Patch Tuesday July 2021: Update Highlights and Known Issues
5 min. read
Updated on
Read our disclosure page to find out how can you help Windows Report sustain the editorial team Read more
Microsoft finally rolled out the July 2021 Patch Tuesday updates, on the second Tuesday of the month, on the 13th of July.
It has become common practice for the Redmond tech company to release a brand new batch of updates every month, with the goal of improving the overall functionality of the OS and fixing existing bugs.
This month’s updates are all about improving the security of most Windows components and apps. If you want to install the latest updates, you can use our direct download links.
We already covered the key changes in these posts. Do check them out to learn what’s new:
- KB5004237 addresses Primary Refresh Tokens vulnerability
- Patch Tuesday July 2021: These are the CRITICAL CVEs released
- How to download KB5004945 and fix the PrintNightmare vulnerability
As you already know, Microsoft releases different Patch Tuesday updates for all the Windows 10 versions currently supported.
For more information on the latest updates, check out our Windows 10 Patch Tuesday update history page.
What are the main changes in the July Patch Tuesday updates?
Microsoft Products and services updates
Across all major versions of Windows 10 that have received cumulative updates, ranging from Windows 10 original version to Windows 10 v21H1.
Here are the main highlights brought by the July Patch Tuesday updates according to Microsoft:
- Updates for verifying usernames and passwords.
- Updates to improve security when Windows performs basic operations.
- Updates an issue that might make printing to certain printers difficult. This issue affects various brands and models, but primarily receipt or label printers that connect using a USB port.
Patch Tuesday list of CVEs
The July 2021 edition of the already famous Patch Tuesday contains a total of 116 CVEs, a much higher number if we compare it to last month when the tech company only released 49.
- Adobe Products
Adobe addressed 26 CVEs this Patch Tuesday, and 22 of them are rated as critical severity impacting Acrobat and Reader, Adobe Framemaker, Illustrator, Dimension, and Adobe Bridge products.
- Microsoft product vulnerabilities
The rest of this month’s vulnerabilities were found affecting Microsoft products, 15 of which were rated as Critical, while the rest are rated Important.
What are the best practices for Patch Tuesday?
There are a few things that you can do in order to make sure that your computer installs the latest Patch Tuesday updates without any issues. We all know that Windows updates often trigger errors.
In extreme cases, they may even render your PC completely unusable. Follow these tips to make sure the update install process goes as smoothly as possible.
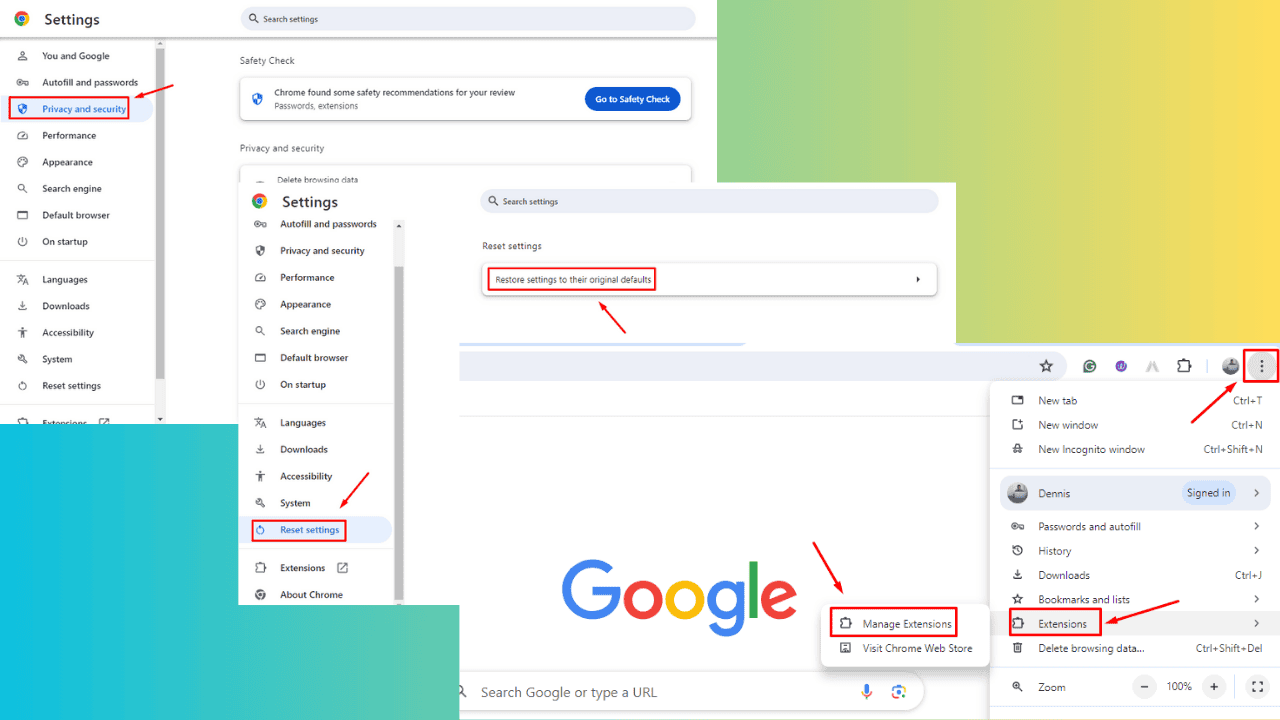
How to download the latest PT updates
While the Patch Tuesday updates are true of greater significance compared to other patches that Microsoft regularly releases, installing them is done in pretty much the same way.
This means that you can perform the actions by following these steps:
- Make sure that no other apps are running in the background.
- Go to one of these sources to get the updates:
- The Windows Update menu
- The Windows Update Catalog (This allows for individual updates to be downloaded one by one manually)
- The Windows Server Update Service (WSUS)
- A Group Policy created by a network administrator
- After downloading the updates, make sure nothing interrupts the update process until it is finished.
- Reboot your PC once the updates are complete to finalize the installation.
Exploit Wednesday & Uninstall Thursday
Right after Patch Tuesday, hackers try to exploit the vulnerabilities left unpatched by Microsoft. This leads to an increase in the number of cyber-attacks.
On the other hand, many users often decide to uninstall the Patch Tuesday updates a few hours after install due to the large number of issues they triggered — hence the name Uninstall Thursday.
Check out this guide to learn more about how to stay safe after Patch Tuesday and make sure the updates don’t brick your computer.
Patch Tuesday: All your Questions Answered
- When is Patch Tuesday released?
Microsoft rolls out new Patch Tuesday updates on the second Tuesday of each month. The next Patch Tuesday Update is expected to arrive on June 8, 2021.
- How does Patch Tuesday work?
We already answered this question in this quick guide. Do check it out to learn more about the mechanisms behind Patch Tuesday.
- What is the bandwidth impact of Patch Tuesday?
When actively downloading updates, you may experience slow connection issues on your Windows 10 computer. This happens especially when updating multiple PCs at the same time.
The solution is to distribute the updates locally via WSUS. This means downloading the updates from Microsoft Servers.
Then, your Windows 10 computers can share the updates in a peer-to-peer manner over the local network resulting in a faster update process.
Patch Tuesday Troubleshooting
Oftentimes, Patch Tuesday updates trigger various errors on Windows computers. These may range from minor glitches to technical issues that may render your computer unusable.
We covered extensively Patch Tuesday issues we compiled hundreds of troubleshooting guides to help you solve these problems quickly.