KB4601318 fixes 11 different Windows service errors, among others
4 min. read
Updated on
Read our disclosure page to find out how can you help Windows Report sustain the editorial team. Read more
Key notes
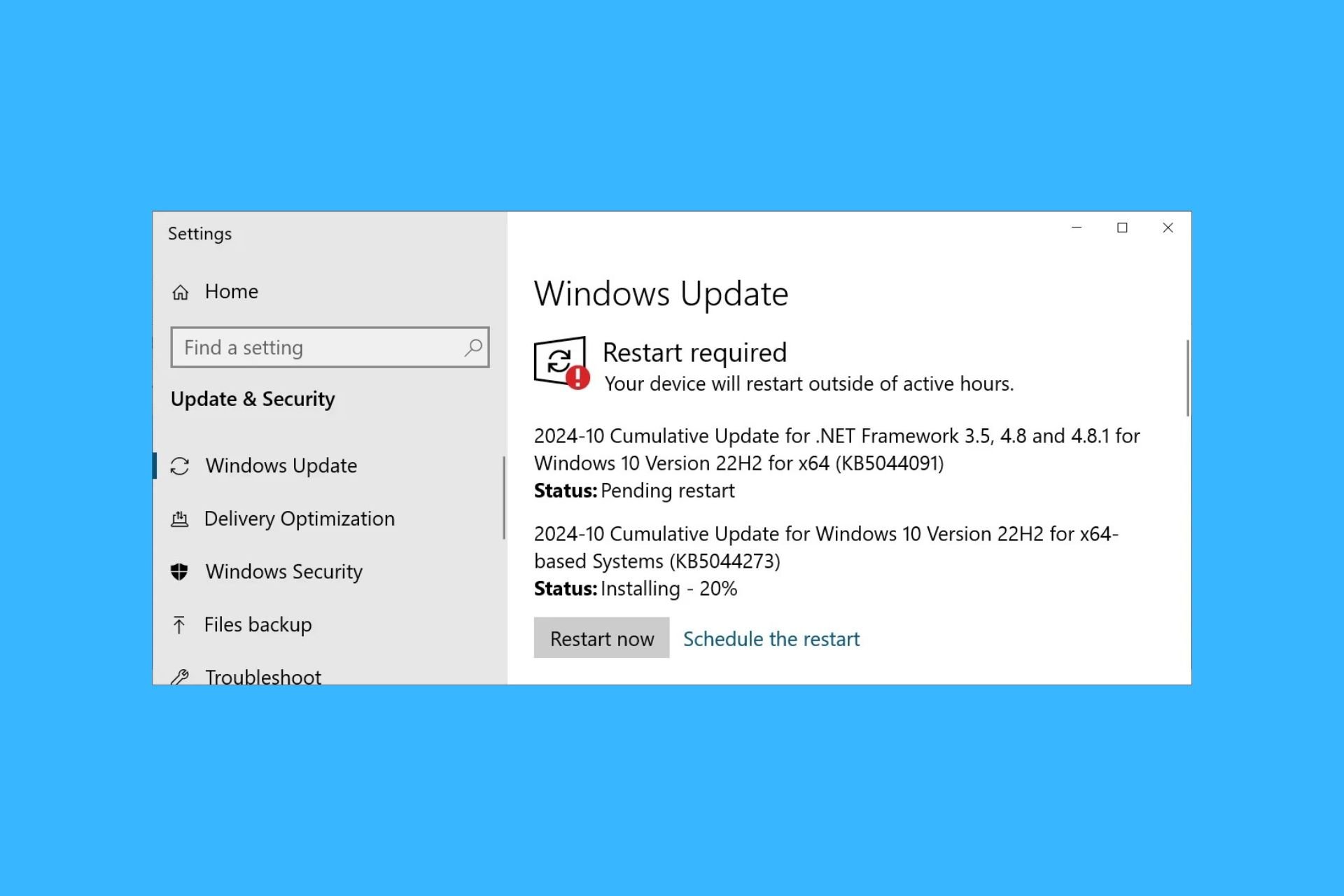
- The February Patch Tuesday updates are here, and they bring updates to all versions of Windows 10.
