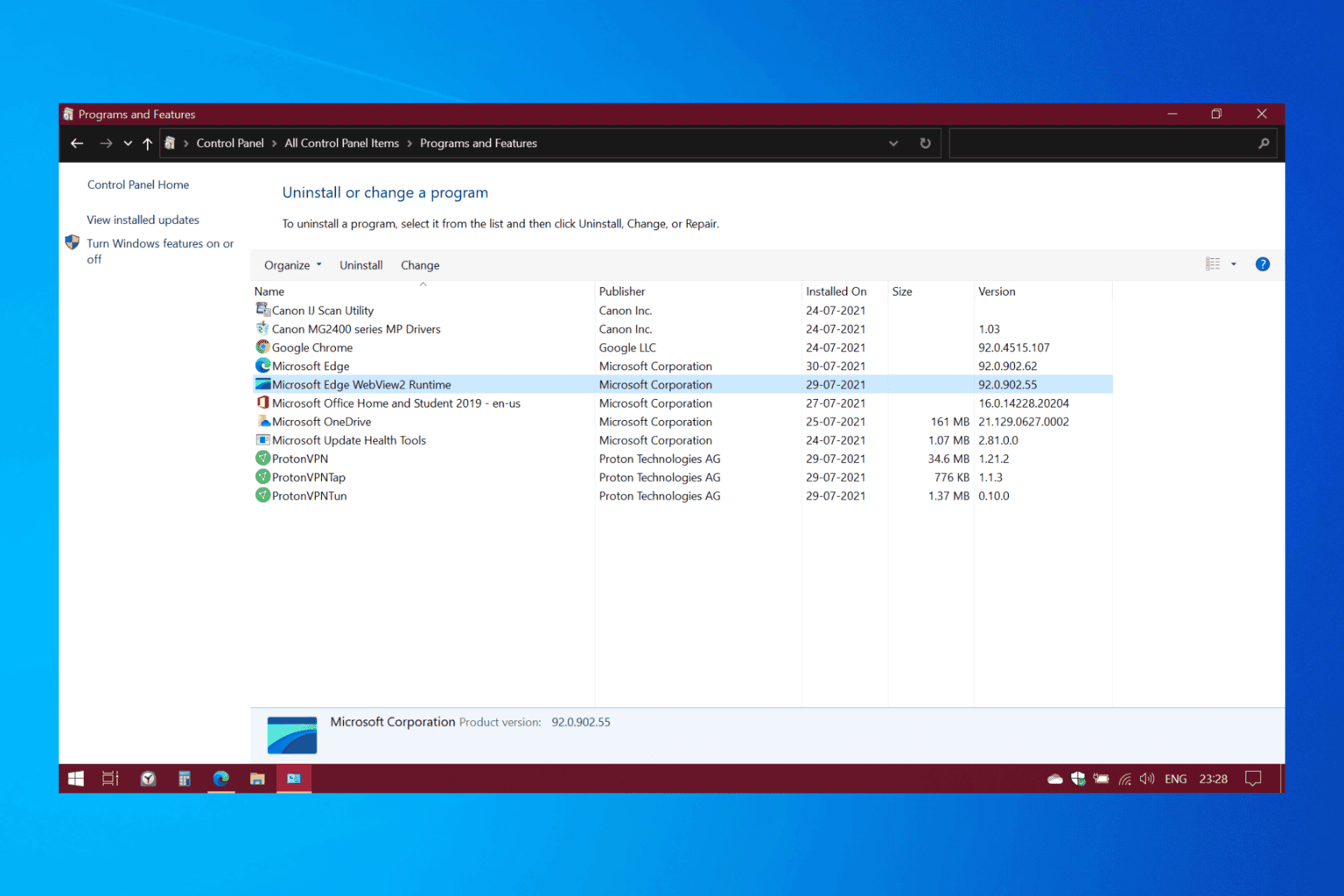
How do I download Tor Browser on Windows 10/11?
