Trojan partially removed in Windows 10: Here's how to remove it for good
5 min. read
Updated on
Read our disclosure page to find out how can you help Windows Report sustain the editorial team Read more

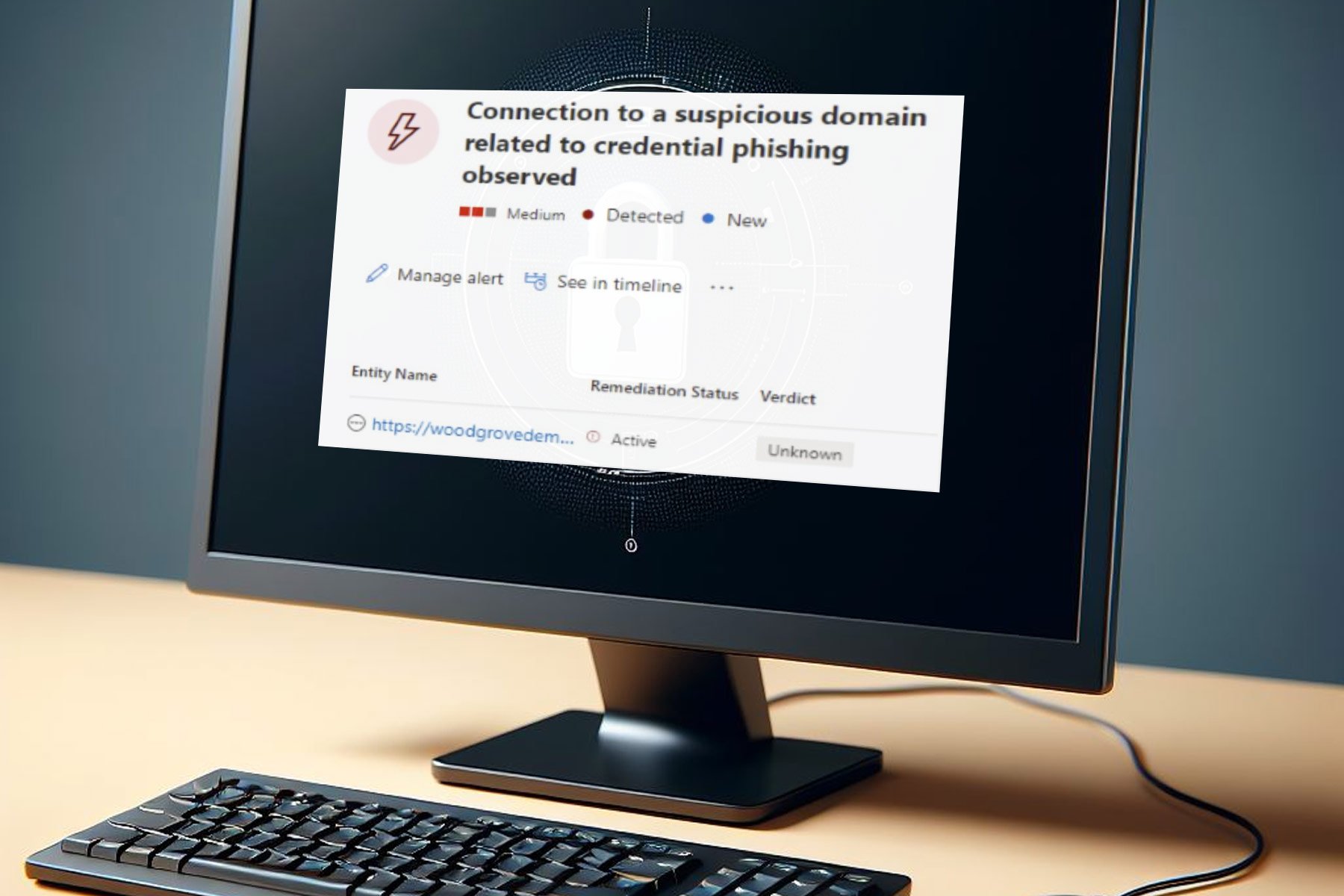
One of the worst things that can happen while we use our Windows 10 device is to experience a malware attack. Technical cams and other malicious processes can jeopardize your security settings, allowing hackers to access your personal files.
Therefore, if you somehow detect a new malware or a Trojan, find the right security solutions for removing the virus as soon as possible. However, if your antivirus program cannot successfully complete the removal operation and if the Trojan is only partially uninstalled, this article may help you.
The reason why certain antimalware or antivirus programs cannot manage to entirely remove persistent Trojans or other similar threats is because they have a limited database. Each security tool contains a dedicated database where various malicious processes are added. So, when a scan is initiated, based on this database and on other specific algorithms the security software detects infected files from your Windows 10 system. If this database is not properly updated or configured, some Trojans might not be entirely deleted. And that’s when you will notice that everything you do is in vain.
You can also use security software that perform in-depth scans on your system. Usually, these tools can remove malware for good.
Anyway, don’t worry; there are a few tricks that once applied, the full scan and a malware removal process gets successfully completed. Here is what you need to do.
