5 Ways to Disable TLS 1.0 and 1.1 and enable TLS 1.2 and 1.3 on Windows Server
TLS is critical for data encryption between the client and a web server
5 min. read
Updated on
Read our disclosure page to find out how can you help Windows Report sustain the editorial team Read more
Key notes
- To ensure maximum security, it’s important to enable TLS on Windows Server properly.
- Modifying a couple of values in your registry is the simplest way to do that.
- If you prefer using the command line, you can enable this feature using PowerShell.
Transport Layer Security 1.0 and 1.1 haven’t been supported for a while, and have been disabled on Windows 11 Insider Preview builds in September 2023 and future Windows OS releases.
However, if you’re running an older version, you can disable them and make sure you are running the latest TLS 1.2.
Therefore, in this guide, we’re going to show you how to properly enable and disable TLS.
How do I disable TLS 1.0 and 1.1 on Windows Server?
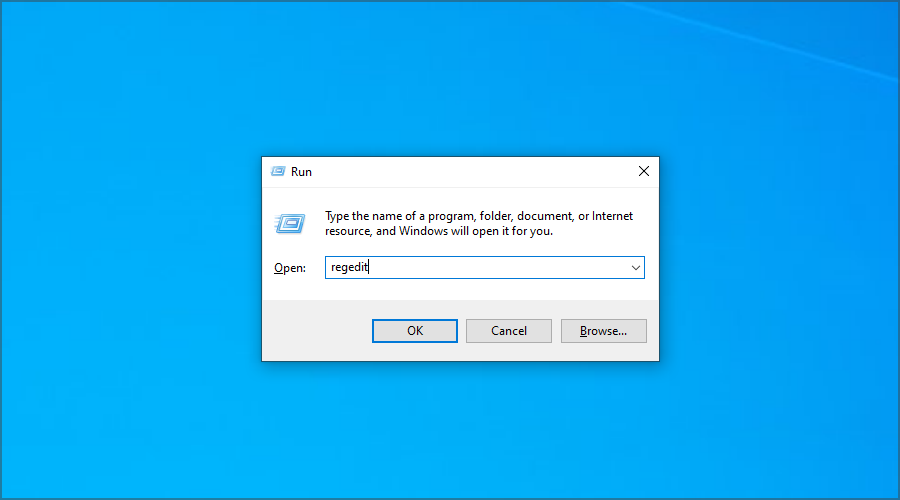
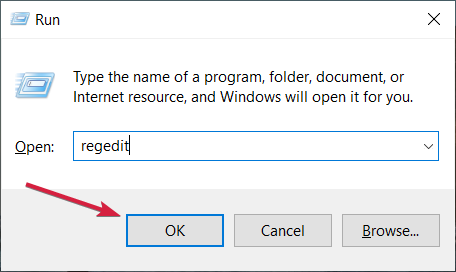
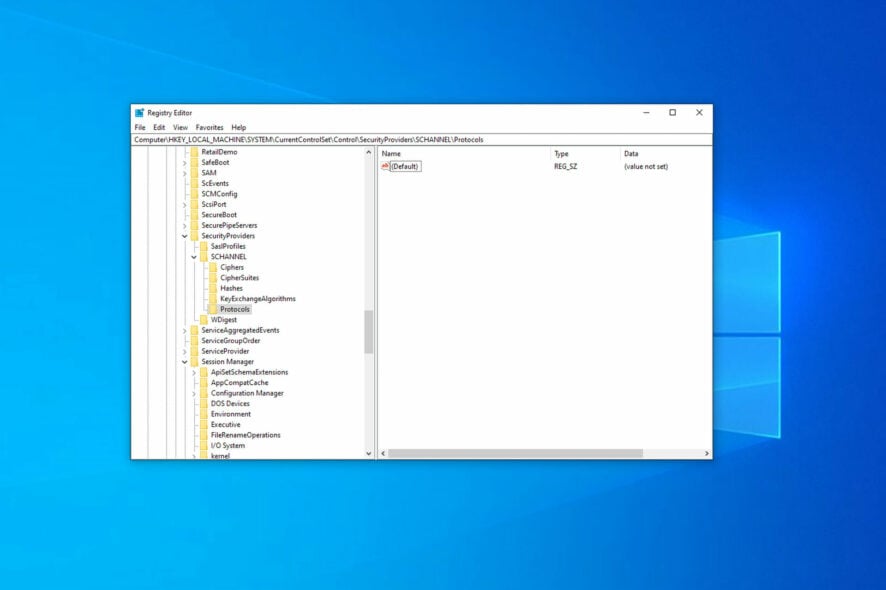
- Press Windows key + R and enter regedit. Now press Enter.
