KB5027231: Patch Tuesday comes with Security updates for you
Patch Tuesday updates are here and they focus on security.
13 min. read
Published on
Read our disclosure page to find out how can you help Windows Report sustain the editorial team. Read more
Key notes
- 73 CVEs are addressed in the update, ranging from moderate to critical.
- Chrome and GitHub vulnerabilities are also addressed.
- You can now download and install the KB5027231 release on your Windows 11.
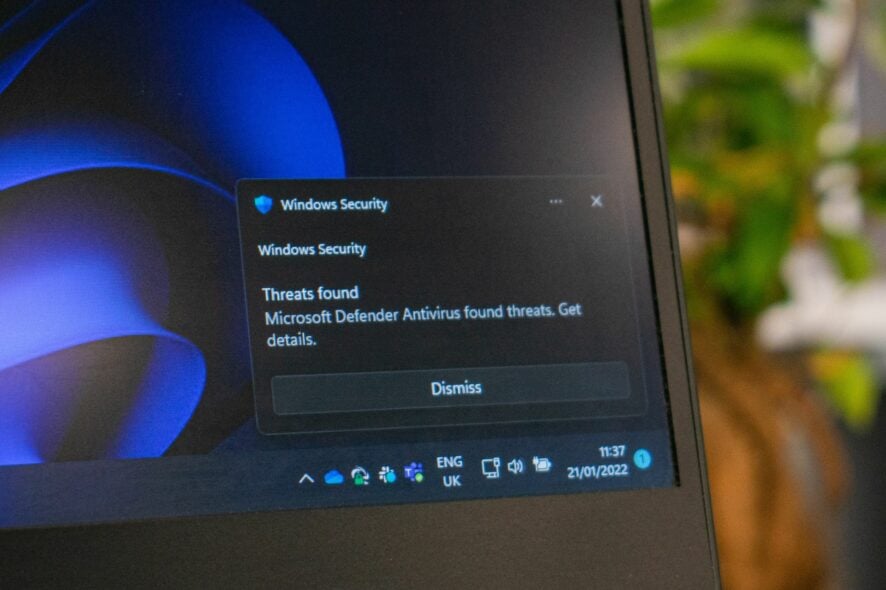
It’s that time of the month again. You guessed it. Patch Tuesday has arrived with some important security updates for Windows 11.
According to the Redmond-based tech giant, the KB5027231 specifically addresses security issues on your Windows 11, including improving on KB5026446‘s features on security.
It’s worth noting that this update focuses on no less than 73 CVEs that are either critical to moderate, and also offers support to 22 non-Microsoft CVEs, especially for Chrome and GitHub.
Fortunately, none of them is actively exploited at the moment, so you can catch your breath if you haven’t updated your Windows 11.
KB5027231: Here’s the complete list of CVEs Microsoft addressed on Patch Tuesday
Some of the most important CVEs addressed in this security update focus on critical CVEs that attack Visual Studio’s Net Framework, as well as Microsoft SharePoint Servers.
There is a particular CVE that is highly prone to attacks, CVE-2023-32013, and it concerns Windows Hyper-V Denial of Service, so you might want to update your system if it’s in your target.
Here’s the complete list of CVEs Microsoft addressed on Patch Tuesday.
| Tag | CVE | Base Score | CVSS Vector | Exploitability | FAQs? | Workarounds? | Mitigations? |
|---|---|---|---|---|---|---|---|
| Azure DevOps | CVE-2023-21565 | 7.1 | CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:L/A:N/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Azure DevOps | CVE-2023-21569 | 5.5 | CVSS:3.1/AV:N/AC:L/PR:L/UI:R/S:U/C:L/I:L/A:L/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| .NET and Visual Studio | CVE-2023-24895 | 7.8 | CVSS:3.1/AV:L/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Microsoft Dynamics | CVE-2023-24896 | 5.4 | CVSS:3.1/AV:N/AC:L/PR:L/UI:R/S:C/C:L/I:L/A:N/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| .NET and Visual Studio | CVE-2023-24897 | 7.8 | CVSS:3.1/AV:L/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| .NET and Visual Studio | CVE-2023-24936 | 8.1 | CVSS:3.1/AV:N/AC:H/PR:N/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Windows CryptoAPI | CVE-2023-24937 | 6.5 | CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:N/I:N/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | No | No | No |
| Windows CryptoAPI | CVE-2023-24938 | 6.5 | CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:N/I:N/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | No | No | No |
| Microsoft Exchange Server | CVE-2023-28310 | 8.0 | CVSS:3.1/AV:A/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation More Likely | Yes | No | No |
| .NET Framework | CVE-2023-29326 | 7.8 | CVSS:3.1/AV:L/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| .NET Core | CVE-2023-29331 | 7.5 | CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:N/I:N/A:H/E:P/RL:O/RC:C | Exploitation Less Likely | No | No | No |
| NuGet Client | CVE-2023-29337 | 7.1 | CVSS:3.1/AV:N/AC:H/PR:L/UI:R/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Microsoft Edge (Chromium-based) | CVE-2023-29345 | 6.1 | CVSS:3.1/AV:N/AC:L/PR:N/UI:R/S:C/C:L/I:L/A:N/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Windows NTFS | CVE-2023-29346 | 7.8 | CVSS:3.1/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Windows Group Policy | CVE-2023-29351 | 8.1 | CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:N/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Remote Desktop Client | CVE-2023-29352 | 6.5 | CVSS:3.1/AV:N/AC:L/PR:N/UI:R/S:U/C:N/I:H/A:N/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| SysInternals | CVE-2023-29353 | 5.5 | CVSS:3.1/AV:L/AC:L/PR:N/UI:R/S:U/C:N/I:N/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Windows DHCP Server | CVE-2023-29355 | 5.3 | CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:L/I:N/A:N/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | Yes |
| Microsoft Office SharePoint | CVE-2023-29357 | 9.8 | CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation More Likely | Yes | No | Yes |
