Perimeter 81: A Simple Remote Access Solution To Use
Key notes
- Perimeter 81 is a remote access solution that will enhance your business' cybersecurity as well as the working functionality.
- This tool has advanced data encryption features as well as cloud security implementation.
- The software allows you to connect across a range of devices and locations, in any moment.

In an era where work from home has become an anchor point of the economy, it’s never been more important that companies maintain rigorous cybersecurity every step of the way.
Imagine you could provide employees with seamless, secure, remote access to your corporate network or shared resources anywhere in the world, at any time.
And all that without the need for oodles of complicated tech and overly difficult networks. Always-on VPN offers a key component in achieving that dream.
Many people have only experienced VPNs as something gamers use, and it’s common to perceive it as some complex, jargon-packed environment only those working in IT could utilize.
Many modern, intuitive solutions exist to help streamline companies’ use of VPNs, however, while still enabling staff to concentrate on their core work.
Today we take a look at Perimeter 81 and how it can enhance business cybersecurity as well as work functionality.
What is Perimeter 81 and how can it help you?
Remote access VPNs like Perimeter 81 allow employees to access company data and infrastructure in the cloud but using a fully secured connection that cuts down on cybersecurity risk.
The user experience is as if they’re in the office, using local servers. This allows a great balance of security and user experience.
Until recently, most network securities was physical and site-centric, unable to adapt easily to remote working.
Cloud environments and SaaS services were either inaccessible unless in the office, or non-existent.
In the fast shift to work from home, this amounted to vulnerability to cyber attacks over unsecured home connections, while still failing to support staff and allow access to key work resources.
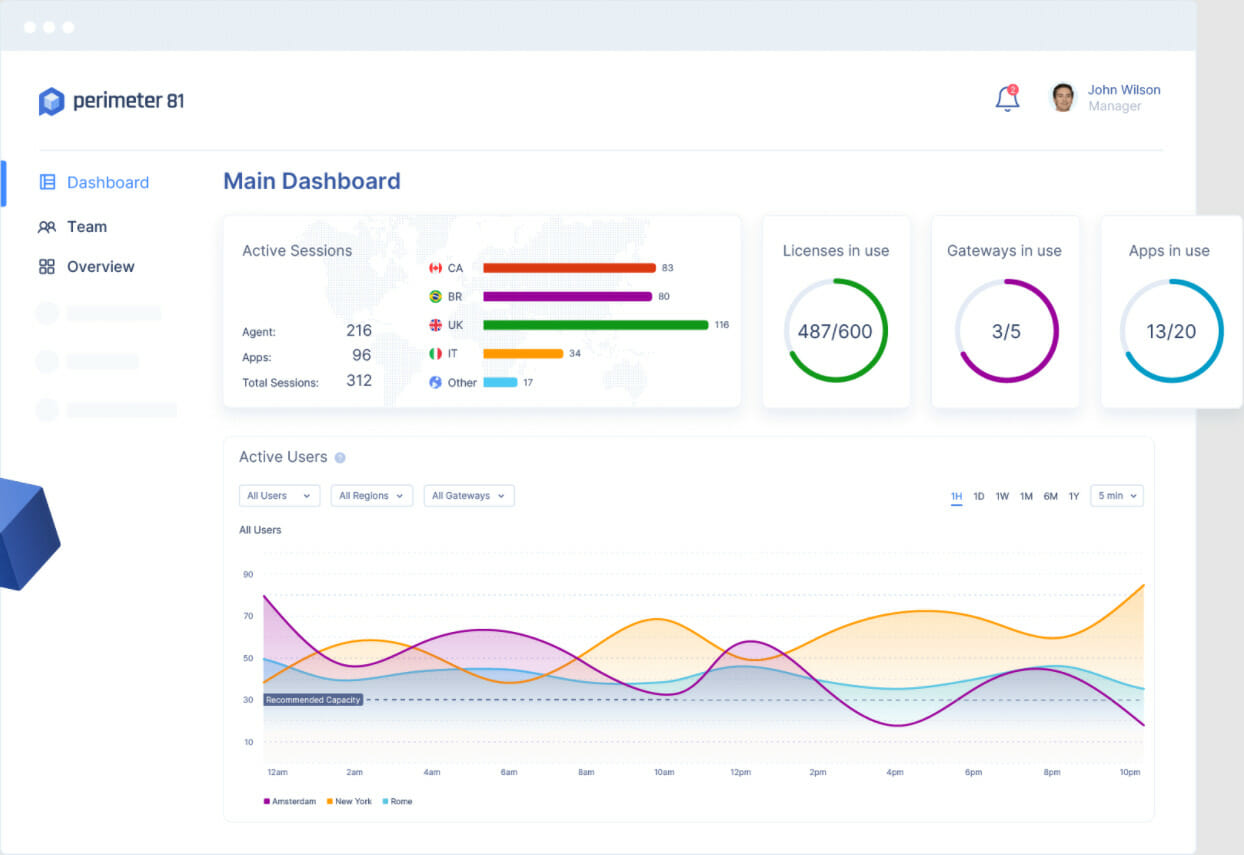
Perimeter 81 offers instant deployment, unified management, and 360-degree visibility to ensure a fast, safe, scalable product that enhances security and helps staff work productively too.