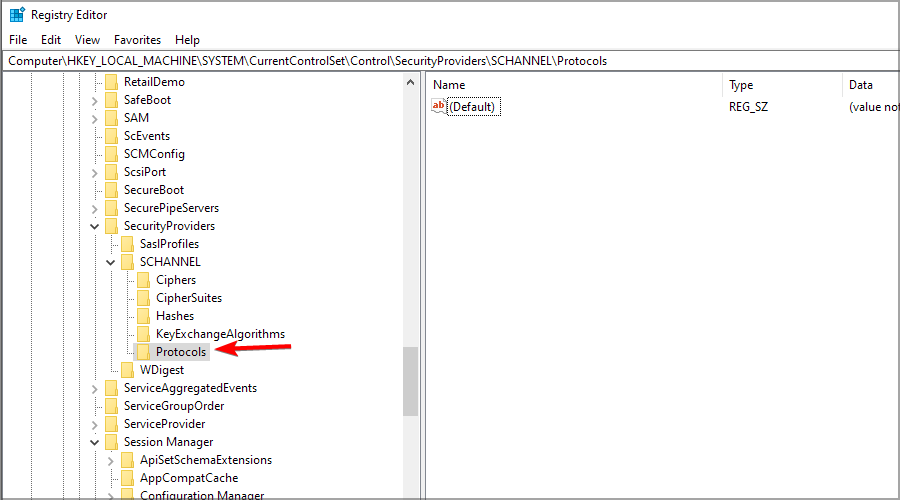
- Navigate to the following key:
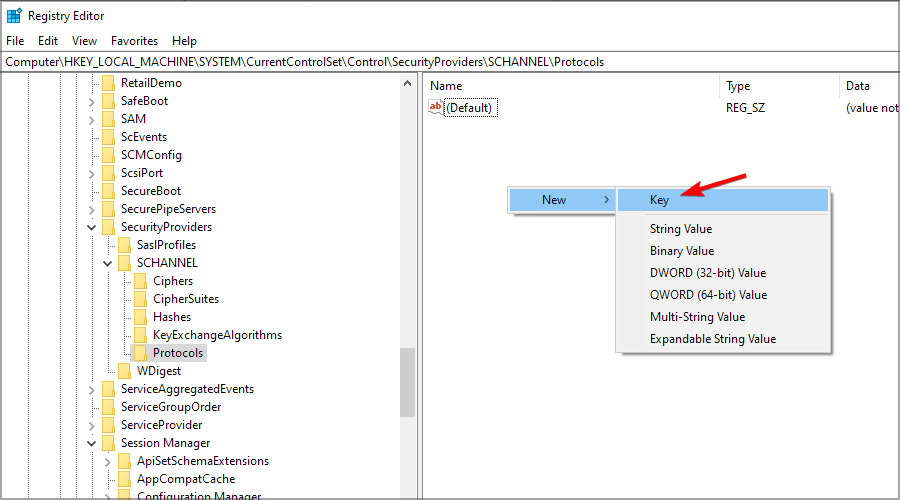
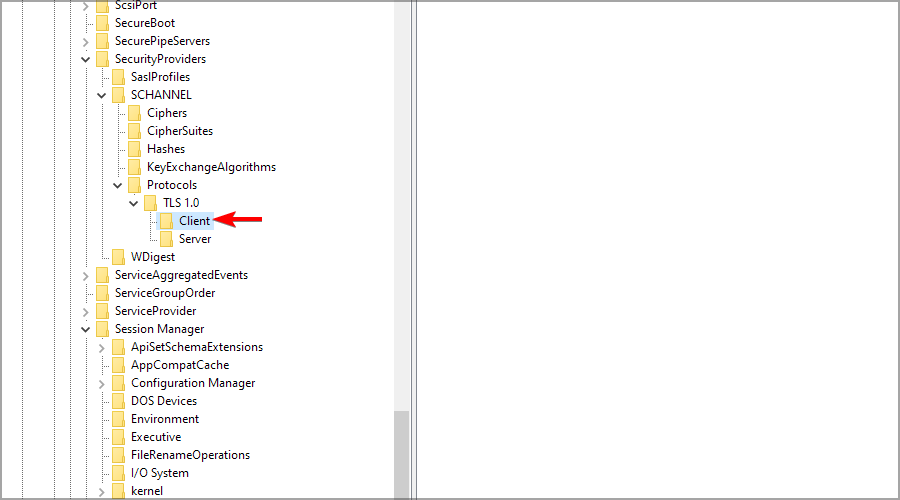
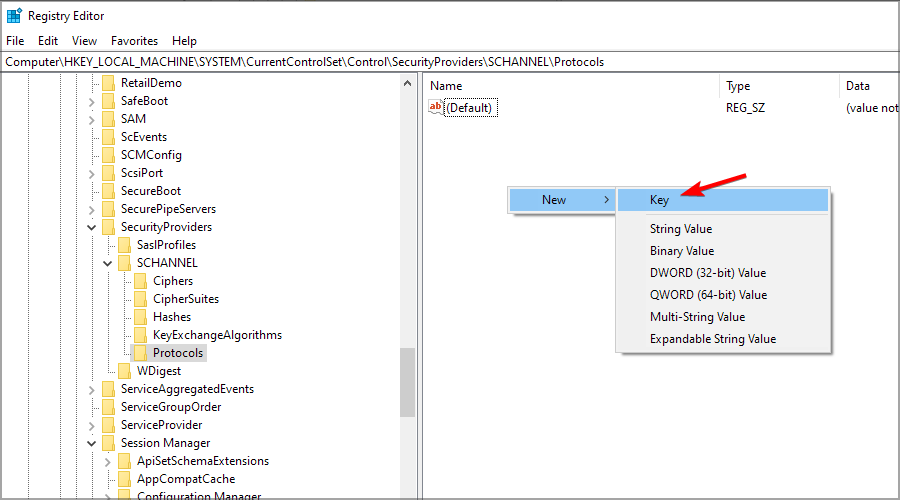
HKLM\SYSTEM\CurrentControlSet\Control\SecurityProviders\SCHANNEL\Protocols - Right-click the right pane, expand the New section and select Key.