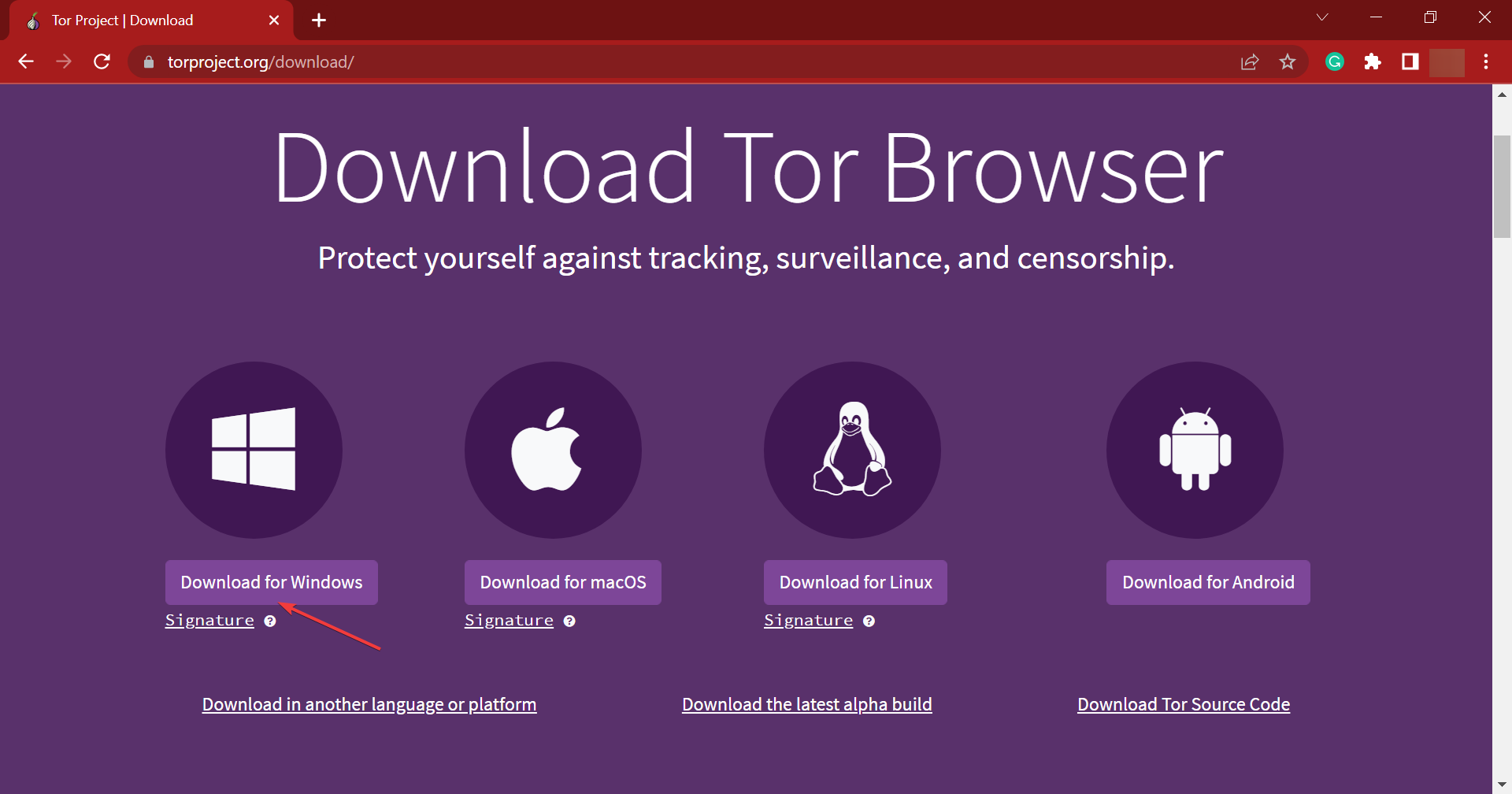
1. Open any safe and reliable browser.
2. Navigate to Tor’s download page.
3. Now, click on the Download for Windows button, and wait for the Tor installer to download.
Download Tor Browser for Windows
Tor helps you protect your online privacy from prying eyes. You can find below step-by-step instructions for downloading Tor Browser for Windows 10 and Windows 11.
That’s it! You now have the setup for the Onion browser for Windows 10/11. To find out how to install it, head to the next section.
