TechBrolo malware: How it works and how to remove it
10 min. read
Updated on
Read our disclosure page to find out how can you help Windows Report sustain the editorial team. Read more
Key notes
- TechBrollo is a malware that fakes all sorts of alerts so that you access so-called tech support services and pay a fee.
- You can remove this malicious software manually by stopping its processes and clearing all its traces from the Registry.
- An offline scan with the built-in antivirus can also help you get rid of this problem.
- Using a third-party security solution can increase, however, the chances of removal.
This article covers everything you need to know about the TechBrolo malware or supportscam:js/techbrolo!rfn, what it is, how it works, and how to completely remove it from your computer.
Malware simply means malicious software (or badware), and these are created with the intent to harm or destroy your data, and devices.
This malware is hosted on malicious sites, which is why it takes the form of advertising or paid search results, cold calls from tech support agents, popup warnings or ads, and popular email scams.
What is TechBrolo Malware and how it infects your computer?
TechBrolo is a JavaScript malware (Trojan), usually classified as rogue, or support scam.
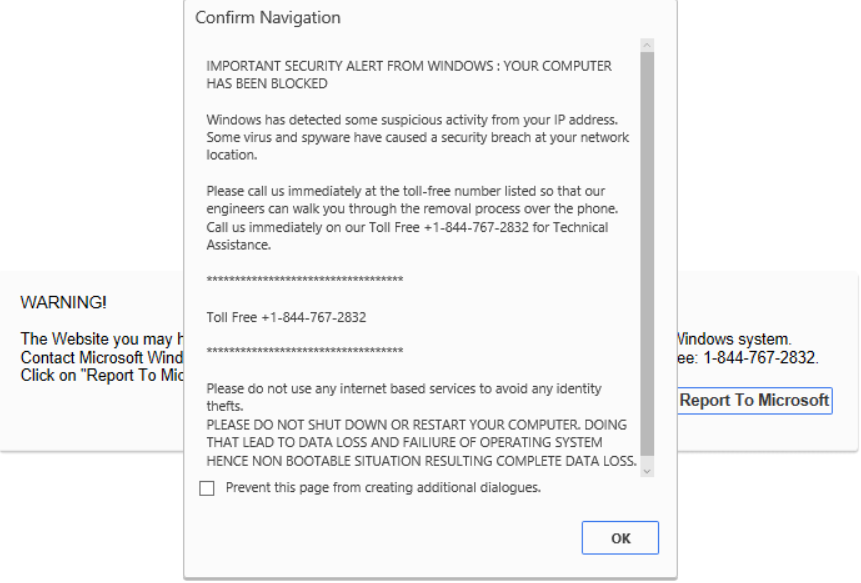
The main characteristic of the TechBrolo virus is the fake alerts that require you to call tech support, then pay a fee in order to get assistance.
How TechBrolo gets into your computer system?
Unsuspecting users are tricked into downloading freeware, or opening spam emails, and other third-party installation setups, which ideally is an open door for letting TechBrolo, and other malware in.
Sometimes the usual activity such as playing online games, downloading pirated software, using infected devices, visiting suspicious links such as popups or torrents can get you into trouble.
Updating your programs or applications from unsupported links is also a sure way for TechBrolo to gain access.
Once in, TechBrolo wastes no time and immediately adds malicious codes that corrupt your files and compromise your computer’s security.
Some symptoms you will begin to see (or probably have already) manifest because of TechBrolo include:
- Bogus popup warnings, and alerts that your computer is at risk due to critical error or severe virus or malware
- Notice that you should purchase a registered version to overcome those issues
If left unchecked, TechBrolo malware can degrade your system’s performance, change your browser settings and redirect to unusual sites.
It can also insert unknown infections and malicious codes to your Registry Editor and other executable files, keep sending fake error warnings and slows down network connectivity.
What’s worse is that it steals private data (like IP address, login credentials, browsing history etc.) and the next thing is to find out that you have less money in your account.
How can I remove TechBrolo malware from my PC?
1. Remove TechBrolo malware manually
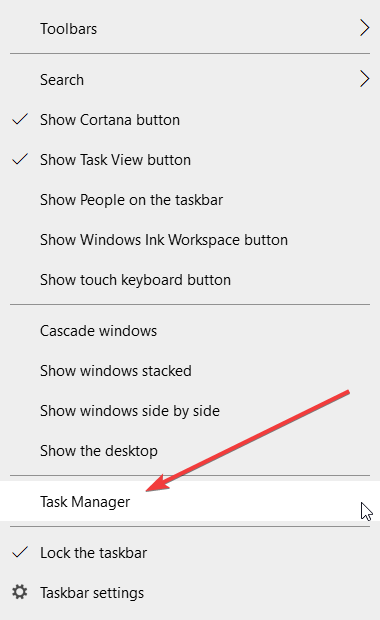
1.1 End the process in Task Manager
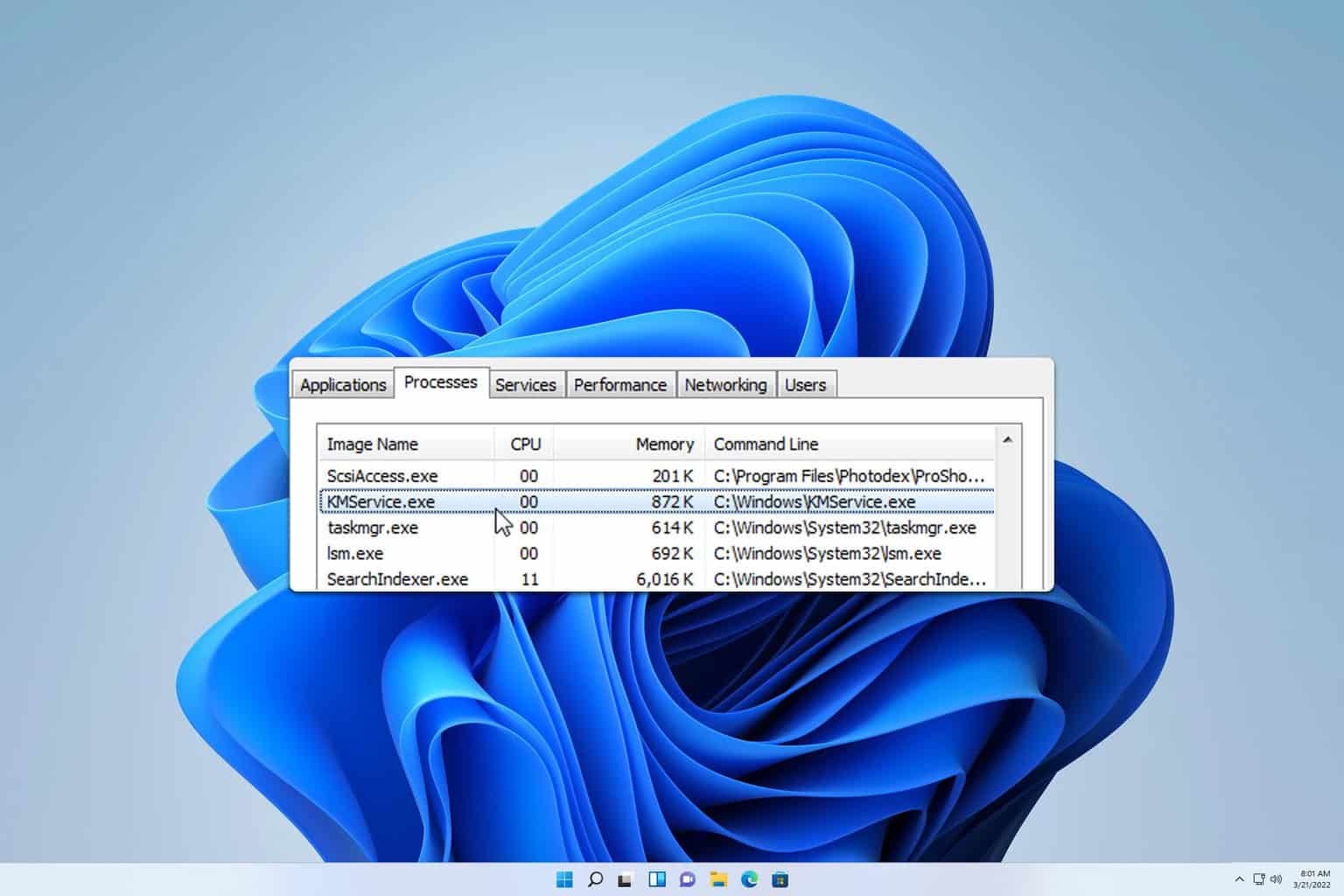
- Right-click the Start button and select Task Manager from the list.
- Click on Processes.
- Identify any process related to Rogue:JS/TechBrolo, select it, then click on the End task button.
This is a preliminary action you need to take in order to be able to remove it from your registry.
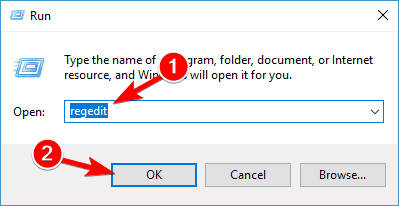
1.2 Remove the registry files
- Press the Windows key + R to open the Run window.
- Type regedit and press Enter or click OK.
- Find all registry files related to Rogue:JS/TechBrolo.
Removing the registry files related to this malware is essential for getting rid of it so try that out.
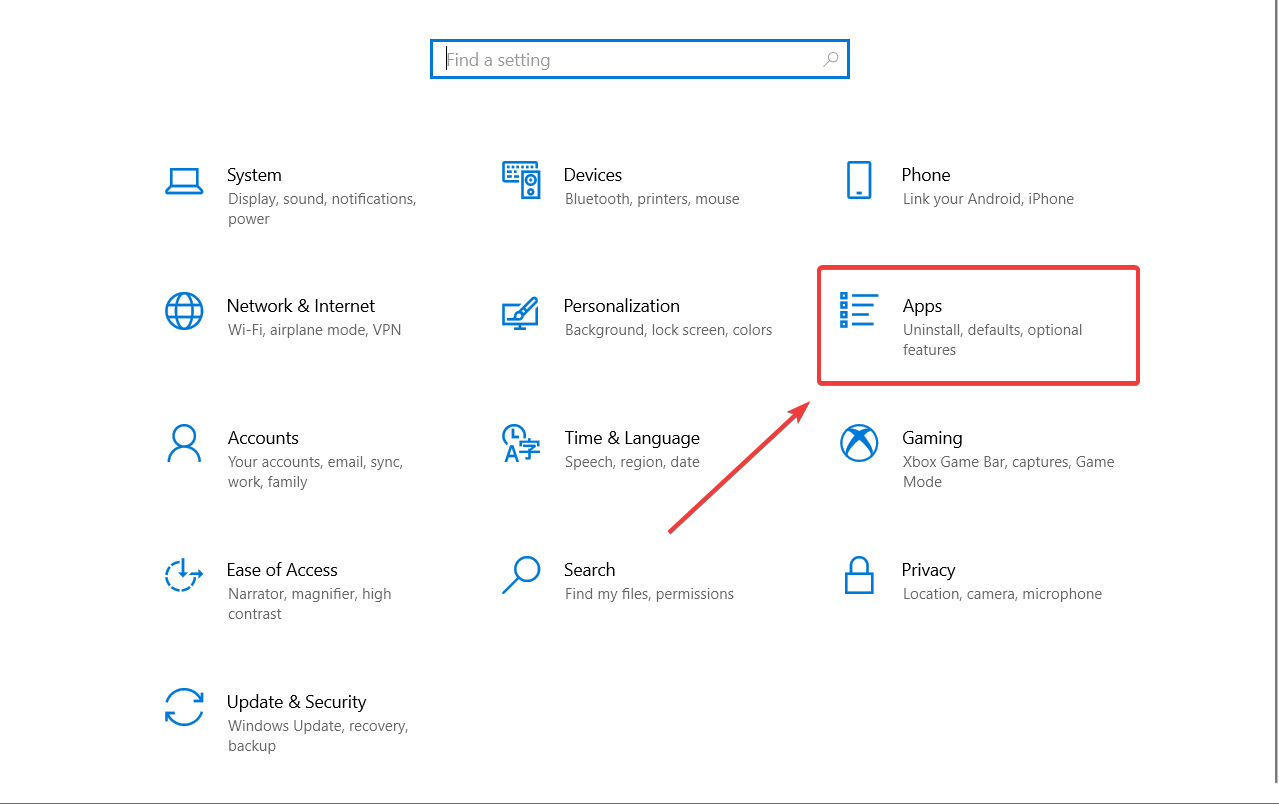
1.3 Remove the apps related to the malware
- Type control in Windows search and select Control Panel from results.
- Click on Apps.
- Find Rogue:JS/TechBrolo and related software, select it, then click on the Uninstall button.
- Follow the instructions on the screen to get through with the uninstallation.
Finally, reboot your computer, and see if there is any remaining suspicious programs in the system.
3. Use a more effective, third-party antivirus
Windows Defender can be a great tool for basic protection, but when it comes to dangerous malware like Rogue:JS/TechBrolo, you will probably need a more powerful ally.
The security solution recommended below can pack a big punch in detecting and removing all malware from your PC.
Moreover, after you will scan your computer and get rid of this pesky threat, you will still be left with one of the best protection tools for your PC.
With just one license you will be able to protect all your devices, including your smartphone, your router and even your webcam so you won’t ever need to go through this again.
This antivirus comes with anti-phishing, anti-ransomware and anti-malware protection and it’s trusted by over 110 million of users around the world so give it a try.

ESET HOME Security Premium
Remove any malware from your PC right away and further protect your system with this great tool.4. Perform a scan using Windows Defender
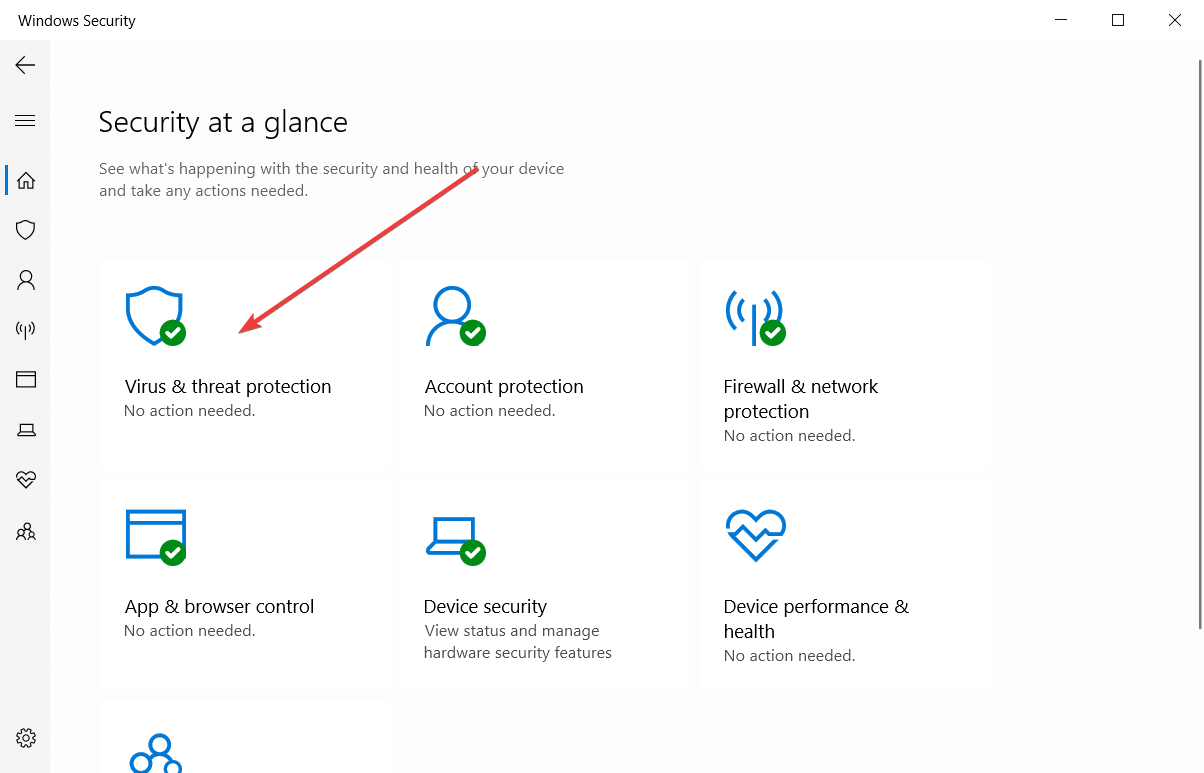
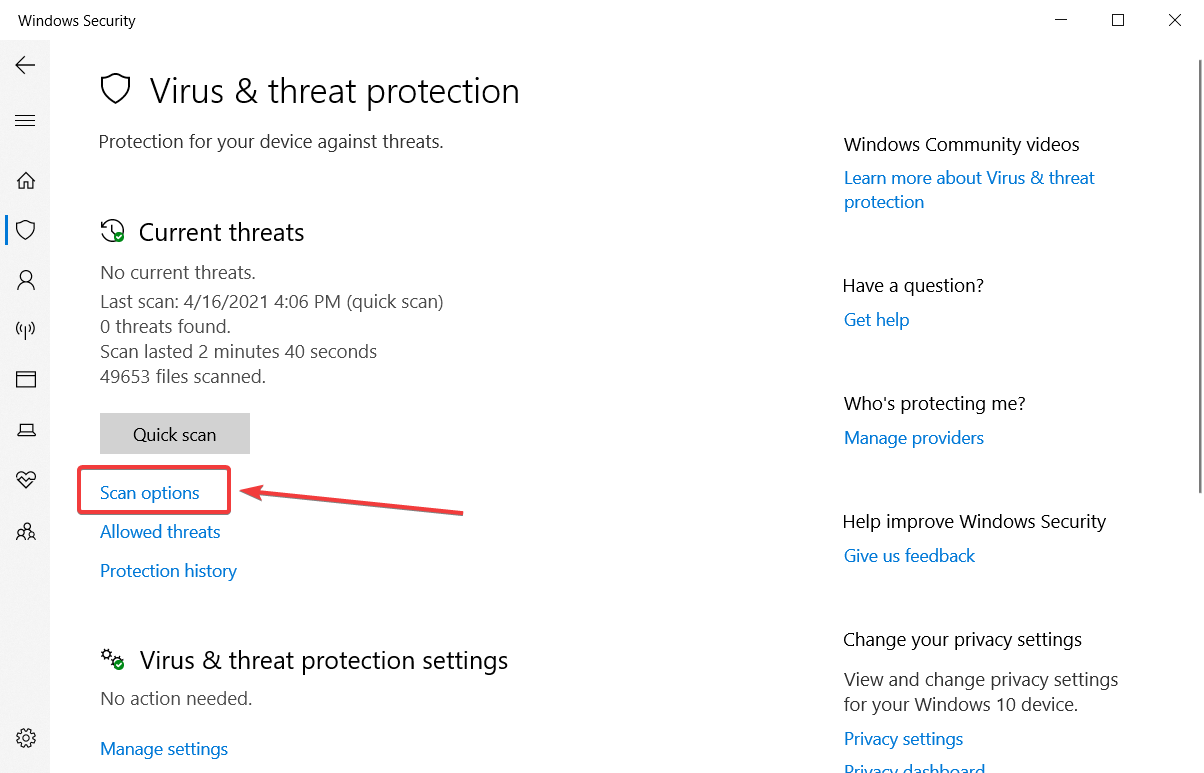
- Click on the shield from the taskbar notification area from the bottom right corner to open Windows Security.
- Choose Virus & threat protection.
- Select Scan options under the Quick scan button.
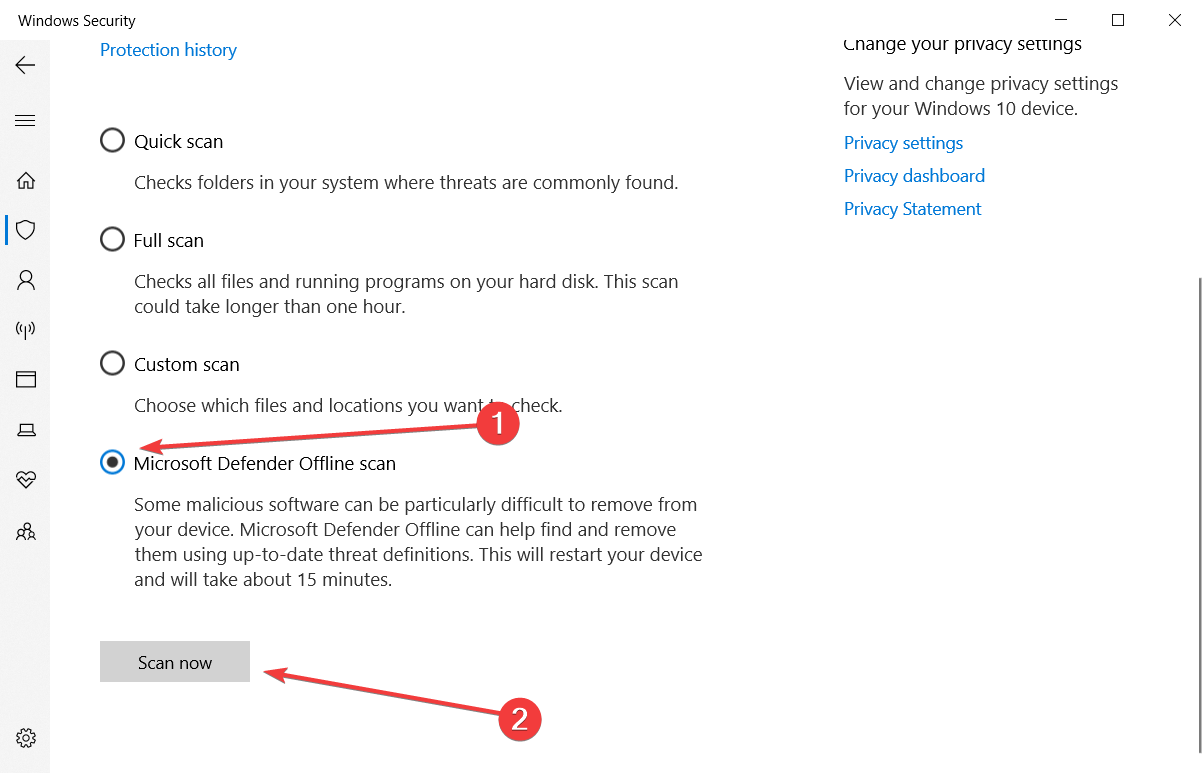
- Scroll down and click on the Windows Defender Offline scan.
- Click Scan now.
- Your PC will restart and the scanning process will begin.
This is an important step in the process of eliminating the malware as the native antivirus tool from Windows can be effective.
5. Use a dedicated software
If you already performed the steps above, the malware should have gone away and your PC should be safe now.
However, if it had time to act and the antivirus eliminated all the infected files, you will be left with programs that are not functioning properly.
That means you will have to uninstall and reinstall them again. You’ve seen how to uninstall any apps in step 1.3 above.
Unfortunately, the standard uninstallation procedures are not perfect and some files will still reside on your computer, and they may block or clog a future install of the same program.
The solution is to use a dedicated PC cleaning utility that will eliminate absolutely all traces of the program you want to uninstall.
We recommend CCleaner because quick, light on your system, and performs the steps automatically so you won’t bother with any technicalities.
6. Remove TechBrolo extensions and add-ons
If you’re using Chrome, internet Explorer, Firefox, or Microsoft Edge, here’s how to remove any extensions and add-ons related to TechBrolo malware.
Remember, TechBrolo brings changes to your browser settings, so you also need to clean it up.
Chrome
- Open Google Chrome.
- Click the menu button (the three vertical dots on the top right corner) on the Chrome browser toolbar.
- Select More tools and click on Extensions.
- Click the trash icon on the extensions you want to get rid of.
- Select Remove on the dialog that appears.
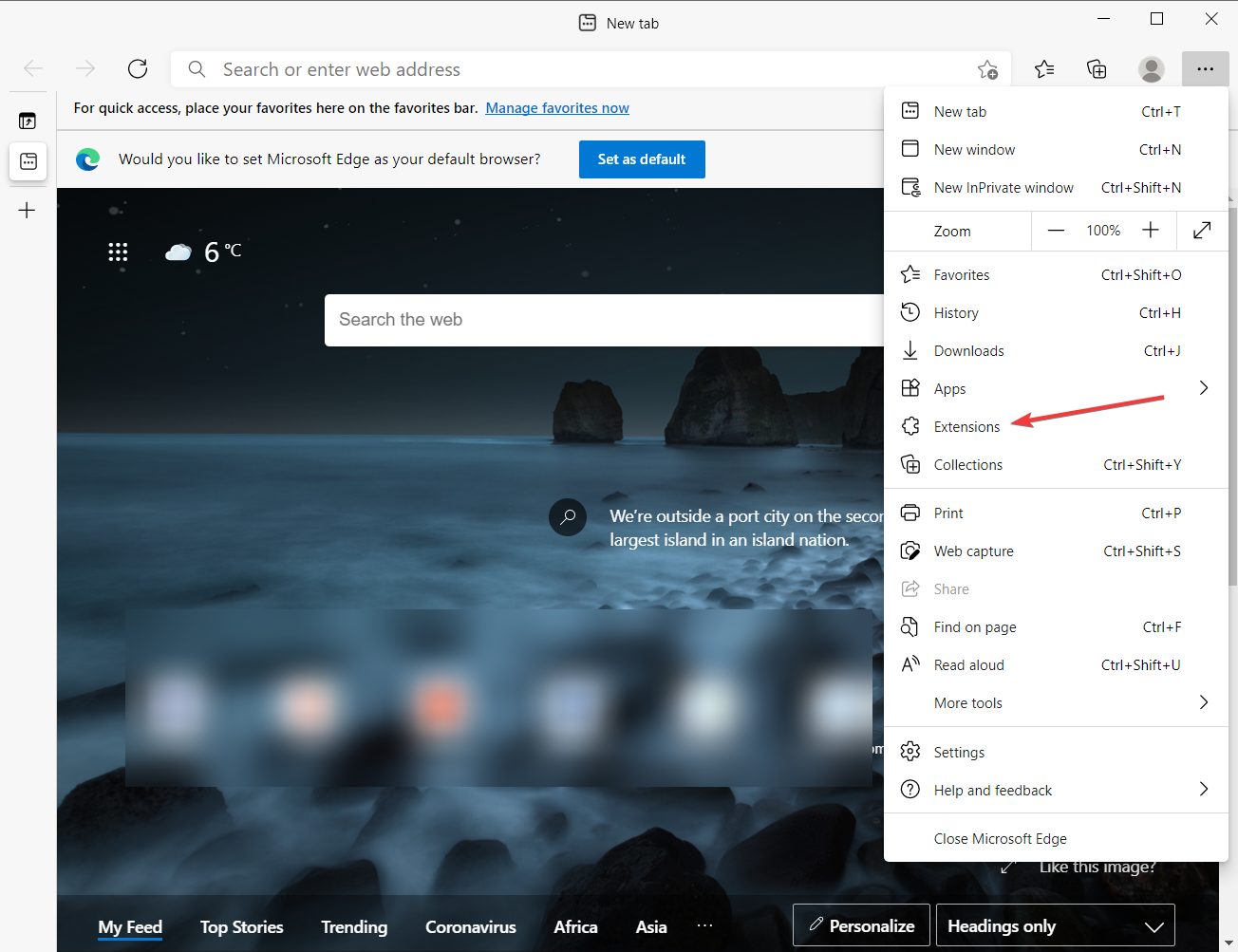
Microsoft Edge
- Open Microsoft Edge.
- Click on the menu button (the three horizontal dots from the top right corner).
- Select Extensions.
- Remove any extensions connected with this malware.
To reset all settings to default click on the menu, and select Settings, then click on the three horizontal lines from the top left corner and select Reset settings.
Finally, click on Restore settings to their default values and click again on the Reset button.
This procedure will reset all settings, including start-up pages, will disable the extensions, clear all cookies and history, but it won’t delete your passwords.