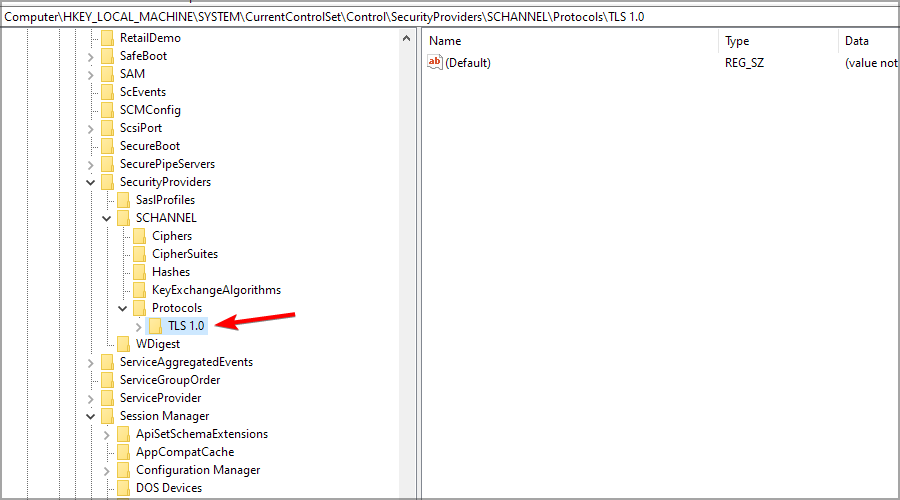
- Name the new key TLS 1.0 and move to it.
- Create a new key called Client and move to it.
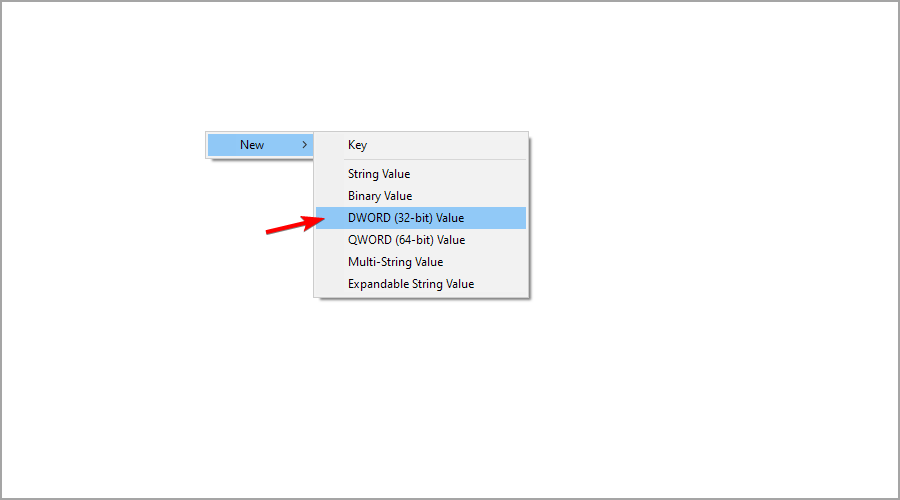
- Now right click the right pane, and select DWORD (32-bit) Value from the New menu.
- Name the new DWORD Enabled and double-click it to open its properties.
- Set the Value data to 0 and click OK to save changes.
If you want to disable TLS 1.1 instead, you will find it under the Protocols and proceed with the same steps.
Check if TLS 1.2 is enabled on Windows Server
- Press the Windows key + R to start Run, type regedit, and press Enter or click OK.