Perimeter 81
Take the full benefit from this cloud-based VPN privacy that ensures data security for anyone.What are the key features of Perimeter 81?
1. Data Encryption
Through top-end encryption and tunneling, Perimeter 81 ensures transmitted data is safe, no matter where or what device sends it. Only authorized connections are allowed
2. Cloud security
Access point security into the network is a key concern of using cloud solutions. Perimeter 81 helps secure access on top of the cloud environment, enhancing security.
3. Safe, fully remote access
Despite these top-end security features, Perimeter 81 allows employees to connect across a range of devices and locations, at any time of the day.
As a remote access always-on VPN, employees can securely access the company’s private network and share data safely, even on public networks.
How can I use Perimeter 81?
Deploying the software will look a little different, organization dependant. However, here’s a rough look at the steps to use Perimeter 81:
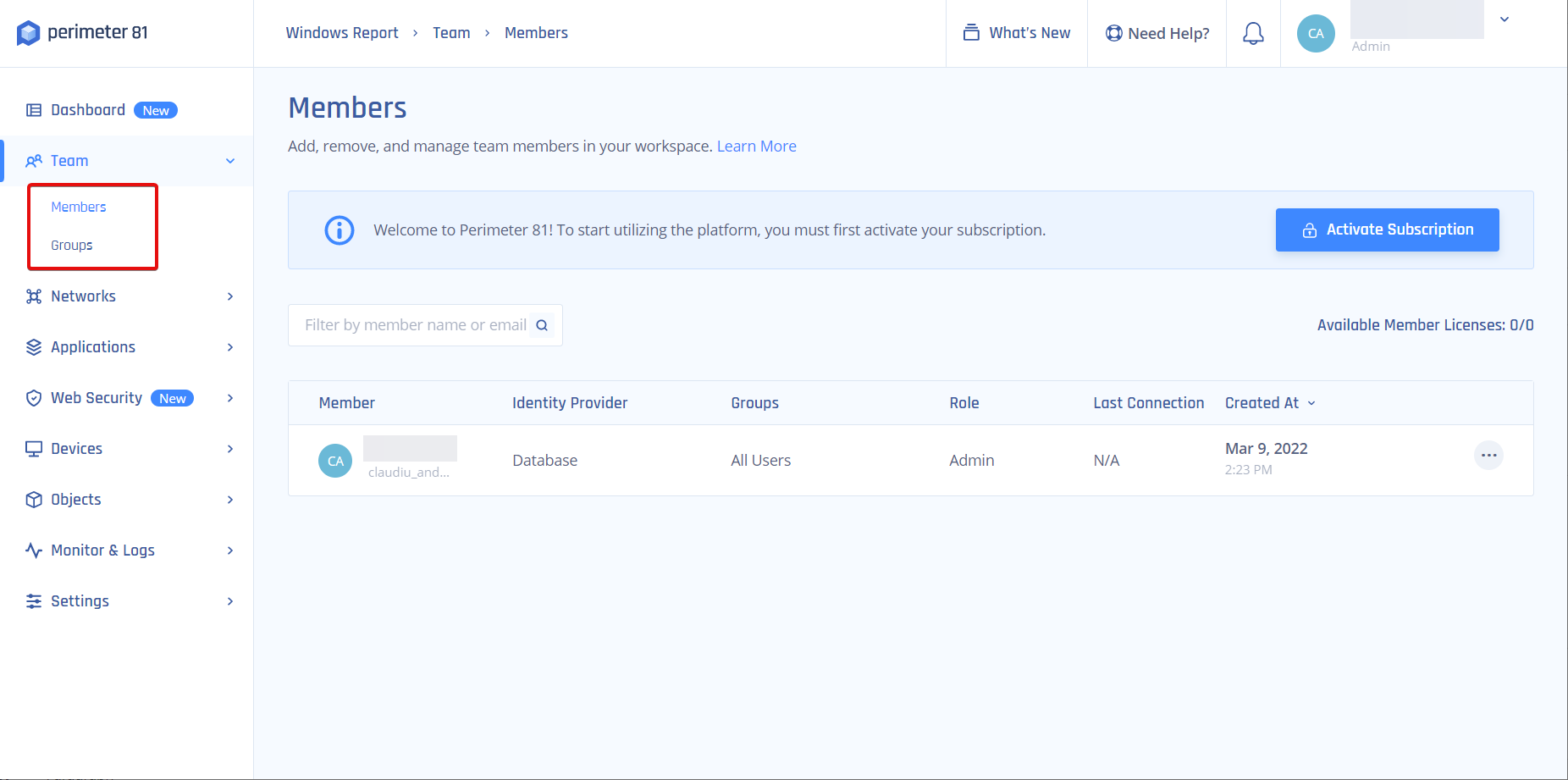
1. Establish the management platform on the cloud
Here, your dedicated IT personnel will manage the team, setting networks and permissions. They can also monitor network activity here.
