Warning: SquirtDanger malware takes screenshots and steals your passwords
4 min. read
Updated on
Read our disclosure page to find out how can you help Windows Report sustain the editorial team Read more

Palo Alto Networks Unit 42 researchers have discovered a new currency stealer which targets cryptocurrencies and online wallets. Hackers can take action screenshots and steal passwords, download files and even steal the content of cryptocurrency wallets through a new malware from the ComboJack malware family.
Cryptocurrencies are increasing in popularity and value, therefore we can expect such malware to pop up in the near future. This calls out users to gain more security for online crypto wallets.
The Swiss Army Knife Malware called SquirtDanger
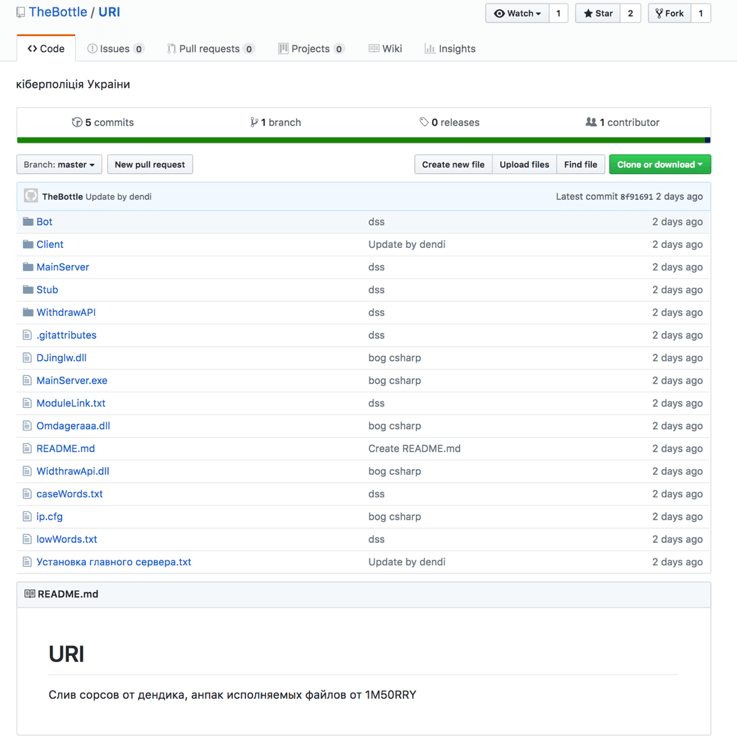
Researchers have related this attack to the prolific Russian malware author aka ‘TheBottle’. Investigating his online activities, researchers found traces that lead to unraveling the actions of a malware family called The Swiss Army Knife. SquirtDanger is a botnet malware and belongs to this malware family.
The attacks are using a DLL file, SquirtDanger.dll, written in C Sharp and come with multiple layers of embedded code. Once SquirtDanger infected a system, a ‘scheduled task’ is set to perform every minute and obtain as much information as possible. The wealth of its functionality allows the malware to do the following:
- Take screenshots
- Send file
- Clear browser cookies
- List processes
- Kill process
- List drives
- Get directory information
- Download file
- Upload file
- Delete file
- Steal wallets
- Steal browser passwords
- Swap identified wallets in the victim’s clipboard
- Execute file
SquirtDanger used ‘raw TCP connections’ for initiating network communications to a remote C&C server and researchers were able to extract an embedded identifier from roughly 400 SquirtDanger samples. Digging in, they’ve discovered a code repository which coincided with the capabilities and style of the samples observed.
You can read full information based on the in-depth analysis of Palo Alto Networks Unit 42.
This malware can steal cryptocurrency wallets
SquirtDanger has already infected individuals and organizations around the world, including a Turkish university, an African telecommunications company, and a Singaporean internet service provider. This smartly developed malware has the ability to seek out wallets for various cryptocurrencies, including the following:
- Bitcoin
- Ethereum
- Monero
- Litecoin
- Bytecoin
- Dash
Best ways to secure your crypto-trading
Keeping your system updated is probably the first most important step to secure your digital work. After several attacks, most companies have developed anti-malware tools and updates to protect from or remove malicious attacks.
If you consider using crypto-trading, it’s impetuous to install a high-quality security software. You can choose one of the best tools available at the moment by reading this article: 5 best security software for crypto-trading to secure your wallet.
We also advise to use strong passwords, keep your valuable data safe on a physical device, like a USB drive that is not connected to the internet. Use two-factor authentication and the enhanced security protocols for your email address, like Gmail’s new confidentiality features.
Bitdefender is using more advanced behavior-based technologies, and this helps the software detect 99% of unknown threats. Bitdefender GravityZone offers high-quality business security, and it’s the ideal tool for your crypto trading.
A highly reliable VPN can hide your IP and replace it with another one from its own network this way preventing third parties to track you online while you are doing your transactions. CyberGhost is one of the leaders in the VPN market and the effective solution that will successfully secure your crypto trading online.
Nevertheless, keep your eyes open and increase your level of awareness for cryptocurrency scams that take advantage of small things to step into your account. Stay informed and updated with cyber-security news.
RELATED STORIES TO CHECK OUT:
- Upcoming Firefox update blocks in-browser cryptojackers
- Here are 6 best VPNs for Bitcoin payment to fully secure your transactions
- BitTorrent client responsible for coin-mining malware affecting over 400,000 PCs
- Outlook vulnerability allows hackers to steal password hashes