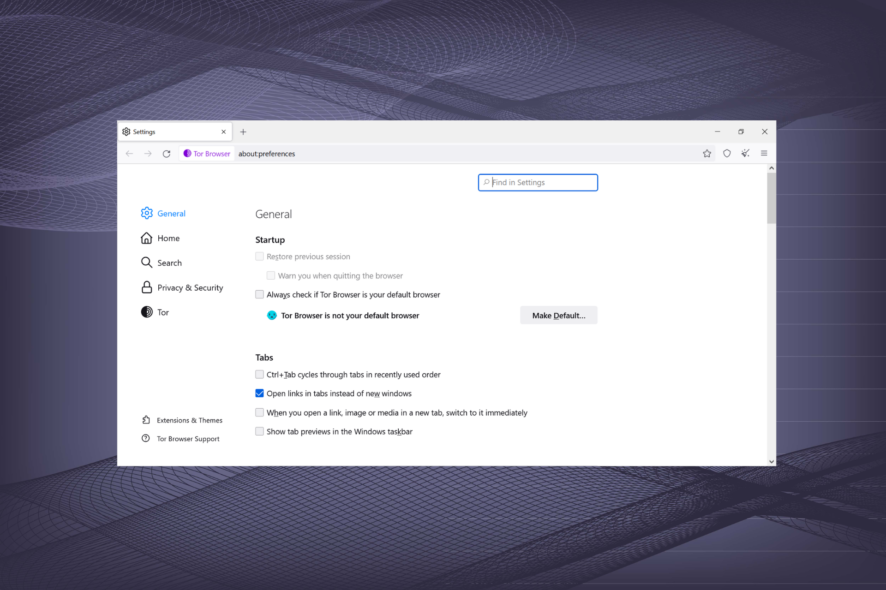
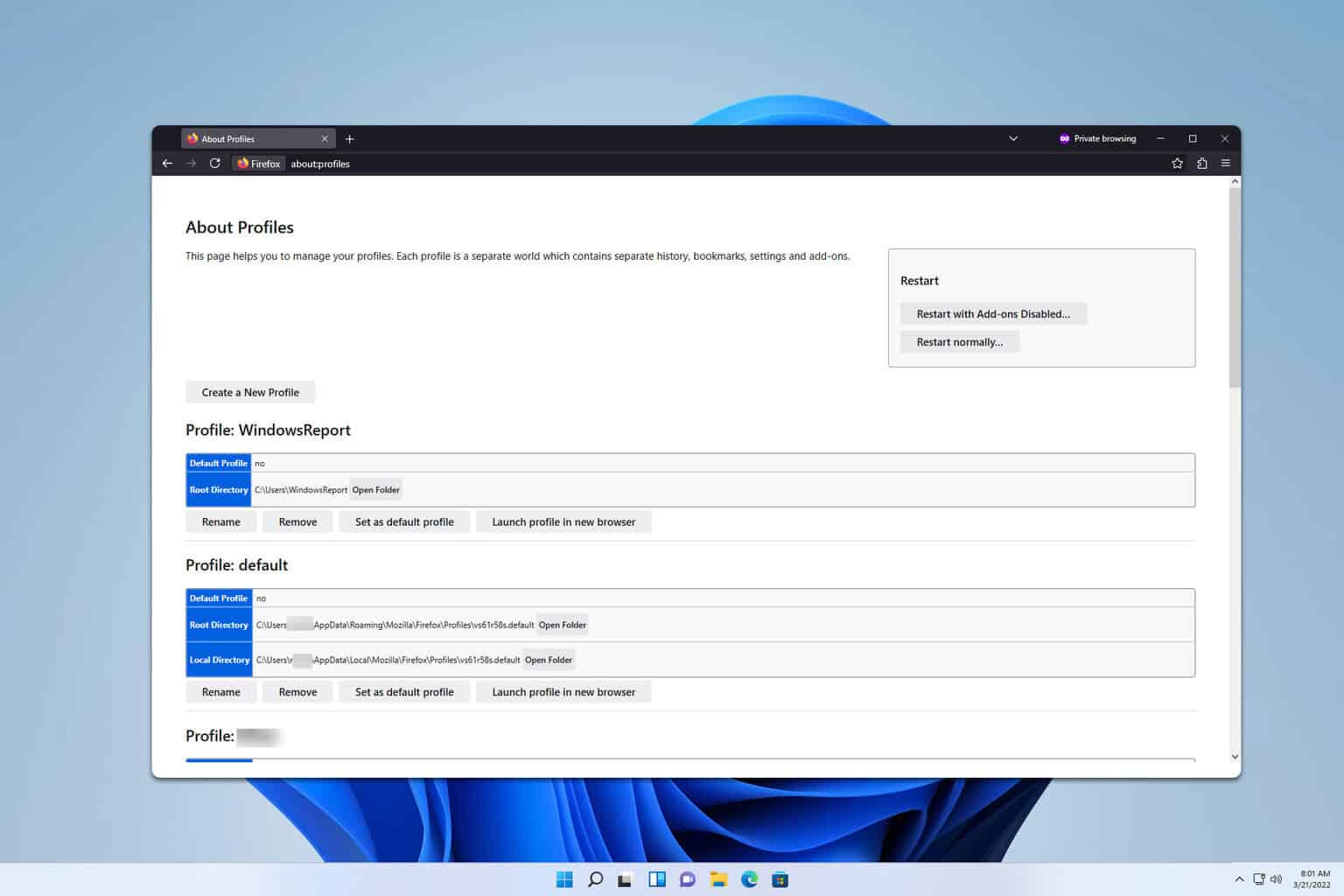
How do I install the Tor Browser?