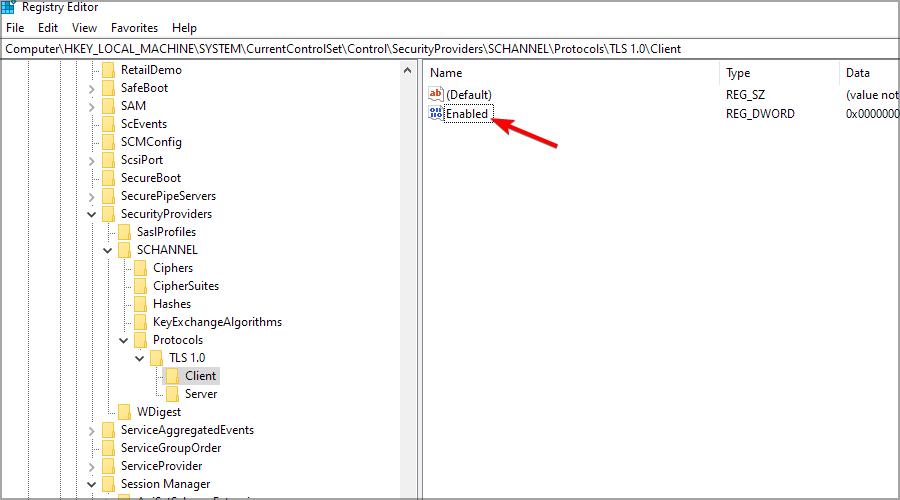
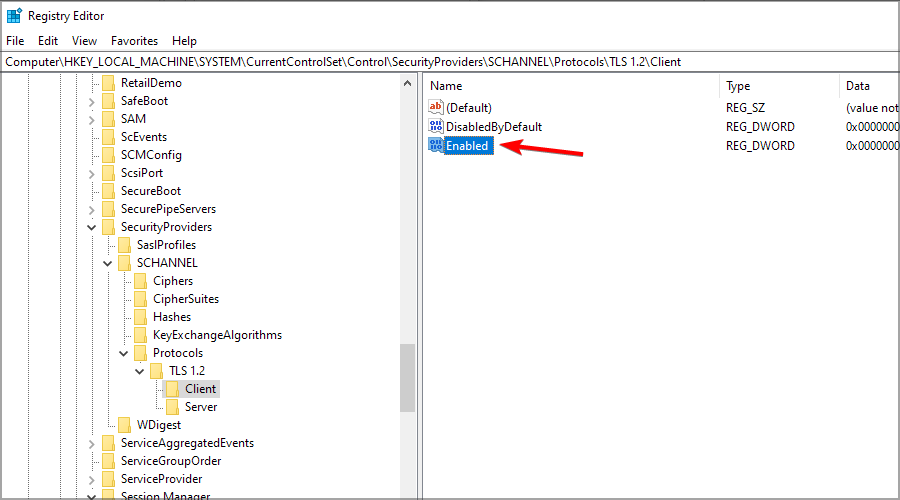
- Now go to the following key and check it. If it’s present, the value should be 0:
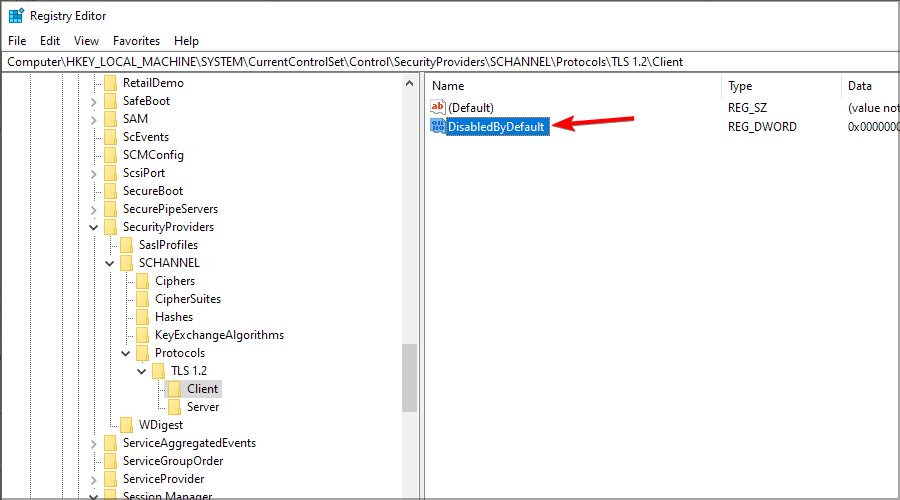
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\SecurityProviders\SCHANNEL\Protocols\TLS 1.2\Client\DisabledByDefault - Also, check the following key. If you find it, its value should be 1:
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\SecurityProviders\SCHANNEL\Protocols\TLS 1.2\Client\Enabled - If you can’t find any of the keys or if their values are not correct, then TLS 1.2 is not enabled.
There are four versions of TLS available, with the latest and safest one being 1.3, so be sure to use it along with reliable antivirus for Windows Server for maximum protection.
