Hotel WiFi Blocking VPN: What To Do If You Can't Connect
Bypass VPN traffic restrictions, blocked ports & more


World-class 24/7 support with 82% for a 2 years plan and 2 months free
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Amazing connection speed with 61% off and 4 months free for the 2-years plan.

Best security protocols with 83% off and 2 months free for a 2-year plan.
When staying in hotels, you might find that VPNs are often restricted, making it tough to connect securely.
As you move around or deal with weak signals, these restrictions can interrupt your access to corporate servers, slowing down your productivity.
Follow the steps below to make this issue go away for good:
What can I do if I can’t connect to a VPN on hotel WiFi?
1. Hide VPN traffic (obfuscation mode)
To bypass VPN blocks, enable your VPN’s obfuscation feature. It is built to make VPN traffic look like regular HTTPS so it doesn’t ring the bells of anti-VPN firewalls/software.
Most modern VPNs come with this feature. Some require you to manually enable it from settings, while others use it by default on all servers.
A great option that falls in the second category is ExpressVPN. The tool has servers in 105 servers, all able to overcome internet restrictions on restrictive networks like those of hotels.
Main features of ExpressVPN include:
- Top-tier security with 256-bit AES encryption
- Guarantees user privacy by not tracking or storing browser data (no logs policy)
- Cross-platform support (mobile, PC, routers, smart TVs & more)
- Over 3,000 servers in 100+ countries
- Advanced features like split tunneling and kill switch

ExpressVPN
Bypass hotel Wi-Fi blocks with ExpressVPN’s secure, obfuscated servers.2. Switch your protocol
- Launch the VPN app on your device.
- Navigate to the settings or connection preferences.
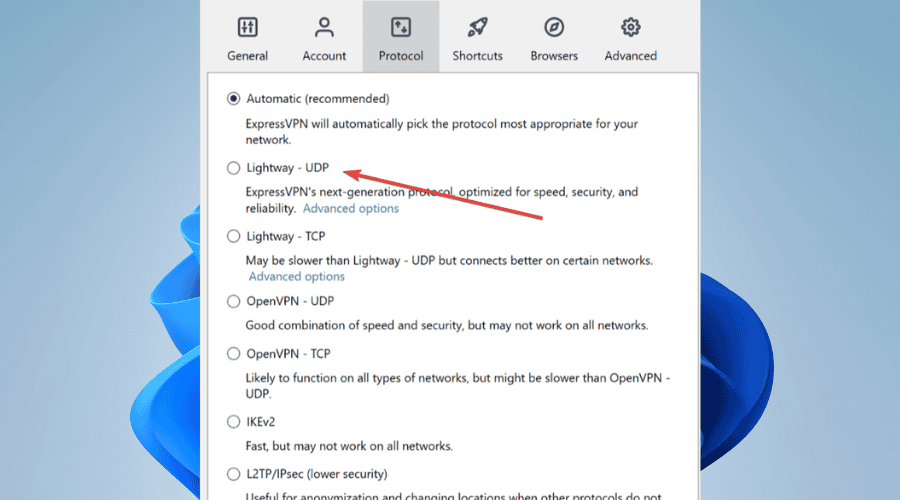
- Look for the option to choose or change VPN protocols.
- Switch to a less commonly blocked protocol like WireGuard, IKEv2, or SSTP.
- Save the settings and reconnect to your VPN using the new protocol.
3. Change ports
You can disguise your VPN traffic as regular web browser traffic, which makes it impossible for the hotel’s network to block your VPN service.
To do this, you need to set OpenVPN on port 443. This port is usually used for SSL/TLS encrypted web traffic. If the hotel’s network would block it, then most of the websites will not work today.
- Launch the VPN app on your device.
- Navigate to the advanced settings or connection options.
- Locate the option to change or specify the VPN port.
- Choose a less commonly blocked port, such as 443, which is often used for HTTPS traffic.
- Save the changes and reconnect to your VPN.