| Windows GDI | CVE-2023-29358 | 7.8 | CVSS:3.1/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation More Likely | Yes | No | No |
| Windows Win32K | CVE-2023-29359 | 7.8 | CVSS:3.1/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation More Likely | Yes | No | No |
| Windows TPM Device Driver | CVE-2023-29360 | 7.8 | CVSS:3.1/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation More Likely | Yes | No | No |
| Windows Cloud Files Mini Filter Driver | CVE-2023-29361 | 7.0 | CVSS:3.1/AV:L/AC:H/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation More Likely | Yes | No | No |
| Remote Desktop Client | CVE-2023-29362 | 8.8 | CVSS:3.1/AV:N/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Windows PGM | CVE-2023-29363 | 9.8 | CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | Yes |
| Windows Authentication Methods | CVE-2023-29364 | 7.0 | CVSS:3.1/AV:L/AC:H/PR:L/UI:N/S:U/C:H/I:H/A:H/E:P/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Microsoft Windows Codecs Library | CVE-2023-29365 | 7.8 | CVSS:3.1/AV:L/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Windows Geolocation Service | CVE-2023-29366 | 7.8 | CVSS:3.1/AV:L/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Windows OLE | CVE-2023-29367 | 7.8 | CVSS:3.1/AV:L/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Windows Filtering | CVE-2023-29368 | 7.0 | CVSS:3.1/AV:L/AC:H/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Windows Remote Procedure Call Runtime | CVE-2023-29369 | 6.5 | CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:N/I:N/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | No | No | No |
| Microsoft Windows Codecs Library | CVE-2023-29370 | 7.8 | CVSS:3.1/AV:L/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Windows Win32K | CVE-2023-29371 | 7.8 | CVSS:3.1/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation More Likely | Yes | No | No |
| Microsoft WDAC OLE DB provider for SQL | CVE-2023-29372 | 8.8 | CVSS:3.1/AV:N/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Windows ODBC Driver | CVE-2023-29373 | 8.8 | CVSS:3.1/AV:N/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Windows Resilient File System (ReFS) | CVE-2023-32008 | 7.8 | CVSS:3.1/AV:L/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Windows Collaborative Translation Framework | CVE-2023-32009 | 8.8 | CVSS:3.1/AV:L/AC:L/PR:L/UI:N/S:C/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Windows Bus Filter Driver | CVE-2023-32010 | 7.0 | CVSS:3.1/AV:L/AC:H/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Windows iSCSI | CVE-2023-32011 | 7.5 | CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:N/I:N/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | No | No | No |
| Windows Container Manager Service | CVE-2023-32012 | 6.3 | CVSS:3.1/AV:L/AC:H/PR:L/UI:N/S:U/C:N/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Windows Hyper-V | CVE-2023-32013 | 6.5 | CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:N/I:N/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Windows PGM | CVE-2023-32014 | 9.8 | CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | Yes |
| Windows PGM | CVE-2023-32015 | 9.8 | CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | Yes |
| Windows Installer | CVE-2023-32016 | 5.5 | CVSS:3.1/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:N/A:N/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Microsoft Printer Drivers | CVE-2023-32017 | 7.8 | CVSS:3.1/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Windows Hello | CVE-2023-32018 | 7.8 | CVSS:3.1/AV:L/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Windows Kernel | CVE-2023-32019 | 4.7 | CVSS:3.1/AV:L/AC:H/PR:L/UI:N/S:U/C:H/I:N/A:N/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Role: DNS Server | CVE-2023-32020 | 3.7 | CVSS:3.1/AV:N/AC:H/PR:N/UI:N/S:U/C:N/I:L/A:N/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Windows SMB | CVE-2023-32021 | 7.1 | CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:N/I:L/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | Yes |
| Windows Server Service | CVE-2023-32022 | 7.6 | CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:L/I:L/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | Yes |
| Microsoft Power Apps | CVE-2023-32024 | 3.0 | CVSS:3.1/AV:N/AC:H/PR:L/UI:R/S:C/C:L/I:N/A:N/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Microsoft Office Excel | CVE-2023-32029 | 7.8 | CVSS:3.1/AV:L/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| .NET and Visual Studio | CVE-2023-32030 | 7.5 | CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:N/I:N/A:H/E:P/RL:O/RC:C | Exploitation Less Likely | No | No | No |
| Microsoft Exchange Server | CVE-2023-32031 | 8.8 | CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation More Likely | Yes | No | No |
| .NET and Visual Studio | CVE-2023-32032 | 6.5 | CVSS:3.1/AV:L/AC:H/PR:L/UI:N/S:U/C:L/I:H/A:H/E:P/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| .NET and Visual Studio | CVE-2023-33126 | 7.3 | CVSS:3.1/AV:L/AC:L/PR:L/UI:R/S:U/C:H/I:H/A:H/E:P/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| .NET and Visual Studio | CVE-2023-33127 | 8.1 | CVSS:3.1/AV:N/AC:H/PR:N/UI:N/S:U/C:H/I:H/A:H/E:P/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| .NET and Visual Studio | CVE-2023-33128 | 7.3 | CVSS:3.1/AV:L/AC:L/PR:L/UI:R/S:U/C:H/I:H/A:H/E:P/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Microsoft Office SharePoint | CVE-2023-33129 | 6.5 | CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:N/I:N/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Microsoft Office SharePoint | CVE-2023-33130 | 7.3 | CVSS:3.1/AV:N/AC:L/PR:L/UI:R/S:U/C:H/I:H/A:N/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Microsoft Office Outlook | CVE-2023-33131 | 8.8 | CVSS:3.1/AV:N/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Microsoft Office SharePoint | CVE-2023-33132 | 6.3 | CVSS:3.1/AV:N/AC:L/PR:L/UI:R/S:U/C:H/I:L/A:N/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Microsoft Office Excel | CVE-2023-33133 | 7.8 | CVSS:3.1/AV:L/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| .NET and Visual Studio | CVE-2023-33135 | 7.3 | CVSS:3.1/AV:L/AC:L/PR:L/UI:R/S:U/C:H/I:H/A:H/E:P/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Microsoft Office Excel | CVE-2023-33137 | 7.8 | CVSS:3.1/AV:L/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Visual Studio | CVE-2023-33139 | 5.5 | CVSS:3.1/AV:L/AC:L/PR:N/UI:R/S:U/C:H/I:N/A:N/E:P/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Microsoft Office OneNote | CVE-2023-33140 | 6.5 | CVSS:3.1/AV:N/AC:L/PR:N/UI:R/S:U/C:H/I:N/A:N/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| ASP .NET | CVE-2023-33141 | 7.5 | CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:N/I:N/A:H/E:P/RL:O/RC:C | Exploitation Less Likely | No | No | No |
| Microsoft Office SharePoint | CVE-2023-33142 | 6.5 | CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:N/I:H/A:N/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Microsoft Edge (Chromium-based) | CVE-2023-33143 | 7.5 | CVSS:3.1/AV:N/AC:H/PR:N/UI:R/S:C/C:L/I:L/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Visual Studio Code | CVE-2023-33144 | 5.0 | CVSS:3.1/AV:L/AC:L/PR:L/UI:R/S:U/C:H/I:N/A:N/E:P/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Microsoft Edge (Chromium-based) | CVE-2023-33145 | 6.5 | CVSS:3.1/AV:N/AC:L/PR:N/UI:R/S:U/C:H/I:N/A:N/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Microsoft Office | CVE-2023-33146 | 7.8 | CVSS:3.1/AV:L/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
On the other hand, the updates also add support for Bluetooth Low Energy audio. If you remember, this particular feature will let you use your wireless Bluetooth headphones much longer while providing the same audio quality.
The technology doesn’t take a lot of your devices’ battery, allowing for a sustainable way to enjoy your music, podcasts, and whatever you’re listening to.
Here’s the list of the other improvements coming to Windows 11 with this new update.
Improvements
- This update addresses a known issue that affects 32-bit apps that are large address aware and use the CopyFile API. You might have issues when you save, copy, or attach files. If you use some commercial or enterprise security software that uses extended file attributes, this issue will likely affect you. For Microsoft Office apps, this issue only affects the 32-bit versions. You might receive the error, “Document not saved.”
- This update addresses a compatibility issue. The issue occurs because of unsupported use of the registry.
- This update addresses an issue that affects the Windows Kernel. This issue is related to CVE-2023-32019. To learn more, see KB5028407.
What do you think about these Patch Tuesday updates? Be sure to let us know in the comments section below.



User forum
0 messages