Enable TLS 1.2 on Windows Server by modifying the registry
- If you are running Windows Server 2008, check this Microsoft’s article regarding the necessary update in order to enable TLS 1.2. Once you’ve installed updates, move to the steps below.
- Open Registry Editor by pressing Windows key + R and entering regedit.
- Since we are dealing with registry, we strongly suggest backing up the current registry state. Incorrect changes to the registry might have detrimental effects on your system.
- Once we’ve dealt with that, follow this path:
Computer\HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\SecurityProviders\SCHANNEL\Protocols - Right-click on the empty space in the right pane and choose New and then Key.
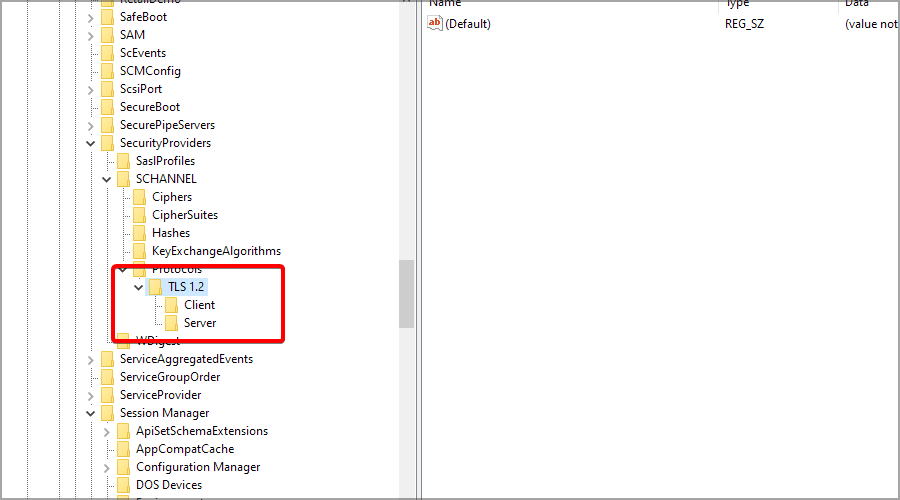
- Name the new key TLS 1.2 and click to expand it.
- Navigate to TLS 1.2, click on the empty space in the right pane and add two new keys. Name the first one Client and the second one Server. It should look like this.
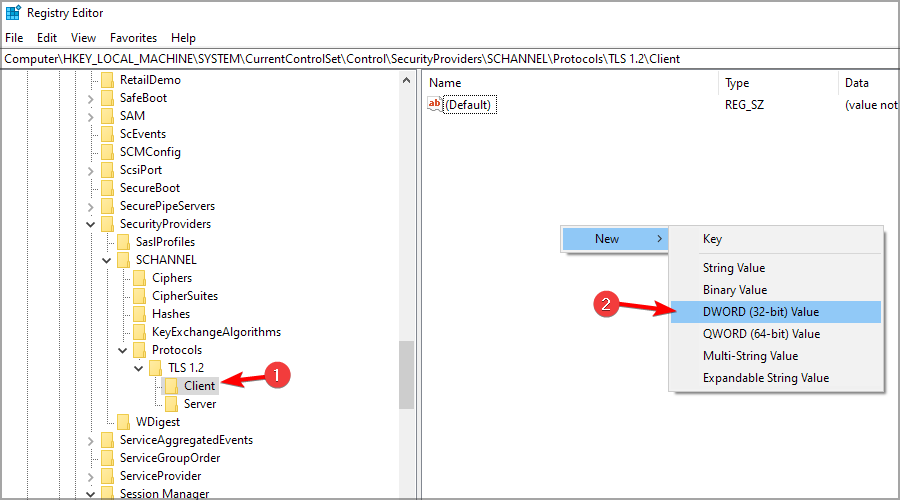
- Now, select the Client key, right-click in the right pane and select New and then DWORD (32-bit) Value.
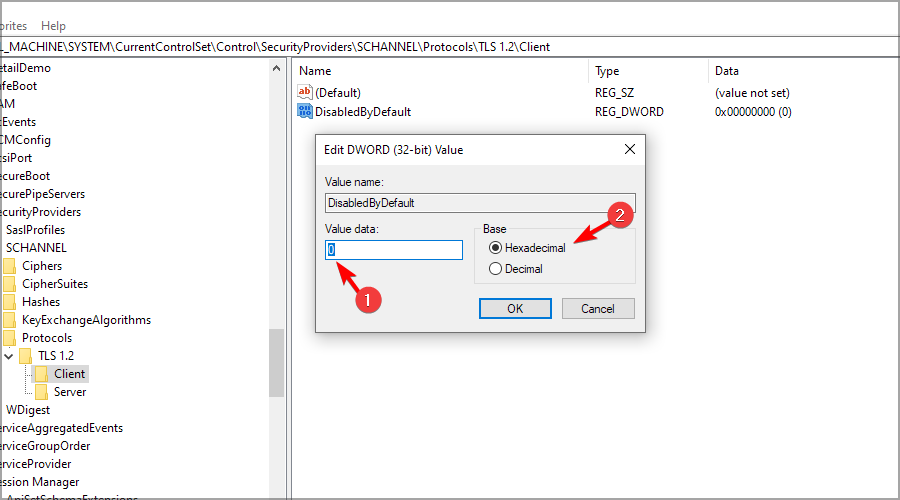
- Name the DWORD DisabledByDefault, and double-click it.