- This includes Windows 10 v1607 and it comes in the form of cumulative update KB4601318.
- It was reported that KB4601318 fixed several issues that resulted in error messages while using WIndows tools.
- Read more about it below and decide whether to install the update or not.
The Patch Tuesday updates for February have finally arrived, and, like always, they bring a host of new features that enrich the Windows 10 OS.
More so, these updates include enhancement to already-existent features and fixes to issues that have been around for a shorter or longer period of time.
Whichever the case, the updates are here and they are ready to download, although you must know that certain cumulative updates do have some issues associated with them.
Such would be the example of KB4601318 that applies to Windows 10 version 1607
KB4601318 fixes high CPU use, fatal error messages, and more
Among this month’s cumulative updates, KB4601318 addresses the most issues, according to the Microsoft changelog:
- Addresses an issue with a Service Host (svchost.exe) process that causes excessive CPU usage in some Input Method Editor (IME) language environments, such as Traditional Chinese. This issue occurs when you try to add an input method in Control Panel.
- Corrects historical daylight savings time (DST) information for the Palestinian Authority.
- Addresses an issue with German translations of Central European Time.
- Addresses an issue that causes LSASS.exe to stop working because of a race condition that results in a double free error in Schannel. The exception code is c0000374, and the Event Log displays Schannel event 36888, fatal error code 20, and error state 960. This issue occurs after installing Windows updates from September 2020 and later.
- Addresses an issue that might cause systems that use BitLocker to stop working and display the error 0x120 (BITLOCKER_FATAL_ERROR).
- Addresses an issue that prevents scheduled tasks that have multiple actions from running again if you have previously disabled them while they were running.
- Addresses an issue that fails to log events 4732 and 4733 for Domain-Local group membership changes in certain scenarios. This occurs when you use the “Permissive Modify” control; for example, the Active Directory (AD) PowerShell modules use this control.
- Addresses an issue that incorrectly reports that Lightweight Directory Access Protocol (LDAP) sessions are unsecure in Event ID 2889. This occurs when the LDAP session is authenticated and sealed with a Simple Authentication and Security Layer (SASL) method.
- Addresses an issue with Server Message Block (SMB). This issue incorrectly logs the Microsoft-Windows-SMBClient 31013 event in the Microsoft-Windows-SMBClient or Security event log of an SMB client when an SMB server returns STATUS_USER_SESSION_DELETED. This issue occurs when SMB client users or applications open multiple SMB sessions using the same set of Transmission Control Protocol (TCP) connections on the same SMB Server. This issue most likely occurs on Remote Desktop Servers.
- Addresses an issue that causes the LanmanServer service to stop unexpectedly. This issue occurs if the OptionalNames registry value is set and the service restarts.
- Addresses an issue that causes stop error 0x54 in SRV2.SYS.
While the two fixes regarding German and Palestinian localizations could be considered minor, the other issues that resulted in common error codes were probably the most expected among users.
Given the sheer number of fixes showcased, it is highly advisable that you get the latest Patch Tuesday update s as soon as they becopme available in your region.
Remember that installing these Patch Tuesday updates is important purely for security reasons.
More so, the identified issues only happen in a handful of cases, and not everyone that gets the cumulative update will automatically experience the.
If you do decide to install the latest Patch Tuesday updates, you can get them through multiple means, including:
- The WIndows Update Catalog
- The Windows Update menu in Windows 10
- The Windows Server Update Service (WSUS)
- Through Gorup policies set up by your network administrator
On the flip side, you can choose to postpone the updates for up to 35 days until the bugs and issues that you are trying to avoid are hopefully solved.
Let us know whether you decided to install the latest cumulative update or not by leaving us your feedback in the comments section below.



User forum
0 messages