We Picked 5 Best File Integrity Monitoring software for Windows
Our educated must-try list at your disposal
Key notes
- A FIM, or File Integrity Monitoring software, is a must-have when sensitive data is concerned.
- All the tools discussed work on Windows and are generally good options for network file management.
You must have found this guide because you are considering using some File Integrity Monitoring software.
In this article, we have explored all the options and have arrived at some that you should prioritize. So without wasting much time, let us take you through all you need to know.
What is a file integrity monitoring tool?
FIM (File integrity monitoring) is a security tool that monitors and tracks changes you make to files on a computer or network. This can include file permissions, ownership, content, and metadata changes.
FIM tools can alert administrators of unauthorized file changes, helping to detect and prevent potential security threats such as malware or insider attacks.
Benefits of file integrity monitoring include:
- Detecting malicious changes – FIM can help detect malicious changes to files. These are those made by malware or an attacker who has gained unauthorized access to a system.
- Compliance – FIM can help organizations comply with regulations that require them to keep track of changes, such as financial records.
- Identifying configuration errors – FIM can help identify configuration errors. Examples are the accidental deletion of important files that could cause a system or application to malfunction.
- Auditing – FIM is useful for monitoring a system’s changes. They also keep track of any changes made over some time.
- Real-time monitoring – Some FIM tools support real-time monitoring that alerts when changes are detected. Others are schedule-based, so the administrator can decide when the check should be run.
It’s a good security practice to use file integrity monitoring to ensure network security for important files and systems.
What Windows File Integrity Monitoring software should I use?
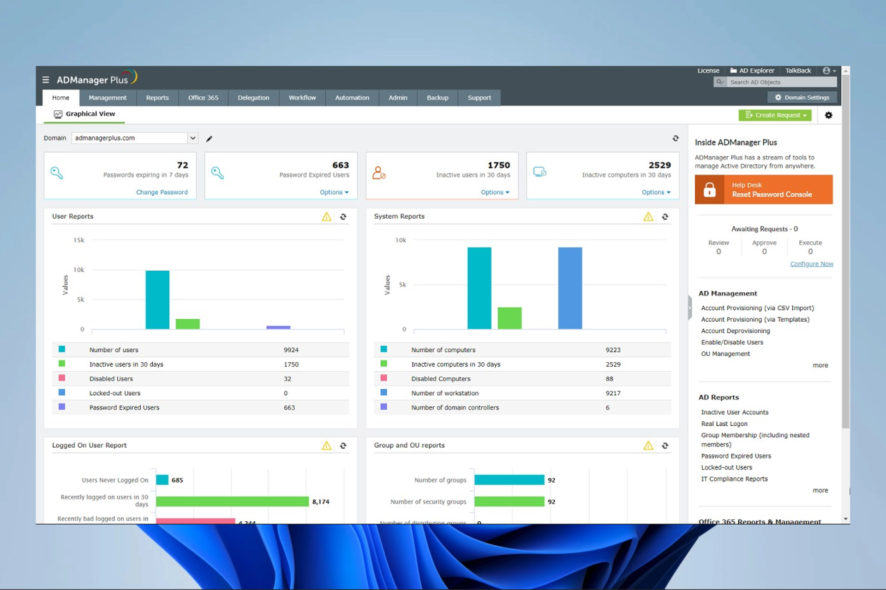
ADAudit Plus – Great all round AD monitoring
ADAudit Plus is a commercial, web-based Active Directory (AD) auditing and reporting tool. It monitors and tracks changes to AD and Windows-based systems, such as file and Exchange servers.
This tool offers real-time auditing and reporting of AD changes such as user account creations, deletions, modifications, group policy changes, and security settings.
It also provides detailed information about the changes, such as who made the change, when it was made, and the specific attributes that were modified.
Additionally, it offers historical reporting because it stores all the AD audit data in a database, allowing you to generate historical reports on changes made over a specified period.
Finally, ADAudit Plus is available for Windows-based systems and requires a Windows-based server.