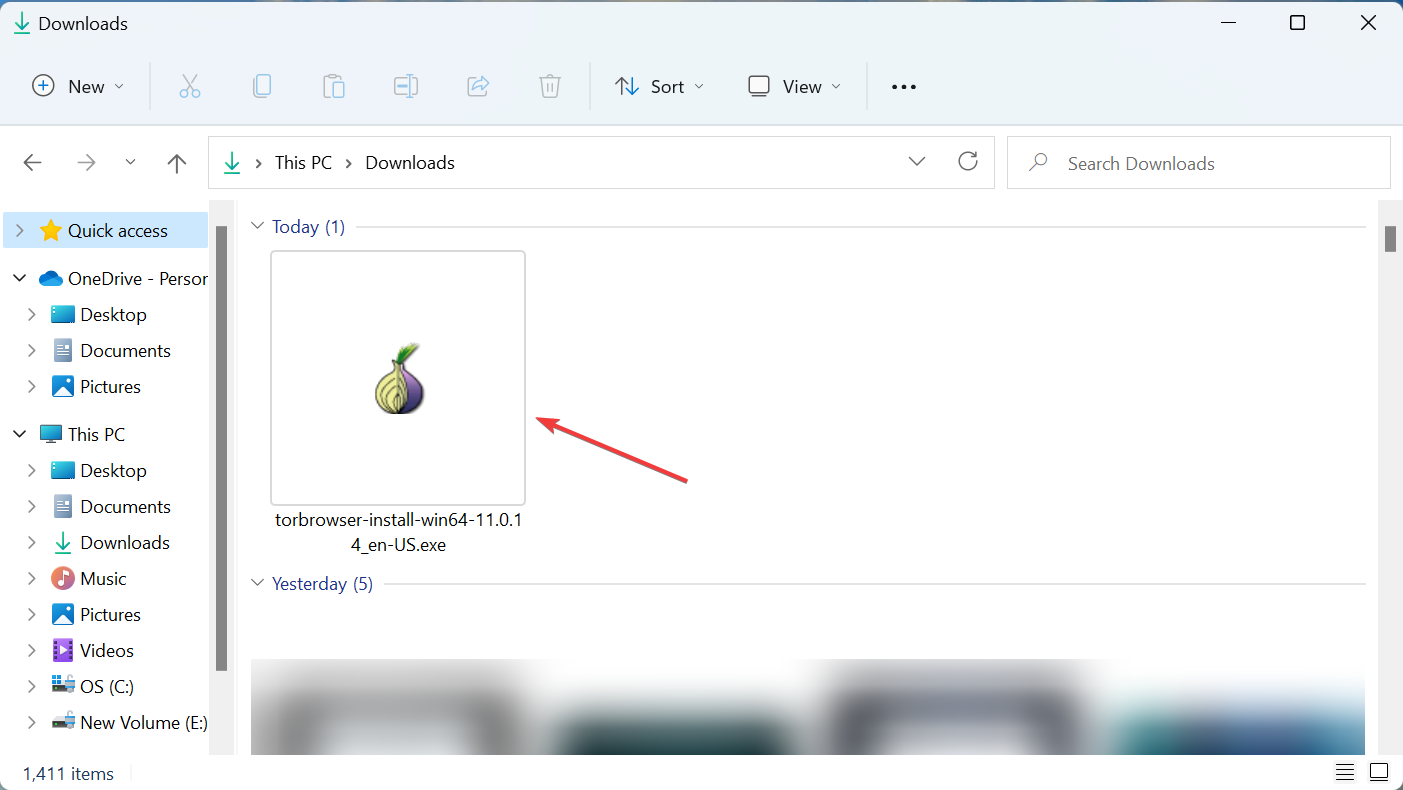
- After the installer is downloaded, navigate to the folder where it is stored, and double-click on it.