The overall interface is intuitive, and Single sign-on integrations, two-factor authentication, and mobile support are built-in and customizable to suit the organization.
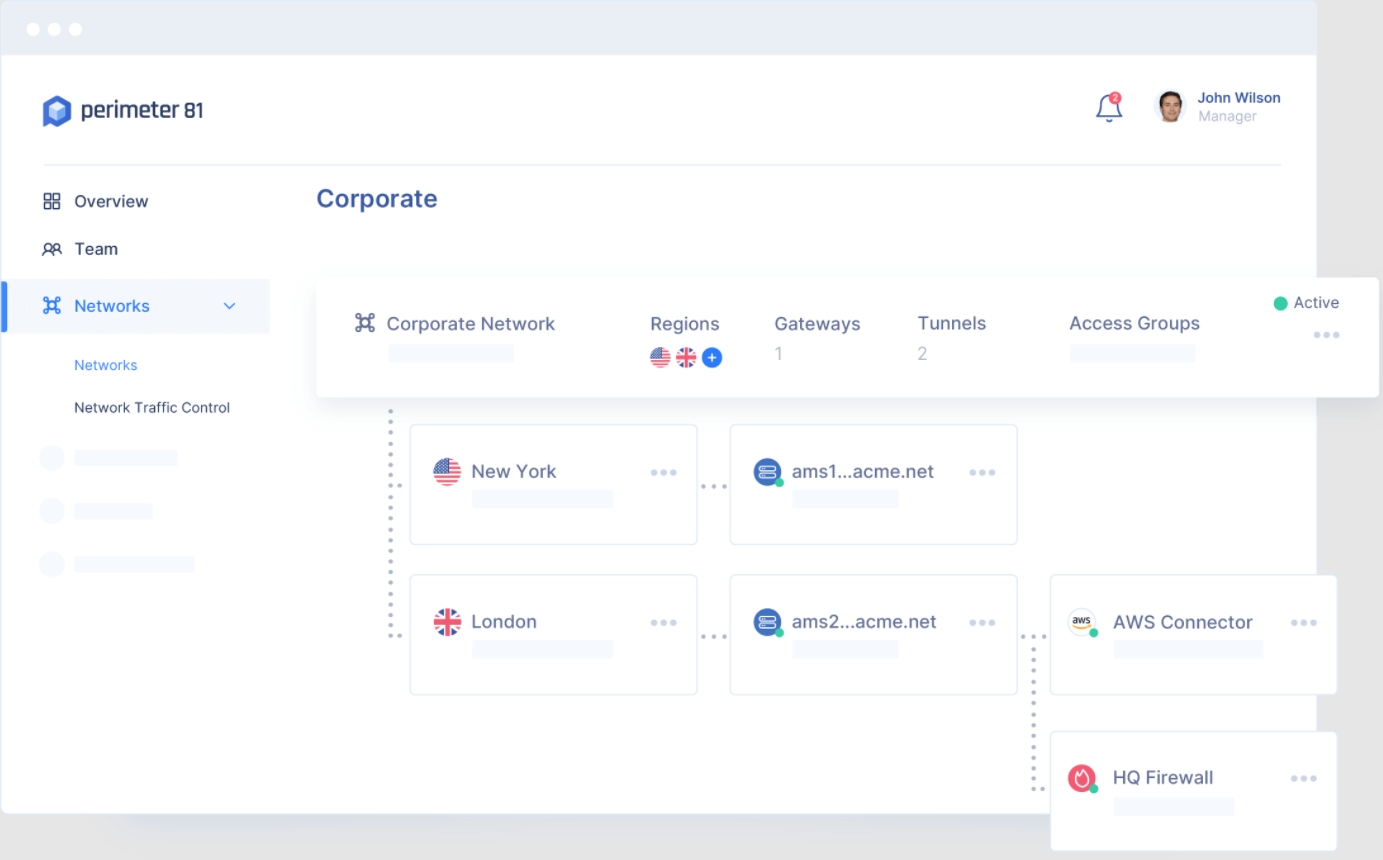
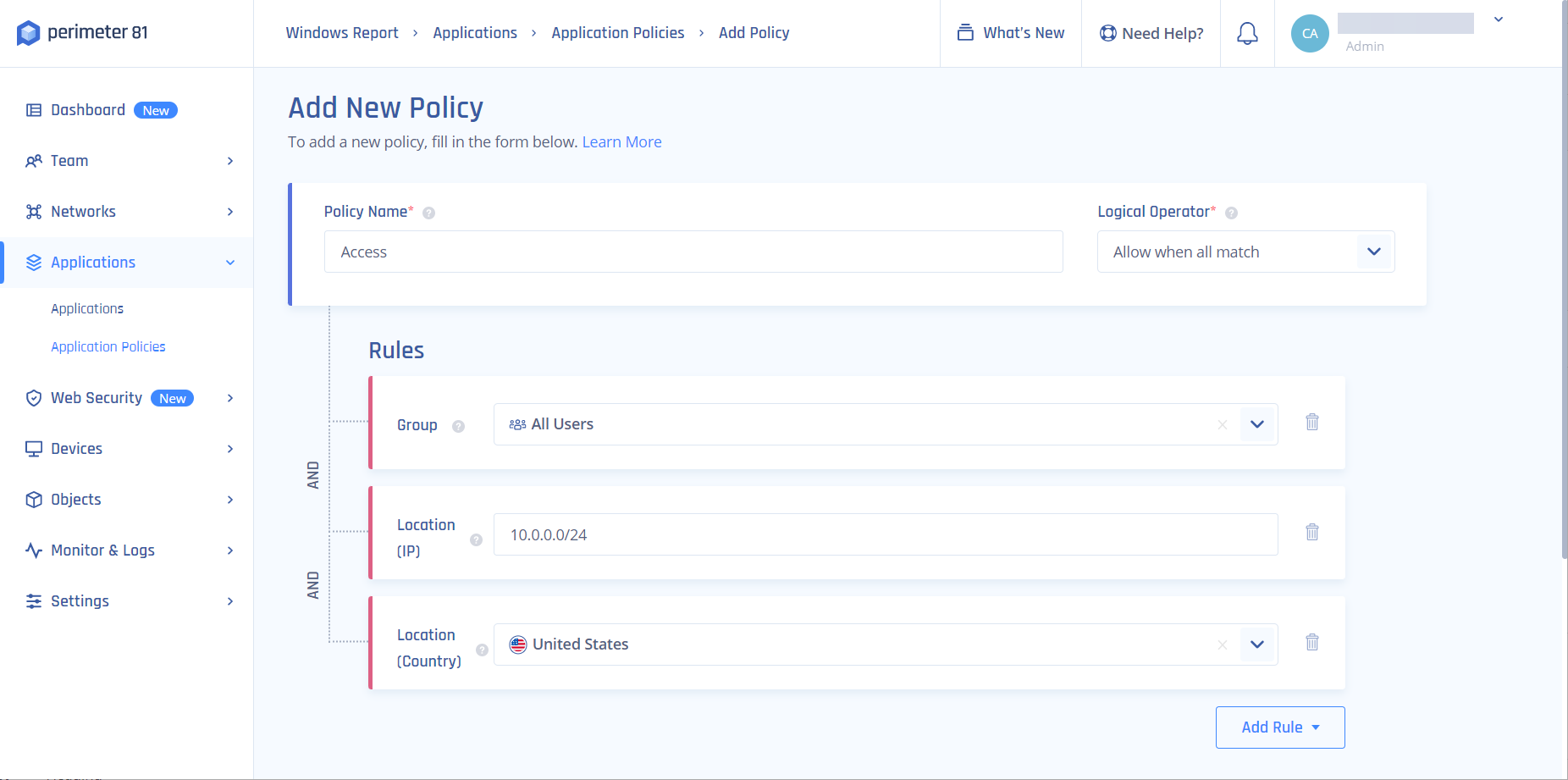
2. Set up the networks and permissions
Now a multi-tenant cloud is established with segmented permissions controlling who can get access to what across several networks. These can interconnect.
Think either a central office with native firewalls or a full cloud service with IP whitelisting.
3. Create agents
The agent modules are installed on the mobile or PC devices that employees use. This leaves them able to access any local or cloud network, with security in place, in one click no matter where they are.
