Hackers are using a Microsoft Office trick to unleash NetSupport RAT
Perception Point is tracking the activity under an operation named Operation PhantomBlu
3 min. read
Published on
Read our disclosure page to find out how can you help Windows Report sustain the editorial team. Read more
Recently, a phishing campaign targeted United States organizations with the intention of deploying NetSupport RAT, a remote access trojan.
Perception Point, an Israeli cybersecurity company, has been tracking the activity under the name Operation PhantomBlu.
A security researcher, Ariel Davidpur, said:
The PhantomBlu operation introduces a nuanced exploitation method, diverging from NetSupport RAT’s typical delivery mechanism by leveraging OLE (Object Linking and Embedding) template manipulation, exploiting Microsoft Office document templates to execute malicious code while evading detection.
What is NetSupport RAT & how does it work?
NetSupport RAT is a malicious variant derived from the legit remote desktop tool NetSupport Manager. It allows cybercriminals to execute a wide range of data-gathering activities on a compromised endpoint.
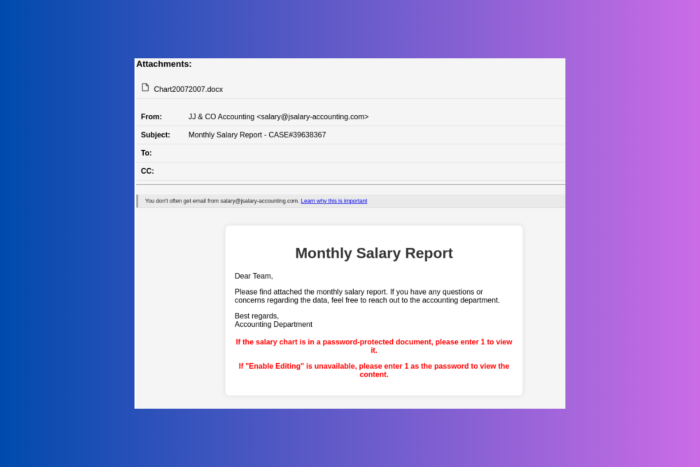
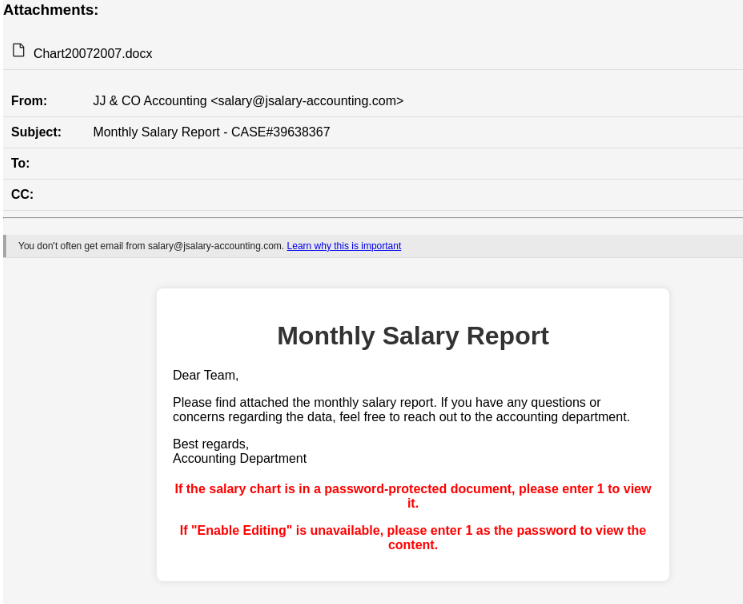
The starting point is a salary-themed phishing email that looks like it has been sent by the accounting team. It asks the recipients to open the attached Microsoft Word document to view the monthly salary report.
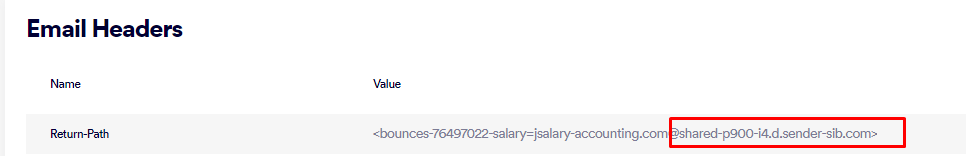
Upon inspecting the email message headers, mainly the Return-Path and Message-ID fields, it was revealed that the hackers used a valid email marketing platform called Brevo (previously called Sendinblue) to send the emails.