How to solve ‘Trojan partially removed’ security issue
- Safe Mode with Networking
- Remove the processes associated with the Trojan virus
- Choose the right antimalware program
- Initiate the scan and remove the malware
Go to Safe Mode with Networking
The first thing to do is to access Safe Mode. In Safe Mode all third party apps and processes are disabled by default. If you don’t disable the files associated with the malware, you might not be able to properly remove it. So, follow the next steps for rebooting Windows 10 into Safe Mode:
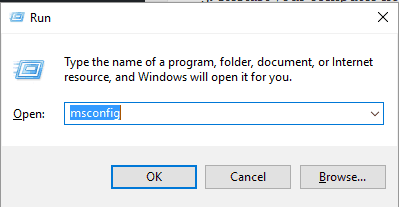
- Press the Win+R keyboard keys and in the Run box that will be displayed type msconfig. Press Enter in the end.
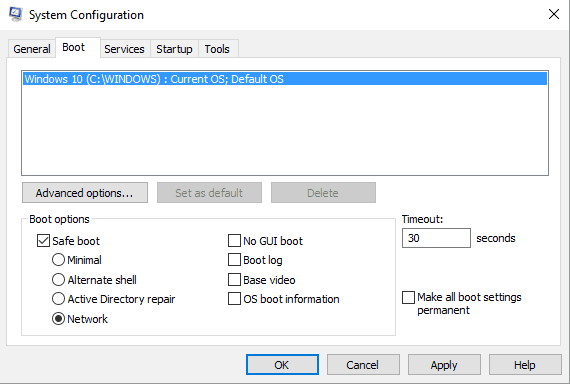
- From System Configuration select the Boot tab.
- Click on Safe Boot.
- From beneath pick Network and click OK followed by Apply in order to save your changes.
- Restart your computer now as Safe Mode with Networking will be automatically reached.
Remove the processes associated with the Trojan virus
You need to manually scan your PC between recent installed apps and processes. You might find something that shouldn’t be there; if you do, manually uninstall the files associated with the malware. Here is how you can complete this task:
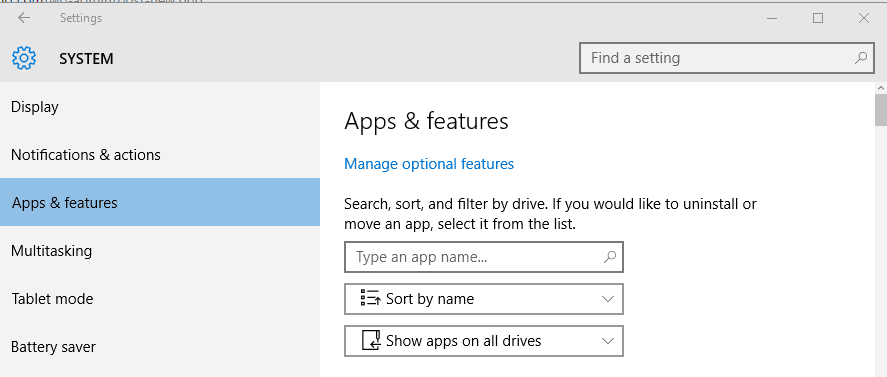
- Click on the Cortana icon in order to launch the Search field.
- There type App & features and select the first entry that’s displayed.
- Just look between the installed apps and choose to delete the software that seems to be related with the Trojan.
- You can remove files easily – right-click on the file and choose ‘uninstall’.
Hint: the virus can also infect your browser. So, I strongly recommend you to remove any possible infected infections from your web browser clients. Depending on the browser you use, the extensions might be accessed differently.
For example, for Chrome you need to access Tools – > Extentions; for Firefox press Shift+Ctrl+A; on Microsoft Edge press Alt+T – > Manage Add-ons – > Toolbars -> Extensions.
Moreover, a good idea will be to reset the browsers. It’s also recommended to delete the Chrome, Firefox and Microsoft Edge shortcuts and create new ones before starting any other security solution.
Finally, from Task Manager you can see the running processes, even the ones that are in the background. Select ‘End task’ for each process that is associated with the malware program.
Choose the right antimalware program
If you are currently using only Windows 10 default security programs, you might not be able to entirely remove the Trojan. You need to choose a complex and professional antivirus solution that can offer dedicated protection against the most common malware and malicious processes.
For more information on the best antivirus solutions to use on Windows 10, check out this article.
Of course, the best security apps are the paid ones (such as Avast, Norton, Bitdefender or Kaspersky), but you can also use free-distributed software such as Malwarebytes. Anyway, the goal is to download and install a program that can scan both the Windows 10 system and the web browser activity.
To keep your browser safe in the future, install one of these antivirus tools for browsing.
Initiate the scan and remove the malware
It’s important to apply the scan in Safe Mode. Otherwise ,the Trojan might block some security features and even the actual scan.
Once in Safe Mode and after manually removing any malicious files and apps, run the antimalware software. Choose to perform a full scan even if that might take a while – depending on how many files are stored on your computer. The antivirus software will detect infected files during this scan.
In the end you will have to select the files which you want to remove. Well, just make sure you remove everything from the scan log. And, when done, restart your Windows 10 device.
Conclusions
When a Trojan is messing with your Windows 10 system, or when you experience any other malware infection, you need to stop the infected processes as soon as possible. Afterwards, by using the right security tools you can remove even the most persistent viruses.
If you cannot manage to remove certain malicious apps and processes, drop us a line in the comments below offering as much information as possible. We will try to find the perfect security solutions for your problems.
RELATED STORIES TO CHECK OUT: