Attackers used Office 365 voicemails as phishing bait
2 min. read
Updated on
Read our disclosure page to find out how can you help Windows Report sustain the editorial team Read more
Key notes
- Reports from multiple cybersecurity firms show that Office 365 users are increasingly being targeted with phishing emails.
- Hackers used Oxford University servers to send phishing emails to Office 365 users..
- Phishing attacks are on the rise, and organizations have to get smarter to beat them. Check out our Cybersecurity page for actionable insights!
- Don't forget to visit the Security & Privacy for updates and more.
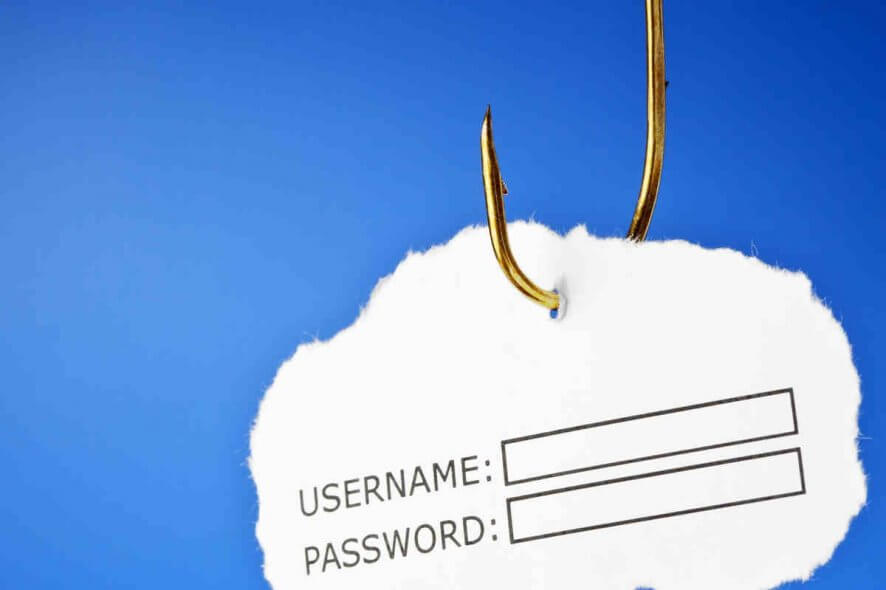
Reports from multiple cybersecurity firms show that Office 365 users are increasingly being targeted with phishing emails.
The phishing attacks are sometimes too sophisticated to detect or stop even using advanced anti-spam filters. That’s partly because cyber criminals are using legitimate domains to send their malicious emails.
An Office 365 phishing campaign that Check Point uncovered recently is enough proof that organizations need to deploy smarter cybersecurity tools to thwart such attacks.
Office 365 voicemail attacks
In this particular Office 365 phishing campaign, targets received email notifications about missed voice messages. The emails prompted them to click a button under the impression that it would take them to their legitimate Office 365 accounts.
But clicking the link redirects the user to a phishing page disguised as the genuine Office 365 sign-in page. This is where the attackers steal the victim’s Office 365 login credentials.
What’s surprising here is the fact that anti-phishing tools should usually detect email links with patterns like that. So, you may wonder how exactly these attackers deploy such malicious redirects and payloads undetected.
The answer is simple: the bad actors include legitimate platforms in their plans. In this case, the attackers sent harmful emails from addresses belonging to genuine servers in the University of Oxford (UK).
Using legitimate Oxford SMTP servers allowed the attackers to pass the reputation check for the sender domain. In addition, there was no need to compromise actual email accounts to send phishing emails because they could generate as many email addresses as they wanted.
However, there are several steps you can take to protect your employees from phishing attacks:
- Educate your staff about phishing and password safety.
- Install email-scanning software that can detect messages with malicious payloads.
- Keep your operating system update. Most importantly, always install Patch Tuesday security updates from Microsoft (they’re free of charge).
- Install an up-to-date antivirus solution.
Does your organization use Office 365? How do you deal with the ever-growing phishing threat? Feel free to share your tricks and methods via the comments section below.
[wl_navigator]