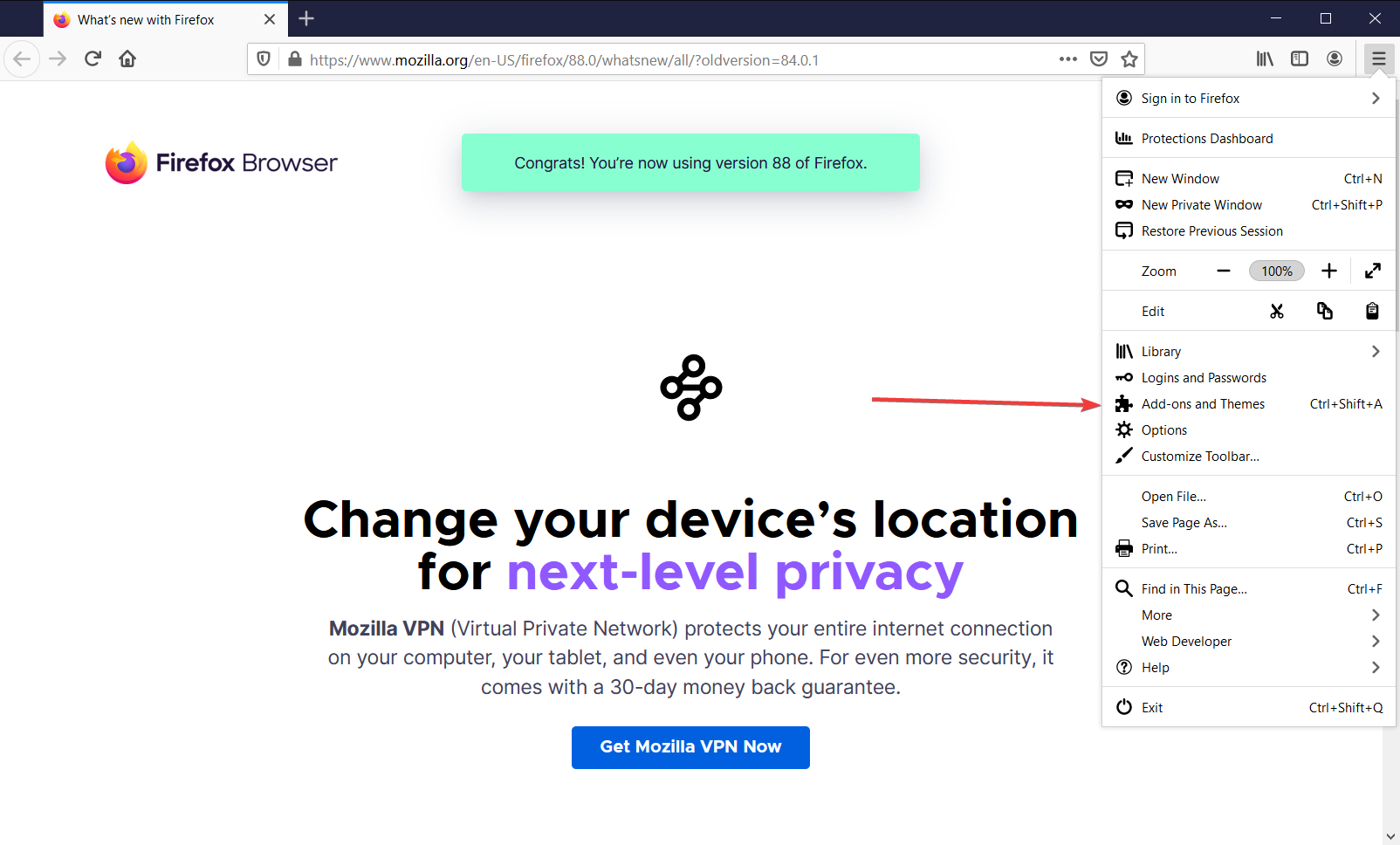
Firefox
- Open Firefox.
- Go to the menu and choose Add-ons and Themes.
- Select Extensions.
- Remove unwanted extensions.
- Click Disable/Remove.
- Select Restart now (in case it pops up).
Hopefully, you managed to clear all problematic extensions and add-ons from all your browsers and you are now completely safe.
Tips to prevent malware attacks
In order to protect your computer from any future malware entry or attacks, here are some tips you can use:
- Use strong passcodes and two-step verification where applicable.
- Connect to secure Wi-Fi.
- Keep your system regularly updated.
- Block popups and turn off auto-fill when you revisit a website to prevent identity theft.
- Clean up your desktop to speed up your computer.
- Install an antivirus if you don’t have one.
- Conduct regular scans.
- Clean up your disk drive and defragment your computer (speeds up the machine).
- Always check your downloads and delete what you don’t need.
- Backup important files – you can also back up your data offline (using storage disks) or online (cloud storage) – as often as daily.
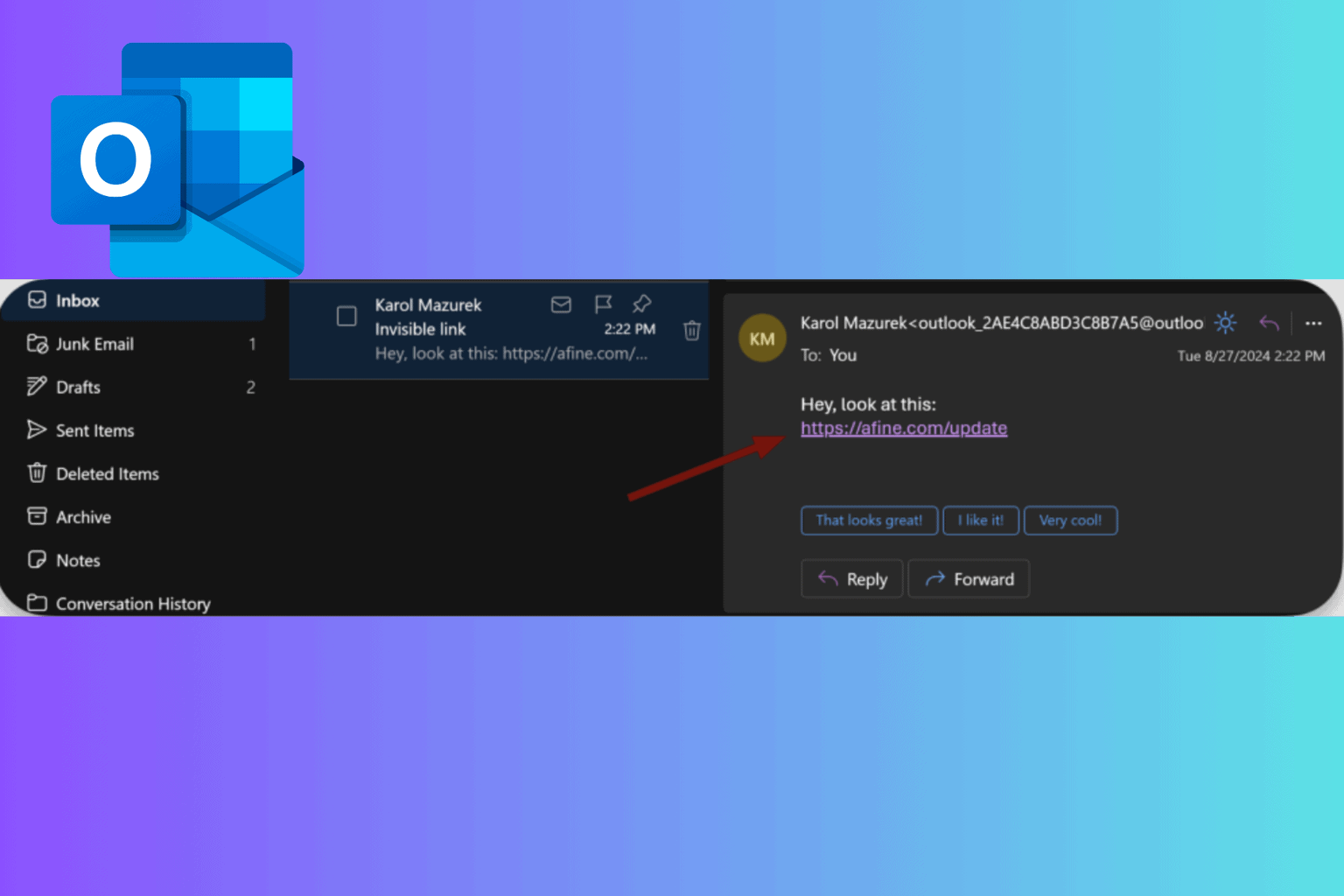
- Avoid opening spam emails, suspicious links, visiting unknown websites, and making purchases from unverified sellers.
Types of malware
Virus: Just like viruses that affect the human system, computer viruses attach themselves to your files and infect them, then spread hysterically while corrupting your files (sometimes deleting them) and damaging your system’s functionalities. These usually appear on your laptop as .exe or executable files.
Ransomware: This type holds your computer hostage threatening to destroy or erase your files and data, unless a ransom is paid to its creator.
Trojan: The Trojan horse comes across as legitimate software but hides among your other clean files and if it goes unnoticed, it moves silently, creating backdoors in your computer’s security system, which then allows other malware into your system.
Spyware: As its name suggests, this malware is meant to spy on your system. It hides in your system, taking stock of all your online activities while saving important and private details such as your passwords, credit card details, and your browsing history.
Worms: This type infects your devices using your network’s interface. The more devices they find their way into, the higher the rates of infection.
Adware: This disguises itself through advertising software that can compromise your computer’s security system to serve you with ads, which then let in more malware.
Checklist of the common warning signs for malware infection
- Unexpected onscreen ads appear, some say virus detected, but they’re rogue;
- An audio message starts playing;
- Popups that ask you to pay for a program to remove a virus;
- System is slow when starting up, and overall performance is sluggish (and it’s not caused by your computer memory);
- Lack of storage space on your hard drive;
- Files are missing, or are encrypted;
- System freezes or shuts down;
- Programs open and close automatically;
- Odd error messages;
- Your hard disk is excessively active – warning signs include continual noises or constant spins even when not using your computer;
- Sluggish web browser;
- The browser on your home page keeps changing or you keep being redirected to unusual websites;
- Increased activity (from the usual) on your Internet connection;
- Email and social media pages hijacked – this is common today when your email contacts and social media; acquaintances or friends, receive messages from you that you didn’t post or send;
- Computer security is compromised such that you cannot install or even open your antivirus program or firewall;
- You’re unable to use common tools such as Task Manager or Registry Editor;
- You get a message saying your administrator has disabled this…;
- A program demands that you pay a ransom before accessing your files again;
- A security program sends scary popup warnings, yet you never installed it in the first place;
- Sometimes everything may look okay, but some malware like bots hide quietly waiting for instruction before executing commands, or a remote Trojan is busy picking up information; always run a scan to be sure.
Keep your computer healthy, and it will serve you well for a long time. We hope that our solutions and tips helped you get rid of the malware on your PC.
The TechBrolo malware can hit the offices of your business too so be proactive and get yourself one of the best antiviruses for Windows Server and protect your company data.
Did you manage to safeguard your computer using our solutions? Do you have others instead? Let us know how you did in the comments section below.




User forum
0 messages