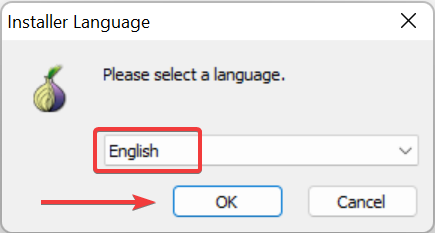
- Select the installation language from the dropdown menu, and click OK.
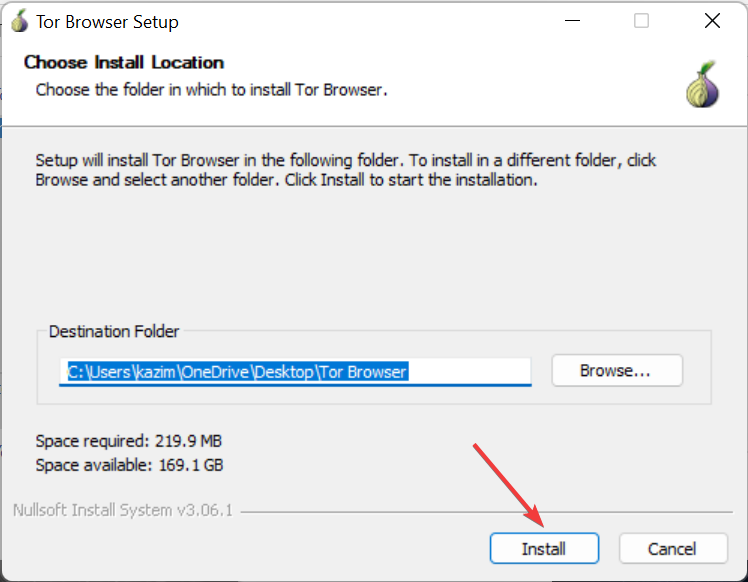
- Now, verify and change the installation folder if required, and then click on Install.
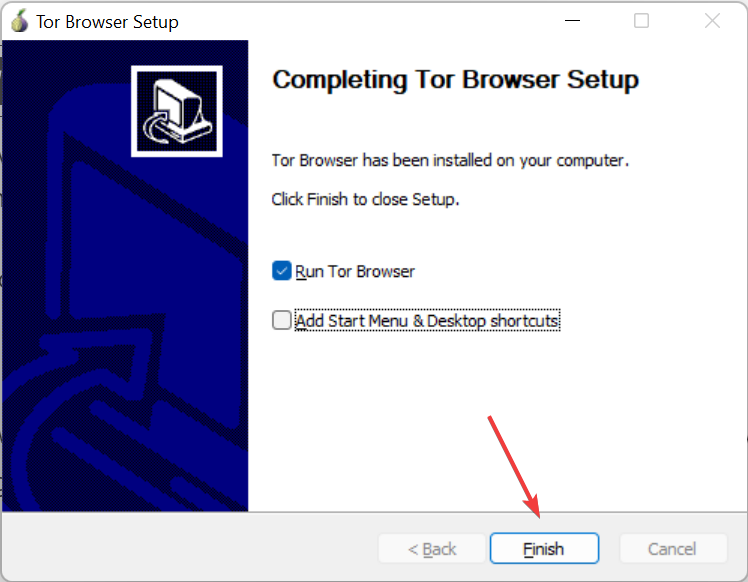
- Once the installation is complete, click on Finish to launch the Tor browser.
The Tor browser will automatically launch now, and you can start using it to browse the web.
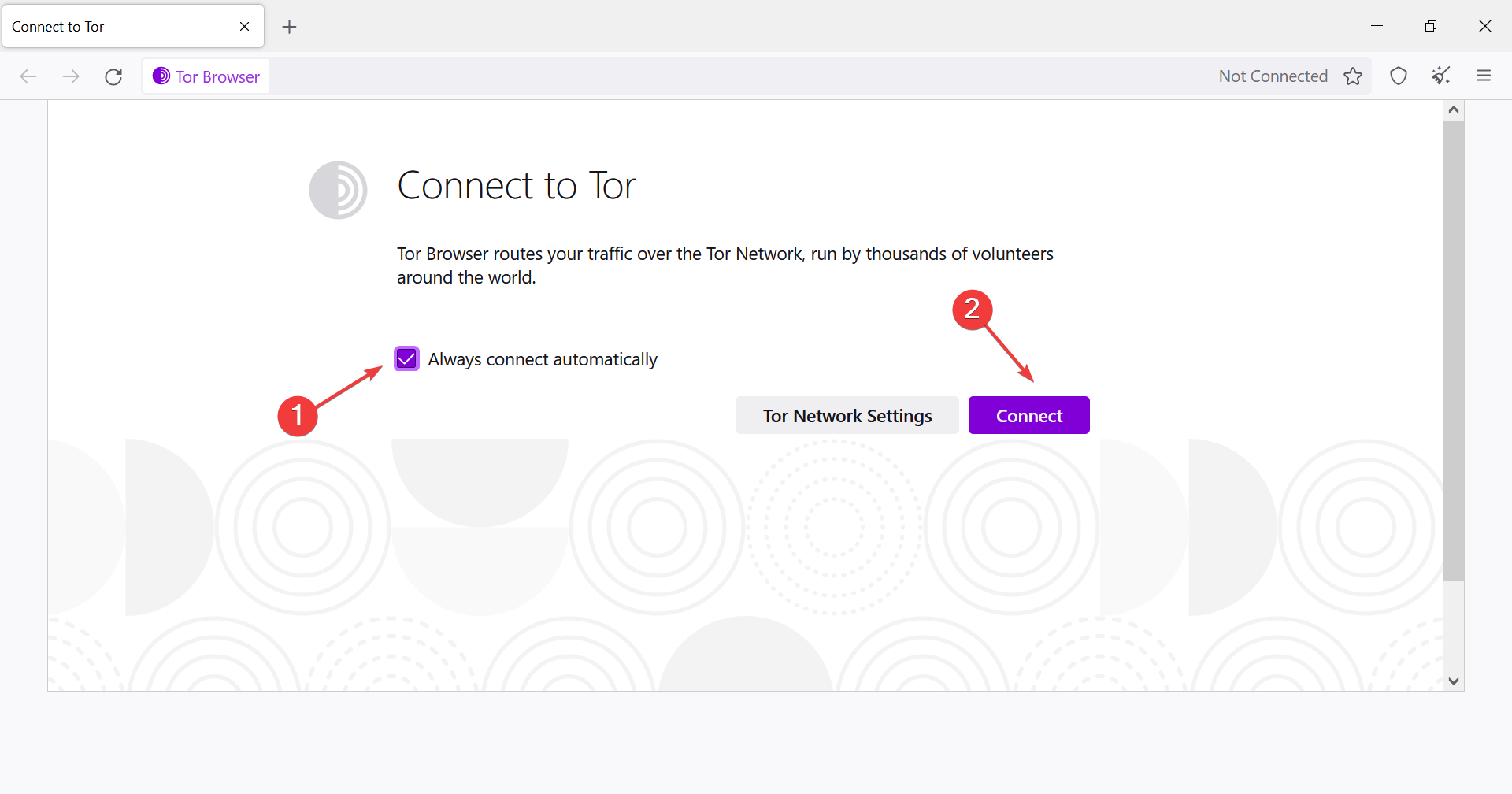
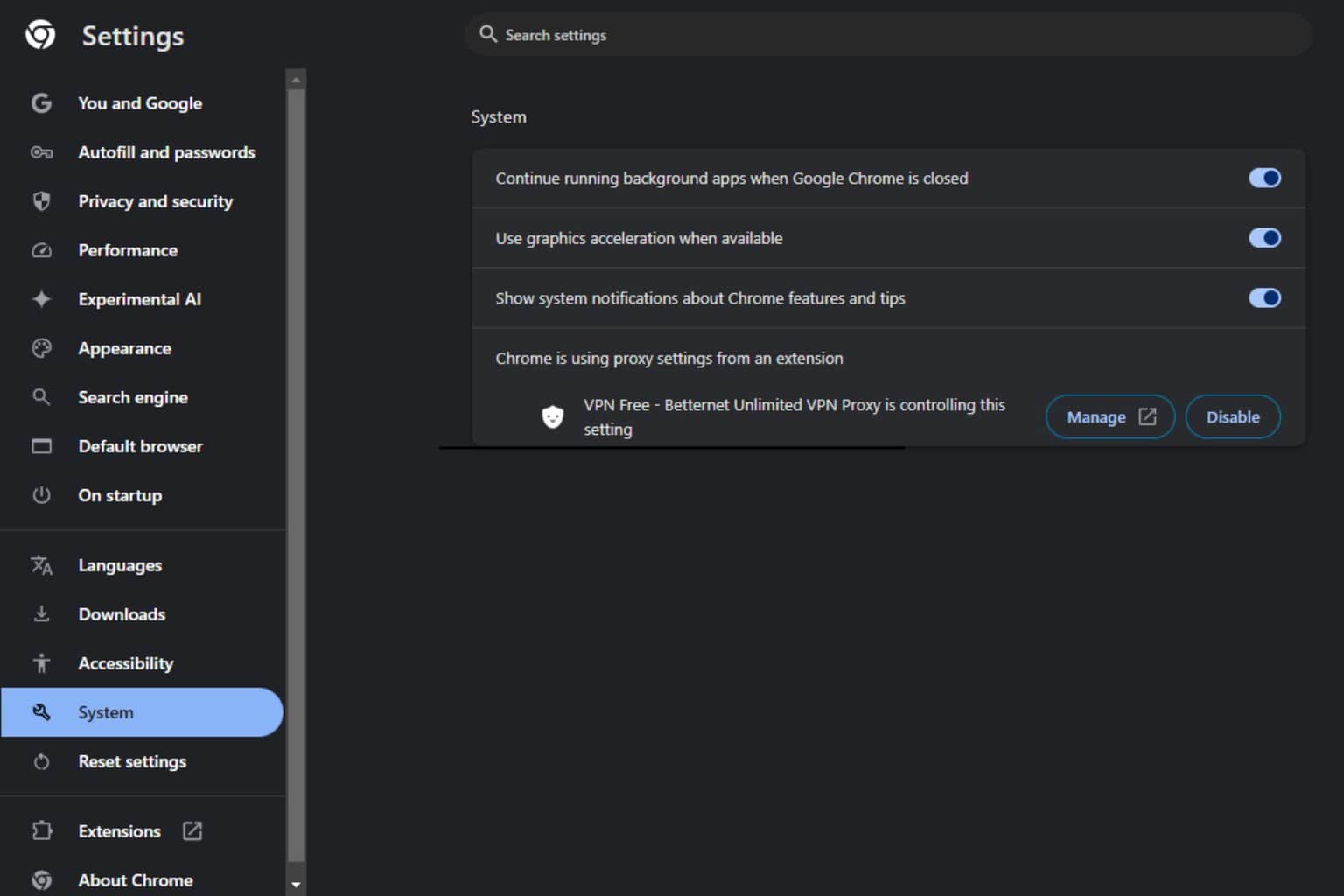
However, before you start, make sure to tick the checkbox for Always connect automatically, and then click on Connect to route your connection through the various nodes for safer browsing.
The Tor Browser or Onion browser for Windows 10/11 works just like any other browser, only that it masks your identity making it hard for people to know who you are and what you are doing online.
Have you already installed the Tor Browser? If so, what are your experiences? Let us hear your opinions in the comments section below.
User forum
1 messages