Some features that we love:
- Compliance reporting
- Delegated auditing
- Alerting and notifications
- Historical reporting

ADAudit Plus
Great audit tool that offers comprehensive file audit and monitoring.AD Manager Plus – Web-based Active Directory (AD) management tool
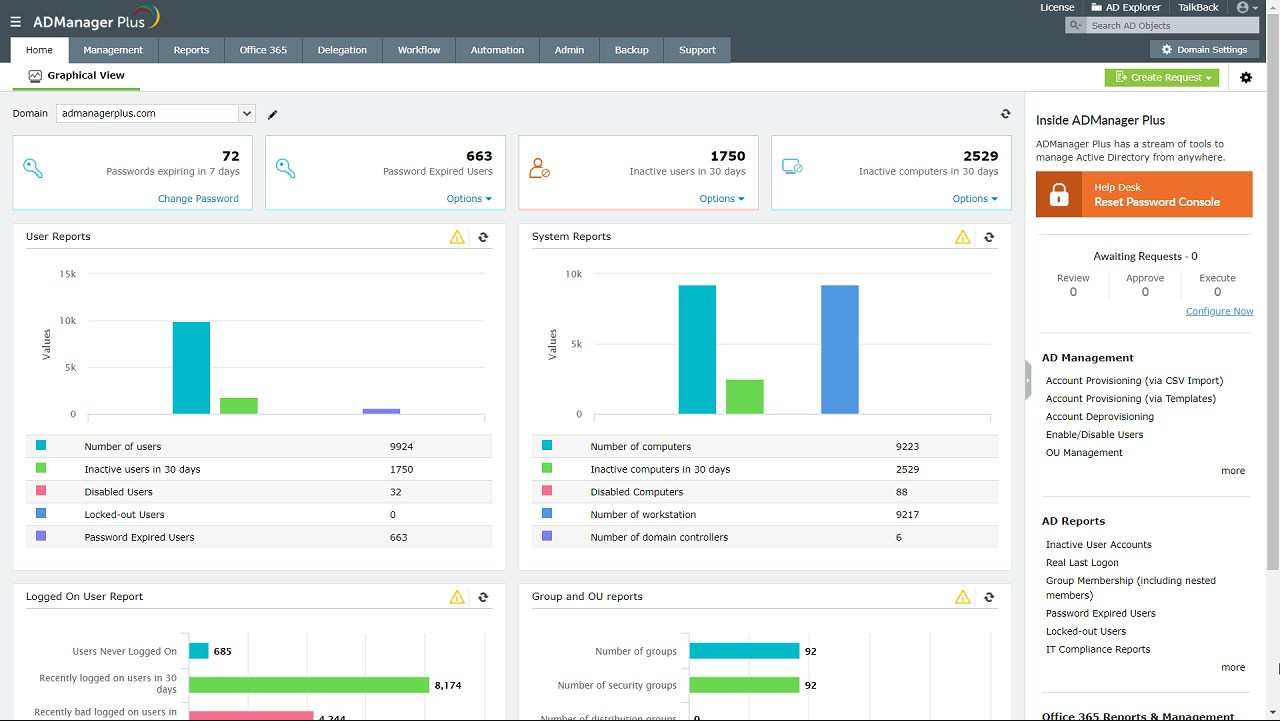
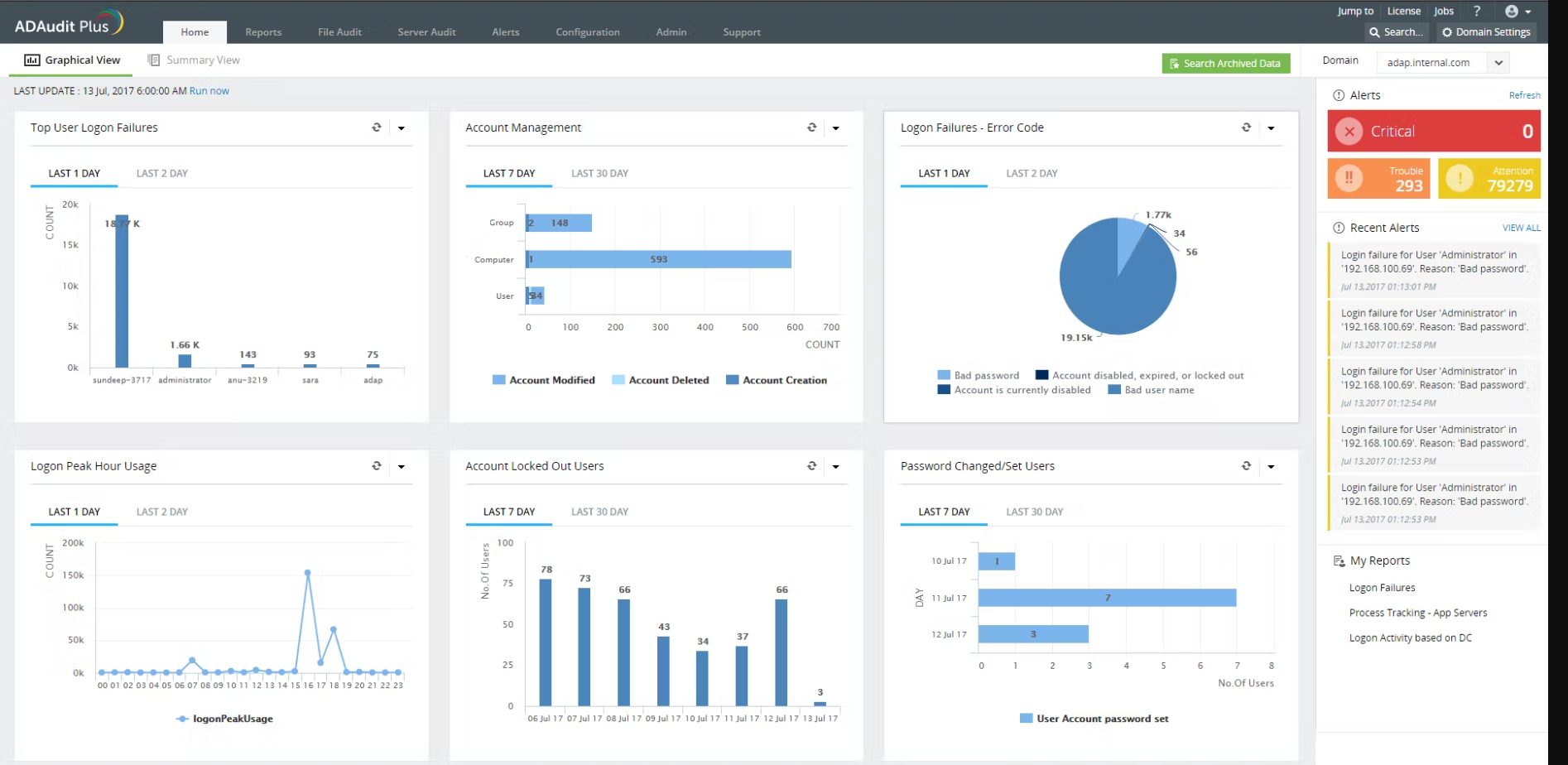
AD Manager Plus is a commercial, web-based Active Directory (AD) management and reporting tool. It provides a centralized platform for managing and reporting on AD and Windows-based systems, such as file and Exchange servers.
The tool offers Active Directory management with elements like managing and creating user accounts, groups, and organizational units (OUs), resetting user passwords, and managing group policy objects (GPOs).
Also, AD Manager Plus can perform bulk management tasks, such as creating or deleting multiple user accounts, resetting multiple user passwords, and moving numerous user accounts between OUs.
Furthermore, it provides a variety of built-in reports for auditing and reporting on AD, such as reports on inactive user accounts, locked-out user accounts, and GPO usage.
We like it because it allows you to delegate AD management tasks to other users, such as helpdesk administrators or departmental managers while maintaining central control and oversight.
Like ADAudit Plus, AD Manager Plus is available for Windows-based systems and requires a Windows-based server.
Some features that we love:
- Active Directory management
- Bulk management
- Reporting
- Delegated administration

AD Manager Plus
An integrated tool for AD (Active Directory), Skype for Business, Exchange, Office 365, and G Suite management and reporting.Tripwire – Great in preventing unauthorized changes
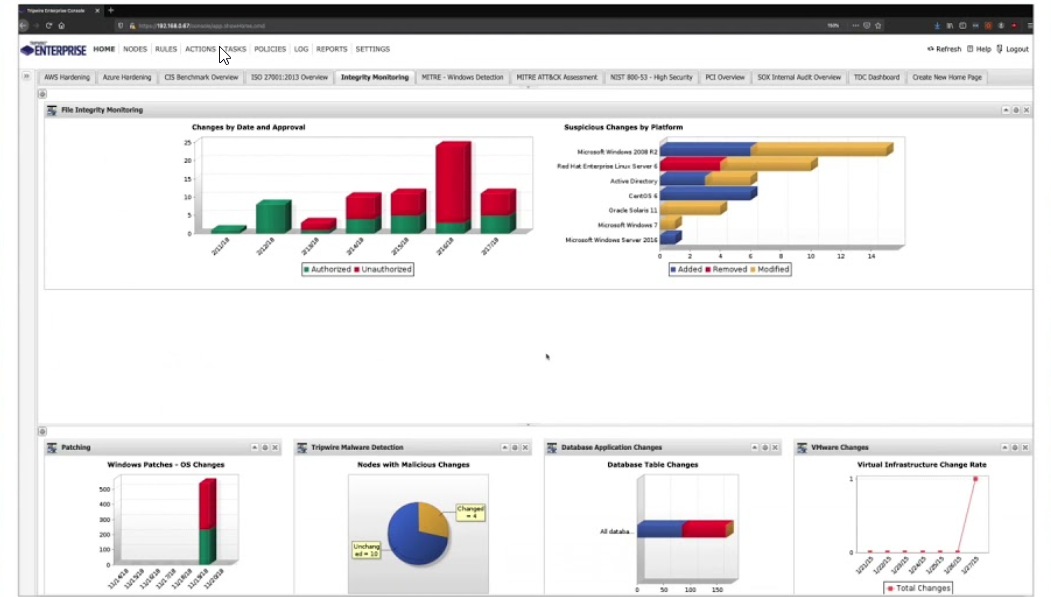
Tripwire is a well-established file integrity monitoring (FIM) tool designed to help organizations detect and prevent unauthorized changes to files and directories on their systems. In addition, it can monitor files and directories on both Windows and Linux systems.
One of the main features of Tripwire is its ability to take a snapshot of a system’s files and directories and then compare this snapshot to the current state of the system to detect any changes.
This can include file permissions, ownership, content, and metadata changes. When changes are detected, Tripwire can generate alerts, create detailed reports, and even take automated actions to remedy the issue, such as rolling back changes or quarantining affected files.
Tripwire can be configured to monitor specific files or directories. It can also be integrated with other security tools, such as intrusion detection systems and log management tools, to provide a more comprehensive security solution. It also has a command-line interface and API, allowing programmatic access and integration with other tools.
Tripwire is available in two versions: Tripwire Enterprise, which is a commercial product that offers additional features such as centralized management and reporting, and Tripwire Open Source, which is a free, open-source version that provides basic FIM capabilities.
Overall, Tripwire is a widely used and respected FIM tool designed to detect and prevent unauthorized changes to files and directories. Hence, it helps to detect and prevent potential security threats such as malware or insider attacks.