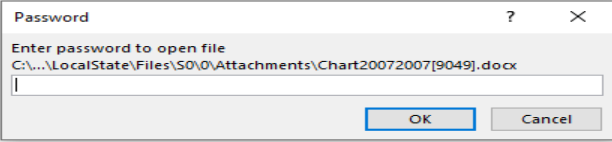
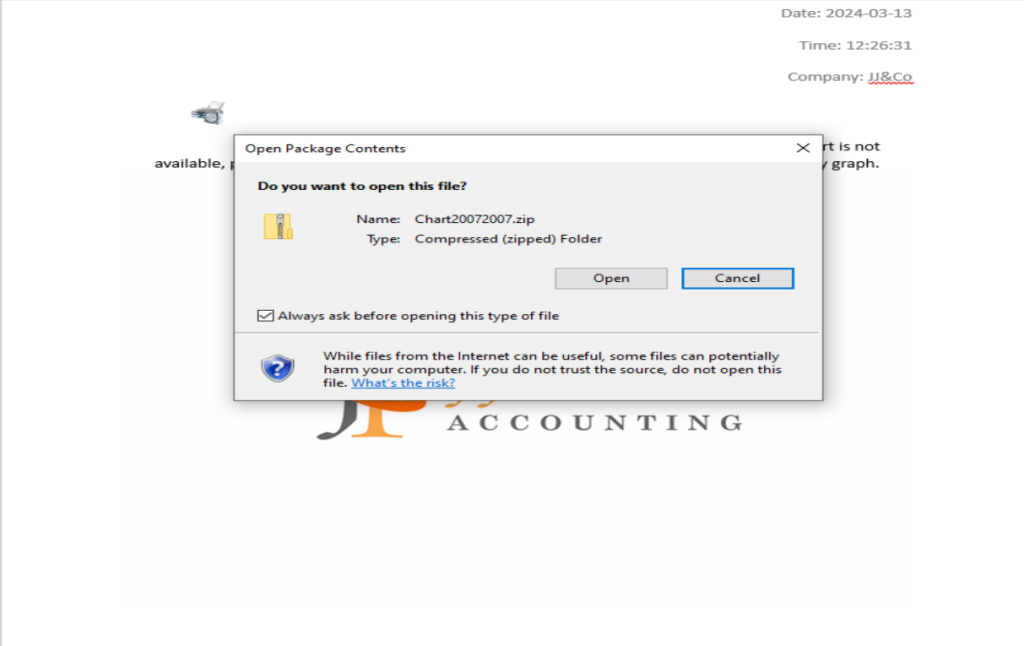
When the victim opens the Word document, it asks them to enter a password mentioned in the email body and enable editing. Then, they double-click the printer icon embedded in the document to view the salary graph.
It will then open a ZIP archive file named Chart20072007.zip, which contains a Windows shortcut file that works as a PowerShell dropper that retrieves and executes a NetSupport RAT binary from a remote server.
Davidpur also mentioned:
By using encrypted .docs to deliver the NetSupport RAT via OLE template and template injection, PhantomBlu marks a departure from the conventional TTPs commonly associated with NetSupport RAT deployments, adding the updated technique showcases PhantomBlu’s innovation in blending sophisticated evasion tactics with social engineering.
This is another instance where threat actors abuse cloud services, such as IBM Cloud, Dropbox, Oracle Cloud Storage, GitHub, and Web 3.0 data-hosting platforms built on the InterPlanetary File System protocol, to generate FUD (fully undetectable) URLs using phishing kits.
These FUD links are easily available on Telegram by vendors like FUDLINKSHOP, XPLOITRVERIFIER, BulletProofLink, and more for a price of around $200 per month for a subscription.
The links are secured behind antibot barriers to filter incoming traffic and make them undetectable. There are tools like HeartSender that make it possible to spread these FUD links on a larger scale.
The phishing campaigns built by hackers could look legit, so it is important to scale through an unknown email before opening attachments to ensure your security.
What are your thoughts on the matter? Share your opinions with readers in the comments section below.








User forum
0 messages