- Ensure that the Base is Hexadecimal and the value is 0 (zero).
- Create a new DWORD and name it Enabled and double-click it.
- Ensure that the Base is, again, Hexadecimal and the Value is set to 1.
- Repeat this for the Server key with the exactly the same DWORDS and values.
- Close the Registry Editor and reboot your server.
- If you want to revert back to the initial settings, just restore the Registry state from the backup.
To avoid any unplanned issues, it might be a good idea to use reliable backup software for Windows Server.
Enable TLS 1.2 with Powershell on Windows Server
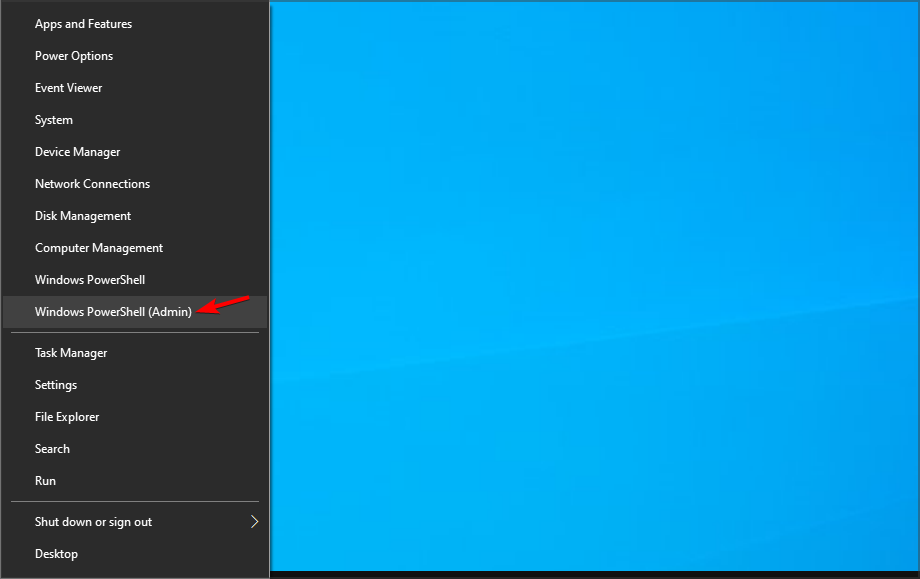
- Press Windows key + X and select Windows PowerShell (Admin) from the menu.
- When PowerShell opens, run the following commands:
New-Item 'HKLM:\SYSTEM\CurrentControlSet\Control\SecurityProviders\SCHANNEL\Protocols\TLS 1.2\Server' -Force
New-Item 'HKLM:\SYSTEM\CurrentControlSet\Control\SecurityProviders\SCHANNEL\Protocols\TLS 1.2\Client' -Force
New-ItemProperty -Path 'HKLM:\SYSTEM\CurrentControlSet\Control\SecurityProviders\SCHANNEL\Protocols\TLS 1.2\Server' -name 'Enabled' -value '1' –PropertyType 'DWORD'
New-ItemProperty -Path 'HKLM:\SYSTEM\CurrentControlSet\Control\SecurityProviders\SCHANNEL\Protocols\TLS 1.2\Server' -name 'DisabledByDefault' -value '0' –PropertyType 'DWORD'
New-ItemProperty -Path 'HKLM:\SYSTEM\CurrentControlSet\Control\SecurityProviders\SCHANNEL\Protocols\TLS 1.2\Client' -name 'Enabled' -value '1' –PropertyType 'DWORD'
New-ItemProperty -Path 'HKLM:\SYSTEM\CurrentControlSet\Control\SecurityProviders\SCHANNEL\Protocols\TLS 1.2\Client' -name 'DisabledByDefault' -value '0' –PropertyType 'DWORD'
So, by applying these commands you trigger Windows Server to enable TLS 1.2 using PowerShell.
Is there any tool to enable TLS 1.2 on Windows Server?