4. Switch between DNS servers
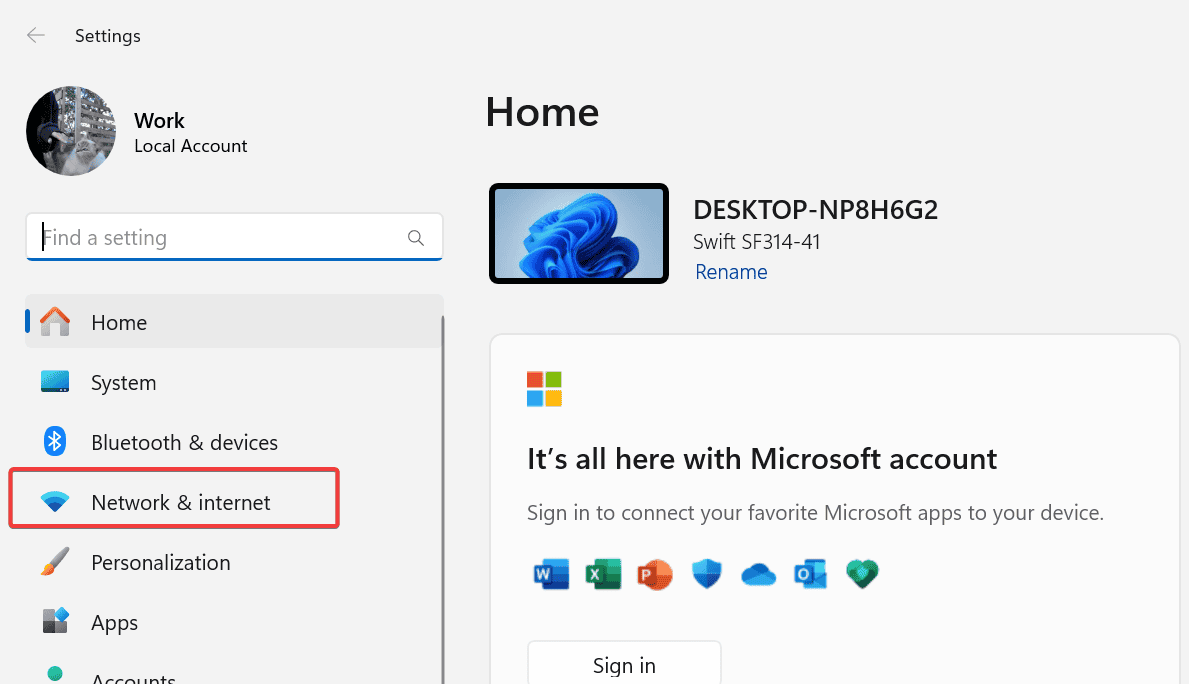
- Press Win + I to open the Settings app.
- Select Network & Internet from the left menu.
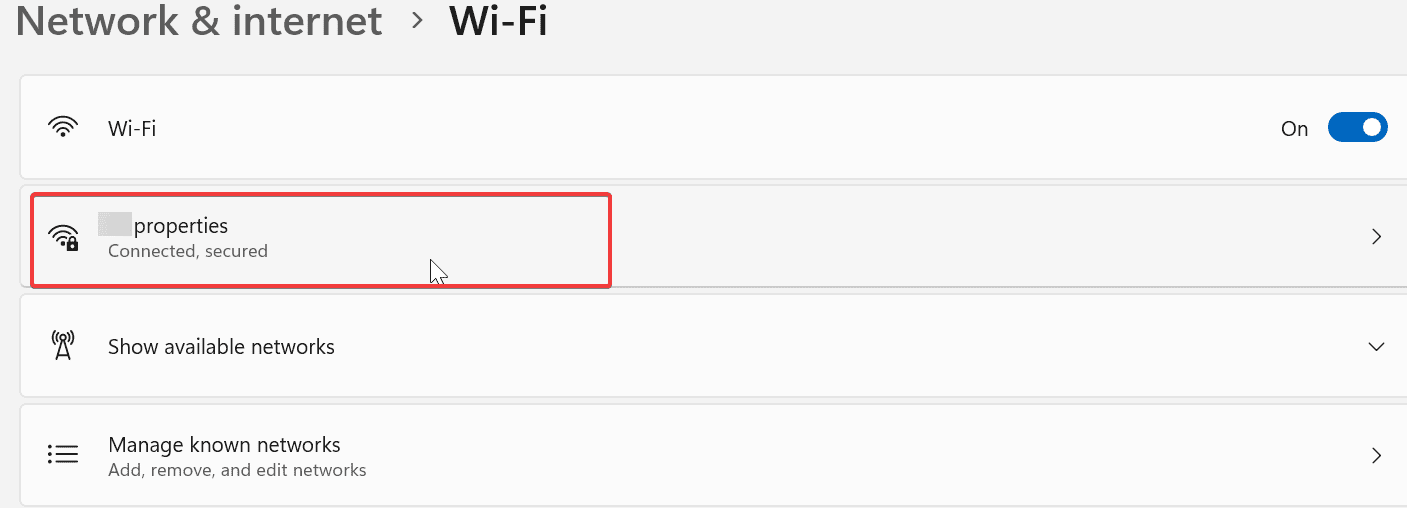
- Click on Wi-Fi or Ethernet depending on your connection.