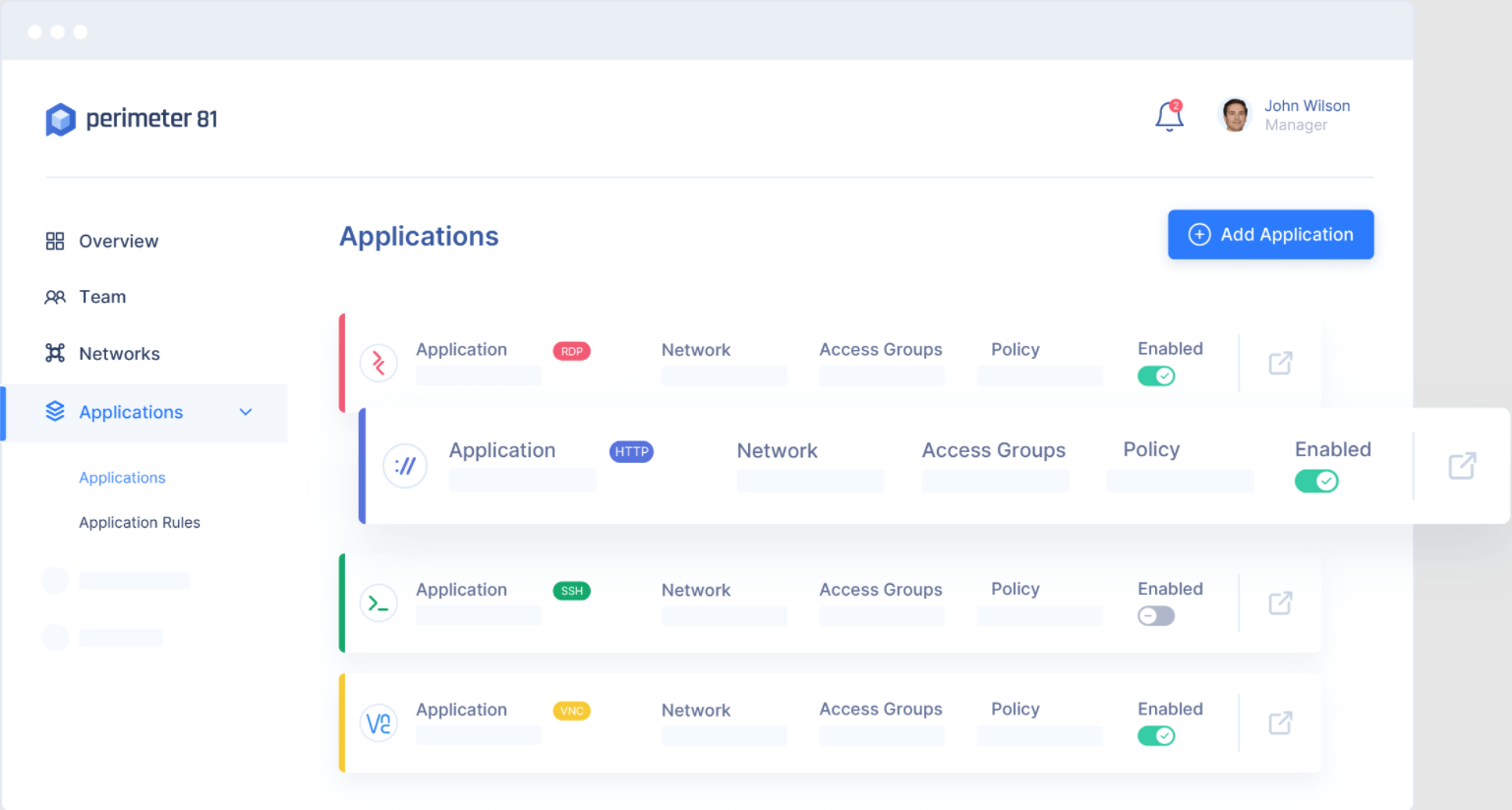
4. Agentless application access
User trust and device policy validation run automatically to authorize the employees before allowing them access in a secure session.
The sessions will be recorded and monitored if you chose this setup in step 1 and can be fully audited. Applications are isolated from the network and use Zero Trust guidelines.
With Perimeter 81 in place, you can leverage the power of an always-on VPN to help safeguard critical company data, without hampering your user experience or slowing down productivity.
You might also be interested in our list including the best remote access tools with session recording options.
If you already used Perimeter 81, share your experience in the comments section below.
Read our disclosure page to find out how can you help Windows Report sustain the editorial team. Read more









User forum
0 messages