Some features that we love:
- Security monitoring for hybrid environments
- Automatic on and offboarding for Cloud Assets
- Automated, flexible multi-policy compliance
- Managing failed configurations with workflow tools
Open Source Security – Excellent open-source FIM tool
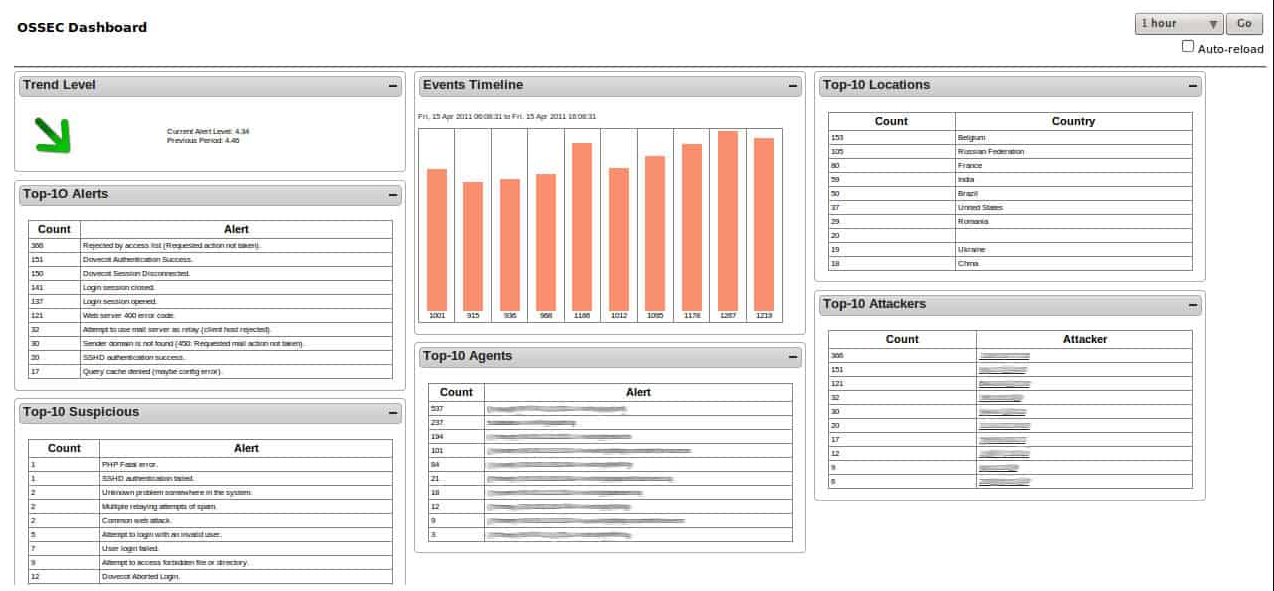
OSSEC (Open Source Security) is an open-source intrusion detection system (IDS) and intrusion prevention system (IPS).
the tool will provide a centralized platform for analyzing security-related data, such as system logs and network traffic. OSSEC can detect and respond to various security threats, including unauthorized access attempts, malicious software, and system misconfigurations.
One of the critical features of OSSEC is its ability to perform log analysis and event correlation in real time. This allows the system to detect and alert potential security incidents as they happen rather than relying on historical data.
OSSEC includes several built-in security rules and is configurable for integration with third-party security tools. These, in most cases, are antivirus software and firewalls.
OSSEC is available for many operating systems, including Windows, Linux, and macOS. Also, you can install it on servers, workstations, and network devices.
Some features that we love:
- Log-based Intrusion Detection
- Active Response
- Malware Detection and Rootkit
CrowdStrike Falcon FileVantage – Great for network file management

CrowdStrike Falcon FileVantage is a feature of the CrowdStrike Falcon platform that allows organizations to quickly and easily search, identify, and manage sensitive files across their network.
It uses advanced machine learning and data classification techniques to automatically identify and classify sensitive files, such as those containing personally identifiable information (PII) or other types of sensitive data.
This allows organizations to manage and secure their sensitive data more effectively, reducing the risk of data breaches and other security incidents.
Lastly, Falcon FileVantage can also perform eDiscovery, compliance reporting, and data leak detection.
Some features that we love:
- Increase overall efficiency
- Central visibility
- Insight from threat intelligence data
To summarize, file integrity monitoring solutions are crucial to your company’s security. They guarantee that your important files and their data are secure from internal and external threats.
Therefore, it is a crucial line of defense in your company’s security and is necessary for all businesses.
Lastly, we have not made this list in any particular order, so you should use what seems best.
Read our disclosure page to find out how can you help Windows Report sustain the editorial team. Read more





User forum
0 messages