- Click Properties under the selected network.
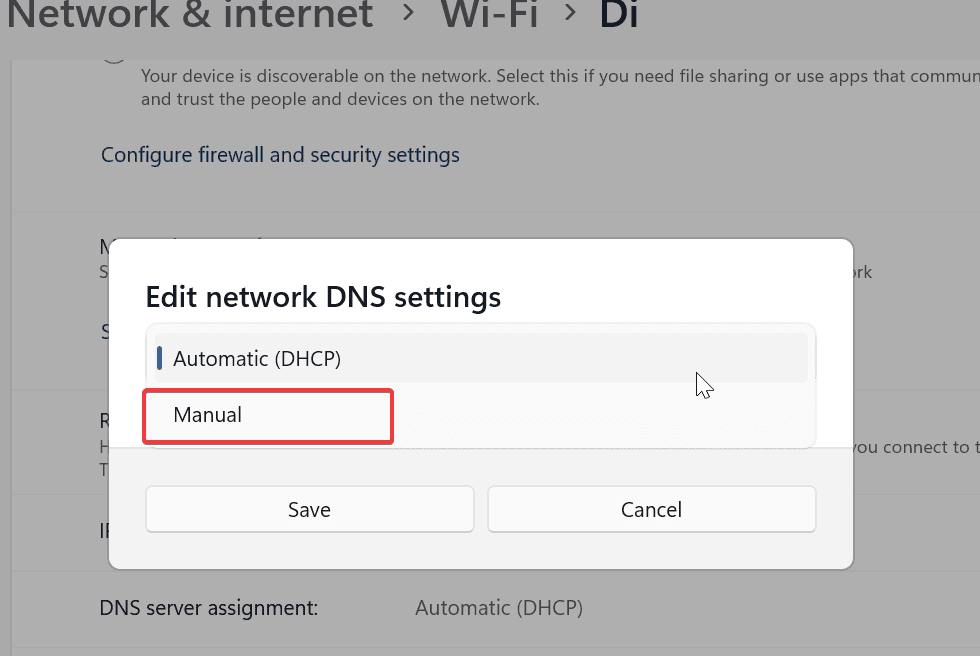
- Click Edit next to DNS server assignment and select Manual.
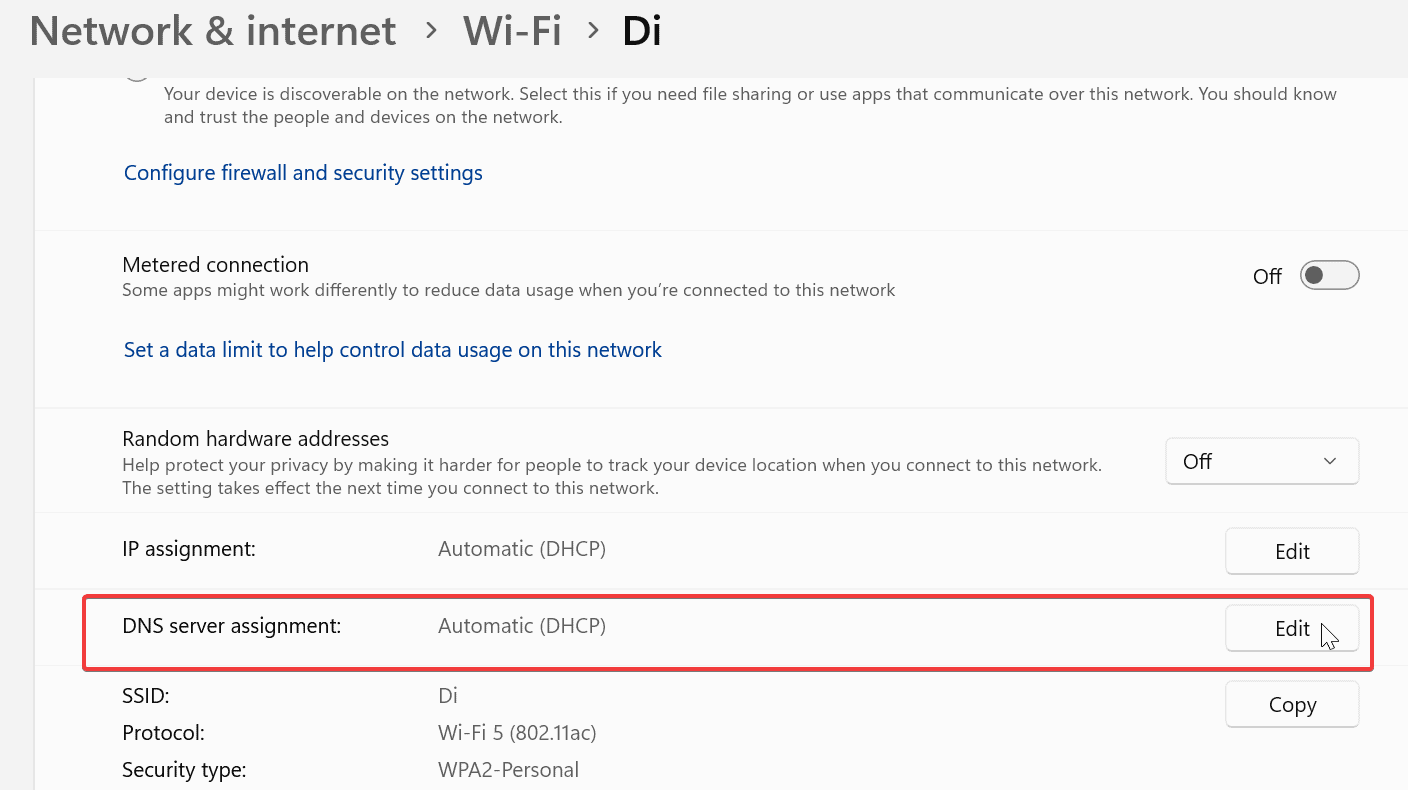
- Select Manual DNS settings.
- Input your preferred DNS addresses and click Save.
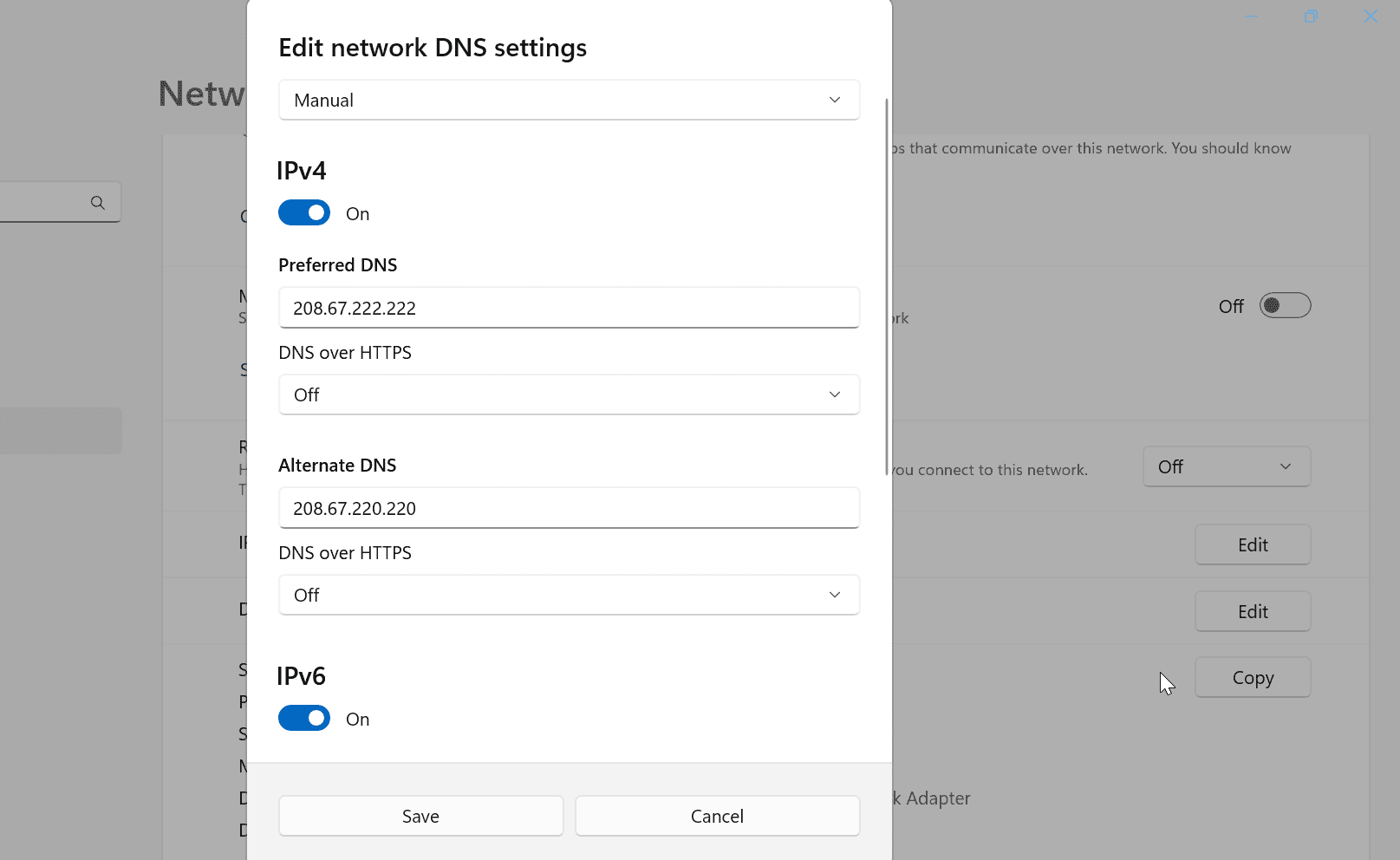
?You can use public DNS services like Google Public DNS (8.8.8.8 and 8.8.4.4), Cloudflare DNS (1.1.1.1 and 1.0.0.1), or OpenDNS (208.67.222.222 and 208.67.220.220) for faster and more secure internet browsing.
5. Check your laptop configuration
If you’re having trouble connecting to work, start by checking with your office IT admin about your computer’s configuration. Inform them of the issue so they can log it and help troubleshoot.
You might be encountering problems due to overlapping subnets or a restrictive hotel firewall.
Overlapping Subnets: If the VPN client connects to a network with the same private IP address range as your office, the addresses can overlap.