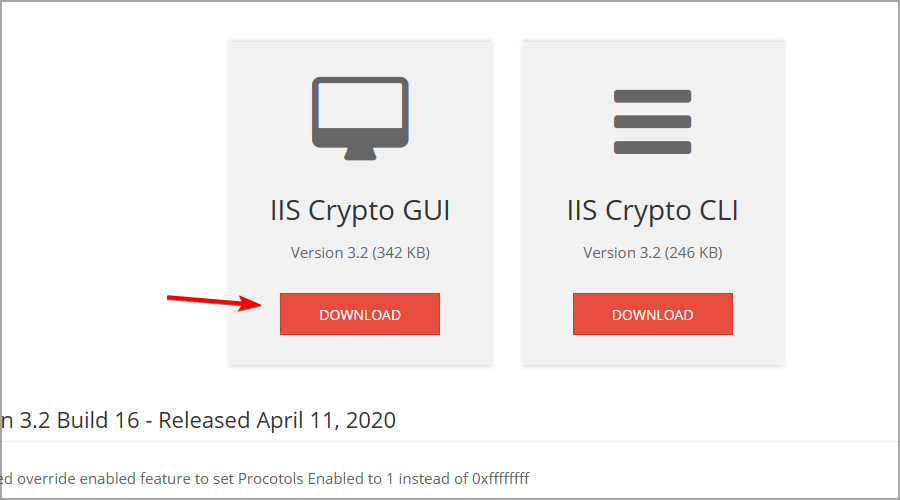
- Download ISS Cryptio GUI.
- Once you download the application, run it.
- Check TLS 1.2 and click on Apply.
How to enable TLS 1.3 on Windows Server?
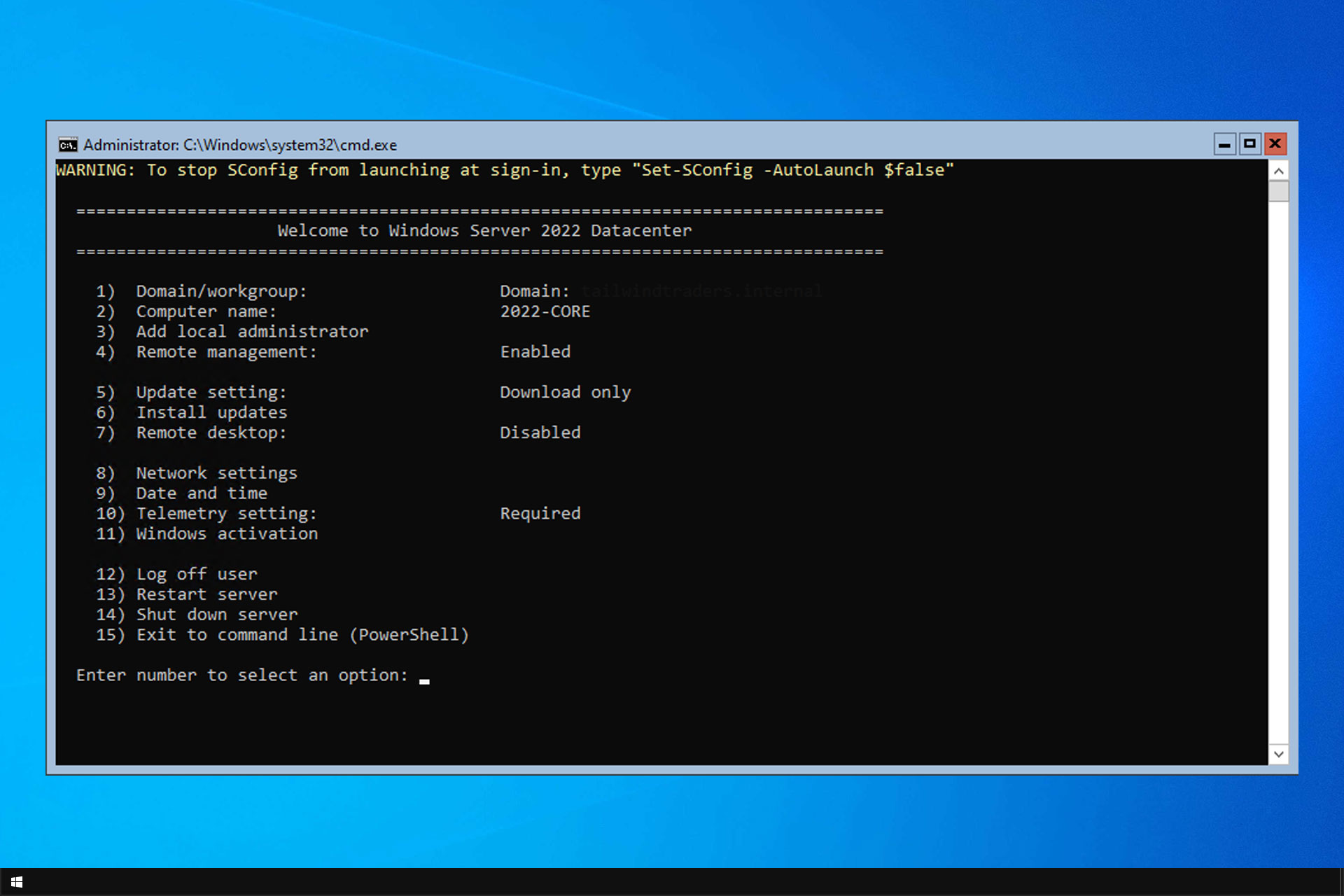
- Make sure you’re using Windows Sever 2022.
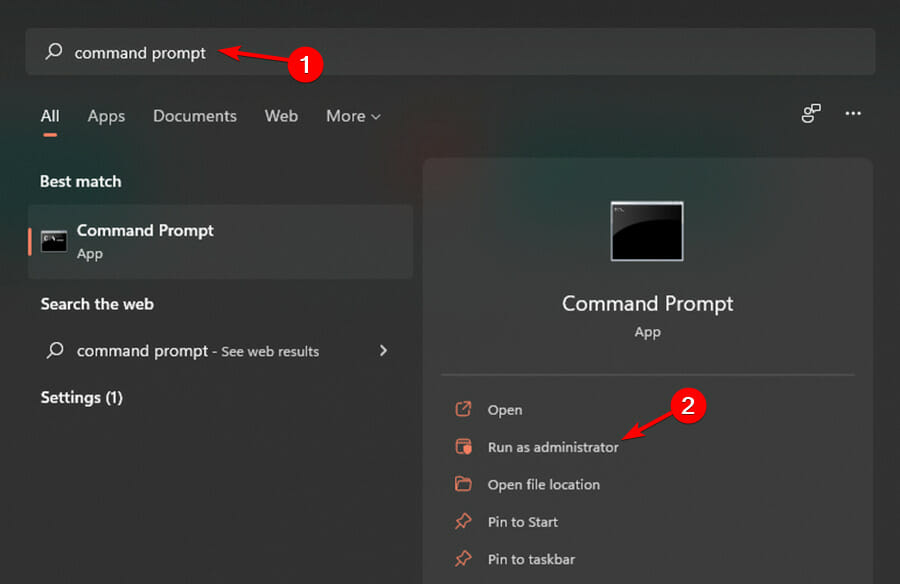
- Press Windows key + S and enter command prompt. Select Run as adminsitrator.
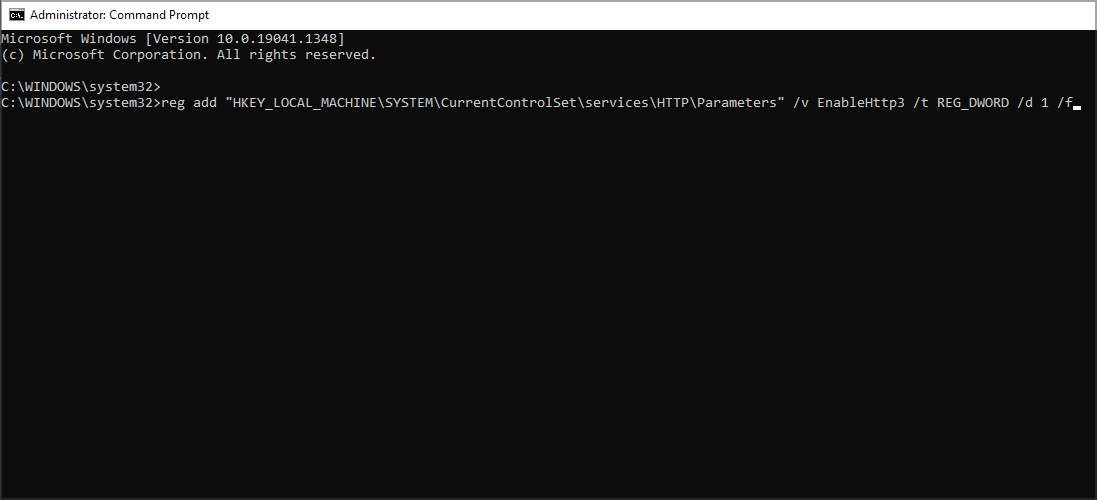
- Run the following command:
reg add "HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\services\HTTP\Parameters" /v EnableHttp3 /t REG_DWORD /d 1 /f
Is TLS 1.2 enabled on Windows Server 2016?
The good news is that starting with Windows Server 2016, TLS 1.2 is supported by default for WSUS.
In other words, there is no need to enable TLS 1.2 on Windows Server 2016 or Windows Server 2019.
Therefore, you only need to update TLS 1.2 on Windows Server 2012 and Windows Server 2012 R2 WSUS servers.
That’s how to enable or disable TLS on Windows Server. With those steps, TLS 1.2 is enabled and TLS 1.0 disabled with ease.
All of these solutions require you to modify your registry, so be sure to create a backup beforehand. Also, we advise you to check our guide on how to restore Windows registry without a backup for more information.
What method do you use to enable TLS 1.2 on Windows Server? Let us know in the comments section below.