For instance, if the hotel router assigns your machine a private IP address range that matches your office network, your VPN client might use this address, causing overlap. This overlap can make your VPN connection appear local to the hotel network, leading to connection issues.
Restrictive Hotel Firewall: If the hotel’s firewall is too restrictive, it might block or modify your IPsec connection.
For example, it could drop or alter the ESP (Encapsulated Security Payload) frames used in IPsec, preventing the VPN from functioning correctly.
Some IPsec clients offer features that help bypass these issues, providing remote access even when behind restrictive firewalls.
Summary
In conclusion, navigating hotel WiFi restrictions can be challenging, but by using techniques like obfuscation mode, changing protocols or ports, switching DNS servers, and checking your laptop configuration, you can maintain secure and uninterrupted VPN access, ensuring your productivity stays intact.
FAQs
Yes, VPN works on hotel WiFi. However, use one with plenty of servers and advanced privacy features. That’s because some hotel network admins may attempt to block known VPN ports and IP addresses. But if you enable advanced features like obfuscation, you shouldn’t worry about that.
Yes, it is safe to use hotel WiFi with a VPN. Once you’re connected, your history and activity are completely private. Network admins or snoopers can’t see any of it.
To use VPN on hotel WiFi, you need a dedicated app installed on your device. Then connect to the hotel WiFi and immediately after to the VPN. This way, there will be no record of anything you do online besides the VPN connection itself.
No. If your VPN works correctly, no logs will be available in your hotel’s network admin panel. The only visible thing is your VPN connection. Everything else you do once connected is 100% hidden.
Read our disclosure page to find out how can you help Windows Report sustain the editorial team. Read more







User forum
0 messages